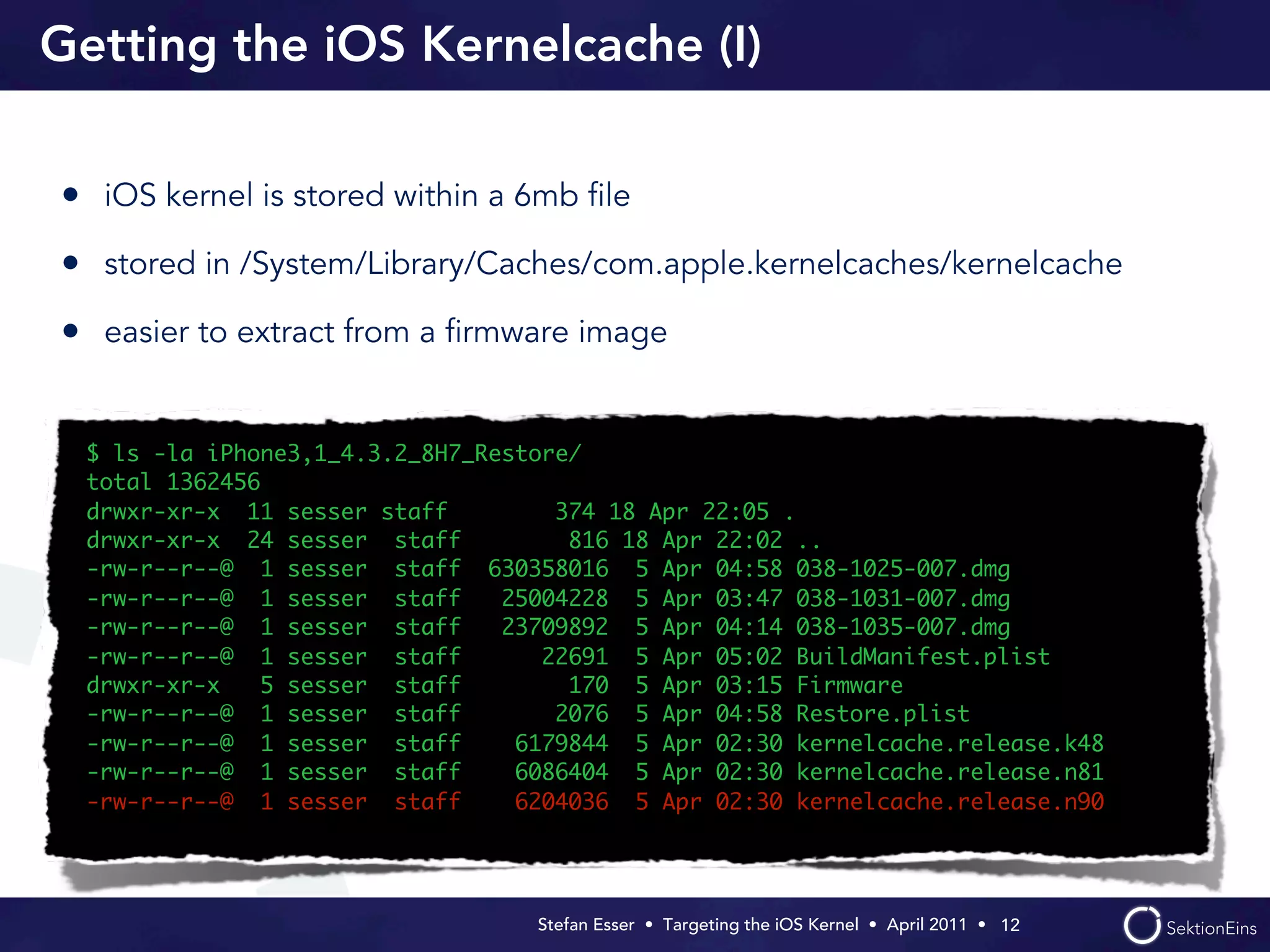
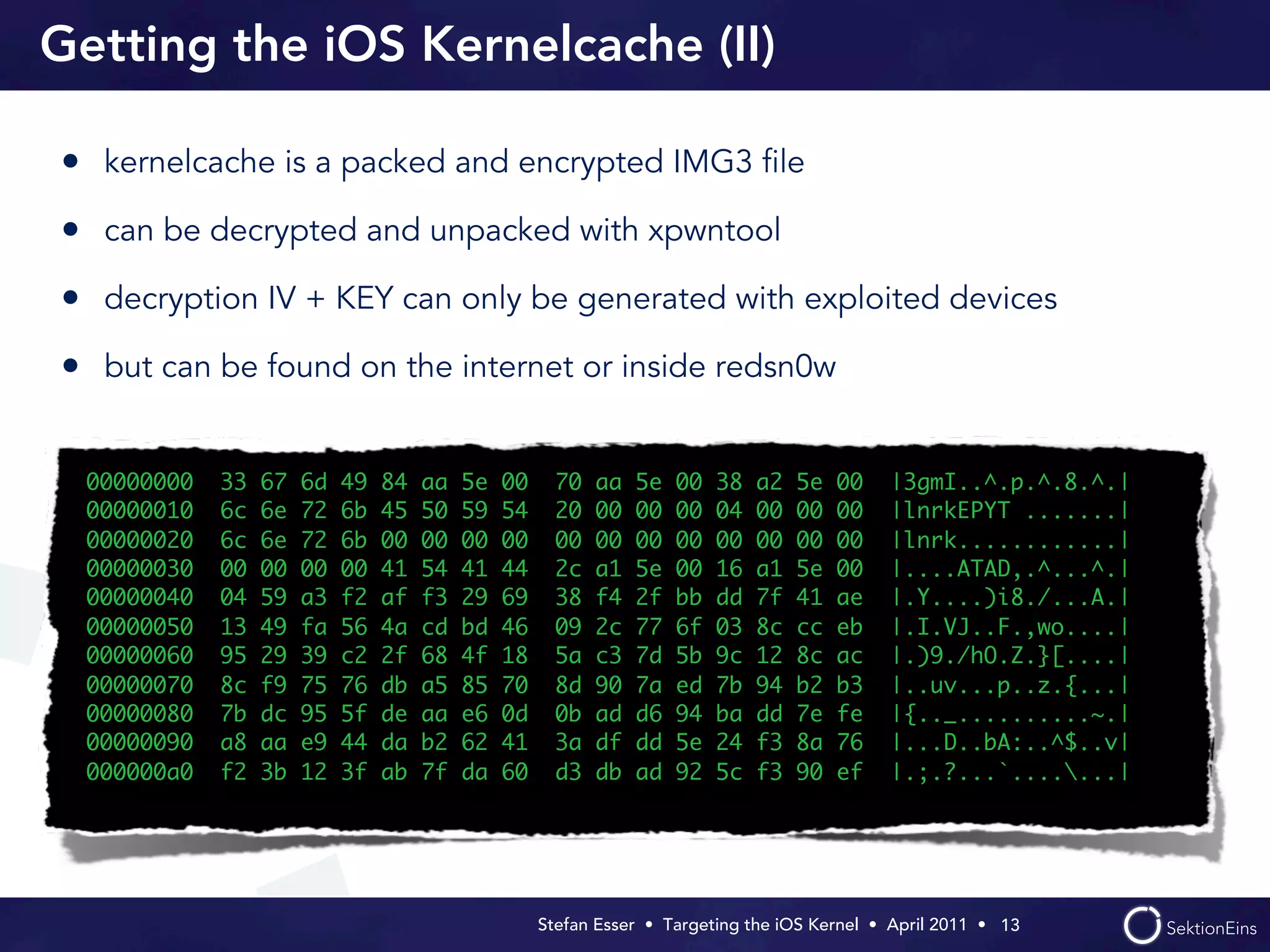
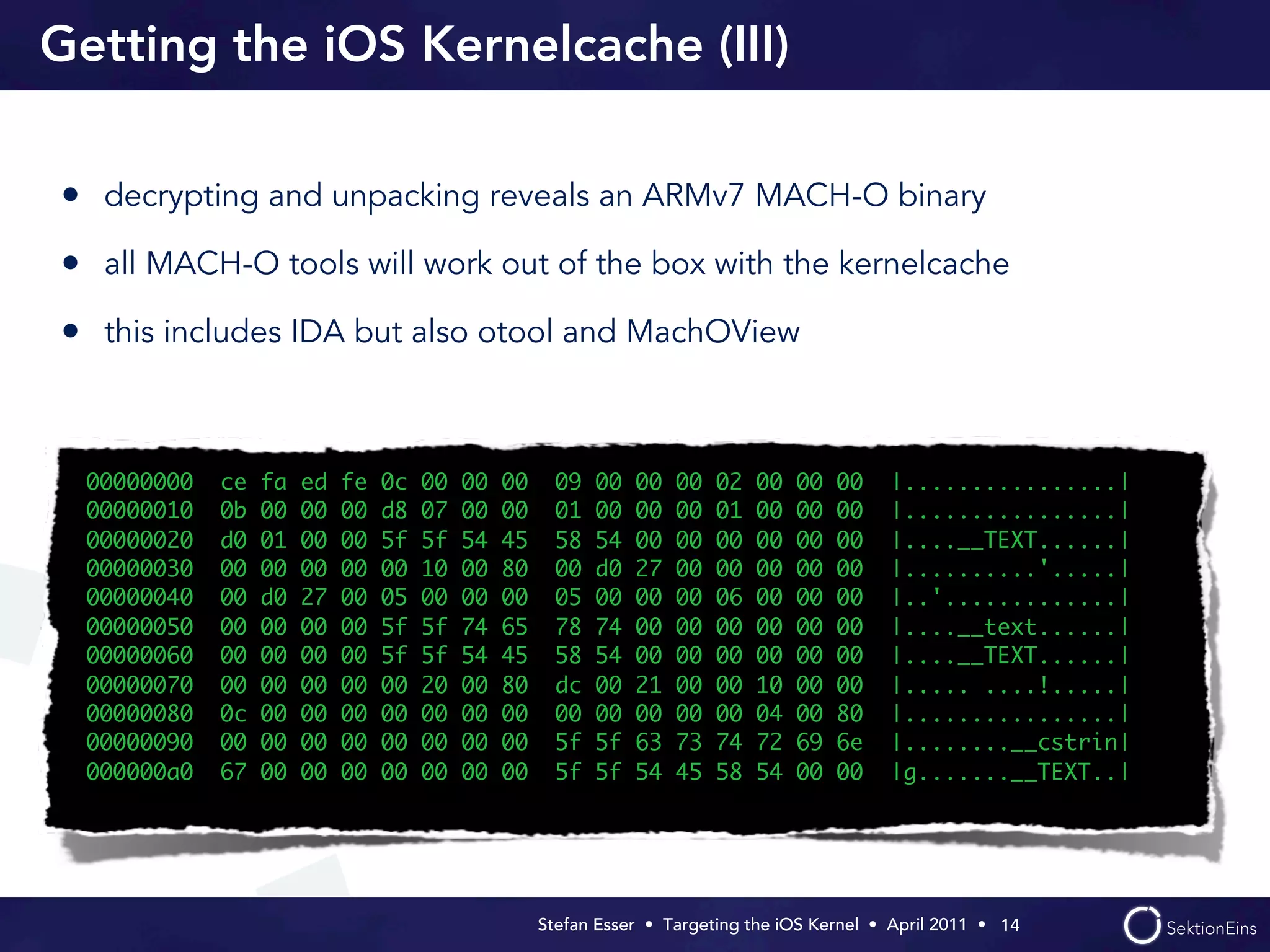
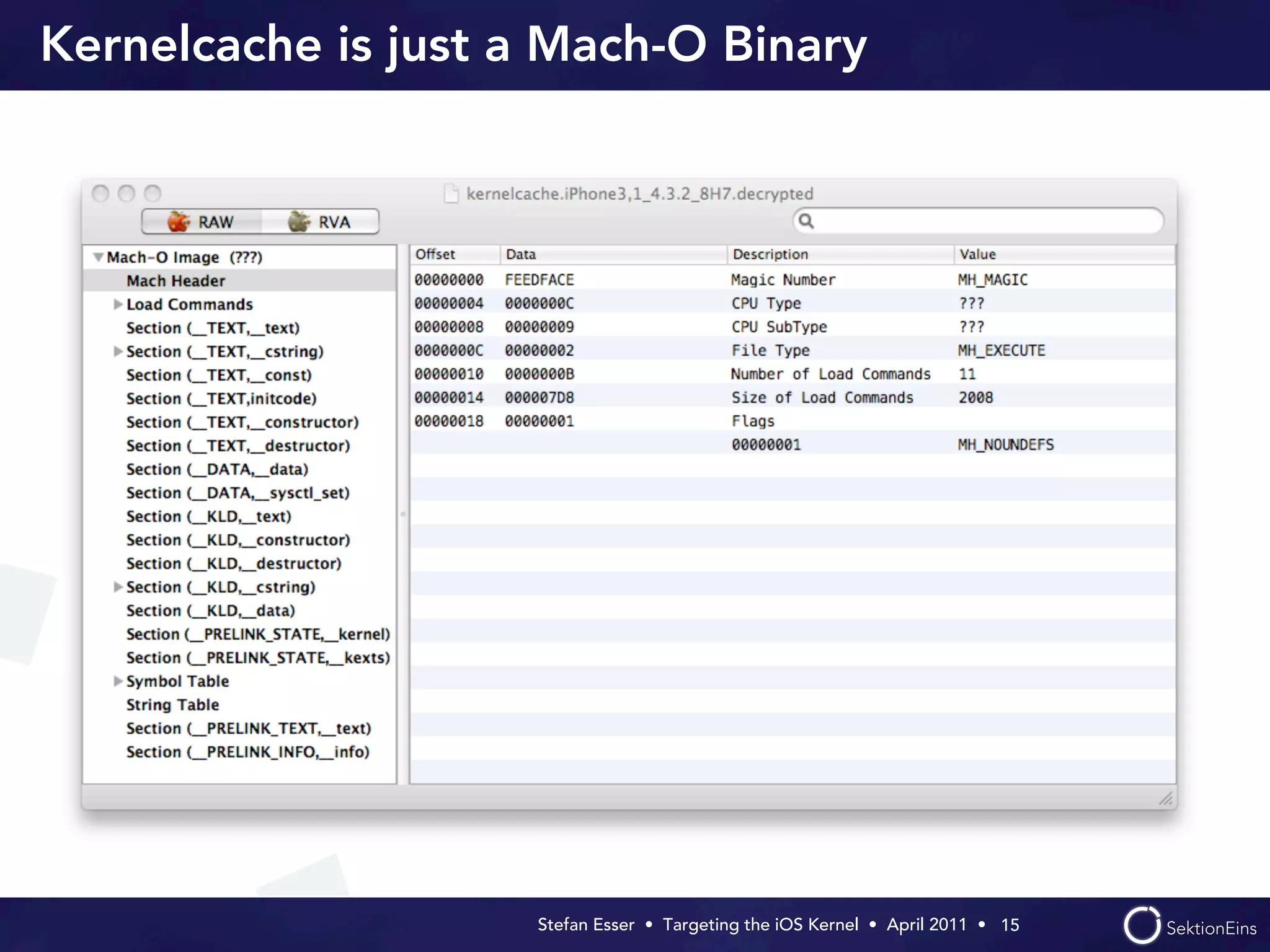
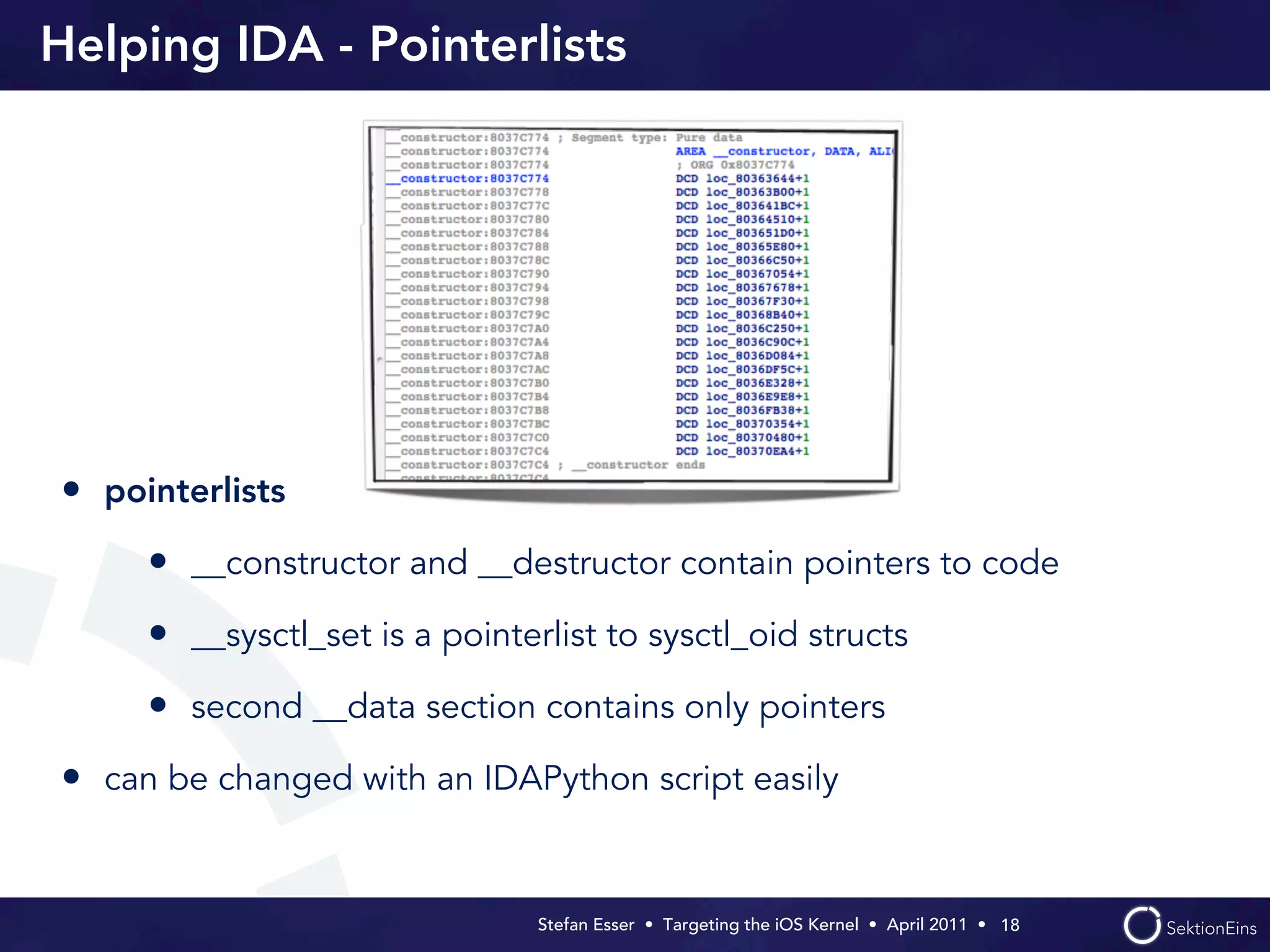
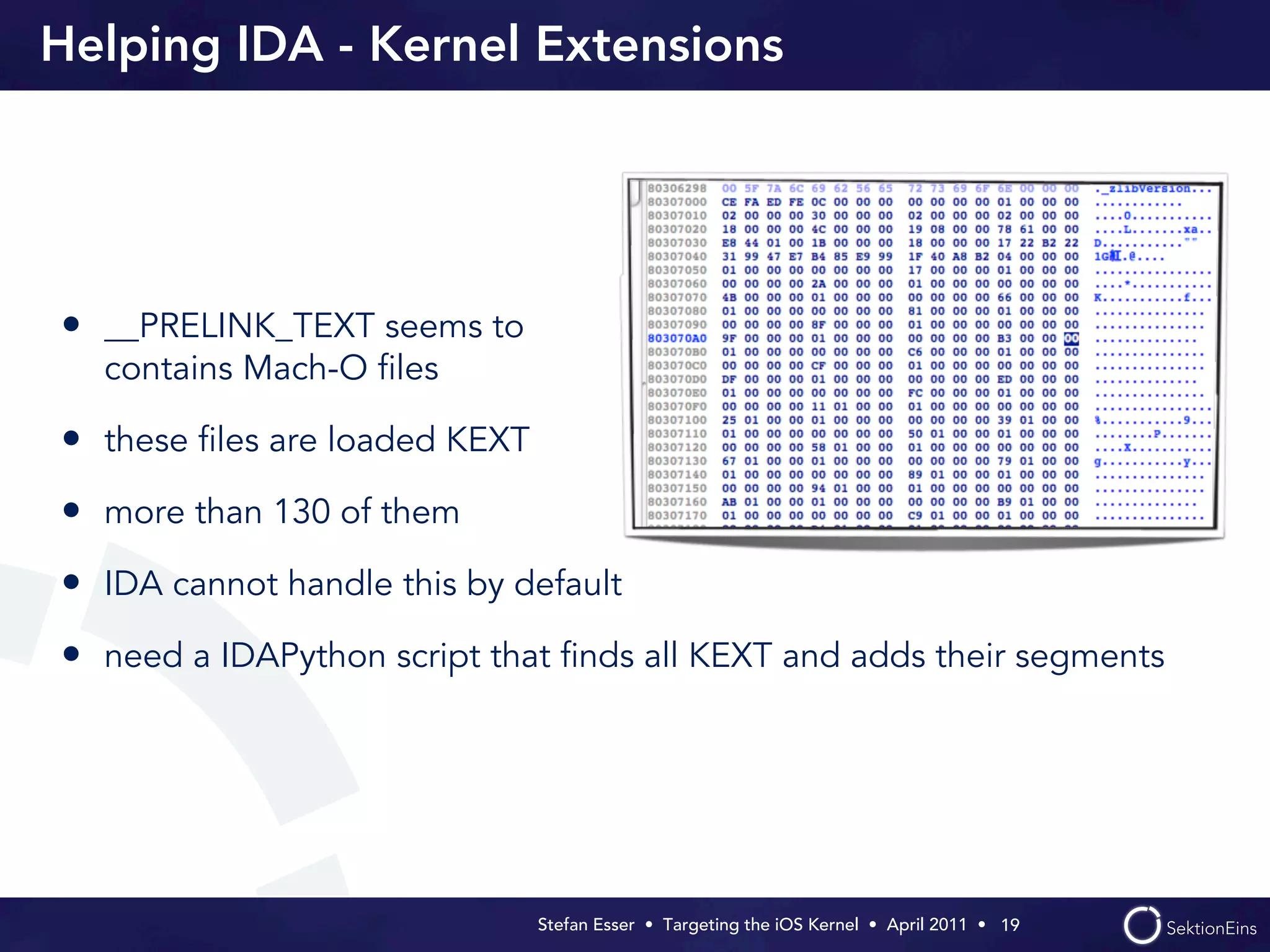
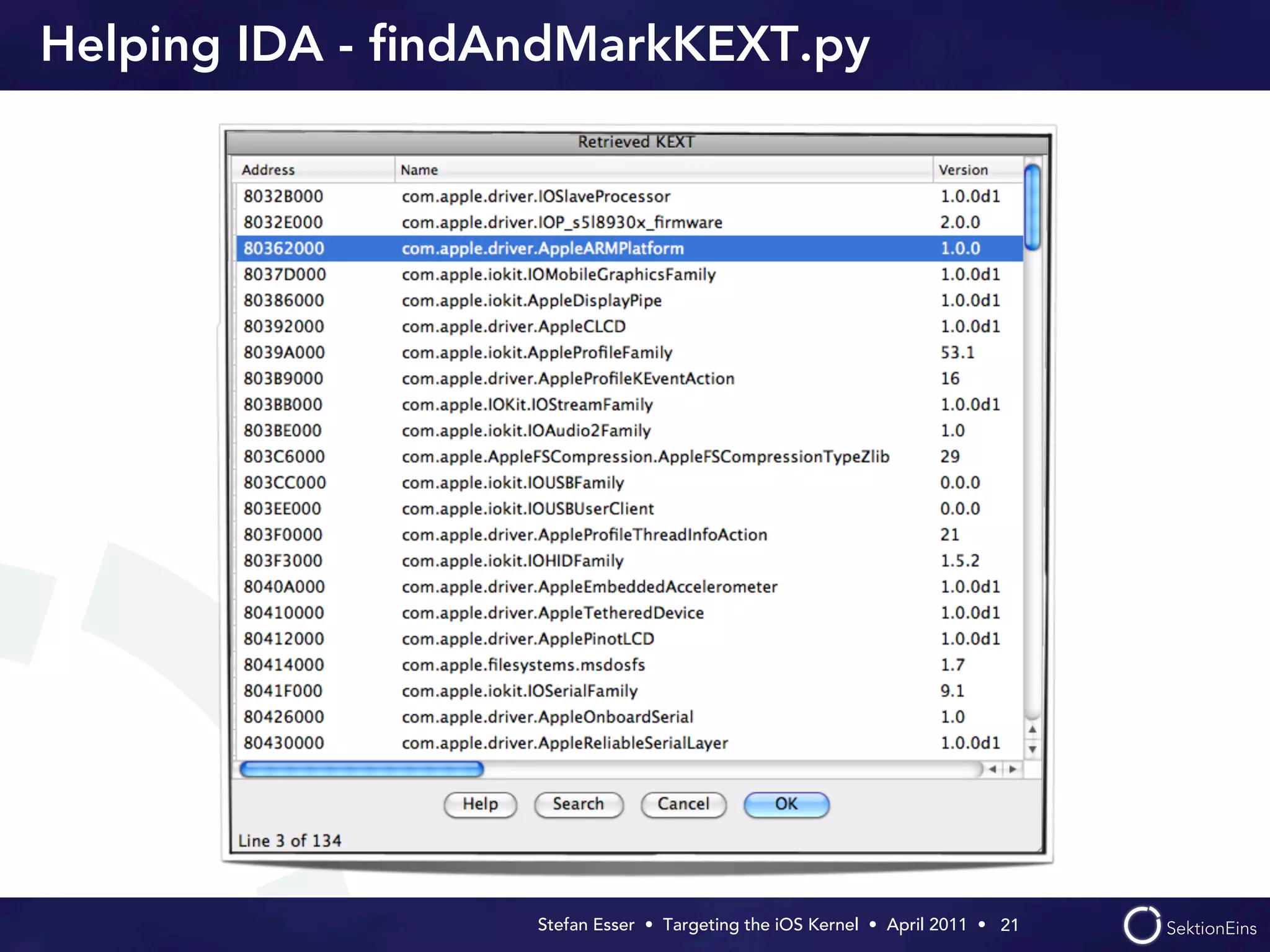
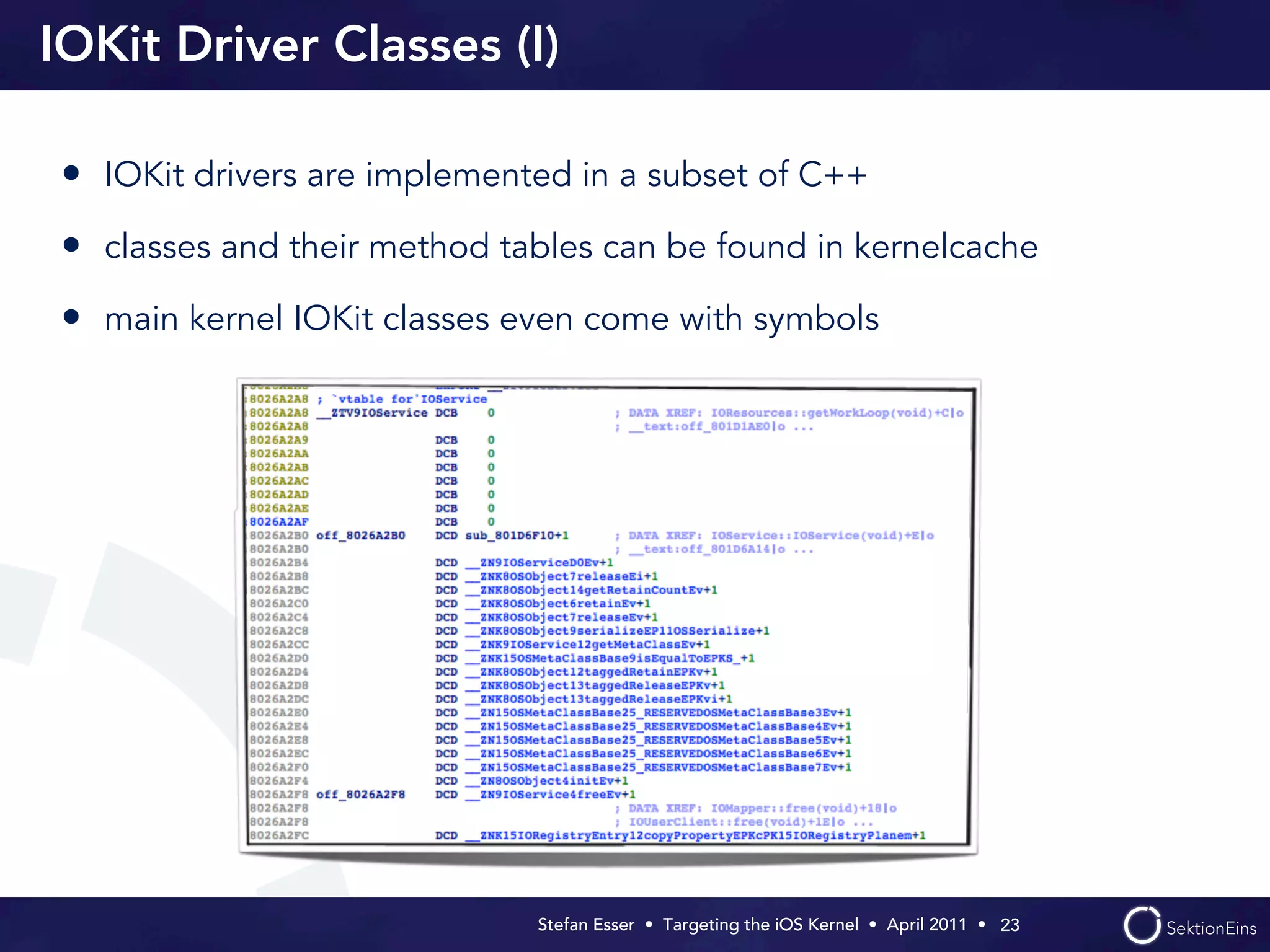
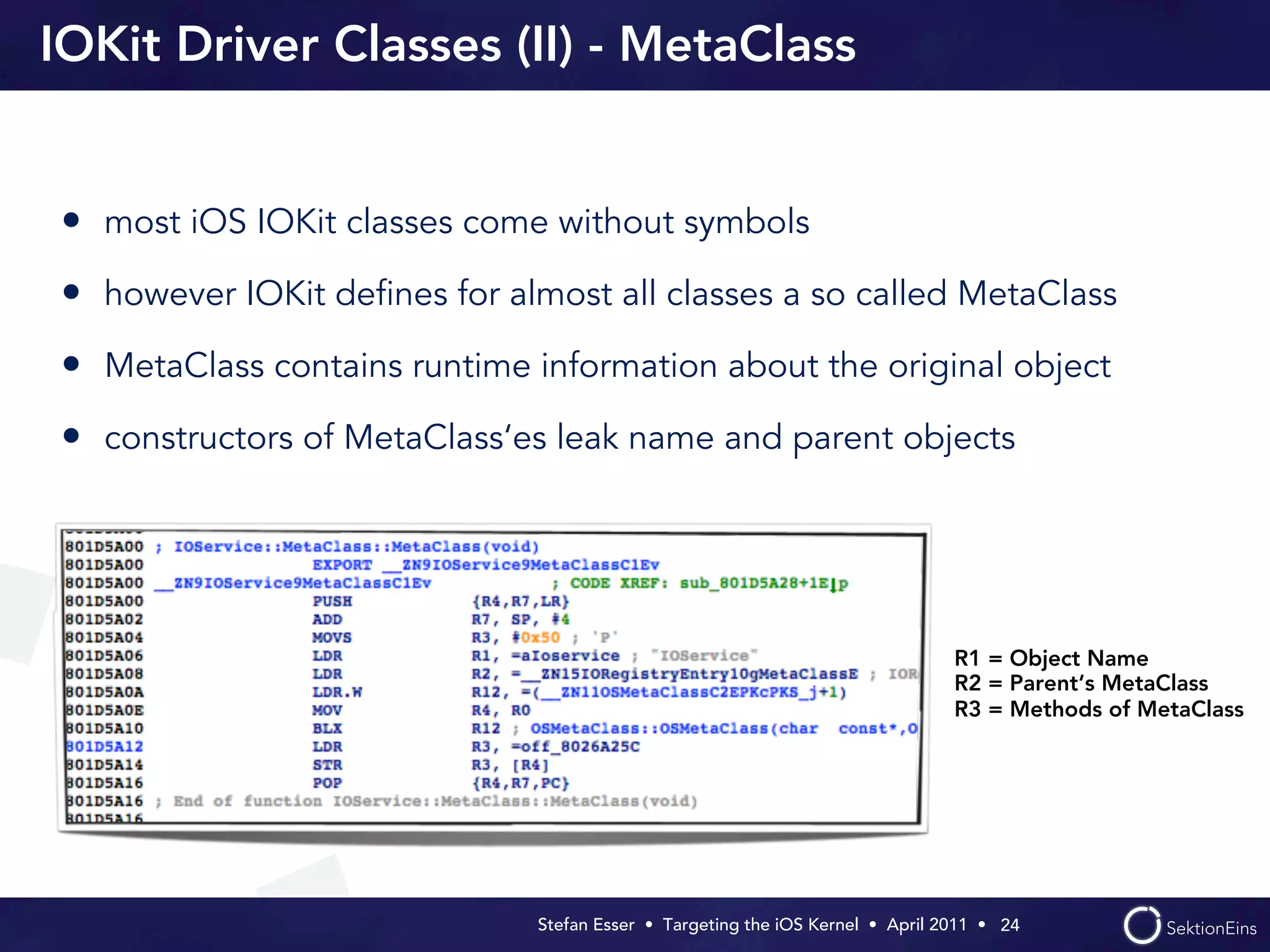
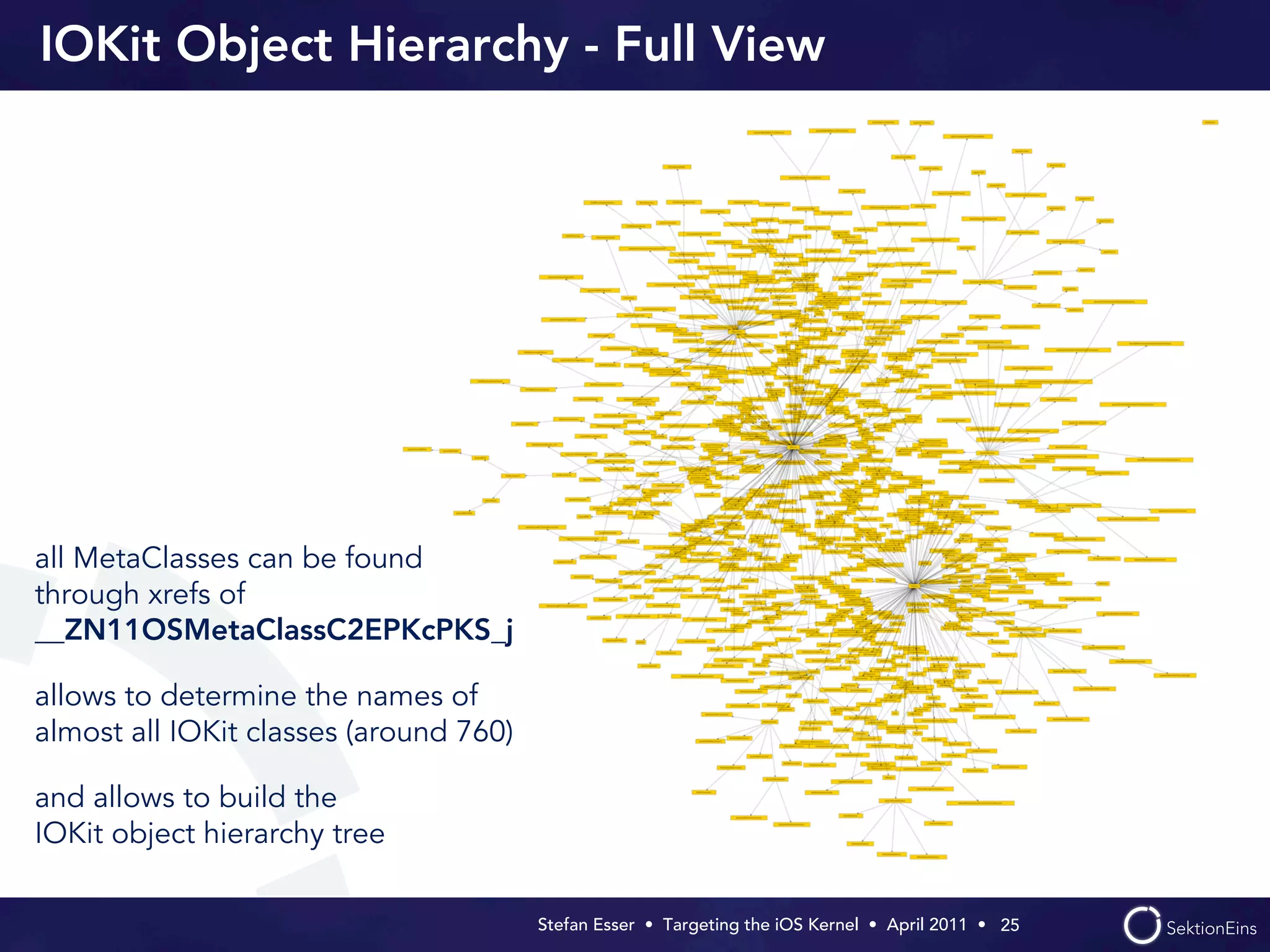
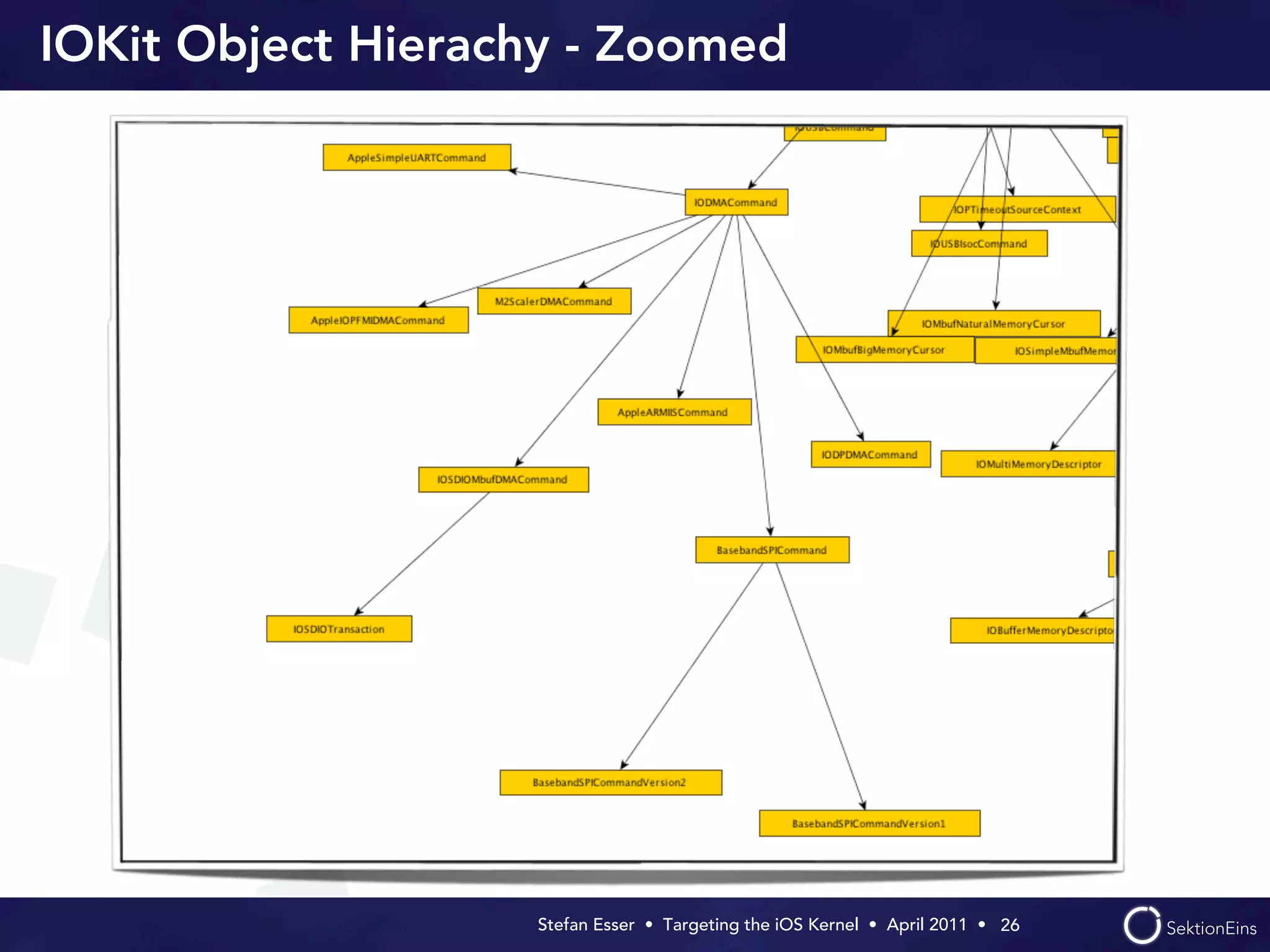
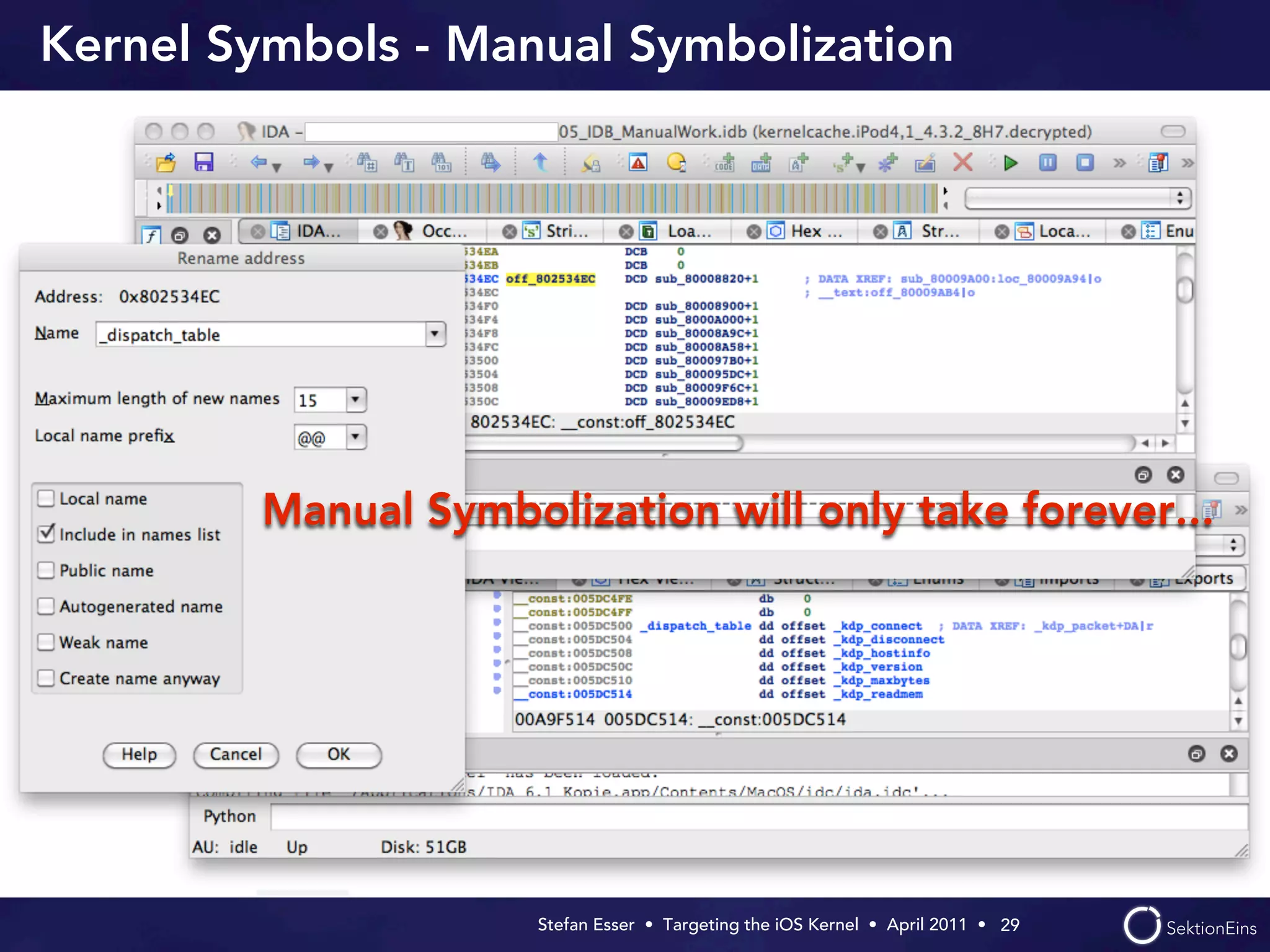
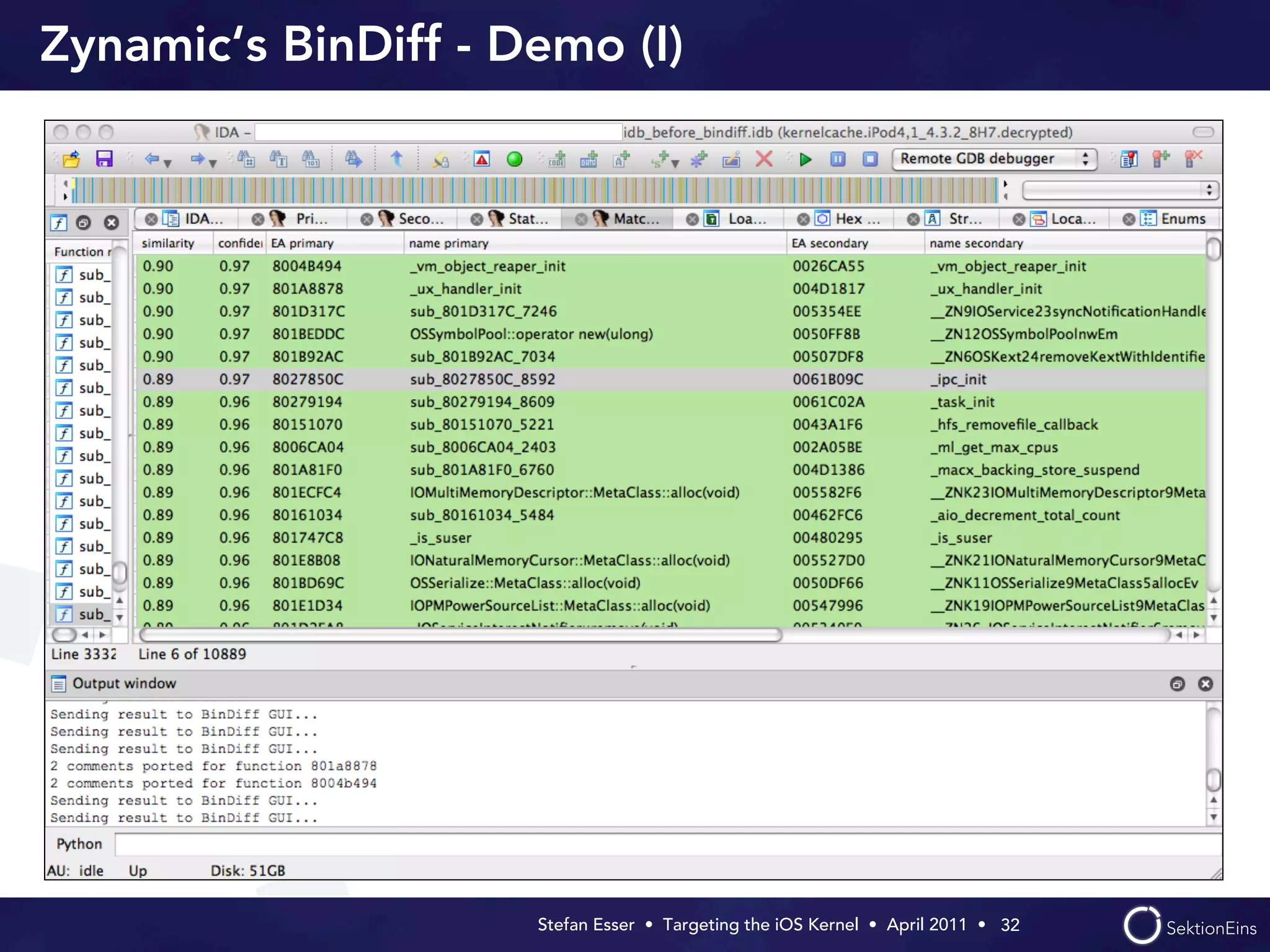
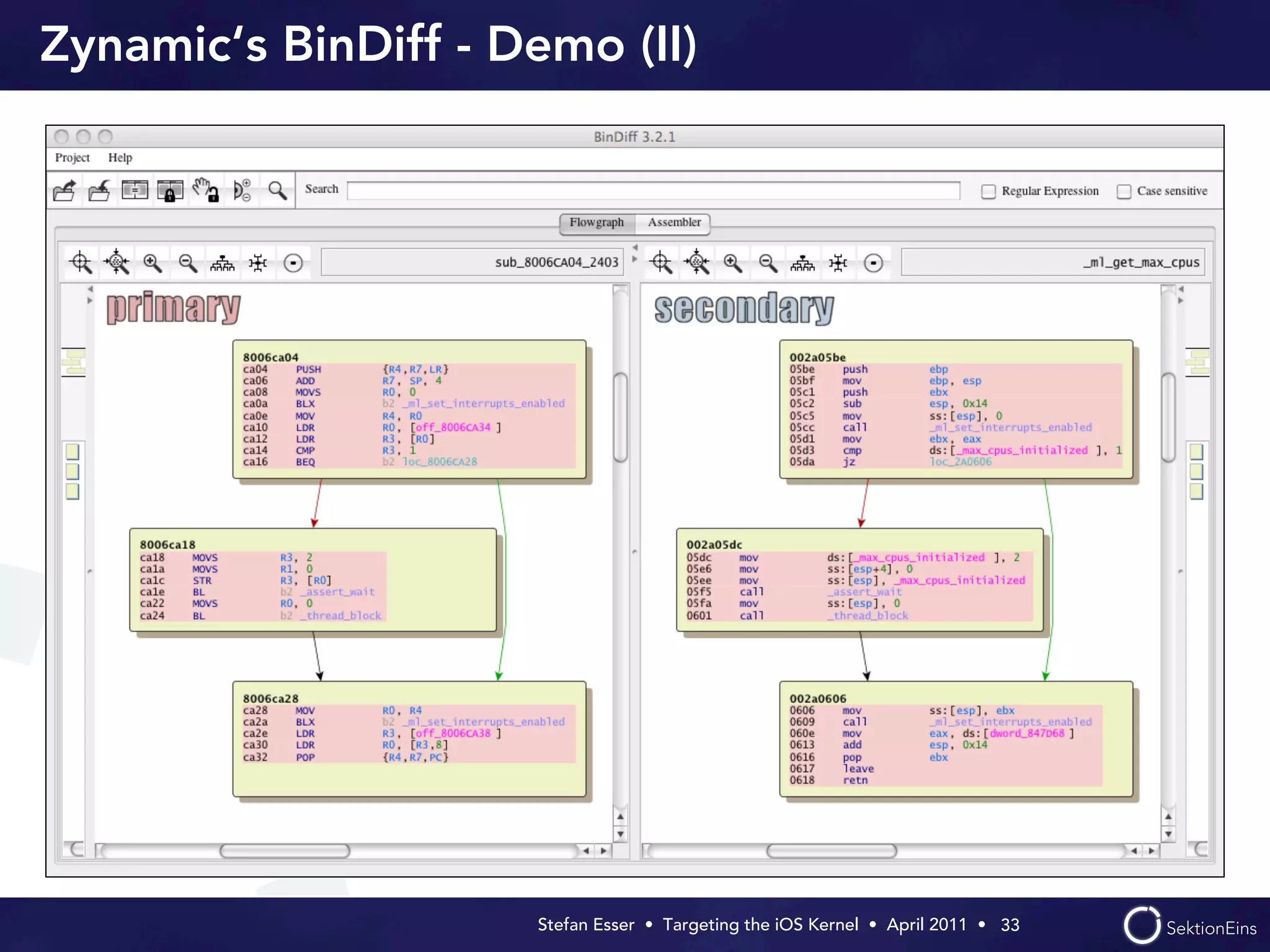
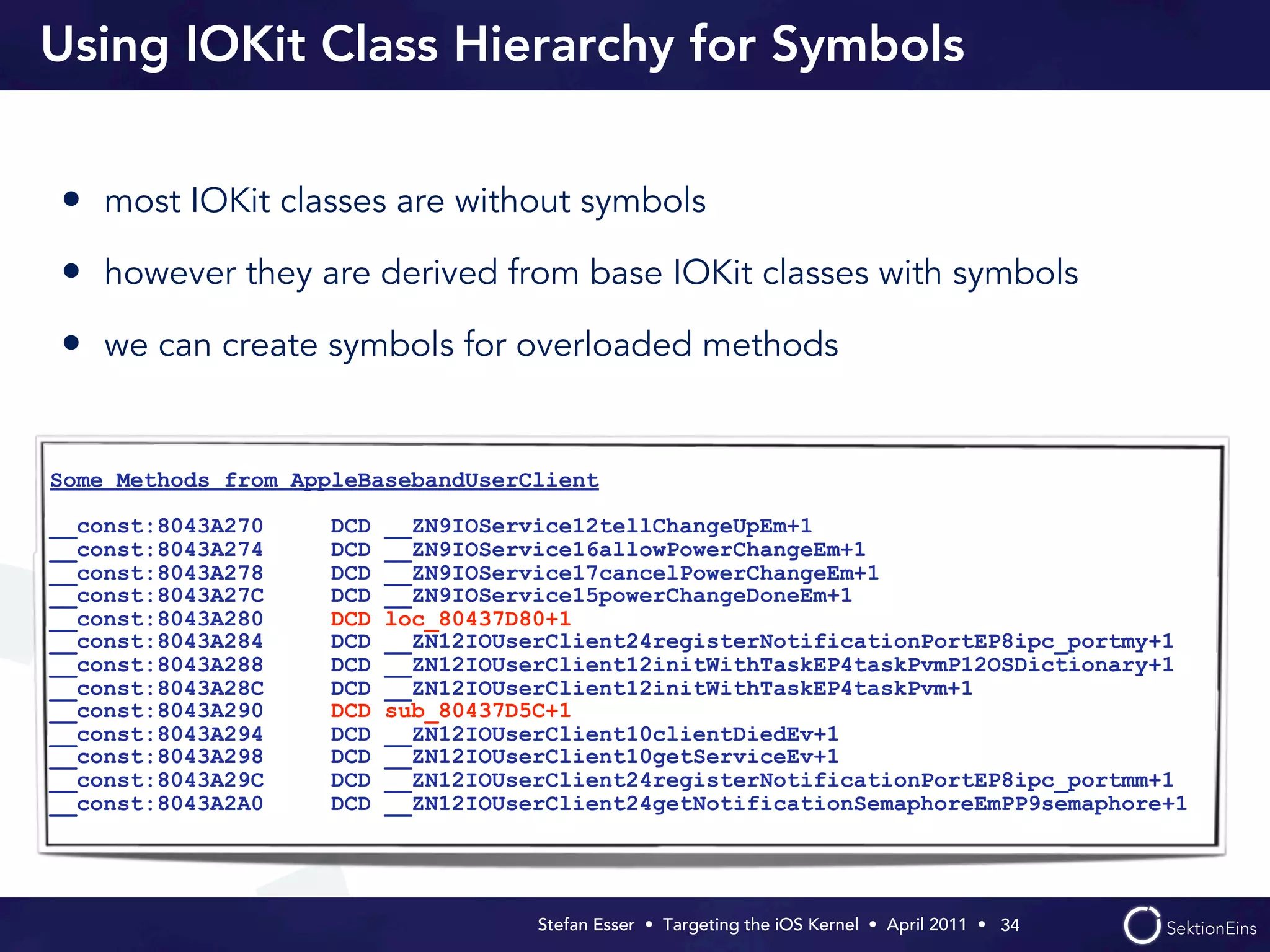
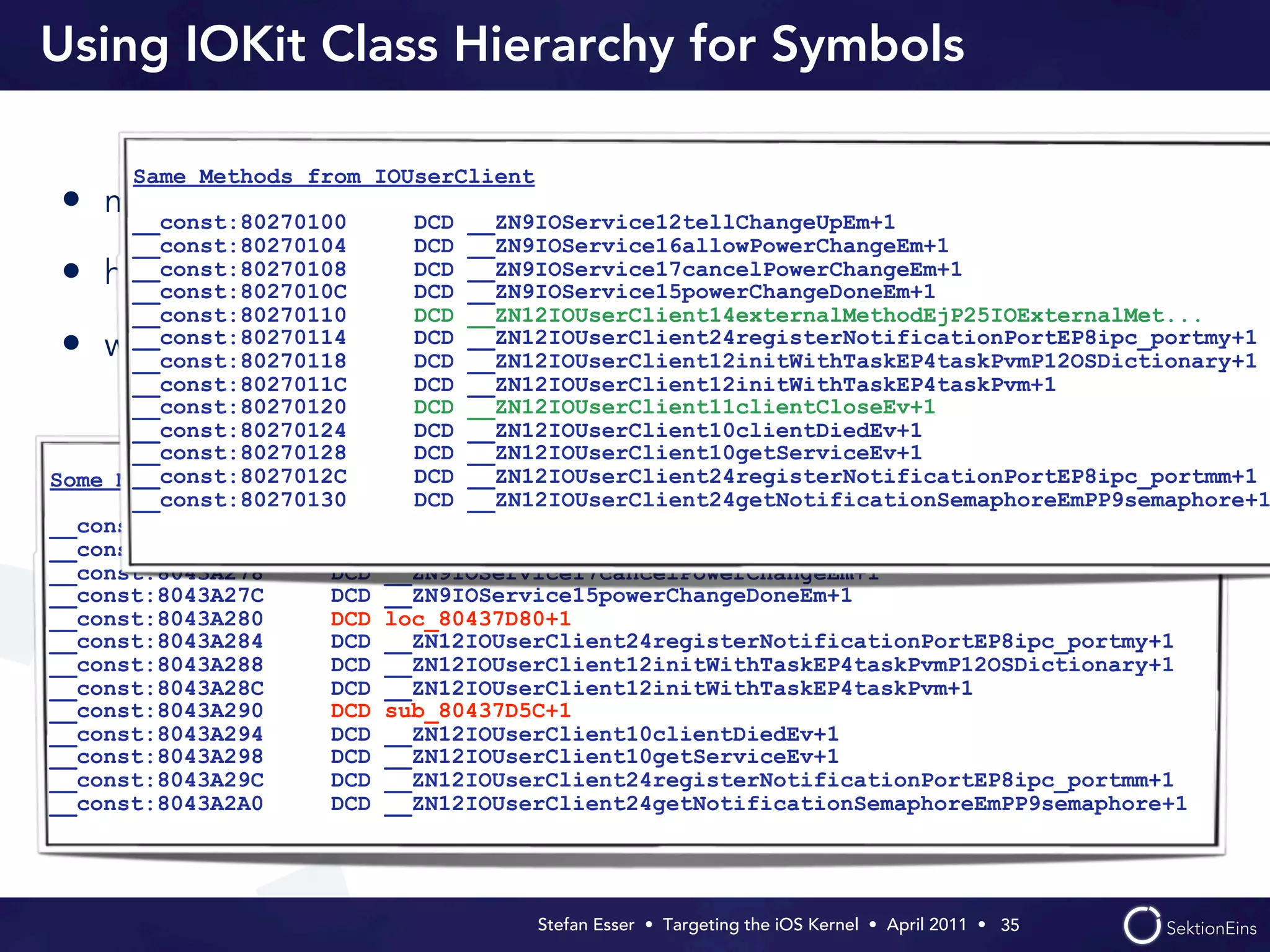
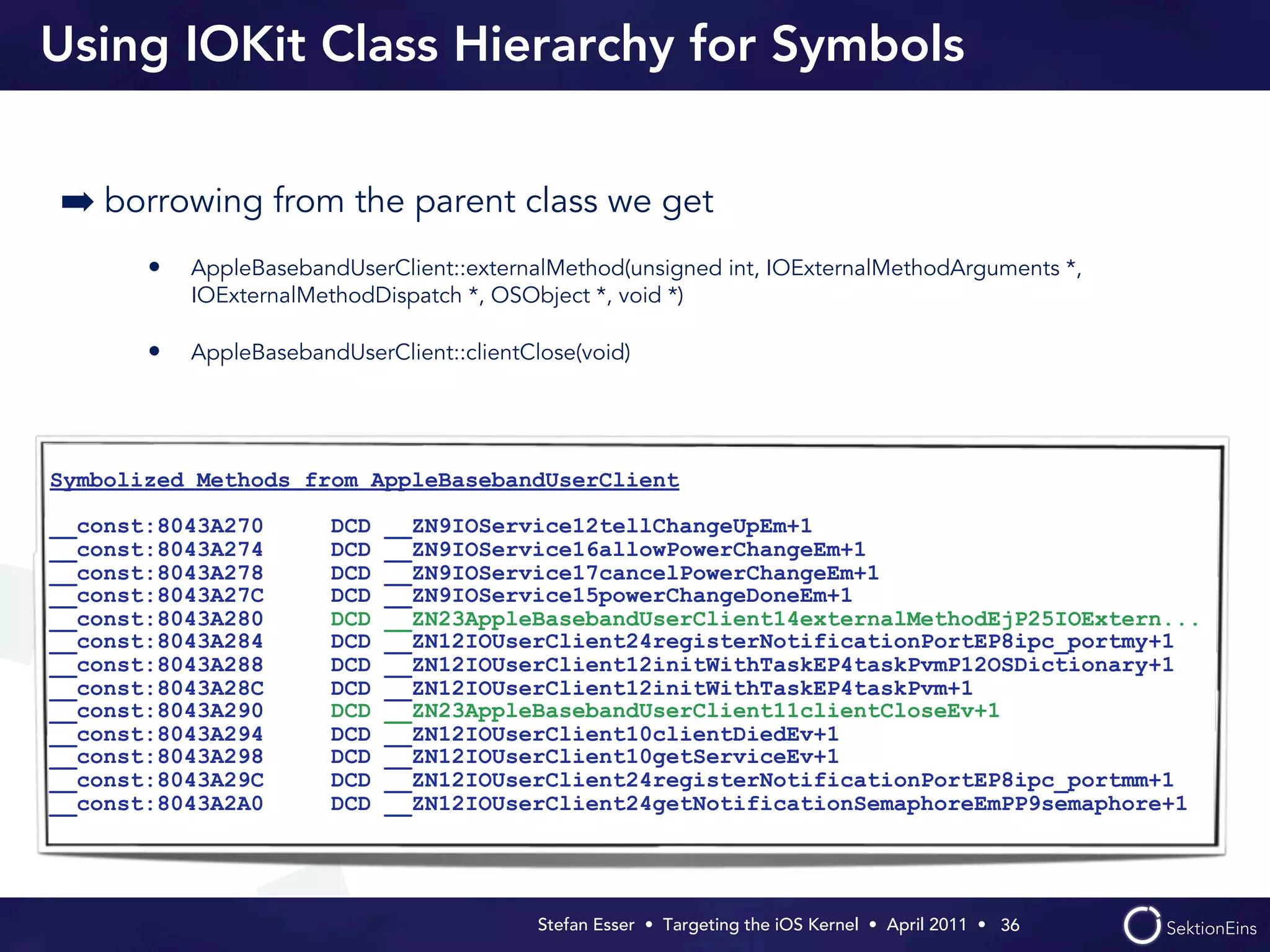
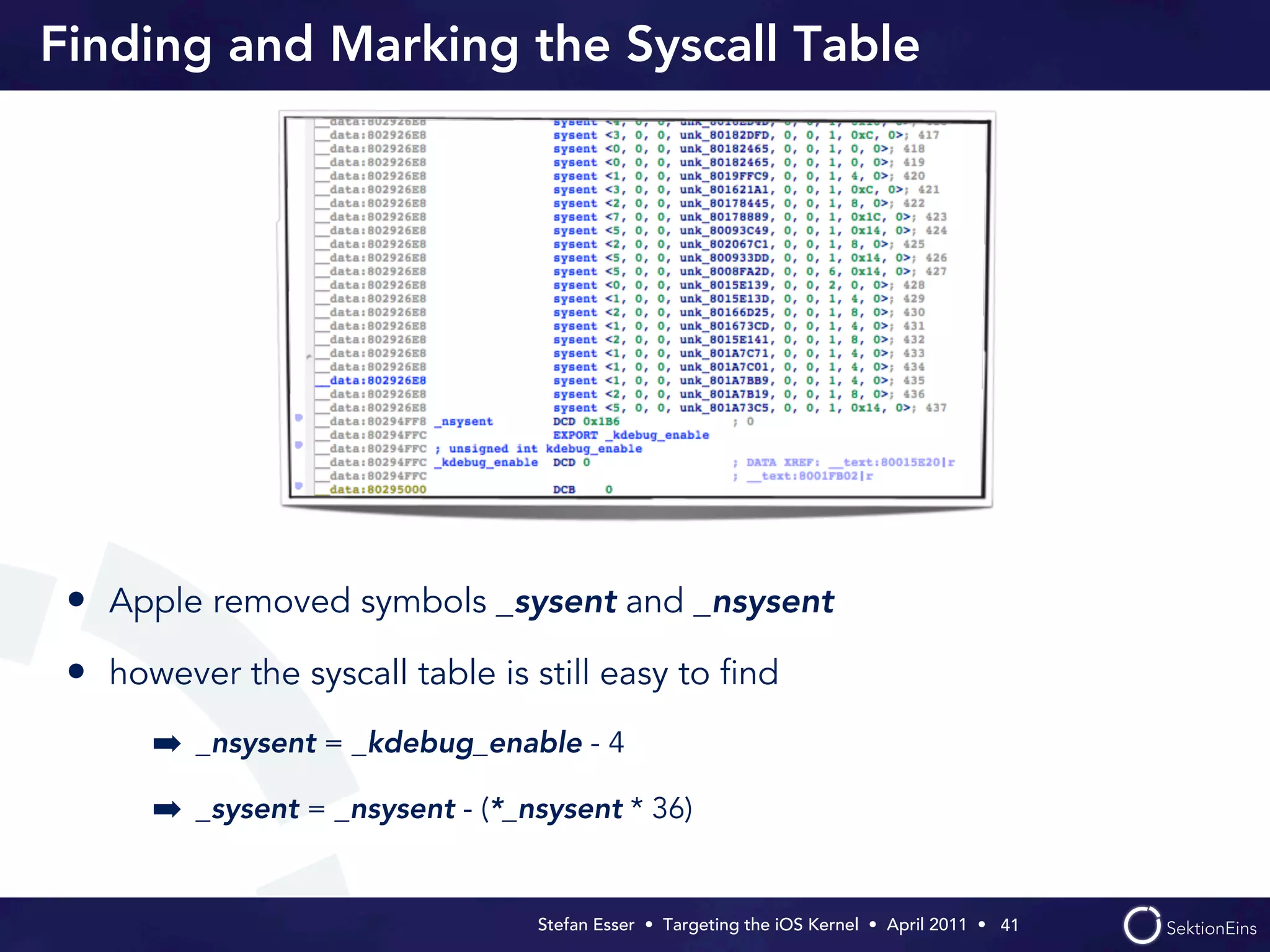
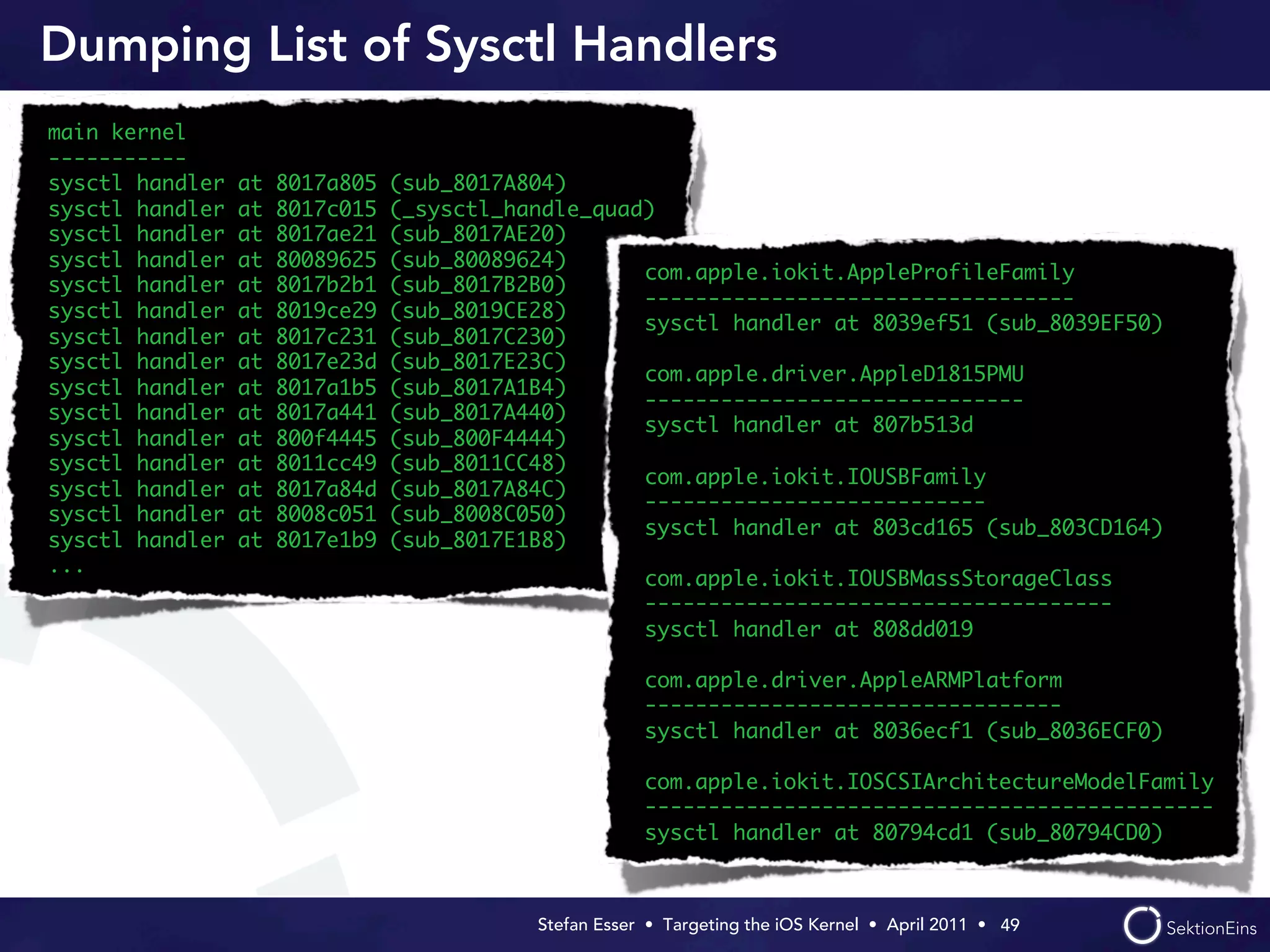
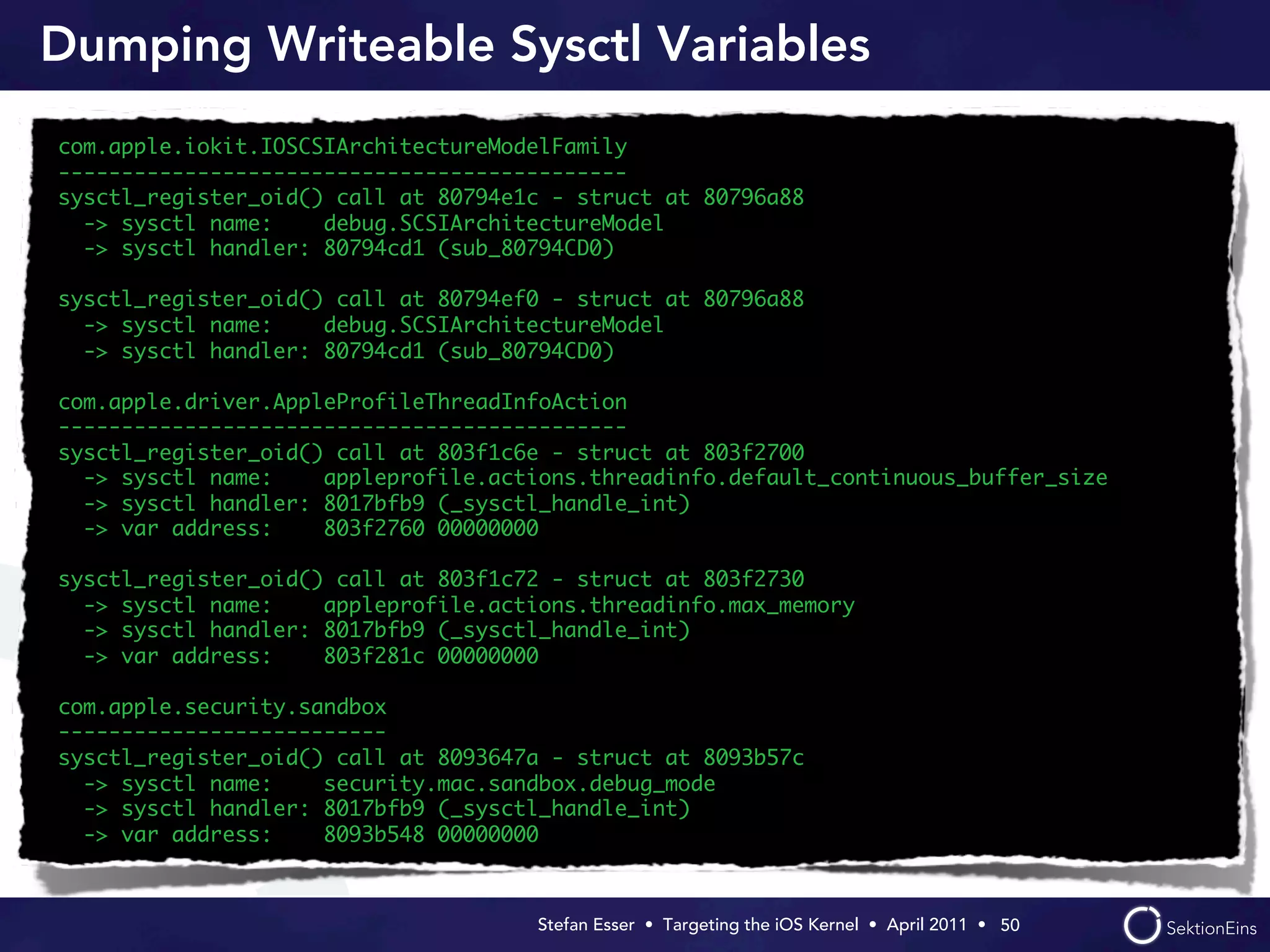
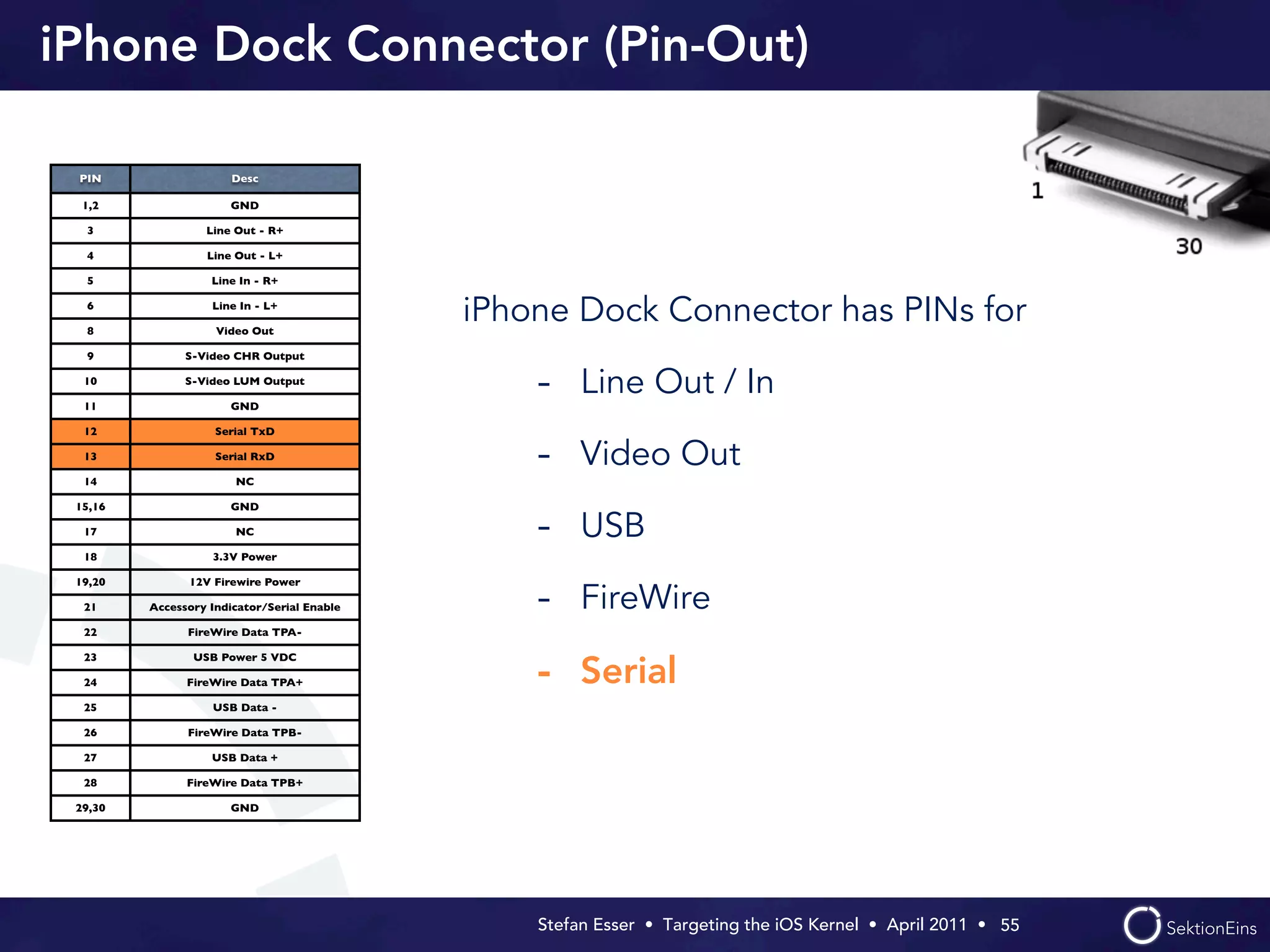
The document outlines a presentation by Stefan Esser on targeting the iOS kernel, focusing on its vulnerabilities, tools for analyzing the kernelcache, and methods for symbol extraction. It discusses the limitations in iOS security, the challenges in finding kernel vulnerabilities, and how to analyze kernel extensions and classes for further insights. The session emphasizes the lack of available source code for iOS and the importance of using tools like IDA and zynamic's bindiff for effective analysis.