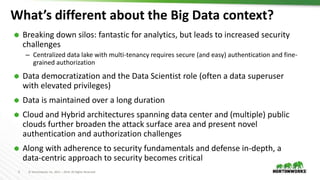
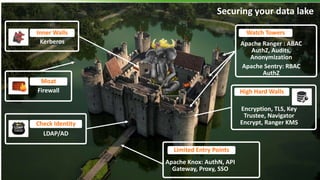
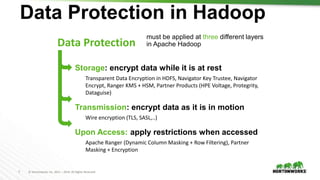
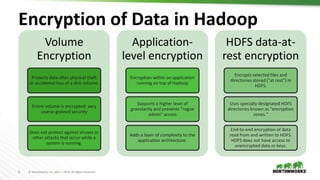
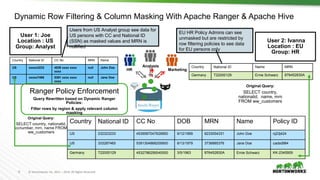
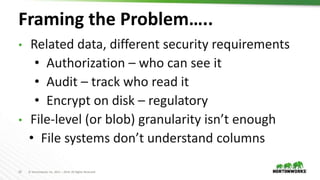
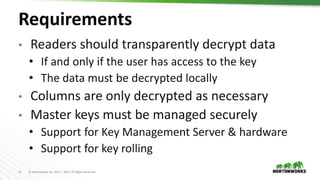
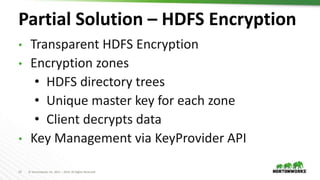
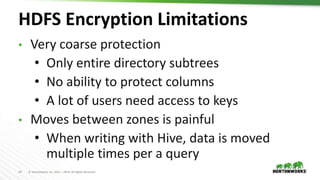
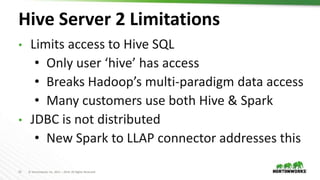
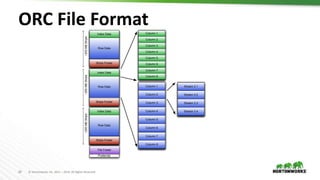
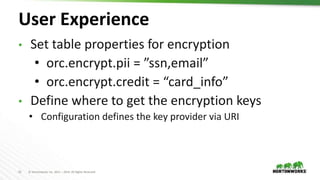
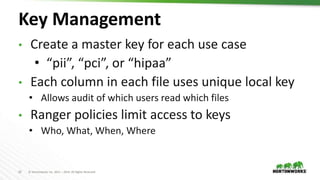
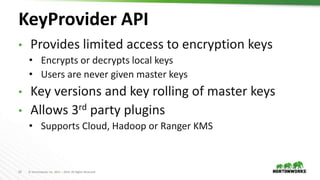
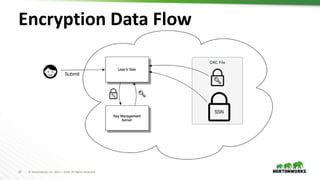
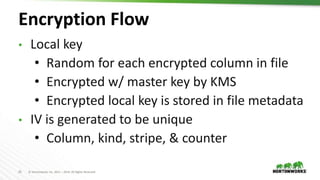
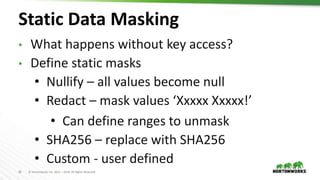
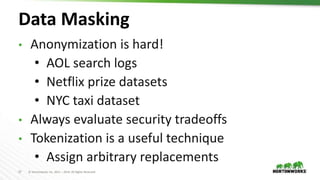
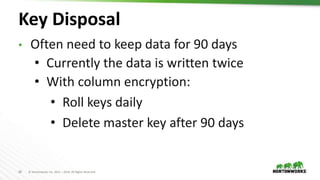
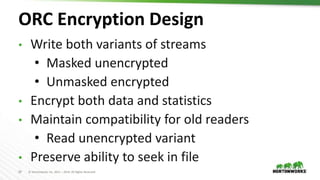
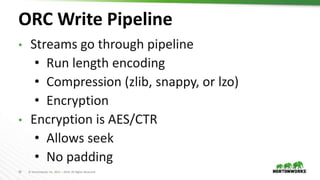
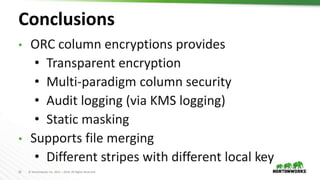
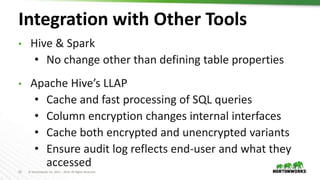
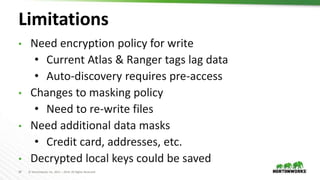
The document discusses fine-grained access control for big data focusing on ORC column encryption, highlighting the importance of data security in Hadoop environments. It addresses challenges related to data democratization, complex multi-cloud architectures, and the necessity for strong authentication and authorization mechanisms. Additionally, it outlines the architecture of columnar encryption, integration with tools like Hive and Spark, and the management of encryption keys while providing transparency and auditing capabilities.