EMPOWERMENT TECHNOLOGIES Q3 W2.pptx
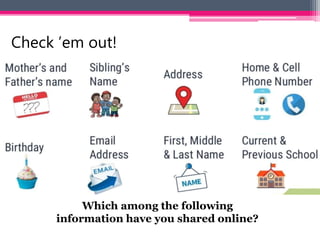
- 1. Which among the following information have you shared online? Check ’em out!
- 2. Online Safety, Security, Ethics, and Etiquette
- 3. Learning Competencies/ Objectives Apply online safety, security, ethics, and etiquette standards and practice in the use of ICTs as it would relate to their specific professional tracks. CS_ICT11/12-ICTPT-Ia-b-2 Unpacked • name the various online threats; • identify the online safety measures; and • apply the online safety and security in using the internet
- 9. • Web-based threats, or online threats, are a subset of cybersecurity risks that involve the potential for an unpleasant event or action to occur through the internet. INFORMATION AT RISKS
- 10. 1. Malware - or malicious software, is any program or file that is harmful to a computer user.
- 11. 2. Spam - an unwanted email mostly from bots or advertisers. It can be used to send malware.
- 12. 3. Phishing - its goal is to acquire sensitive personal information like passwords and credit card details. This is done by sending you an e-mail that will direct the user to visit a fake website and be asked to update his/her username, password, credit card or personal information.
- 13. 4. Predators and Hackers - Computer security dangers and malware are created by people, not machines. Hackers and predators are programmers who prey on others for their personal advantage by hacking into computer systems in order to steal, alter, or destroy data.
- 14. 5. Pharming- Pharmers frequently design web pages that look exactly like those of a reputable organization, such as an online banking log-in page.
- 16. SUM IT UP! •MALWARE •SPAM •PHISHING •HACKERS •PHARMING malicious software junk emails that contains advertisements malicious emails that steal information Programmers malicious code that automatically installed
- 17. Can you give some safety measures on how to stay safe online?