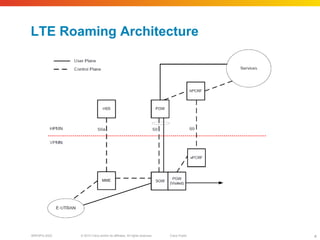
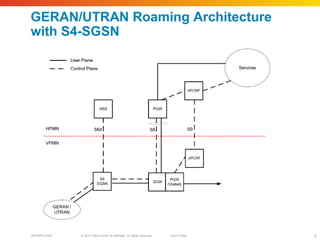
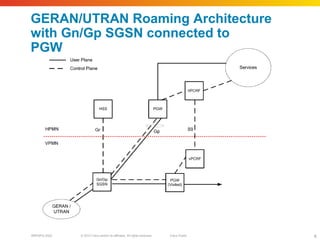
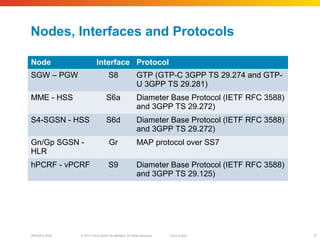
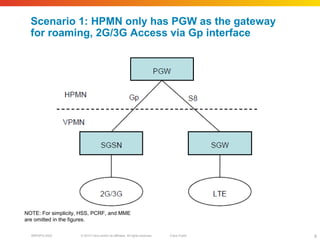
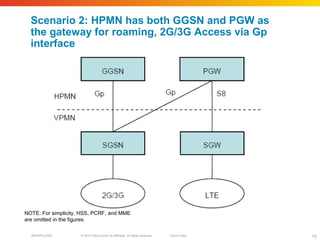
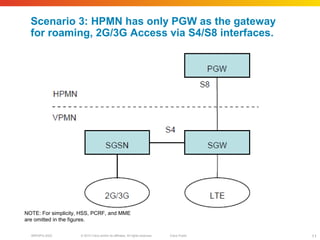
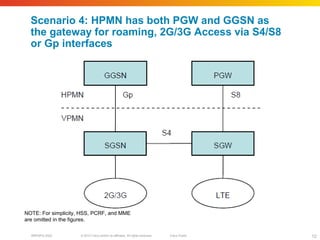
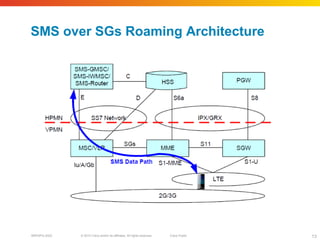
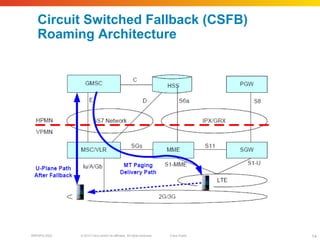
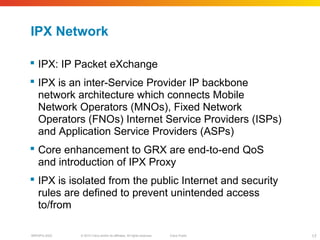
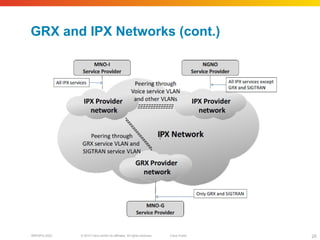
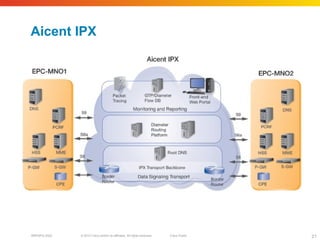
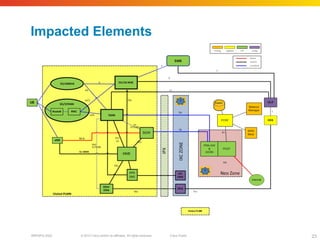
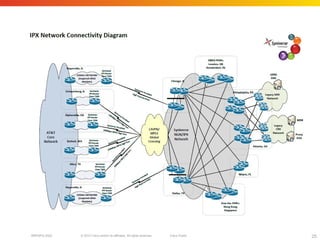
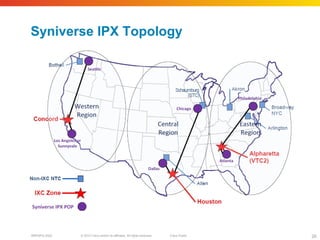
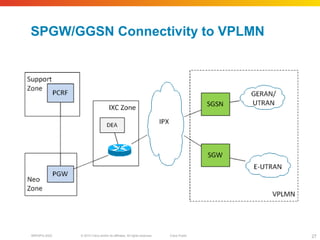
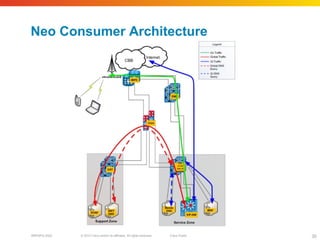
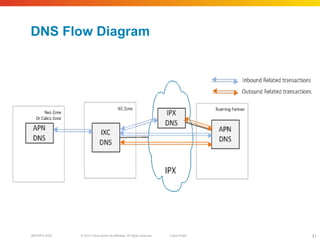
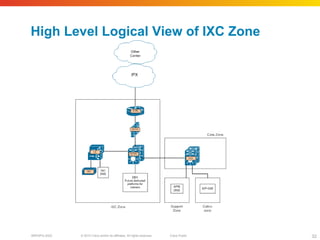
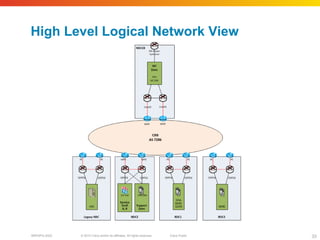
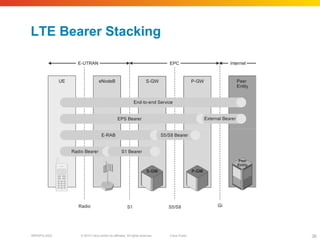
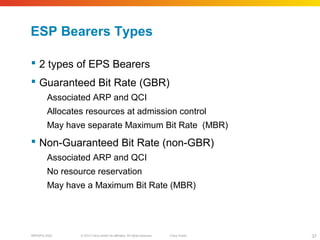
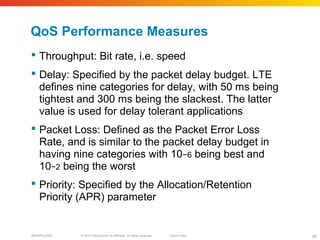
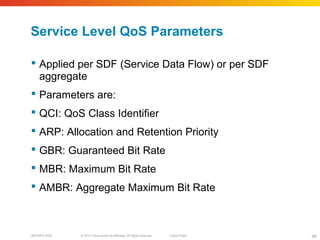
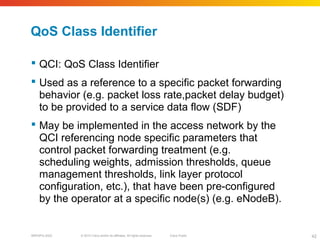
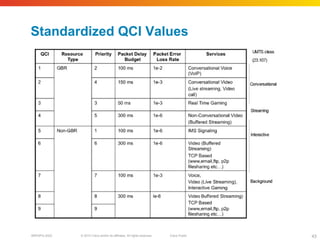
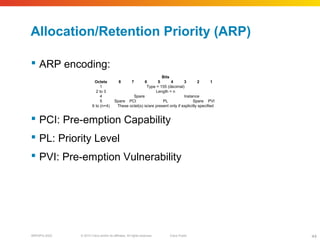
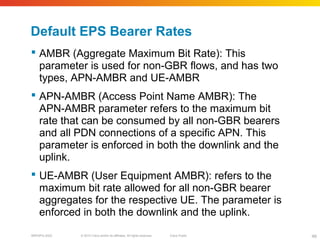
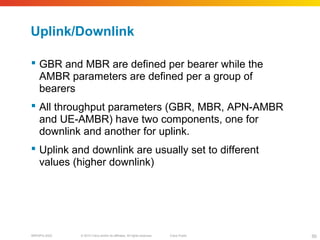
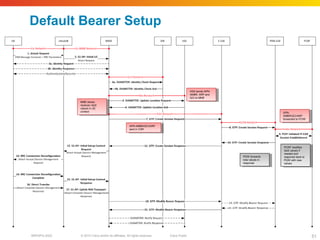
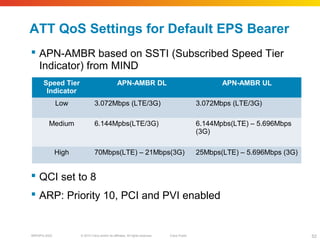
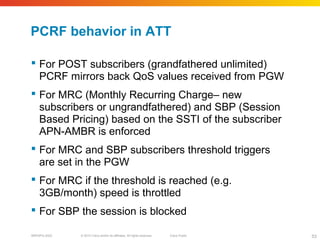
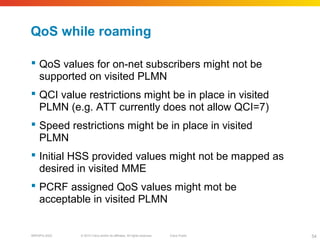
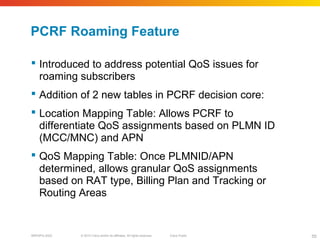
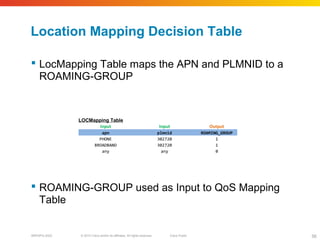
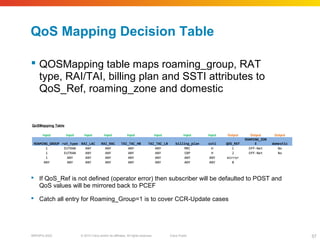
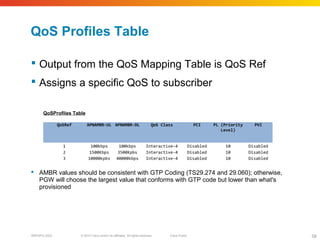
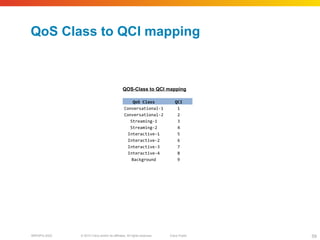
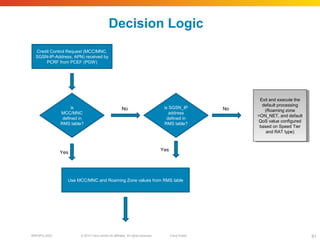
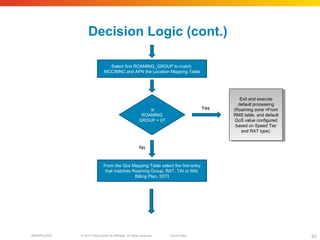
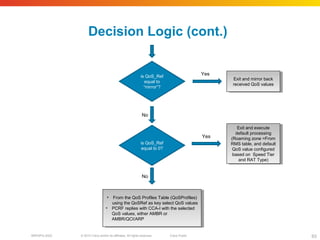
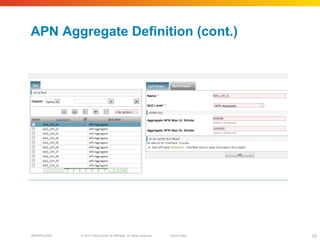
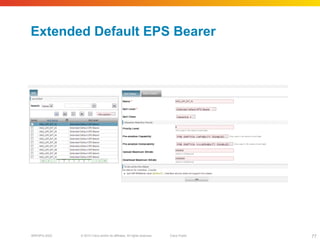
This document provides an overview of LTE outbound roaming and PCRF roaming features. It discusses roaming network architectures including 4G LTE, 3G, and 2G networks. It also covers topics like quality of service, bearers, allocation and retention priority, roaming agreements between operators, and the ATT mobile core network architecture as it relates to roaming. Diagrams are included to illustrate different roaming scenarios and network components.