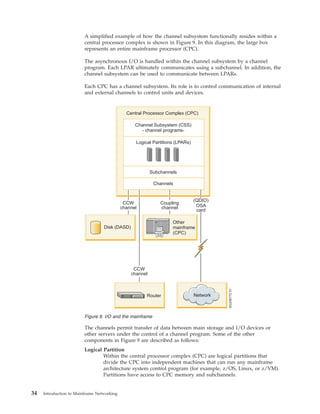
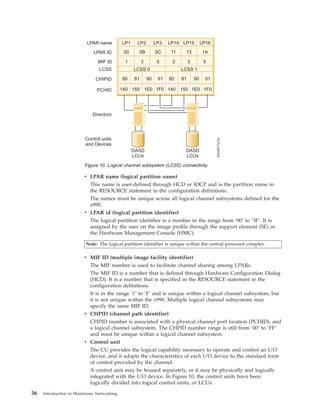
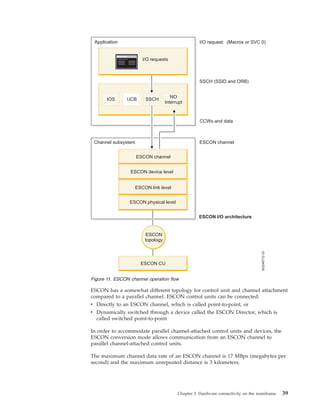
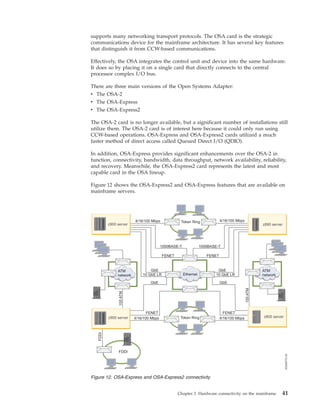
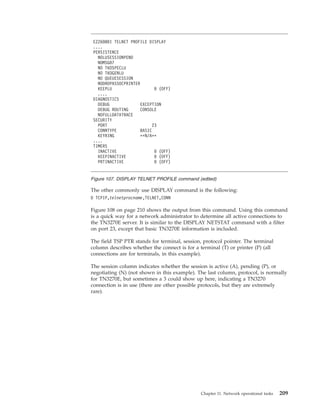
The document serves as a comprehensive guide to networking on the z/os platform, outlining essential skills and knowledge necessary for systems personnel to utilize mainframe communication facilities. It covers networking principles, hardware, and software components, aiming to enhance understanding for professionals familiar with non-mainframe systems. Additionally, it encourages feedback on the publication and provides resources for further assistance.