Running head THE NETWORK INFASTRUCTURE OF JETS INC1THE NETWORK.docx
- 1. Running head: THE NETWORK INFASTRUCTURE OF JETS INC 1 THE NETWORK INFASTRUCTURE OF JETS INC 13 The Network Infrastructure of Jets Inc. Name: sunil patel Institution Affiliation:Iglobal university MIT 681 : MSIT capston final project Executive Summary According to estimates, there will be ten billion devices in the next half a decade, which is equivalent to 1.5 for every human being. As mobile devices increasingly become integrated with all sectors of our personal lives, companies realize that employees progressively want to utilize their own mobile devices along with company-issued devices to perform work- related roles; many employees are urging the IT department to facilitate this. Companies have come to the conclusion that it is impossible to stop the utilization of mobile device for both work and private purposes, but they need to have the framework to regulate it. In the present economic climate, firms require employees that are highly efficient; having a secure mobile framework that permits personal devices to be utilized safely to perform work roles can increase worker productivity and be a substantial competitive edge. It can even facilitate a higher
- 2. acceptance rate in the process of recruitment. On that account, the following study will examine the network infrastructure of data analytic firm Jest Inc. In particular, will evaluate the systems and factors that will enable the project to be a success The Network Infrastructure of Jets Inc. Jets Inc. is a data analytics firm that helps manufacturing companies to improve companies improve the process to gain better efficiency. A key part of Jets’ operations is its network infrastructure. The infrastructure consists of cloud computing, big data systems, and the accompanying information security and DR protocols. To that end, it is important that Jets’ invests in suitable and efficient network infrastructure to enable it to offer optimal services to its clients. The following paper will illustrate the network infrastructure of Jets Inc. It will begin by exploring its cloud computing services, followed by the information security and DR security, and then the big data and data warehouse. CLOUD SERVICES Since Jets Inc’s data analytic services are tailored for manufacturing firms, the company will opt for a Cloud ERP System from Microsoft. Some of the advantages that the cloud- based ERP solution provides to companies include lower cost as the deployment of the ERP will need very few hardware investments and the traditional internal system maintenance won’t be required during an occasional upgrade. In the cloud, computing time is saved as organizations won't physically be
- 3. required internal computing resources as the services will be virtually outsourced to third parties via the web who have advanced technological IT hosting resources. Cloud computing will enhance mobility as the organization can access ERP cloud applications anywhere through web browsers using other handheld mobile devices such as tablets, laptops smartphones without necessarily having to use traditional PCs. Key strategies for successful Cloud-Based ERP adoption The top management should entirely support the implementation of Cloud-based ERP for its adoption and upgrade to be successful. The organization should also use other IS applications in case of larger organizations specific functions and not entirely rely on cloud computing in cross-functional cooperation. For data security, the companies implementing Cloud ERP should be very careful when selecting the cloud ERP service providers and the signing of contracts and other legal entities should be strictly taken care of. Cloud-based ERP provides a set of new features to helps organizations to solve technical barriers that result from the traditional in-house ERP implementation. The time and the cost that organizations incur during the in-house ERP system upgrade is hugely reduced with the advent of cloud ERP. A location restriction for ERP user is a factor that makes it impossible for the organization to access the system whenever they are outside the boundaries of the organization premises. The cloud ERP computation provides solutions that do not make it necessary for users to be within the physical environment of the ERP machinery but can simply access it virtually through the web. For a company that is very big with several international branches, the adoption of Cloud computing makes it simple to upgrade the system without the difficulty of physically accessing the companies’ PCs in every branch. The communication via the web is such efficient that cloud computing services provider will just have to primarily upgrade the system at the headquarters and integrate the same features to all branches virtually.
- 4. Effect of Cloud ERP on Performance The use of cloud ERP system considerably increases the speed in which data is processed. The cloud system provides organizations with an effective way of upgrading their systems as it’s virtually done. Considerably reduction in the cost of implementing ERP as human resources, time and investments to manage it is reduced. The ERP mobility is highly enhanced as users can actually access ERP services using mobile technologies such as smartphones, tablets or laptops. Jets Inc. Cloud Policy for Users Jets will grant its workers the joy of using tablets and smartphones that they prefer at the workplace for the convenience. It maintains the right to remove the program if users do not follow the procedures and policies that are stated in the next section. Regulations are meant to guard the integrity and security of the Jets’ technological infrastructure and data. Restricted allowances to the regulation may happen because of the differences in platforms and devices. The employees must consent to the rules and guidelines established in the regulation to be facilitated with access to the company’s network through their mobile devices... Suitable Usage · Jets’ describes the suitable application as actions that directly or indirectly reinforce its operations. · Jets’ describes suitable usage of personal devices on work hours as rational and restricted individual interaction or relaxing, such as playing a game or reading. · Certain sites are restricted from employee access on company time or while linked to the firm’s infrastructure with the knowledge of the enterprise. These sites include limited to social media sites, video sharing sites, entertainment blogs, and pornographic sites. · The camera of devices and video capabilities should be disabled when one is the company’s premises. · At no time, should devices be used to store or distribute explicit materials, store or distribute proprietary data that
- 5. belongs to another firm, harassment, engage in activities that are not related to Jets’, among others? · Social media sites are only allowed when engaging in company business. · Applications that are not downloaded through Windows Store, Google Play, or iTunes are not allowed. · Personal mobile devices have access to some resources belonging to the frim like documents, emails, calendars, and contacts, among others. · Jets’ apply a zero-tolerance for emailing or texting by a driver. Hands-free communication is allowed. Gadgets and Support · Various platforms including Windows phones, iPhones, Blackberry, and Android are permitted. The IT department usually releases a list of the required operating system versions and models. · Tablets such as Android and iPad are permitted. The IT department releases a list of the required operating system versions and models. · The IT department supports issues regarding connectivity: workers should contact the manufacturer of the device or network carrier in the case that IT fails to address the issue. · Devices must be introduced to the IT department for comprehensive provisioning of job and installation of conventional software like office efficiency programs, web browsers, and safety application prior to being handed permission to the network. Reimbursement · Jets’ does not compensate workers for the part of the total cost of the mobile gadget. Instead, the company facilitates workers with an allowance that will cover the data plan. · The company does not compensate employees for the following charges; plan overcharges, roaming, among others. Security · To restrict unsanctioned entree, gadgets must feature PIN
- 6. protection using the inbuilt applications of the gadget and a secure password is needed to facilitate admission to the firm’s network. · Jets’ robust password guideline is: Passwords should have an of a minimum of eight letterings and a mix of lower and upper- case letters, symbols, and numbers. Passwords are changed after three months, and the novel password cannot be any of the user passwords. · The gadget should lock itself with a PIN or password if it stays unused for three minutes. · In the event of failed attempts to log in, the device will self- lock. Employees usually contact IT to gain back access to the network. · JailbrokeniOS devices or rooted Android devices are strictly restricted from gaining access to the firm’s infrastructure. · Workers are restricted from downloading, configuring, and utilizing any program that that is not approved by the firm. · Tablets and smartphones that are on the list of devices that are supported by the company are not permitted to connect to the network. · Tablets and smartphones that are owned by employees for the sole reason of personal use are not permitted access to the network. · Access to company data by employees is restricted on the basis of user-profiles described by the It department, and are enforced automatically. · The device of an employee may be wiped remotely if 1) the device gets lost 2) the employment of a worker is terminated 3) IT department detects a breach of policy or data, a virus or a similar type of security risk to the company’s technological infrastructure and data. Risk/Liabilities/Disclaimers · Whereas the IT department takes a comprehensive precaution to prevent the loss of employee’s personal data if a remote wipe must be performed, it is the duty of a worker to use extra defenses like storing contacts and email.
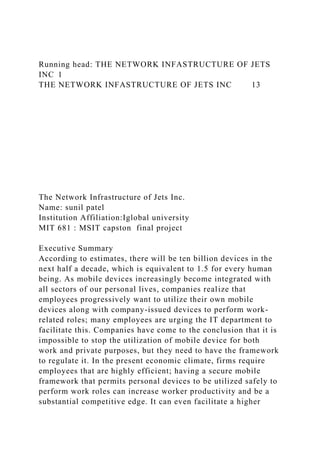
- 7. · The company maintains the right to disable services or disconnect devices without prior notice. · Stolen or lost devices must be stated to the IT department within 24 hours. It is the responsibility of employees to notify their mobile carries once a device is lost. · The employee is anticipated to use his/her device in a manner that is ethical at all times and comply with the user policy that is accepted by the company as illustrated above. · It is a personal liability of employees for all costs that are related to his/her gadget. · Workers should take entire responsibility for risks like complete or partial damage of personal and company data as a result of bugs, failure of the operating system, malware, viruses, and other failures related to the software or hardware, or errors related to programming that make the device to become unusable. · Jets’ maintains the right to take the necessary disciplinary steps including termination of employment for failure to comply with this policy. Network Diagram Image 1: The Design of Jets’ Network
- 8. SECURITY AND DR Governance of Privacy Enhancing legislation concerning privacy is an occurrence that will be more profound in the near future. As Jets’ designs security controls for BYOD, these may affect with individual anticipation of privacy. To address this issue, the company uses the BYOD policy to address privacy concerns. The BYOD policy is well-formed and includes clear and defined expectations on procedures that impact privacy. In some geographical regions, the company is forced to facilitate employees with an alternative to BYOD thus potentially reducing the savings that are to be realized by the entire program. For example, in Europe, it is more common for the employer to facilitate the hardware that enables work to be performed, induced mainly by the inability to force workers to have their own smartphones (French, Aaron, Chengqi, & Shim, 2013). Consequently, this may either bring about a BYOD program that is hybrid, that is, where there are both organization-owned and private programs and devices that are inclusive of provisions for the purchase of these devices. On the other hand, US regulations hand companies the right to observe and wipe the device of a user (French, Aaron, Chengqi, &Shim, 2013). It is key that the company examines the risk that surrounds this practice, creates a policy and communicates to users about the implications of privacy of using their personal device. Protection of Data In the implementation of a BYOD program, protection of data is not only relevant to company data. Federal and state regulations that guide the dispensation of personal information in a BYOD setting apply, and if the firm is gathering personal information from the device of an employer, security, expiration, the purpose, among others, of the accumulated data must be clearly defined in the BYOD policy (Zhang, Kunjithapatha.,Jeong, & Gibbs, 2011). Jets will perform an assessment of the risks that
- 9. are related to the dispensation. If a third party is used to process data, that is, if the firm uses a provider of cloud service, it is crucial that that data is protected through an agreement of data processing with the third party (Thomson, 2012). With the transfer of data, the duty of protecting the data should be shifted and the compliance should be verified. The Right to Erasure and Be Forgotten It is gradually more widespread for regulation involving privacy to include provisions for the right to be forgotten for the employees, and to have an individual’s personal data deleted when he/she leaves the company (Hunt, 2012). Therefore, since Jetsoperates in regions where such regulations are in place, it assesses the effect to the company and develops support procedures that are formalized to handle these requests. The company takes advantage of these processes to include employees that are enrolled in BYOD. Monitoring Privacy at the Work Place There is a broad range of requirements and laws centered on monitoring, data protection, and wiping. For example, privacy regulations in the EU state that surveillance should be restricted to the use of the device at the workplace only. Company-wide and worldwide monitoring may also be limited, as EU limits transfer of data to countries that are not-EAA (French, Aaron, Chengqi, &Shim, 2013). Labor laws depend on the state and limit the company for monitoring the personal information of employees. This may restrict the firm’s ability to control and monitor sent to mobile devices for the purpose of security. These needs are complicated further when, for example, an employee gives a child the device to play a game. To avoid these pitfalls involving measures that monitor privacy, Jets’ uses a product that enables the monitoring ability to occur entirely around activities that are work-related. Breach Investigation and Report Due to breaches, digital investigations on personal devices may seem like an invasion of privacy. As such, it is important for the company to reserve the right to analyze the devices of
- 10. employees when in the event of such an incidence (Gatewood, 2012). If such a right is not reserved on the BYOD policy that is agreed upon, the company may encounter legal difficulties and delays when examination of information on personal devices is required. The present trend for future and novel laws are starting to address notification of data breaches, with exclusions around notice if certain criteria surrounding data protection are met (Thomson, 2012). The company prepares for these statutes by keeping a dynamic record of the devices, the data that they possess, and the security measures used to protect the information. Encryption Systems Bit locker and The Kerberos authentication system Bit locker is a program created by Microsoft to enhance the security of its operating systems. The software is easy-to- use and can encrypt an entire hard drive and can assist to defend an O.S against malware. BitLocker is available to any user who has Windows Vista and above. The Kerberos authentication system is developed above tickets or credentials. The main idea underlying the system is that one does not submit his/her password for each service that he/she requires. Instead, one keeps tracks of his/her tickets on the local system and only displays each service a ticket particularly for that service and cannot be applied for anything else (Araki, Barak, Furukawa, Lindell, Nof, &Ohara, 2016). When one begins to use his/her system, he she uses a password to acquire a master ticket termed as the ticket-granting ticket (TGT); regardless whether one is using Kerberos for Windows, Linux, or Macintosh. The ticket master has a validity of 25 hours and should be renewed with the password after this period (Araki et al, 2016). Whenever one goes through a service that applies Kerberos, he/she displays the ticket master to the service’s server and acquires a custom ticket for that service. After this step, one displays the ticket for that particular service to the service to confirm his/her identity. The tickets are preserved in a ticket cache in one’s local system.
- 11. The conventional password is similar to one’s birth certificate, national identification card or passport since it proves his/her identity. It is not well reinforced against forgery, its bothersome to type, and has all the data required to acquire one’s identity (Araki et al, 2016). Indeed, one does not want to display such documents whenever they want to get an official document from the government. On that account, the Kerberos TGT is like one’s national I.D. It is a powerful means of identification but workers more effectively with anti-forgery reinforcement. One can use the identification to prove his/her identity and acquire secondary identities for particular situations (Araki et al, 2016). In other words, the Kerberos service tickets are similar to other single-purpose identifiers like match tickets. The apparent benefit of this system is that a service receives a custom ticket. One does not need to submit his/her I.D, thus, the service does not have the opportunity to acquire one’s I.D and apply it for personification (Khurana, Saggar, &Kaur, 2016). If applied for its original purpose, Kerberos is a multifaced protection tool. It protects a user’s personal files and defends against a person personating an email server to acquire an identity to use somewhere else. Unfortunately, there are some clients and services that do not have direct support for Kerberos. For instance, several mail clients do not comprehend Kerberos and can only interpret passwords. When utilizing such clients or services, one may have to insert their password, so that it is relayed to the server. The server utilizes the password to acquire the master ticket for a user and validate that the master ticket is the right one (Khurana, Saggar, &Kaur, 2016). Even though this method is applicable, it is not convenient. It is like a person handing over his/her social security number and birth certificate to each service that he/she wants to use, instead of simply displaying a ticket customized for that service. Even though most services can be trusted, such a method creates additional risk. In that regard, one should try to reduce the number of services that need password and attempt to utilize actual Kerberos tickets in
- 12. every situation possible. Additionally, a user should validate every application that requests a password. Nonetheless, requesting a password is not the most effective or safe way to utilize Kerberos. The ideal situation is where one has to insert his/her password into his/her computer once a day. As such, one should seek for a software that is compatible with Kerberos to evade the hassle of typing the password each time and reinforce the security of the account. Overall, even though the Kerberos system has its vulnerabilities, it provides adequate security for one’s data. BIG DATA AND DATA CENTER The components that will make up Jet’s Big Data system include software, hardware, the connections and its users and storage place of the system. The most common types of Big Data systems include management information systems, operation support systems, Executive information systems, and decision support systems. Many manufacturing firms are currently seeking for ways of managing their big data while at the same time increasing their production efficiency using well- established information architecture. As such, the manufacturing firms have to collect information from various data sources to improve the outcome of the process. Doing this often improve both productive and analytical capabilities of a company. This section highlights the big data systems that Jets will use, benefits of big data, key business challenges, the issue associated with the handling of big data, and how to overcome these issues.
- 13. Jets’ Big Data Systems The big data systems that have been recommended for use in Jets’ operations include relational database management systems, and they are ideal for managing structured data. Other are MOLAP databases, NoSQL, distributed file system, and big table inspired databases. Benefits of Big Data to Jets Big data are quite beneficial to the Jets. They help in optimizing production and plant operations, thus, maximizing quality and productivity while at the same keeping costs to a minimum level. These systems are also helpful in minimizing threats in the supply such. Besides, they are useful tools for planning as well as support services that ensure good quality of the outcome (Marcus, 2013). Furthermore, they ensure improved forecasting of services, prevention of loss and revenue protection, and enhanced efficiency in IT operations. Challenges The key business challenges that these systems aim at addressing include quality of manufacturing and support services, customer experience and intimacy, and improvement of operational efficiency. Issues Associated with Handling of Big Data in Manufacturing Firms Generally, the issues that manufacturers face while handling big data include data variety, volume, value, and velocity. These have been discussed thoroughly in the paper. Overcoming these Issues To overcome these issues, it is prudent that the company should consider its current and existing gaps to achieve its future objectives. In this case, the company has to adjust its technology architecture to accommodate the change made. Further, the firm has to match the existing capabilities with appropriate tools (Marcus, 2013). The company should also consider security and data governance. Finally, for a project to be successful, the firm should use data models, reference
- 14. architecture, and simulations to improve reliability. Dimensions of Jets’ Big Data System Organizational Today, organizations are highly dependent on information systems to execute and keep track of their operations, interact with suppliers and clients and to give them a competitive edge in the market. Firms use Big Data for crucial operations such as finance and human resource and to get customer feedback while governments utilize it to provide timely and cheap services to citizens. People Human beings rely mostly on internet-based information systems to run their daily lives. From entertainment to shopping to socializing and even banking, individuals use information systems to run their personal lives Technology The technology dimension includes all software, hardware and telecommunication devices which are integrated to make up an information system. Data and Literacy Data is a term used to represent raw, random facts which are unclassified since they are not processed while information represents data that has already processed, i.e., it is classified and structured in a way that it has meaning and use to the specific user. Information system literacy entails possessing a framework for searching, understanding, evaluating and utilizing information technology in order to obtain relevant information through critical thinking and analysis (Lin, 2012). On the other hand, computer literacy refers to having fluency with various computer hardware and software. Best Practices for Jets’ Data Centers Measurement of PUE PUE stands for Power Usage Effectiveness; it is a measurement
- 15. of how efficiently a data center utilizes energy. It is the ratio of the overall amount of energy used by a data center to the amount delivered to IT equipment (Lin, 2012). The value of PUE that firms should strive for is 1.2 which means that the data center is running very efficiently. Through measurement of PUE, the energy that a data center uses can be tracked and thus improvements can be made. Measurements should be done regularly and over the entire year. Management of Airflow Sufficient airflow management is important if any data center is to be run effectively. The flow of cold and hot air should be controlled using various methods such as the use of blanket plates. Constant adjustment of the Thermostat Google recommends the use of an economizer so that the thermostat of devices can be adjusted to allow more “free cooling” intervals and thus save on energy. Utilization of Free Cooling Free cooling is a technique that removes heat from a data center without the use of an electronic chiller. It reduces the cost of chillers which are the biggest energy users in a data center. Power Distribution Optimization Optimization involves the reduction of steps involved in power conversion by using highly efficient models such as Power Distribution Units (PDUs). Factors that retard or accelerate the power consumption of a data center The following factors affect the power consumed by a data center: · Location- Energy costs are highly dependent on a location since different areas have diverse techniques of power generation and varying tax regimes · Design- Data centers that are designed to allow more of free cooling consume less power than those that utilize chillers. · Size- Generally, the bigger the data center and the more
- 16. equipment it has, the more power it consumes. · Maintenance- Constant maintenance of a data center is important if it is to consume power efficiently. · Power Density- It is an indication of how much IT equipment can be placed in individual racks. A data center with many racks will have less power density and thus consume less power. Overall, Big Data will be critical Jets. This is because they are capable of exposing certain problems associated with the company’s operations. Otherwise, big data is very helpful in improving processes to achieve sustainable growth. Conclusion The adoption of cloud computing will be intertwined with the use of big data systems. Cloud computing is a service that is transforming how organizations store and use their data. The technology will enable the access and utilization of numerous server-based computational resources through a digital network (WAN) or internet connection, which can be accessed using several devices. In cloud computing, the users do not install or download applications on their personal computer or device; rather it is a third-party service provider that handles all an organization’s data. Its usage at Jets will enable the adoption of autonomic and utility computing, service-oriented architecture, and virtualization. References Araki, T., Barak, A., Furukawa, J., Lindell, Y., Nof, A., &Ohara, K. (2016, October).High-Throughput Secure Three- Party Computation of Kerberos Ticket
- 17. Generation.In Proceedings of the 2016 ACM SIGSAC Conference on Computer and Communications Security (pp. 1841-1843).ACM. Caldwell, C., Zeltmann, S, and Griffin K. (2012). BYOD (Bring Your Own Device). Competitive Forum. French A.M., Guo, C and Shim J.P (2014). Current Status, Issues, and Future of Bring Your Own Device (Bring Your Own Device). Communications of the Associations of Information Systems.191-197. Gaff, B.M. (2015).BYOD?OMG.Computer.10-11. Gatewood B. (2012). The Nuts and Bolts of Making BYOD Work.Information Management Journal. Hunt, J. (2012). BYOD Policy. What Businesses Need to Consider. Credit Control, no. 5. Kahlke, R. M. (2014). “Generic qualitative approaches: Pitfalls and benefits of methodological mixology.” International Journal of Qualitative Methods, 13(1), 37-52. http://journals.sagepub.com/doi/full/10.1177/160940691401300 119 Khurana, N., Saggar, S., &Kaur, B. (2016). Data security during cloud storage in public cloud using “Kerberos: An authentication protocol”. JIMS8I-International Journal of Information Communication and Computing Technology, 4(2), 226-231 Liu, B. (2012). "Sentiment analysis and opinion mining."Synthesis lectures on human language technologies, 5(1), 1-167. Marcus, S. (2013). Automating knowledge acquisition for expert systems (Vol. 57). New York: Springer Science & Business Media. Singh, N. (2012). BYOD is out of the Bottle- Devil or Angel. Journal of Business Management and Social Science Research.1-12. Thomson, G. (2012). BYOD: Enabling the Chaos. Network Security. 5-8 Zhang, X., Kunjithapatham, A., Jeong, S., & Gibbs, S. (2011).
- 18. Towards an elastic application model for augmenting the computing capabilities of mobile devices with cloud computing. Mobile Networks and Applications, 16(3), 270-2 N 90° 0' 0" E 10.600 N 90° 0' 0" E 10.700 Router Wireless Access Point Printer 1 Laptop and Computer Connection Points Boardroom 1 projector and TV Printer 2 Boardroom 2 Projector and TV Printer 3 Boardroom 3 Projector and TV Wireless Access Point Wireless Access Point Laptop and Computer Connection Points Laptop and Computer Connection Points Internet