computer forensics, involves the preservation, identification, extraction, and documentation of computer evidence stored as data or magnetically encoded information
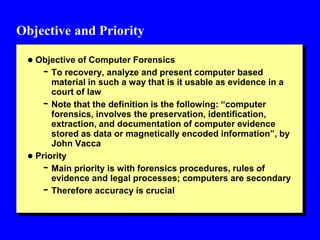
- 1. Objective and Priority Objective of Computer Forensics - To recovery, analyze and present computer based material in such a way that is it usable as evidence in a court of law - Note that the definition is the following: “computer forensics, involves the preservation, identification, extraction, and documentation of computer evidence stored as data or magnetically encoded information”, by John Vacca Priority - Main priority is with forensics procedures, rules of evidence and legal processes; computers are secondary - Therefore accuracy is crucial
- 2. Accuracy vs Speed Tradeoffs between accuracy and speed - E.g., Taking 4 courses in a semester vs. 2 courses; more likely to get Bs and not As - Writing a report in a hurry means likely less accurate Accuracy: Integrity and Security of the evidence is crucial - No shortcuts, need to maintain high standards Speed may have to be sacrificed for accuracy. - But try to do it as fast as you can provided you do not compromise accuracy
- 3. The Job of a Forensics Specialist Determine the systems from which evidence is collected Protect the systems from which evidence is collected Discover the files and recover the data Get the data ready for analysis Carry out an analysis of the data Produce a report Provide expert consultation and/or testimony?
- 4. Applications: Law Enforcement Important for the evidence to be handled by a forensic expert; else it may get tainted Need to choose an expert carefully - What is his/her previous experience? Has he/she worked on prior cases? Has he/she testified in court? What is his/her training? Is he CISSP certified? Forensic expert will be scrutinized/cross examined by the defense lawyers Defense lawyers may have their own possibly highly paid experts?
- 5. Applications: Human Resources To help the employer - What web sites visited? - What files downloaded - Have attempts been made to conceal the evidence or fabricate the evidence - Emails sent/received To help the employee - Emails sent by employer – harassment - Notes on discrimination - Deleted files by employer
- 6. Applications: Other Supporting criminals - Gangs using computer forensics to find out about members and subsequently determine their whereabouts Support rogue governments and terrorists - Terrorists using computer forensics to find out about what we (the good guys) are doing We and the law enforcement have to be one step ahead of the bad guys Understand the mind of the criminal
- 7. Services Data Services - Seizure, Duplication and preservation, recovery Document and Media - Document searched, Media conversion Expert witness Service options Other services
- 8. Data Services Data Seizure - The expert should assist the law enforcement official in collecting the data. - Need to identify the disks that contain the data Data Duplication and Preservation - Data absolutely cannot be contaminated - Copy of the data has to be made and need to work with the copy and keep the original in a safe place Data Recovery - Once the device is seized (either local or remote) need to use appropriate tools to recover the data
- 9. Data Services: Finding Hidden Data When files are deleted, usually they can be recovered The files are marked as deleted, but they are still residing in the disk until they are overwritten Files may also be hidden in different parts of the disk The challenge is to piece the different part of the file together to recover the original file There is research on using statistical methods for file recovery http://www.cramsession.com/articles/files/finding-hidden- data---how-9172003-1401.asp http://www.devtarget.org/downloads/ca616-seufert- wolfgarten-assignment2.pdf
- 10. Document and Media Services Document Searches - Efficient search of numerous documents - Check for keywords and correlations Media Conversion - Legacy devices may contain unreadable data. This data ahs to be converted using appropriate conversion tools - Should be placed in appropriate storage for analysis
- 11. Expert Witness Services Expert should explain computer terms and complicated processes in an easy to understand manner to law enforcement, lawyers, judges and jury - Computer technologists and lawyers speak different languages Expertise - Computer knowledge and expertise in computer systems, storage - Knowledge on interacting with lawyers, criminology - Domain knowledge such as embezzlement, child exploitation Should the expert witness and the forencis specialist be one and the same?
- 12. Service Options Should provide various types of services - Standard, Emergency, Priority, Weekend After hours services Onsite/Offsite services Cost and risks – major consideration Example: Computer Forensics Services Corporation - http://www.computer-forensic.com/ - As stated in the above web site, this company provides “expert, court approved, High Tech Investigations, litigation support and IT Consulting.” They also "Preserve, identify, extract, document and interpret computer data. It is often more of an art than a science, but as in any discipline, computer forensic specialists follow clear, well-defined methodologies and procedures.”
- 13. Other Services Computer forensics data analysis for criminal and civil investigations/litigations Analysis of company computers to determine employee activity - If he/she conducting his own business and/or downloading pornography - Surveillance for suspicious event detection Produce timely reports
- 14. Benefits of using Professional services Protecting the evidence - Should prevent from damage and corruption Secure the evidence - Store in a secure place, also use encryption technologies such as public/private keys Ensure that the evidence is not harmed by virus Document clearly who handled the data and when - auditing Cleint/Attoney privilege Freeze the scene of the crime – do not contaminate or change
- 15. Using the Evidence: Criminal and Civil Proceedings Criminal prosecutors Civil litigation attorneys – harassment, discrimination, embezzlement, divorce Insurance companies Computer forensics specialists to help corporations and lawyers Law enforcement officials Individuals to sue a company Also defense attorneys, and “the bad guys”
- 16. Issues and Problems that could occur Computer Evidence MUST be - Authentic: not tampered with - Accurate: have high integrity - Complete: no missing points - Convincing: no holes - Conform: rules and regulations - Handle change: data may be volatile and time sensitive - Handle technology changes: tapes to disks; MAC to PC - Human readable: Binary to words
- 17. Legal tests Countries with a common law tradition - UK, US, Possibly Canada, Australia, New Zealand Real evidence - Comes from an inanimate object and can be examined by the court Testimonial evidence - Live witness when cross examined Hearsay - Wiki entry “Hearsay in English law and Hearsay in United States law, a legal principle concerning the admission of evidence through repetition of out-of-court statements” Are the following admissible in court? - Data mining results, emails, printed documents
- 18. Traditional Forensics vs Computer Forensics Traditional Forensics - Materials tested and testing methods usually do not change rapidly - Blood, DNA, Drug, Explosive, Fabric Computer Forensics - Material tested and testing methods may change rapidly - We did not have web logs in back in 1990 - We did not have RAID storage in 1980
- 19. Types of Acquisition Static Acquisition - Acquire data from the original media - The data in the original media will not change Live Acquisition - Acquire data while the system is running - A second live acquisition will not be the same Will focus on static acquisition
- 20. Digital Evidence Storage Formats Raw formats - Bit by bit copying of the data from the disk - Many tools could be used Proprietary formats - Vendors have special formats Standards - XML based formats for digital evidence - Digital Evidence Markup Language (Funded by National Institute of Justice) - Experts have argued that technologies that allow disparate law enforcement jurisdictions to share crime-related information will greatly facilitate fighting crime. One of these technologies is the Global Justice XML Data Model (GJXDM). - http://ncfs.ucf.edu/digital_evd.html
- 21. Acquisition Methods Disk to Image File Disk to Disk Logical acquisition - Acquire only certain files if the disk is too large Sparse acquisition - Similar to logical acquisition but also collects fragments of unallocated (i.e. deleted) data
- 22. Compression Methods Compression methods are used for very large data storage - E.g., Terabytes/Petabytes storage Lossy vs Lossless compression - Lossless data compression is a class of data compression algorithms that allows the exact original data to be reconstructed from the compressed data. The term lossless is in contrast to lossy data compression, which only allows an approximation of the original data to be reconstructed, in exchange for better compression rates.
- 23. Contingency Planning Failure occurs during acquisition - Recovery methods Make multiple copies - At least 2 copies Encryption decryption techniques so that the evidence is not corrupted