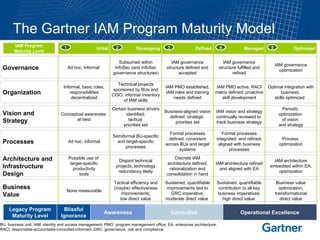
The document describes the Gartner Identity and Access Management (IAM) Program Maturity Model which outlines 5 levels of maturity for an organization's IAM program:
1. Initial - Ad hoc processes with little awareness or value.
2. Defined - Certain business drivers identified and tactical priorities set with informal roles and processes.
3. Managed - IAM vision and strategy defined and aligned with business, formal processes and governance established.
4. Operational Excellence - IAM architecture refined, processes integrated and contribution to business imperatives is high.
5. Transformational - IAM vision, strategy, processes, architecture and governance optimized for maximum business value.