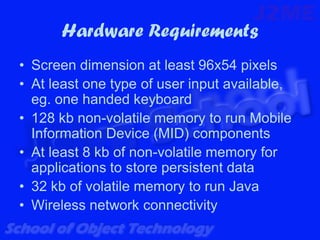
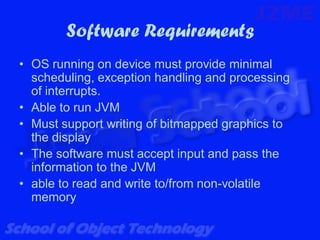
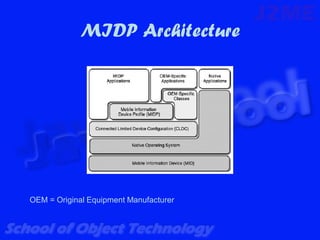
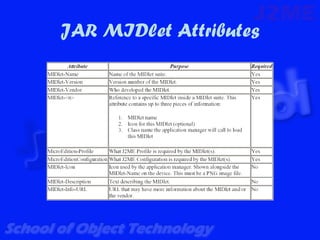
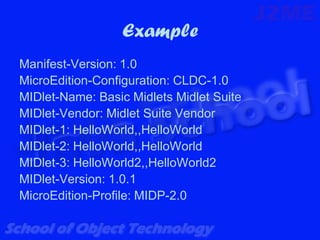
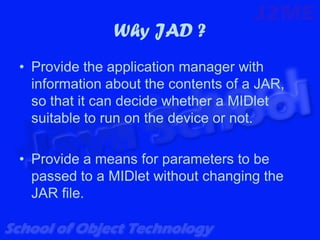
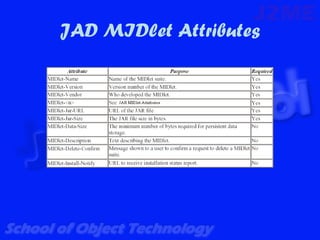
This document describes the hardware, software, and architecture requirements for a mobile information device (MID). It specifies the minimum hardware requirements including screen size, memory, and connectivity. It also outlines the necessary software requirements such as an OS, JVM, and ability to run Java MIDlets. The architecture uses MIDP on top of CLDC. MIDlets are packaged in JAR files and described using a JAD file. The JAR and JAD files contain metadata to identify and deploy the MIDlets.