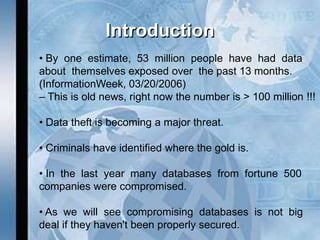
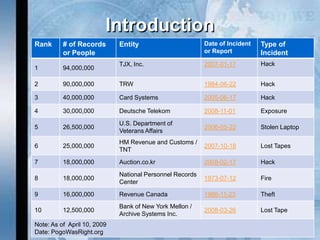
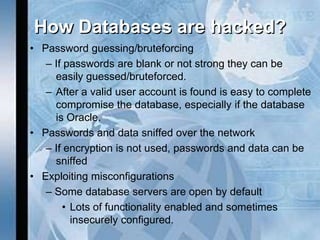
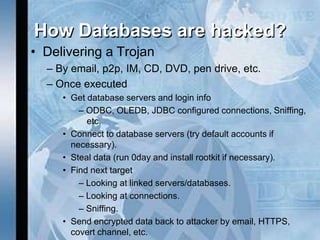
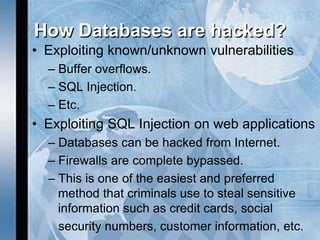
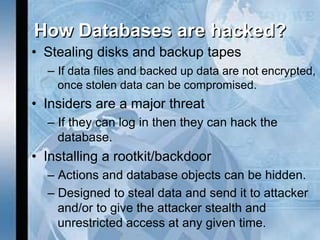
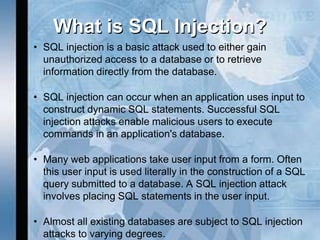
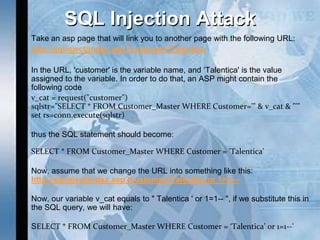
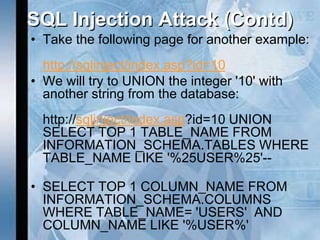
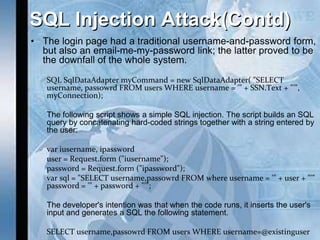
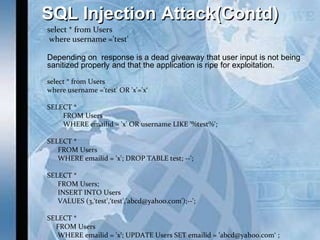
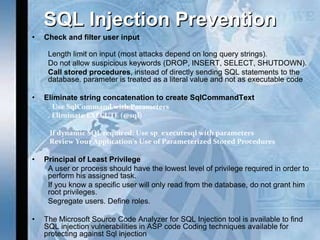
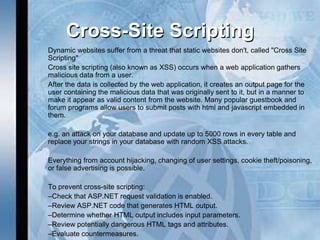
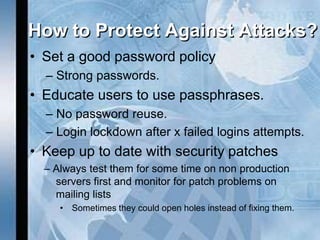
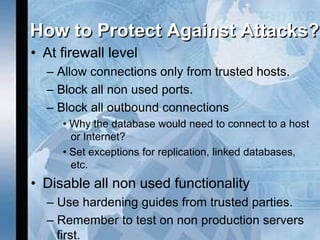
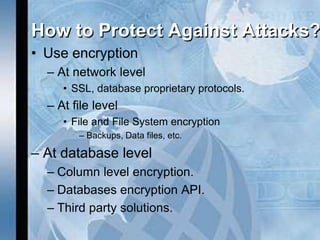
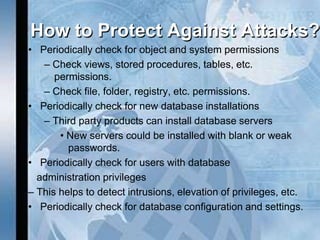
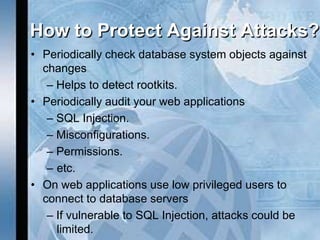
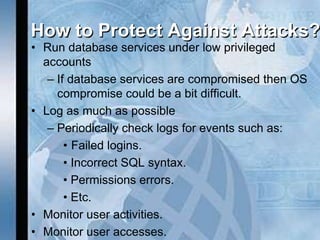
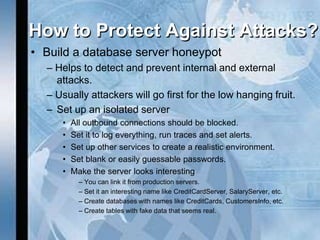
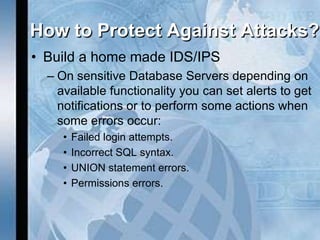
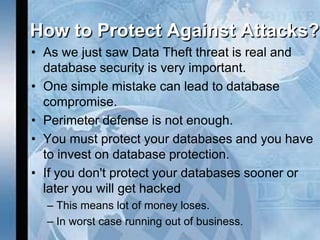
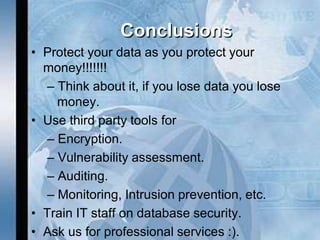
The document discusses the critical importance of database security, highlighting how vulnerabilities, especially through SQL injection, can lead to significant data breaches and financial losses. It outlines methods of hacking databases, preventative measures, and emphasizes the necessity of robust security practices to protect sensitive information. Recommendations include using encryption, strong password policies, and regular audits to safeguard against attacks.