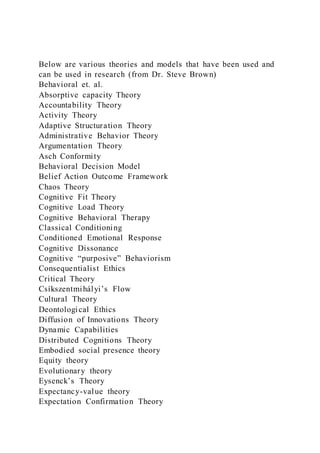
Below are various theories and models that have been used and can
- 1. Below are various theories and models that have been used and can be used in research (from Dr. Steve Brown) Behavioral et. al. Absorptive capacity Theory Accountability Theory Activity Theory Adaptive Structuration Theory Administrative Behavior Theory Argumentation Theory Asch Conformity Behavioral Decision Model Belief Action Outcome Framework Chaos Theory Cognitive Fit Theory Cognitive Load Theory Cognitive Behavioral Therapy Classical Conditioning Conditioned Emotional Response Cognitive Dissonance Cognitive “purposive” Behaviorism Consequentialist Ethics Critical Theory Csíkszentmihályi’s Flow Cultural Theory Deontological Ethics Diffusion of Innovations Theory Dynamic Capabilities Distributed Cognitions Theory Embodied social presence theory Equity theory Evolutionary theory Eysenck’s Theory Expectancy-value theory Expectation Confirmation Theory
- 2. False Memory Syndrome Field Theory Fishbein's Attitude General Deterrence Theory Gestalt Theory of Personality General Strain theory Goal Contagion Theory Gompertz Model (based upon Social Conflict Theory) Grounded Theory Hermeneutics Illusion of Control Impression Management Theory Information Processing Theory Impression Management Theory Information Asymmetry Theory Information Security Management Theory Institutional Theory Integrated Systems Theory Keller's Motivational Model Language action perspective Law of Effect Law of Emotion Learned Helplessness Theory McClelland’s Needs Theory Neutralization Theory Operant Conditioning Mitchel’s Personality theory Prospect Theory Protection Motivation Theory Self Determination Theory Self-Efficacy Theory Social Action Theory Social Conflict Theory Social Cognitive Theory Social Exchange Theory Social Identity Theory
- 3. Social Influence Theory Social Learning Theory Socio Technical Systems Theory Task Closure Theory Technology Acceptance Model Technology Threat Avoidance Theory Theory of Contextualism Theory of Contiguity Theory of Equipotentiality Theory of Planned Behavior Theory of Protection Motivation Theory of Reasoned Action Theory of Planned Behavior Trait Theory Virtue Ethics Unified theory of acceptance and use of technology (UTAUT) Universal Law of Generalization Non-Behavioral Accountability obfuscation Actor Network theory Attack Tree and Vague Sets Bayes Theorem Bayesian Inference Bayesian Belief Network Bayesian Networks Boundary Object Theory Broadbent’s Filter Theory Model Complexity Theory Cooperative game theory Conformity Theory Critical Realism Theory Customer Based Discrepancy Theory Customer Focus Theory Deferred Action Theory Design Theory Elaboration Likelihood Model
- 4. Fit-Viability Theory Flow Theory Game Theory Garbage Can Theory General Systems Theory General Deterrence Theory Hebbian Theory Human Agency Theory Information Warfare Institutional theory International Information Systems Theory Internationalization Theory Information Technology Portfolio Knowledge Management Noncooperative game theory Organization Based Access Control Role-base access control Management (ITPM) model Mere Exposure Effect Multi-attribute Utility Theory Multi-motive Information Systems Continuance Model Organizational culture theory Organizational information processing theory Organizational knowledge creation Organizational learning theory Portfolio theory Process virtualization theory P3P privacy policies Poliheuristic decision theory Privacy-enhancing technologies Retrieval-induced forgetting Social Information Processing Theory Social Learning Theory Social Network Theory Social Penetration Theory Task-technology Fit Model
- 5. Technology Dominance Theory Technology-Organization-Environment TOE Framework Theory of Information Warfare Transaction Cost Economics Tulving’s Model Zeigarnik Effect Internet of Things (IoT), security with TLS Digital Certificates 1 5 Internet of Things (IoT), security with TLS Digital Certificates Internet of Things (IoT), security with TLS Digital Certificates Sai Balaji Yamsani University of the Cumberland’s
- 6. Internet of Things (IoT), security with TLS Digital Certificates Introduction The cited problem is security issues that occur in the application of Internet of Things. The platform encounters a lot of challenges due to the variety of devices connected and numerous operations that depend on the online communicatio ns (Sfar, 2018). Security incidents such as hacking are prone as the IoT gets targeted for its high performance and capability of promoting connectivity. The persons mainly affected by problems in IoT are the device manufacturers, clients, and technical teams that get constantly engaged with the devices to facilitate their seamless operations. The purpose of this research is to asses IoT issues that lead to the suitable solution which is to implement the use of digital TLS 1.2 certificates for internet of things. (Comments from professor :Need a reference to support this ) Comment by Dr_Webb: Need a reference to support this Problem and Research Theory Model The IoT industry has faced challenging issues related to its capability of connecting devices and implementing high quality technology for manufacturing industry. An issue discovered is transition of already existent systems to full IoT functions that can improve on business functionality. Change from M2M to IoT is exposed to such issues that require more study to determine a smooth transition procedure (SierraWireless, 2017). The theoretical framework suitable for this study is use of a conceptual framework to analyze different components in the
- 7. area of IoT. It is possible to determine variables in research using the theoretical framework. In this paper, the variables are IoT devices, TLS certificates, and technology improvements in the areas. (Professor comments - You need to identify a model. Comment by Dr_Webb: You need to identify a model. I have provided a list in the announcements. Issues of security in the IoT are connected lack of accuracy in access control, limited privacy, little trust in the connectivity for the devices, and inability to identify the required operations to enhance the IoT’s adaptations in many industries. The security challenges have been common since digital transformation has resulted in the majority of people in the industry adapting to the use of IoT devices in their daily lives and for work purposes (Sfar, 2018). The deployment of IoT technology in different industries results in security issues due to the new connectivity required as well as the need to employ persons with the appropriate knowledge. The population involved in this project is persons who use IoT devices, technical teams required to maintain the devices, and manufacturers that adopt the use of IoT for their products. The common IoT devices include “smart fridges, smart Mobiles, smart refrigerators, smart watches, smart fire alarm, smart door lock, smart bicycle, medical sensors, fitness trackers, smart security system” (Software Testing, 2021). The population to get studied shall provide suitable insight into how the IoT devices function. It would be possible to determine adaptability of the devices to the current market. All technical teams involved would lead to a discovery of the required developments to handle the system’s operations. (professor comments: your population is too broad. Need a better one.) Application of a qualitative research model is the effective way of improving the value of understanding IoT industries. Qualitative research method is applicable by studying documents that contain information related to the topic (McLeod, 2019). The study shall assess different documents to determine how use of TLS certificates gets conducted in the
- 8. current IT environment. Analysis of documents developed by persons qualified to handle the topics would be an effective method of supporting use of TLS certificates. There are numerous documents created by valid persons with experience in handling TLS certificates in the IoT industry. Comment by Dr_Webb: Your population is too broad. The article chosen for this approval paper is “Enhancing Digital Certificate Usability in Long Lifespan IoT Devices by Utilizing Private CA” by Yamakawa et al. (2018). The article is closely related to my topic since it explains that the IoT’s security issues can get managed by adopting the use of digital certificates. The article offers effective connection to the topic since it is possible to generate proper solutions for the challenges connect to IoT operations. The participants in the article were persons that possessed technical knowledge of operation of IoT devices. The study analyzed how cloud server operations and the security components promote the development of factual security performance enhancement. It is possible to increase the widespread manufacture of IoT devices after adopting the operations to facilitate accuracy and smooth operability.
- 9. Reference SierraWireless. (2017). What is M2M? : The Evolution from M2M to IoT. Retrieved 5 June 2021 from https://www.sierrawireless.com/iot-blog/m2m-vs-iot-vs-ioe/. Software Testing. (2021). 18 Most Popular IoT Devices In 2021 (Only Noteworthy IoT Products). Retrieved 5 June 2021 from https://www.softwaretestinghelp.com/iot-devices/. Sfar, A. R., Natalizio, E., Challal, Y., & Chtourou, Z. (2018). A roadmap for security challenges in the Internet of Things, Digital Communications and Networks, 4, (2). 118-137, https://doi.org/10.1016/j.dcan.2017.04.003. Yamakawa, D., Okimoto, T., Teerakanok, S., Inomata, A., & Uehara, T. (2021). Enhancing Digital Certificate Usability in Long Lifespan IoT Devices by Utilizing Private CA. Security And Communication Networks, 2021, 1-14. https://doi.org/10.1155/2021/6610863