QSIT-QuantumCryptography.ppt
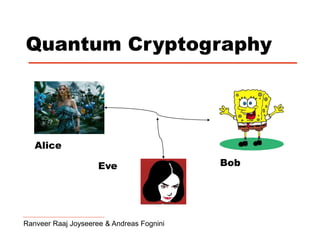
- 1. Quantum Cryptography Ranveer Raaj Joyseeree & Andreas Fognini Alice Bob Eve
- 2. Classical Algorithms 1. Asymmetrical (public-key) cryptosystems: - First implementationnn RSA (Ronald Rivest, Adi Shamir, and Leonard Adleman) 1978 - Very convenient, Internet - Idea is based on computational complexity f(x) = y, x = ?. - rely on unproven assumptions Private Public Message Message Encrypted message
- 3. Classical Algorithms Classical Algorithms 2. Symmetrical (secret-key) cryptosystems: - only provably secure cryptosystem known today - not handy, key as long as message - key only valid for one transmission - how to send the key in a secure manner? M: 1 0 1 0 1 0 1 0 K: 1 0 0 0 1 1 1 0 S: 0 0 1 0 0 1 0 0 Distribute key over secure channel M M S S: 0 0 1 0 0 1 0 0 K: 1 0 0 0 1 1 1 0 M: 1 0 1 0 1 0 1 0 XOR XOR
- 4. Quantum Cryptography: The BB84 Portocol Ingredients: 1) One photon no copying, 2) Two non orthonormal bases sets 3) Insecure classical channel; Internet What it does: Secure distribution of a key, can't be used to send messages How it works: 50% correlated Physikalische Blätter 55, 25 (1999)
- 5. Copy machine: e.g. Eve's copy machine 50% decrease in correlation! Alice and Bob recognize attack from error rate!
- 6. Conclusion Quantum cryptography means just the exchange of keys Actual transmission of data is done with classical algorithms Alice & Bob can find out when Eve tries to eavesdrop.
- 7. Hacking Quantum Key Distribution systems QKD systems promise enhanced security. In fact, quantum cryptography is proveably secure. Surely one cannot eavesdrop on such systems, right?
- 8. Hacking QKD systems Security is easy to prove while assuming perfect apparatus and a noise-free channel. Those assumptions are not valid for practical systems e.g. Clavis2 from ID Quantique and QPN 5505 from MagiQ Technologies. Vulnerabilities thus appear.
- 9. Hacking by tailored illumination Lydersen et al. (2010) proposed a method to eavesdrop on a QKD system undetected. The hack exploits a vulnerability associated with the avalanche photo diodes (APD‘s) used to detect photons.
- 10. Avalanche photo diodes Can detect single photons when properly set. However, they are sensitive to more than just quantum states.
- 11. Modes of operation of APD’s Geiger and linear modes
- 12. Geiger mode VAPD is usually fixed and called bias voltage and in Geiger mode, Vbias > Vbr. An incident photon creates an electron-hole pair, leading to an avalanche of carriers and a surge of current IAPD beyond Ith. That is detected as a click. Vbias is then made smaller than Vbr to stop flow of carriers. Subsequently it is restored to its original value in preparation for the next photon.
- 13. Linear mode Vbias < Vbr. Detected current is proportional to incident optical power Popt. Clicks again occur when IAPD > Ith.
- 14. Operation in practical QKD systems Vbias is varied as shown such that APD is in Geiger mode only when a photon is expected That is to minimize false detections due to thermal fluctuations. However, it is still sensitive to bright light in linear mode.
- 15. The hack in detail Eve uses an intercept-resend attack. She uses a copy of Bob to detect states in a random basis. Sends her results to Bob as bright light pulses, with peak power > Pth, instead of individual photons. She also blinds Bob‘s APD‘s to make them operate as classical photodiodes only at all times to improve QBER.
- 16. The hack in detail C is a 50:50 coupler used in phase-encoded QKD systems. When Eve‘s and Bob‘s bases match, trigger pulse from Eve constructively interferes and hits detector corresponding to what Eve detected. Otherwise, no constructive interference and both detectors hit with equal energy. Click only observed if detected current > Ith.
- 17. The hack in detail Clicks also only observed when Eve and Bob have matching bases. This means Eve and Bob now have identical bit values and basis choices, independently of photons emitted by Alice. However, half the bits are lost in the process of eavesdropping.
- 18. Performance issues? Usually, transmittance from Alice to Bob < 50%. APDs have a quantum efficiency < 50%. However, trigger pulses cause clicks in all cases. Loss of bits is thus compensated for and Eve stays undetected
- 19. Other methods Method presented is not the only known exploit. Zhao et al. (2008) attempted a time-shift attack. Xu et al. (2010) attempted a phase remapping attack.
- 20. Conclusion QKD systems are unconditionally secure, based on the fundamental laws of physics. However, physical realisations of those systems violate some of the assumptions of the security proof. Eavesdroppers may thus intercept sent messages without being detected.
- 21. Rev Mod Phys 74, 145 (2002) Physikalische Blätter 55, 25 (1999) Nature Photonics 4, 686 (2010) Experimental demonstration of phase-remapping attack in a practical quantum key distribution system. Xu et al. (2010) Hacking commercial quantum cryptography systems by tailored bright illumination. Lydersen et al. (2010) Quantum hacking: Experimental demonstration of time-shift attack against practical quantum-key-distribution systems. Zhao et al. (2008). Used Material