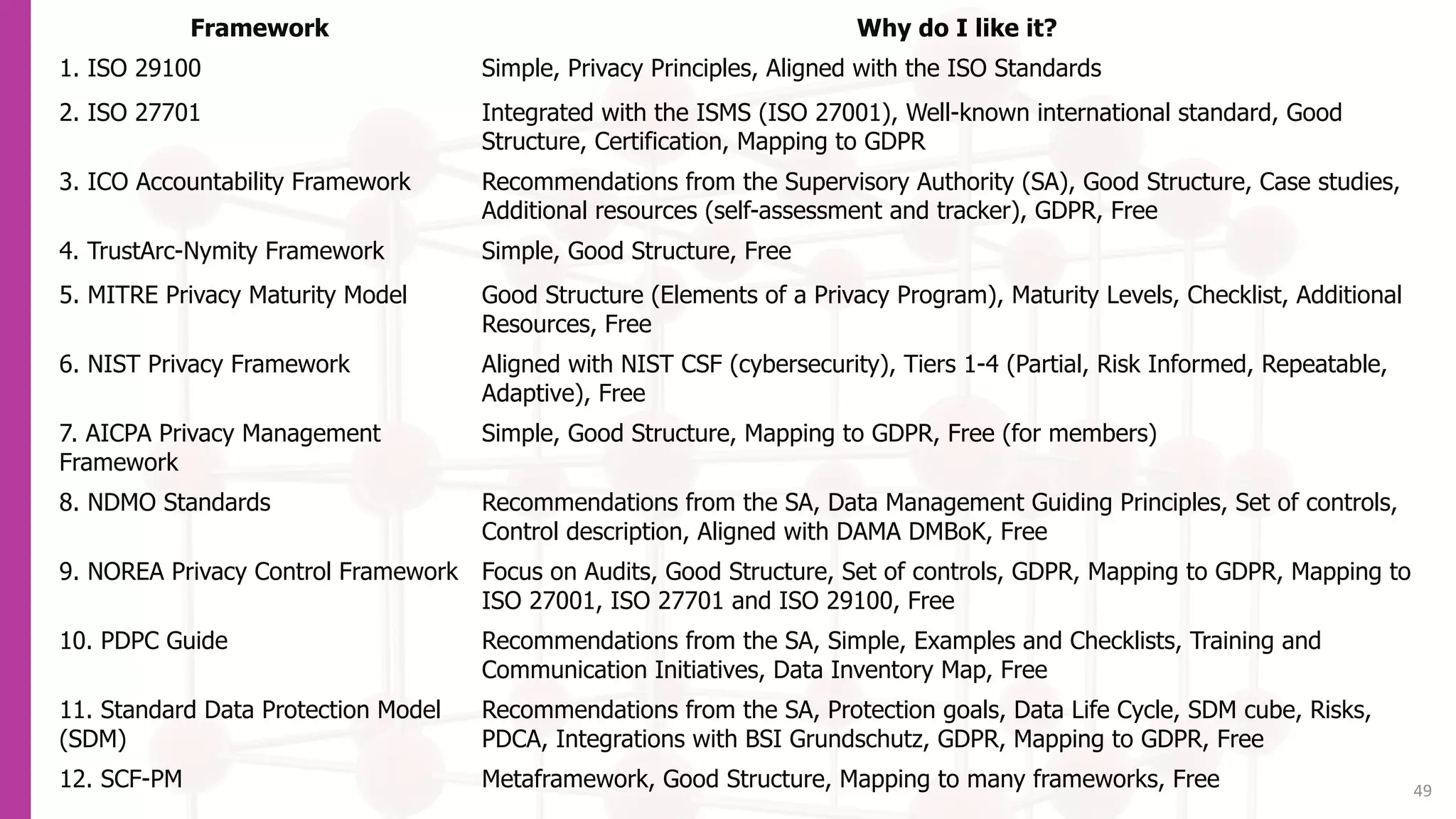
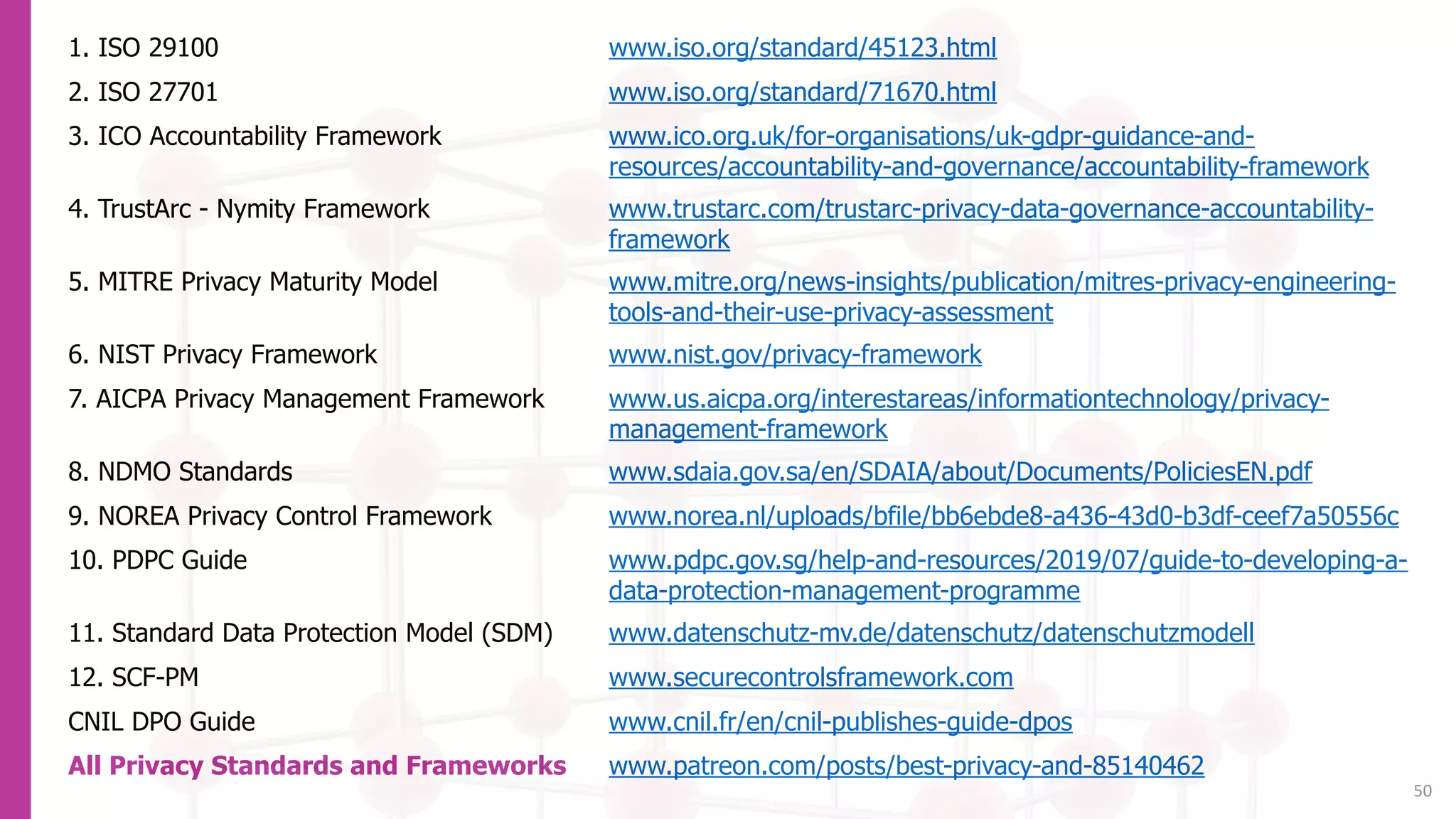
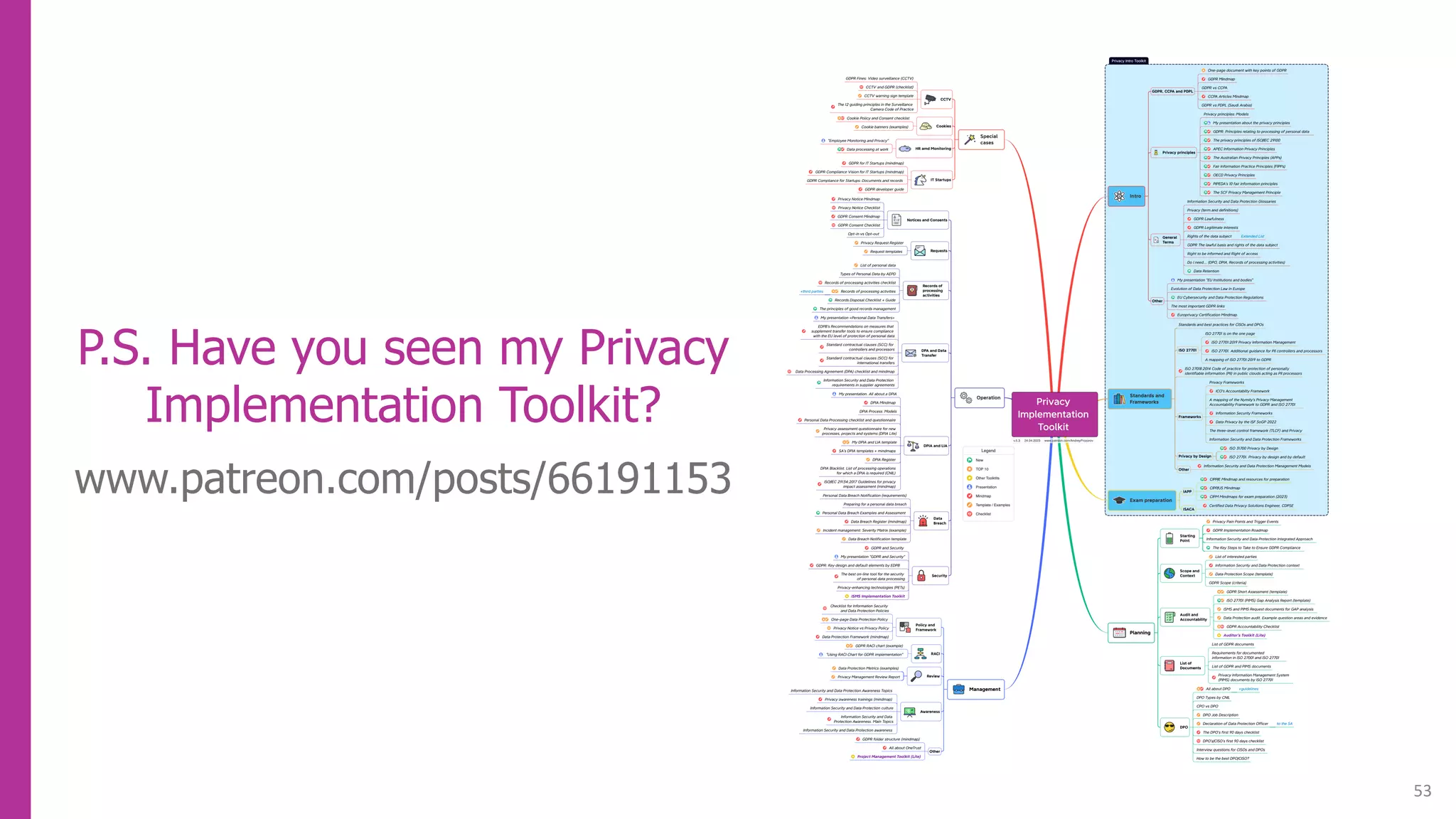
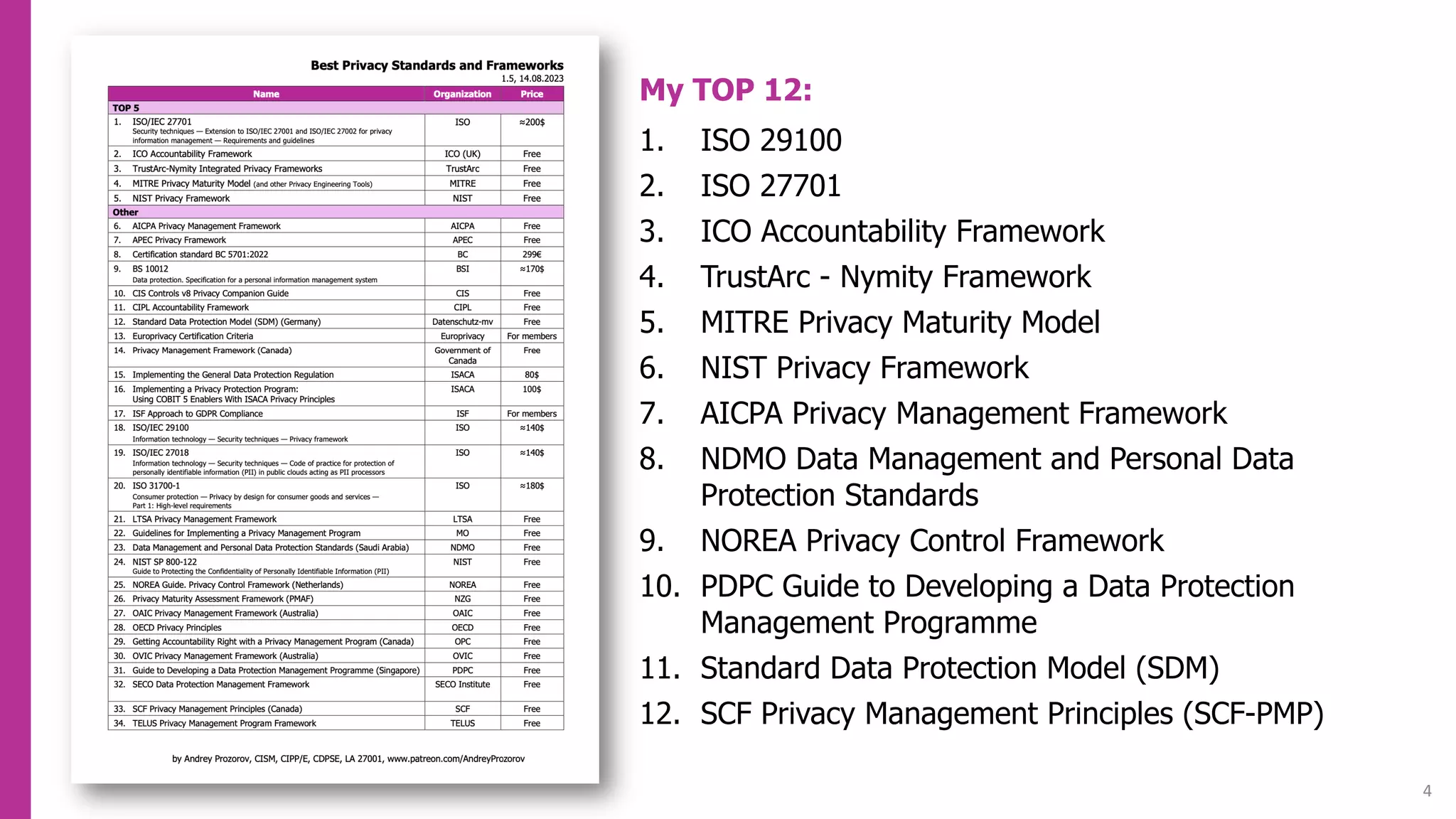
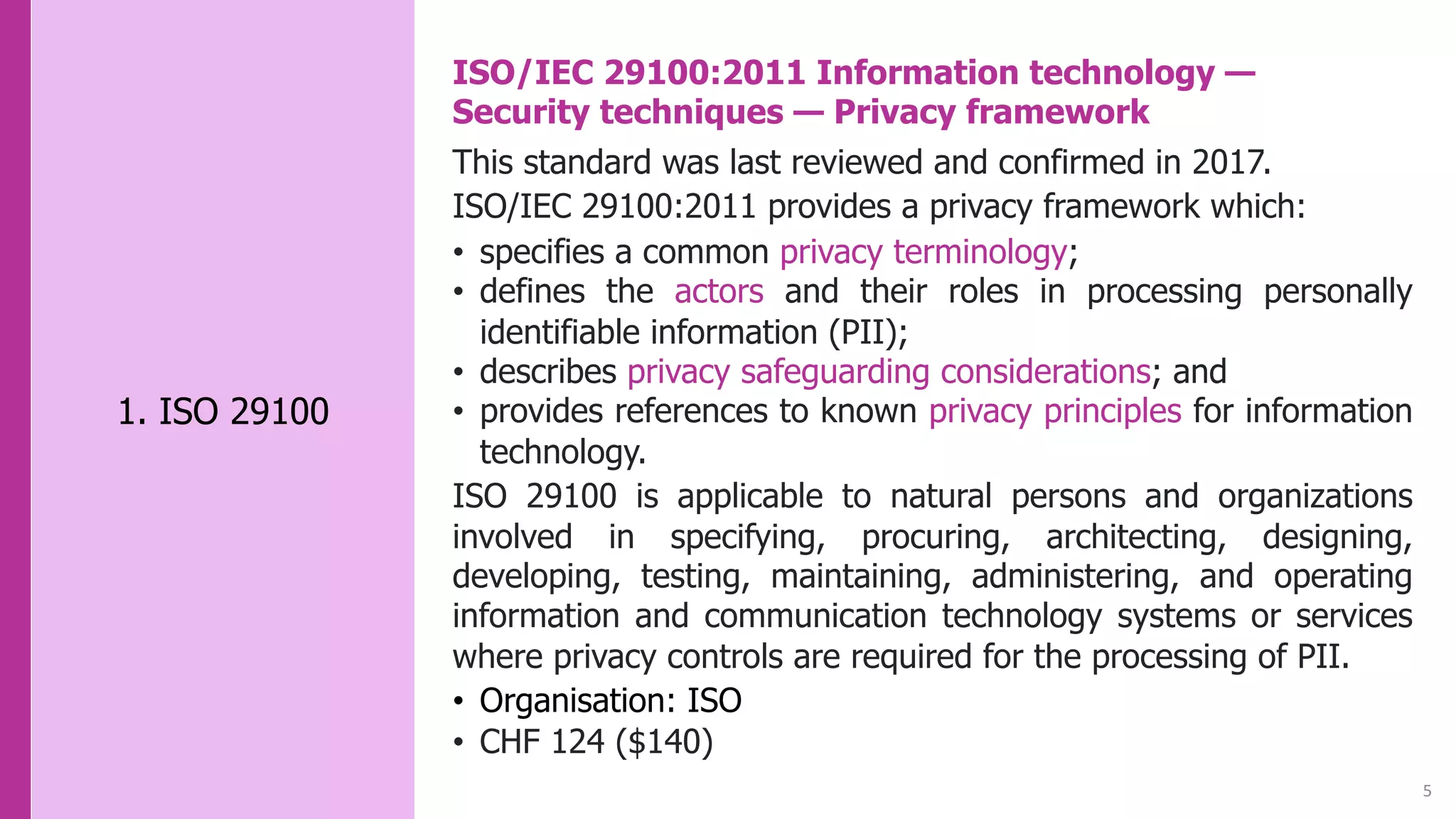
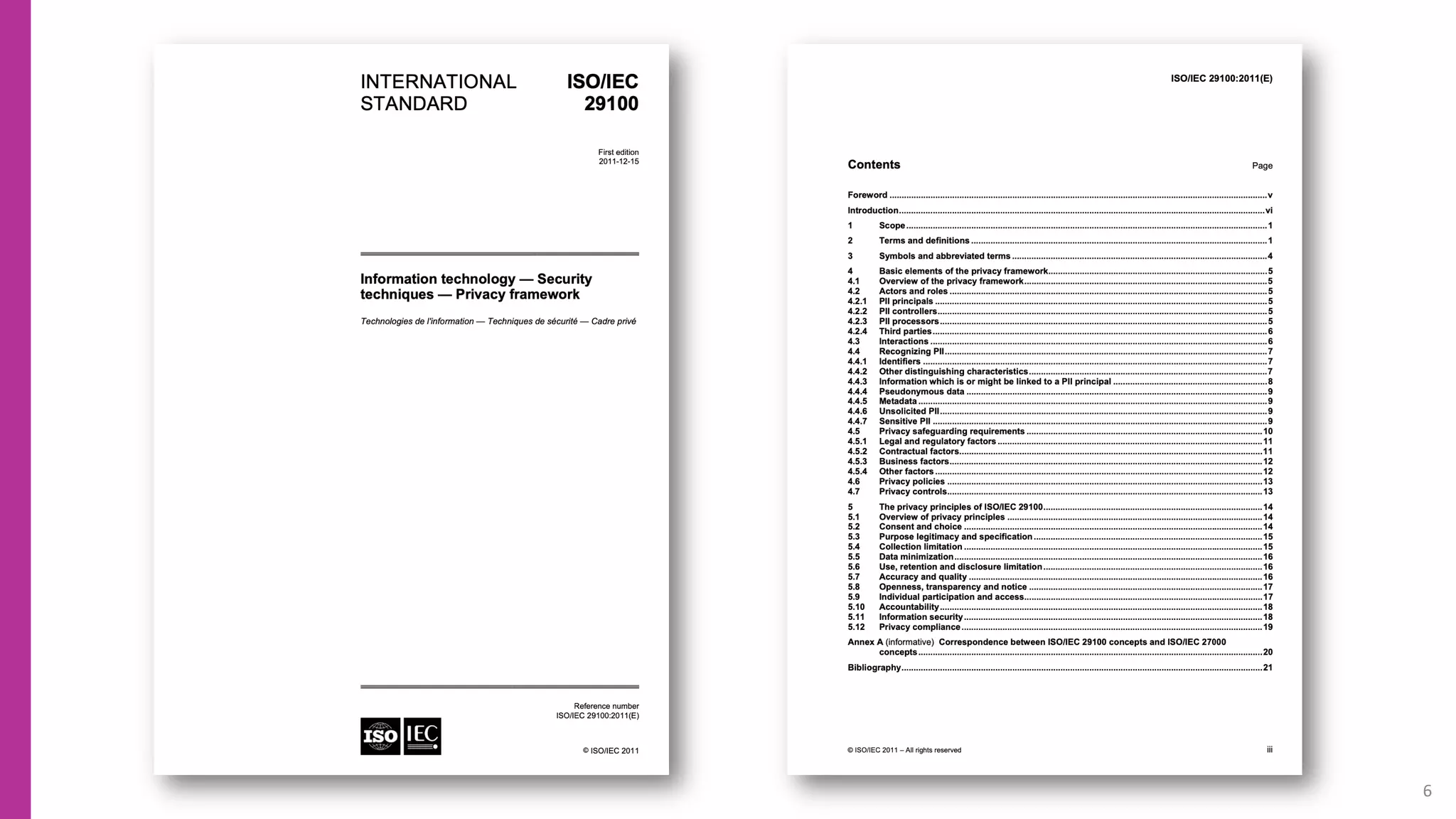
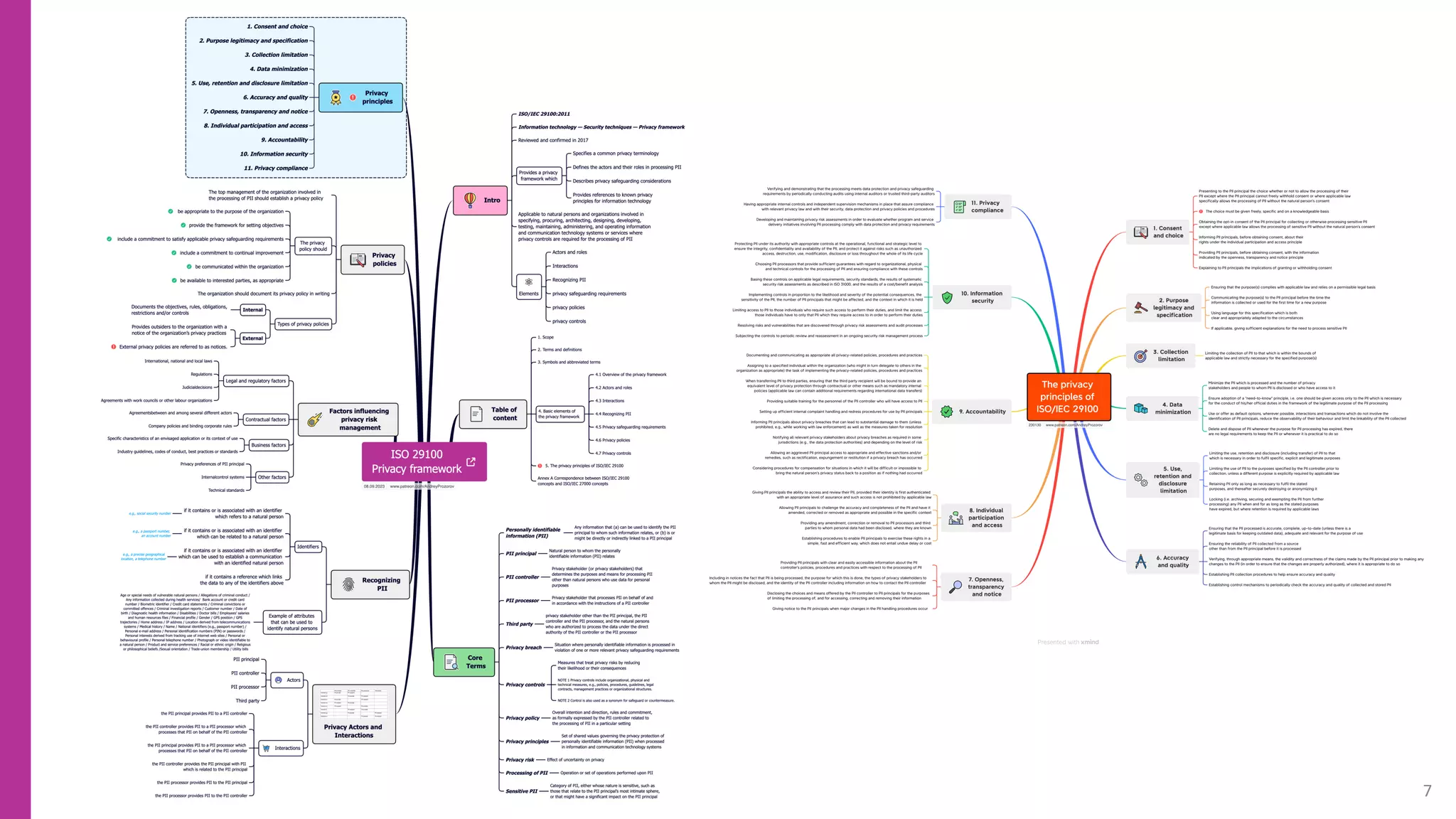
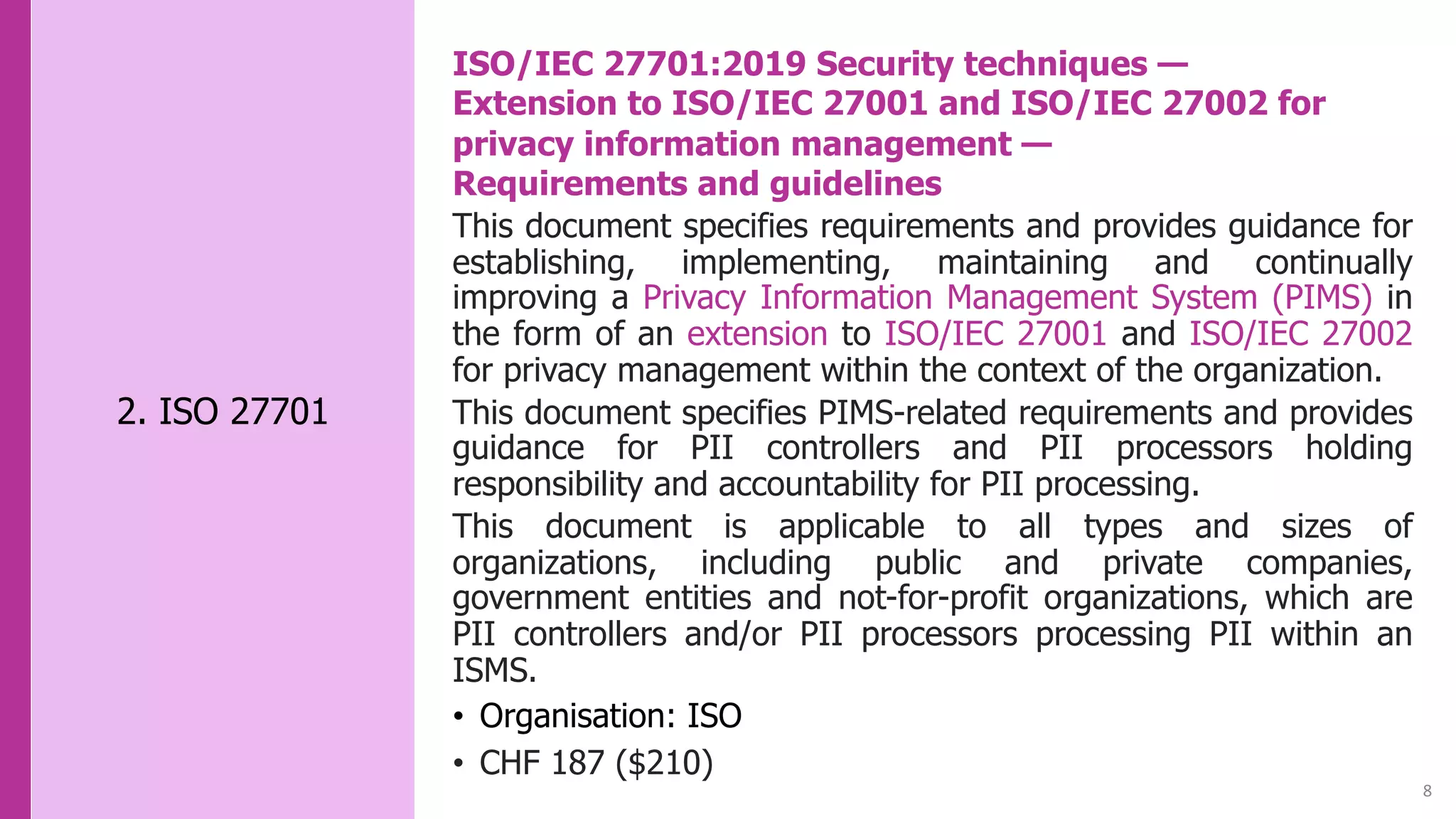
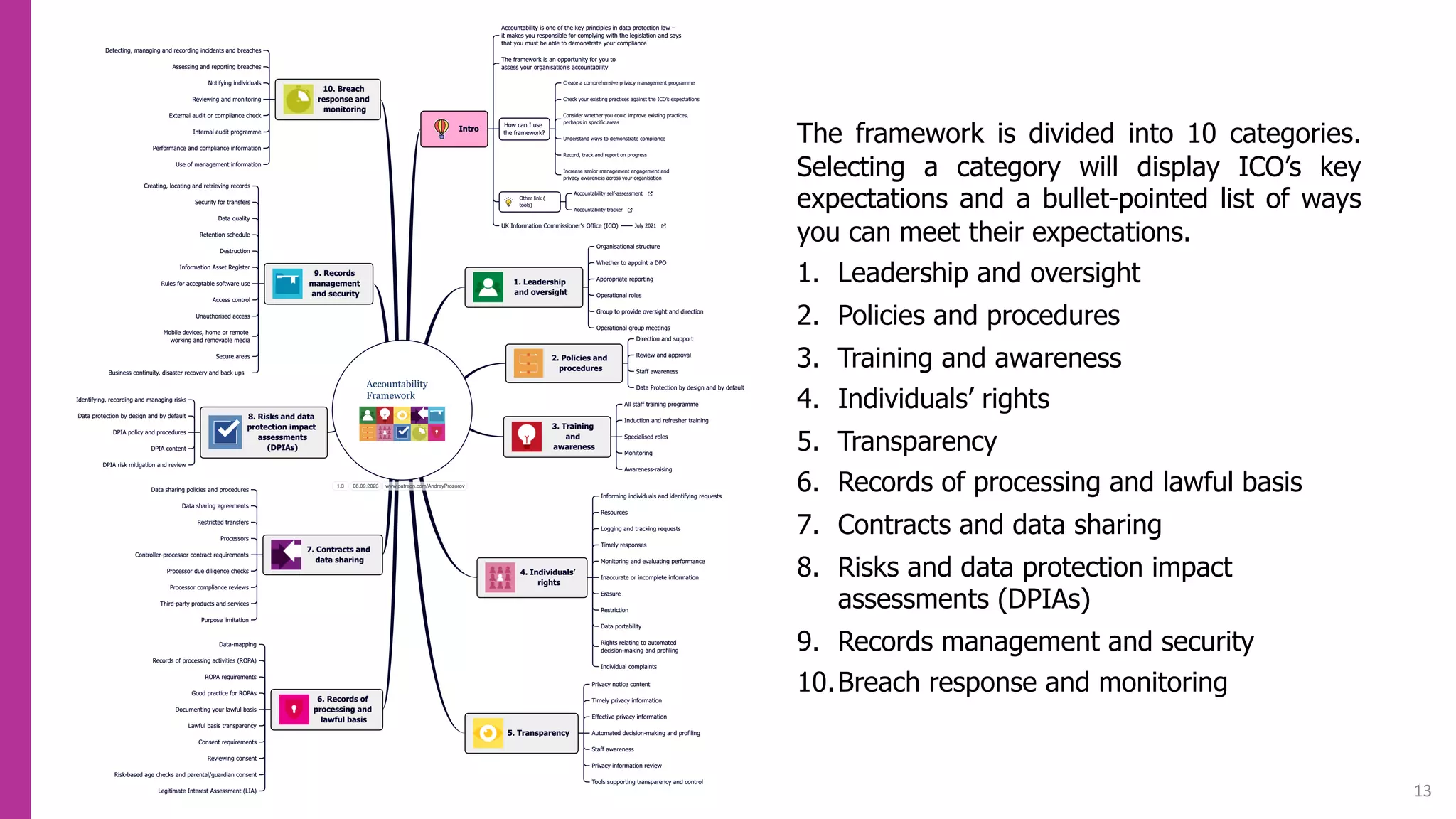
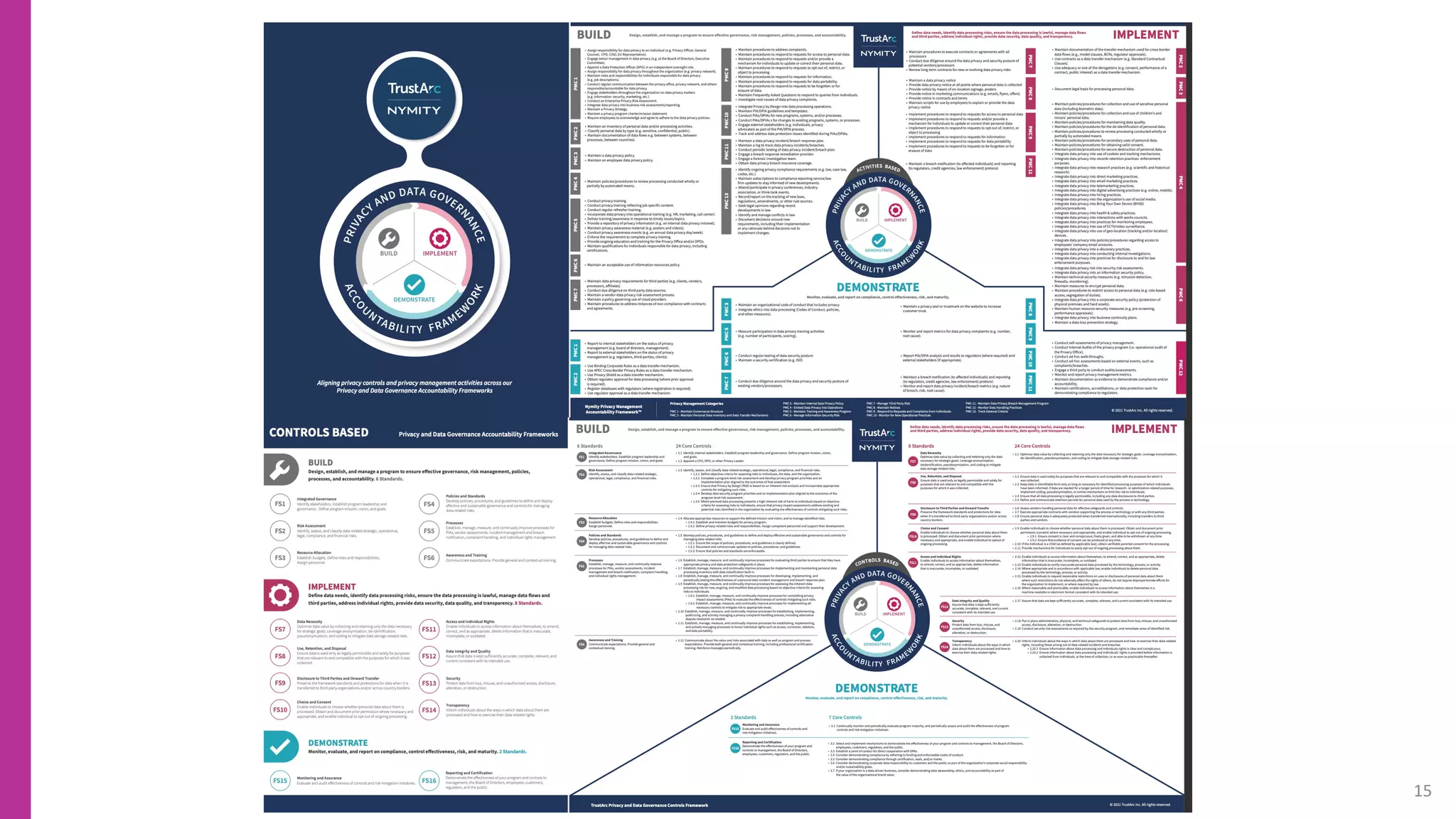
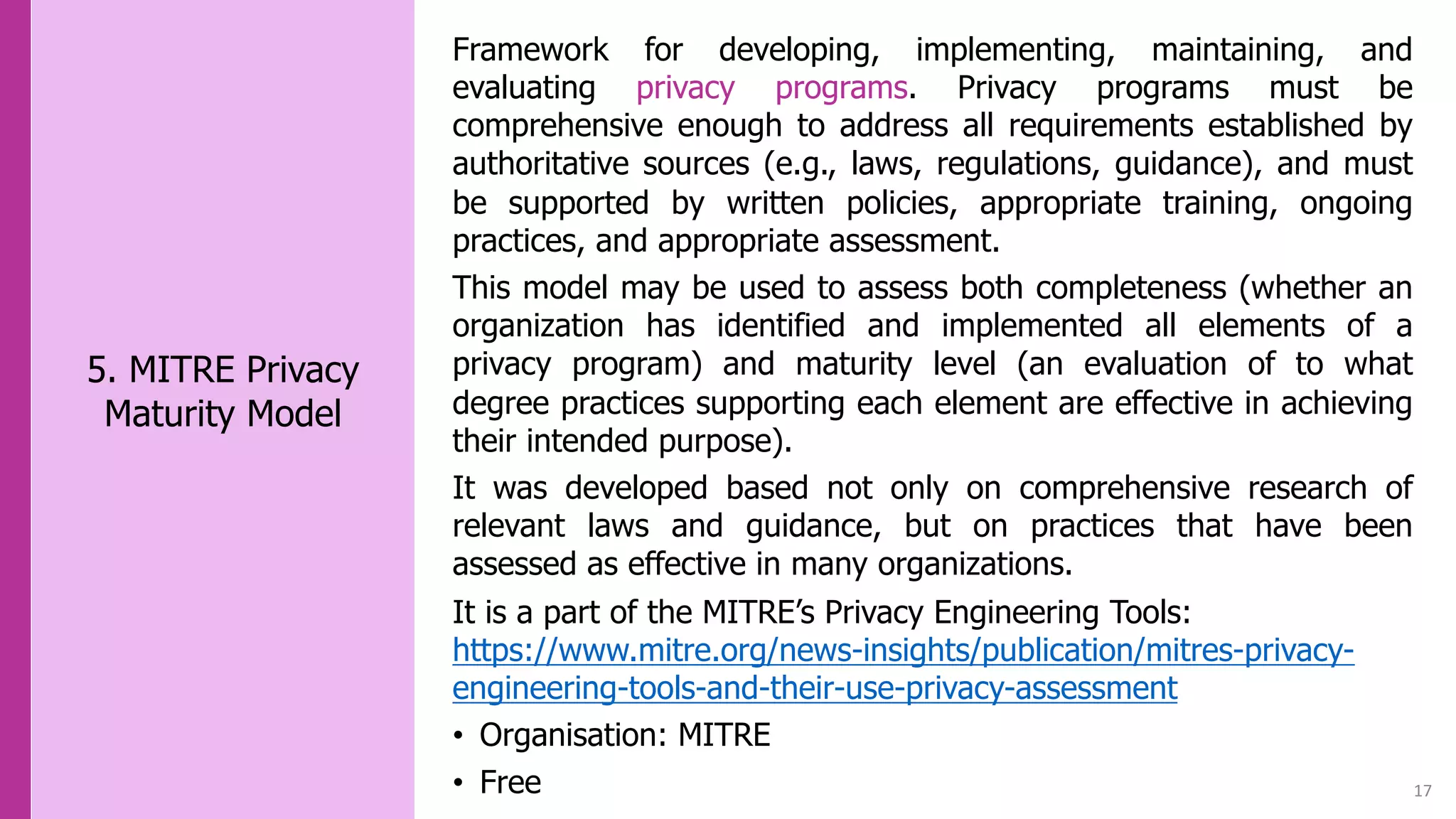
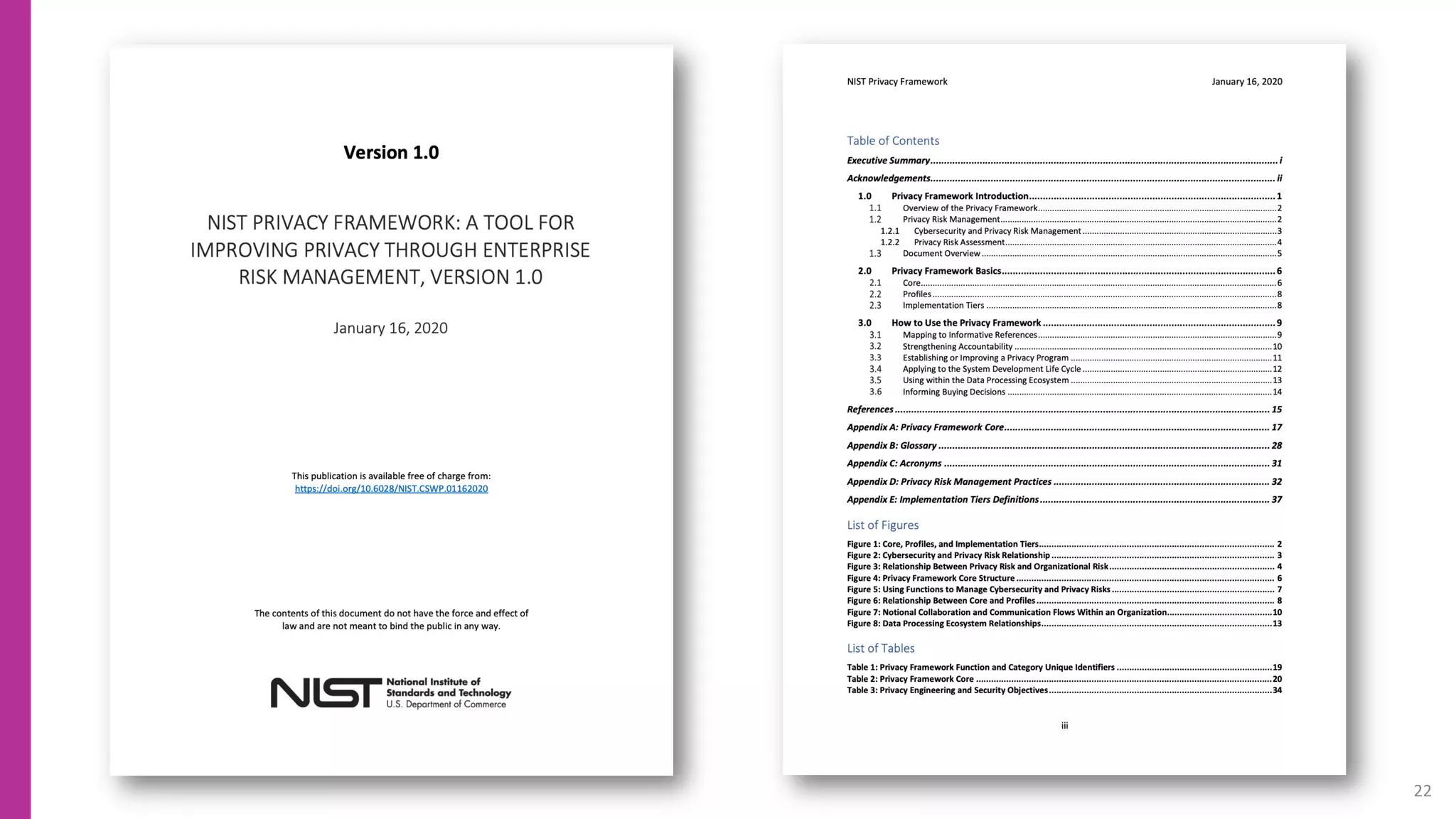
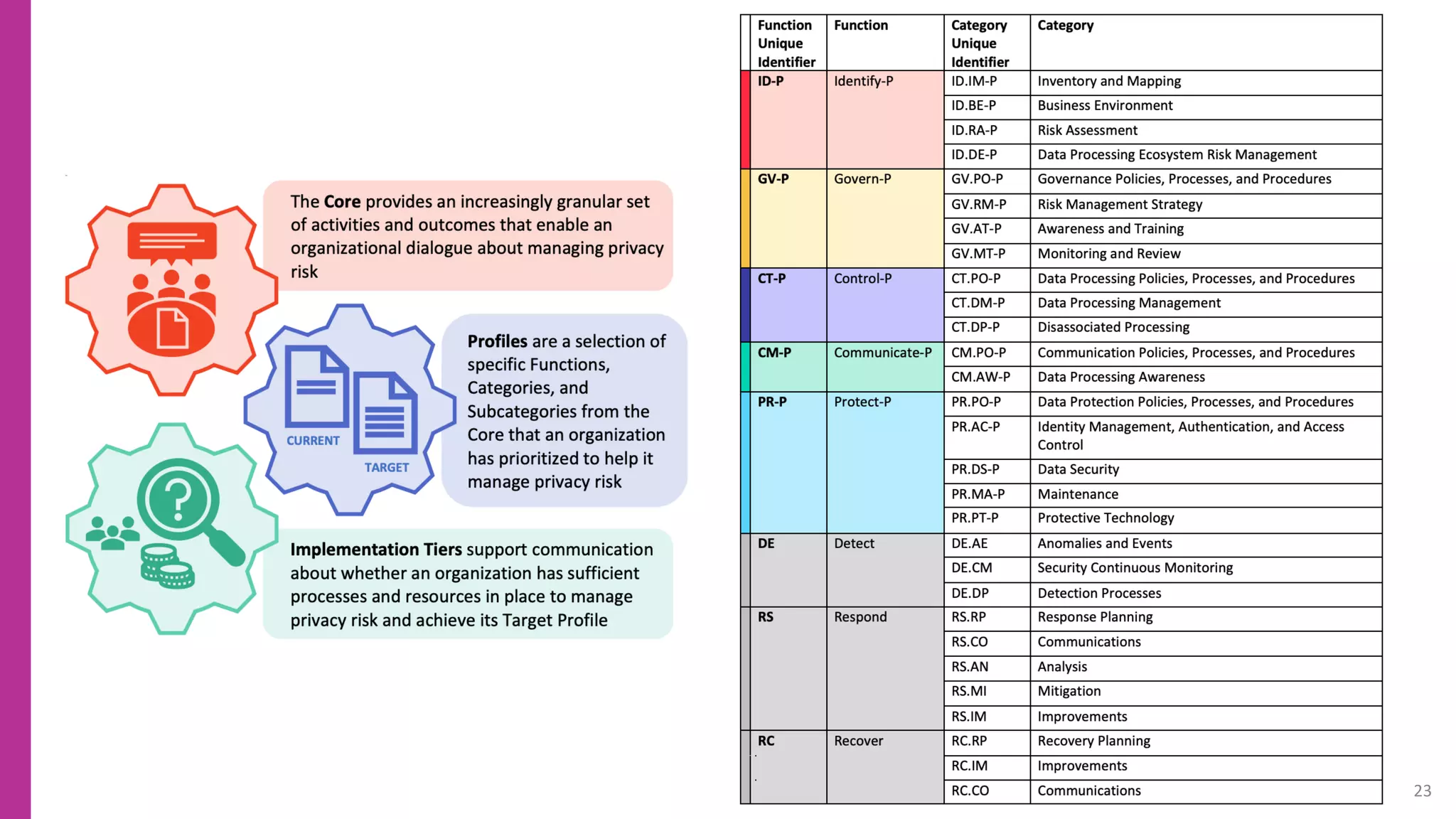
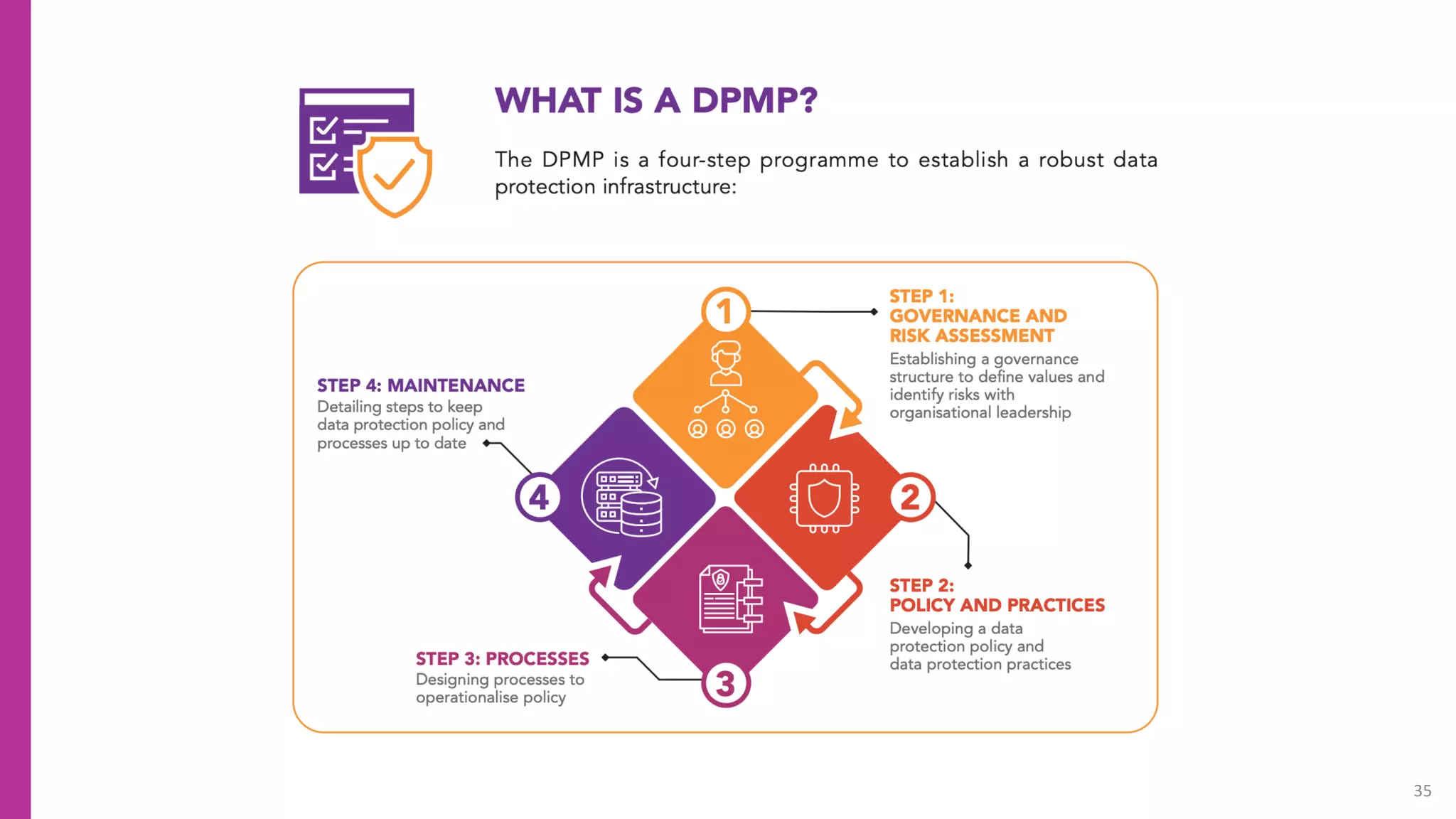
The document provides an overview of 12 privacy frameworks that can be used to develop comprehensive privacy programs. It describes each framework, including its organization, cost, and key benefits. The top frameworks are ISO 29100, ISO 27701, the ICO Accountability Framework, and the TrustArc-Nymity Framework. They provide standards, guidelines and best practices for building privacy into products and governance. The document aims to help privacy professionals select the most appropriate framework for their needs without needing to reinvent existing approaches.
























![44
[Concept] Mapping - An indication that one
concept is related to another concept. NIST](https://image.slidesharecdn.com/prprivacyframeworks230908-230910194707-ea5cc149/75/12-Best-Privacy-Frameworks-44-2048.jpg)