Red Clay Renovations Security Controls Baseline
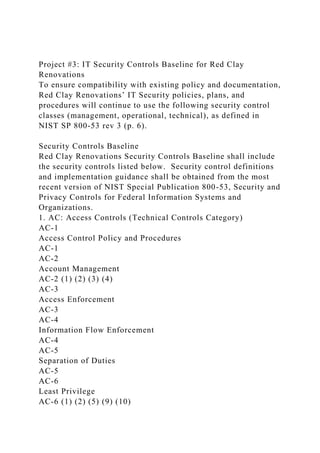
- 1. Project #3: IT Security Controls Baseline for Red Clay Renovations To ensure compatibility with existing policy and documentation, Red Clay Renovations’ IT Security policies, plans, and procedures will continue to use the following security control classes (management, operational, technical), as defined in NIST SP 800-53 rev 3 (p. 6). Security Controls Baseline Red Clay Renovations Security Controls Baseline shall include the security controls listed below. Security control definitions and implementation guidance shall be obtained from the most recent version of NIST Special Publication 800-53, Security and Privacy Controls for Federal Information Systems and Organizations. 1. AC: Access Controls (Technical Controls Category) AC-1 Access Control Policy and Procedures AC-1 AC-2 Account Management AC-2 (1) (2) (3) (4) AC-3 Access Enforcement AC-3 AC-4 Information Flow Enforcement AC-4 AC-5 Separation of Duties AC-5 AC-6 Least Privilege AC-6 (1) (2) (5) (9) (10)
- 2. AC-7 Unsuccessful Logon Attempts AC-7 AC-8 System Use Notification AC-8 AC-11 Session Lock AC-11 (1) AC-12 Session Termination AC-12 AC-14 Permitted Actions without Identification or Authentication AC-14 AC-17 Remote Access AC-17 (1) (2) (3) (4) AC-18 Wireless Access AC-18 (1) AC-19 Access Control for Mobile Devices AC-19 (5) AC-20 Use of External Information Systems AC-20 (1) (2) AC-21 Information Sharing AC-21 AC-22 Publicly Accessible Content AC-22 2. AT: Awareness and Training (Operational Controls Category) AT-1 Security Awareness and Training Policy and Procedures
- 3. AT-1 AT-2 Security Awareness Training AT-2 (2) AT-3 Role-Based Security Training AT-3 AT-4 Security Training Records AT-4 3. AU: Audit and Accountability (Technical Controls Category) AU-1 Audit and Accountability Policy and Procedures AU-1 AU-2 Audit Events AU-2 (3) AU-3 Content of Audit Records AU-3 (1) AU-4 Audit Storage Capacity AU-4 AU-5 Response to Audit Processing Failures AU-5 AU-6 Audit Review, Analysis, and Reporting AU-6 (1) (3) AU-7 Audit Reduction and Report Generation AU-7 (1) AU-8 Time Stamps AU-8 (1)
- 4. AU-9 Protection of Audit Information AU-9 (4) AU-10 Non-repudiation Not Selected AU-11 Audit Record Retention AU-11 AU-12 Audit Generation AU-12 4. CA: Security Assessment and Authorization (Management Controls Category) CA-1 Security Assessment and Authorization Policies and Procedures CA-1 CA-2 Security Assessments CA-2 (1) CA-3 System Interconnections CA-3 (5) CA-5 Plan of Action and Milestones CA-5 CA-6 Security Authorization CA-6 CA-7 Continuous Monitoring CA-7 (1) CA-9 Internal System Connections CA-9
- 5. 5. CM: Configuration Management (Operational Controls Category) CM-1 Configuration Management Policy and Procedures CM-1 CM-2 Baseline Configuration CM-2 (1) (3) (7) CM-3 Configuration Change Control CM-3 (2) CM-4 Security Impact Analysis CM-4 CM-5 Access Restrictions for Change CM-5 CM-6 Configuration Settings CM-6 CM-7 Least Functionality CM-7 (1) (2) (4) CM-8 Information System Component Inventory CM-8 (1) (3) (5) CM-9 Configuration Management Plan CM-9 CM-10 Software Usage Restrictions CM-10 CM-11 User-Installed Software CM-11
- 6. 6. Contingency Planning (Operational Controls Category) CP-1 Contingency Planning Policy and Procedures CP-1 CP-2 Contingency Plan CP-2 (1) (3) (8) CP-3 Contingency Training CP-3 CP-4 Contingency Plan Testing CP-4 (1) CP-5 Withdrawn --- CP-6 Alternate Storage Site CP-6 (1) (3) CP-7 Alternate Processing Site CP-7 (1) (2) (3) CP-8 Telecommunications Services CP-8 (1) (2) CP-9 Information System Backup CP-9 (1) CP-10 Information System Recovery and Reconstitution CP-10 (2) 7. IA: Identification and Authentication (Technical Controls Category)
- 7. IA-1 Identification and Authentication Policy and Procedures IA-1 IA-2 Identification and Authentication (Organizational Users) IA-2 (1) (2) (3) (8) (11) (12) IA-3 Device Identification and Authentication IA-3 IA-4 Identifier Management IA-4 IA-5 Authenticator Management IA-5 (1) (2) (3) (11) IA-6 Authenticator Feedback IA-6 IA-7 Cryptographic Module Authentication IA-7 IA-8 Identification and Authentication (Non-Organizational Users) IA-8 (1) (2) (3) (4) 8. IR: Incident Response (Operational Controls Category) IR-1 Incident Response Policy and Procedures IR-1 IR-2 Incident Response Training IR-2 IR-3 Incident Response Testing IR-3 (2) IR-4
- 8. Incident Handling IR-4 (1) IR-5 Incident Monitoring IR-5 IR-6 Incident Reporting IR-6 (1) IR-7 Incident Response Assistance IR-7 (1) IR-8 Incident Response Plan IR-8 9. MA: Maintenance (Operational Controls Category) MA-1 System Maintenance Policy and Procedures MA-1 MA-2 Controlled Maintenance MA-2 MA-3 Maintenance Tools MA-3 (1) (2) MA-4 Nonlocal Maintenance MA-4 (2) MA-5 Maintenance Personnel MA-5 10. MP: Media Protection (Operational Controls Category)
- 9. MP-1 Media Protection Policy and Procedures MP-1 MP-2 Media Access MP-2 MP-3 Media Marking MP-3 MP-4 Media Storage MP-4 MP-5 Media Transport MP-5 (4) MP-6 Media Sanitization MP-6 MP-7 Media Use MP-7 (1) 11. PE: Physical and Environmental Protection (Operational Controls Category) PE-1 Physical and Environmental Protection Policy and Procedures PE-1 PE-2 Physical Access Authorizations PE-2 PE-3 Physical Access Control PE-3 PE-4 Access Control for Transmission Medium PE-4
- 10. PE-5 Access Control for Output Devices PE-5 PE-6 Monitoring Physical Access PE-6 (1) PE-8 Visitor Access Records PE-8 PE-9 Power Equipment and Cabling PE-9 PE-10 Emergency Shutoff PE-10 PE-11 Emergency Power PE-11 PE-12 Emergency Lighting PE-12 PE-13 Fire Protection PE-13 (3) PE-14 Temperature and Humidity Controls PE-14 PE-15 Water Damage Protection PE-15 PE-16 Delivery and Removal PE-16 PE-17 Alternate Work Site PE-17
- 11. 12. PL: Planning (Management Controls Category) PL-1 Security Planning Policy and Procedures PL-1 PL-2 System Security Plan PL-2 (3) PL-4 Rules of Behavior PL-4 (1) PL-8 Information Security Architecture PL-8 13. PS: Personnel Security (Operational Controls Category) PS-1 Personnel Security Policy and Procedures PS-1 PS-2 Position Risk Designation PS-2 PS-3 Personnel Screening PS-3 PS-4 Personnel Termination PS-4 PS-5 Personnel Transfer PS-5 PS-6 Access Agreements PS-6 PS-7 Third-Party Personnel Security
- 12. PS-7 PS-8 Personnel Sanctions PS-8 14. RA: Risk Assessment (Management Controls Category) RA-1 Risk Assessment Policy and Procedures RA-1 RA-2 Security Categorization RA-2 RA-3 Risk Assessment RA-3 RA-5 Vulnerability Scanning RA-5 (1) (2) (5) 15. SA: System and Services Acquisition (Management Controls Category) SA-1 System and Services Acquisition Policy and Procedures SA-1 SA-2 Allocation of Resources SA-2 SA-3 System Development Life Cycle SA-3 SA-4 Acquisition Process SA-4 (1) (2) (9) (10) SA-5 Information System Documentation
- 13. SA-5 SA-8 Security Engineering Principles SA-8 SA-9 External Information System Services SA-9 (2) SA-10 Developer Configuration Management SA-10 SA-11 Developer Security Testing and Evaluation SA-11 16. SC: System and Communications Protection (Technical Controls Category) SC-1 System and Communications Protection Policy and Procedures SC-1 SC-5 Denial of Service Protection SC-5 SC-7 Boundary Protection SC-7 SC-8 Transmission Confidentiality SC-8 SC-18 Mobile Code SC-18 SC-19 Voice Over Internet Protocol SC-19 SC-28 Protection of Information at Rest
- 14. SC-28 SC-39 Process Isolation SC-39 17. SI: System and Information Integrity (Operational Controls Category) SI-1 System and Information Integrity Policy and Procedures SI-1 SI-2 Flaw Remediation SI-2 (2) SI-3 Malicious Code Protection SI-3 (1) (2) SI-4 Information System Monitoring SI-4 (2) (4) (5) SI-5 Security Alerts, Advisories, and Directives SI-5 SI-7 Software, Firmware, and Information Integrity SI-7 (1) (7) SI-8 Spam Protection SI-8 (1) (2) SI-10 Information Input Validation SI-10 SI-11 Error Handling SI-11 SI-12 Information Handling and Retention
- 15. SI-12 SI-16 Memory Protection SI-16 18. PM: Program Management (Management Controls Family) PM-1 Information Security Program Plan all PM-2 Senior Information Security Officer all PM-3 Information Security Resources all PM-4 Plan of Action and Milestones Process all PM-5 Information System Inventory all PM-6 Information Security Measures of Performance all PM-7 Enterprise Architecture all PM-8 Critical Infrastructure Plan all PM-9 Risk Management Strategy all PM-10
- 16. Security Authorization Process all PM-11 Mission/Business Process Definition all PM-12 Insider Threat Program all PM-13 Information Security Workforce all PM-14 Testing, Training, and Monitoring all PM-15 Contacts with Security Groups and Associations all PM-16 Threat Awareness Program all CSIA 413: Cybersecurity Policy, Plans, and ProgramsProject #3: System Security Plan WARNING: YOU MUST PARAPHRASE INFORMATION USED IN THIS ASSIGNMENT. Copy/Paste is only allowed for the names and designators of security controls and/or control families. All other information used in this assignment must be rewritten into your own words. Company Background & Operating Environment Red Clay Renovations is an internationally recognized, awarding winning firm that specializes in the renovation and rehabilitation of residential buildings and dwellings. The company specializes in updating homes using “smart home” and
- 17. “Internet of Things” technologies while maintaining period correct architectural characteristics. Please refer to the company profile (file posted in Week 1 > Content > CSIA 413 Red Clay Renovations Company Profile.docx) for background information and information about the company’s operating environment. In addition to the information from the company profile, you should: · Use the Wilmington Headquarters (staff) office as the target for the System Security Plan · Use Verizon FiOS as the Internet Services Provider (see http://www.verizonenterprise.com/terms/us/products/internet/sla / ) Policy Issue & Plan of Action A recent risk assessment highlighted the need to formalize the security measures required to protect information, information systems, and the information infrastructures for the company’s headquarters and field offices. This requirement has been incorporated into the company’s risk management plan and the company’s CISO has been tasked with developing, documenting, and implementing the required security measures. The IT Governance board also has a role to play since it must review and approve all changes which affect IT systems under its purview. The CISO has proposed a plan of action which includes developing system security plans using guidance from NIST SP- 800-18 Guide for Developing Security Plans for Federal Information Systems. The IT Governance board, after reviewing the CISO’s proposed plan of action, voted and accepted this recommendation. In its discussions prior to the vote, the CISO explained why the best practices information for security plans from NIST SP 800-18 was suitable for the company’s use. The board also accepted the CISO’s recommendation for creating a single System Security Plan for a General Support System since, in the CISO’s professional judgement, this type of plan would best meet the “formalization” requirement from the company’s
- 18. recently adopted risk management strategy. Your Task Assignment As a staff member supporting the CISO, you have been asked to research and then draft the required system security plan for a General Support System. In your research so far, you have learned that: · A general support system is defined as “an interconnected set of information resources under the same direct management control that shares common functionality.” (See NIST SP 800- 18) · The Chief of Staff for the company is the designated system owner for the IT support systems in the Wilmington, DC headquarters offices. · The system boundaries for the Wilmington, DE office’s General Support System have already been documented in the company’s enterprise architecture (see the case study). · The security controls required for the Wilmington, DE office’s IT systems have been documented in a security controls baseline (see the controls baseline attached to this assignment). Section 13 of this document will take you the most time to research and write because it requires the most original writing on your part. You must write a description for EACH CONTROL CATEGORY (managerial, operational, and technical). Then, paste in the table from the Security Controls Baseline. THEN, write a descriptive paragraph explaining how these specific controls will work together to protect the Red Clay Renovations IT Infrastructure for the Wilmington, DE Offices (Headquarters). URLs for Recommended Resources For This Project Title Type Link
- 19. Service Level Agreement (SLA) Internet Dedicated Services | Verizon Enterprise Web Page http://www.verizonenterprise.com/terms/us/products/internet/sla / NIST SP 800-100 Information Security Handbook: A Guide for Managers PDF https://doi.org/10.6028/NIST.SP.800-100 NIST SP 800-12 R1: An Introduction to Information Security PDF https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.8 00-12r1.pdf NIST SP 800-18: Guide for Developing Security Plans for Federal Information Systems PDF http://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublicatio n800-18r1.pdf NIST SP 800-53 Security and Privacy Controls for Federal Information Systems and Organizations PDF http://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.8 00-53r4.pdf Research: 1. Review the information provided in the case study and in this assignment, especially the information about the headquarters and field offices and the IT systems and networks used in their day to day business affairs. 2. Review NIST’s guidance for developing a System Security Plan for a general support IT System. This information is presented in a. NIST SP 800-12 R1 https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.8 00-12r1.pdf Pay special attention to Chapter 2 and Section 5.4
- 20. b. NIST SP 800-18. http://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublicatio n800-18r1.pdf Pay special attention to the Sample Information System Security Plan template provided in Appendix A. 3. Review the definitions for IT Security control families as documented in NIST SP 800-12 R1 Chapter 10. https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.8 00-12r1.pdf 4. Review the definitions for individual controls as listed in Appendix F Security Control Catalog in NIST SP 800-53 Security and Privacy Controls for Federal Information Systems and Organizations. http://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.8 00-53r4.pdfYou should focus on those controls listed in the security controls baseline provided with this assignment. Write: 1. Use the following guidance to complete the System Security Plan using the template from Appendix A of NIST SP 800-18. a. Sections 1 through 10 will contain information provided in the assigned case study. You may need to “interpret” that information when writing the descriptions. “Fill in the blanks” for information about the company or its managers which is not provided in the case study, i.e. names, email addresses, phone numbers, etc.). Make sure that your fictional information is consistent with information provided in the case study (name of company, locations, etc.). b. Section 11 should contain information about the Wilmington, DE headquarters office’s Internet connection Do not include the table. Use the business Internet Services Provider listed at the top of this assignment file. Describe the system interconnection type in this section and service level agreement. c. Section 12 should contain information derived from the case study. You will need to identify the types of information processed in the headquarters offices and then list the laws and regulations which apply. For example, if the case study
- 21. company processes or stores Protected Health Information, then this section must include information about HIPAA. If the company processes or stores credit card payment information, then this section must include information about the PCI-DSS requirements. For the Headquarters Offices you also have financial information which may be covered by regulations issued by the Securities and Exchange Commission. d. Section 13 of the SSP will take the most research and writing time. You MUST provide the required descriptive paragraphs for the three categories AND the explanations as to how the security controls within the control families will be used to secure the IT infrastructure. You MUST use the selected security control families and security controls as provided security controls baseline. i. Create 3 sub sections (13.1 Management Controls, 13.2 Operational Controls, and 13.3 Technical Controls). You must provide a description for each category (see the definitions provided in Annex 11.B Minimum Security Controls in NIST SP 800-100 Information Security Handbook: A Guide for Managers). ii. Using the information provided in the security controls baseline, place the required control families and controls under the correct sub section. iii. Use the exact names and designators for the security control families and individual security controls. BUT, you MUST paraphrase any and all descriptions. Do NOT cut and paste from NIST documents. e. Section 14: use the due date for this assignment as the plan complete date. f. Section 15: leave the approval date blank. You will not have any other text in this section (since the plan is not yet approved). 2. Use a professional format for your System Security Plan. Your document should be consistently formatted throughout and easy to read.
- 22. 3. You must include a cover page with the assignment title, your name, and the due date. Your reference list must be on a separate page at the end of your file. These pages do not count towards the assignment’s page count. 4. Common phrases do not require citations. If there is doubt as to whether or not information requires attribution, provide a footnote with publication information or use APA format citations and references. 5. You are expected to write grammatically correct English in every assignment that you submit for grading. Do not turn in any work without (a) using spell check, (b) using grammar check, (c) verifying that your punctuation is correct and (d) reviewing your work for correct word usage and correctly structured sentences and paragraphs. 6. Consult the grading rubric for specific content and formatting requirements for this assignment. Submit For Grading Submit your System Security Plan in MS Word format (.docx or .doc file) for grading using your assignment folder. (Attach the file.) Copyright ©2019 by University of Maryland University College. All Rights Reserved Information System Security Plan 1. Information System Name/Title: • Unique identifier and name given to the system. [use information from the case study] 2. Information System Categorization: • Identify the appropriate system categorization [use the information from the case study]. 3. Information System Owner:
- 23. • Name, title, agency, address, email address, and phone number of person who owns the system. [Use the field office manager] 4. Authorizing Official: • Name, title, agency, address, email address, and phone number of the senior management official designated as the authorizing official. [Use the company’s Chief Information Officer.] 5. Other Designated Contacts: • List other key personnel, if applicable; include their title, address, email address, and phone number. [include the CISO, the ISSO, and other individuals from the case study, if appropriate] 6. Assignment of Security Responsibility: • Name, title, address, email address, and phone number of person who is responsible for the security of the system. [use the case study information] 7. Information System Operational Status: • Indicate the operational status of the system. If more than one status is selected, list which part of the system is covered under each status. [Use the case study information.] 8.0 Information System Type: • Indicate if the system is a major application or a general support system. If the system contains minor applications, list them in Section 9. General System Description/Purpose. [use the case study information] 9.0 General System Description/Purpose • Describe the function or purpose of the system and the information processes. [use the case study information] 10. System Environment • Provide a general description of the technical system. Include
- 24. the primary hardware, software, and communications equipment. [use the case study information and diagrams. Add brand names, equipment types as required (if not provided in the case study)] 11. System Interconnections/Information Sharing • List interconnected systems and system identifiers (if appropriate), provide the system name, owning or providing organization, system type (major application or general support system) … add a fictional date of agreement to interconnect, and the name of the authorizing official. 12. Related Laws/Regulations/Policies • List any laws or regulations that establish specific requirements for the confidentiality, integrity, or availability of the data in the system. 13. Minimum Security Controls Use the security controls baseline as provided for this assignment. Include descriptive paragraphs for each section. Cut and paste the tables from the provided security controls baseline to add the individual security controls under each section. Use the sections and sub-sections as listed below. 13.1 Management Controls [provide a descriptive paragraph – DO NOT COPY TEXT FROM OTHER DOCUMENTS] 13.1.1 [first control family] [provide a descriptive paragraph – DO NOT COPY TEXT FROM OTHER DOCUMENTS]
- 25. 13.1.2 [second control family] ………… 13.2 Operational Controls [provide a descriptive paragraph – DO NOT COPY TEXT FROM OTHER DOCUMENTS] 13.2.1 [first control family] 13.2.2 [second control family] ………….. 13.3 Technical Controls [provide a descriptive paragraph – DO NOT COPY TEXT FROM OTHER DOCUMENTS] 13.3.1 [ first control family] 13.3.2 [ second control family] ………… Example: 14. Information System Security Plan Completion Date: _____________________ • Enter the completion date of the plan. 15. Information System Security Plan Approval Date: _______________________
- 26. • Enter the date the system security plan was approved and indicate if the approval documentation is attached or on file. 2