Xsl Transformations(Xslt)1.0
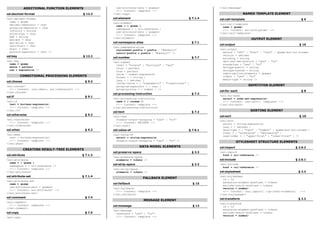
- 1. ADDITIONAL FUNCTION ELEMENTS use-attribute-sets = qnames> </xsl:message> <!-- Content: template --> NAMED TEMPLATE ELEMENT xsl:decimal-format § 12.3 </xsl:copy> xsl:element § 7.1.4 xsl:call-template §6 <xsl:decimal-format name = qname <xsl:element <xsl:call-template decimal-separator = char name = { qname } name = qname> grouping-separator = char namespace = { uri-reference } <!-- Content: xsl:with-param* --> infinity = string use-attribute-sets = qnames> </xsl:call-template> minus-sign = char <!-- Content: template --> NaN = string OUTPUT ELEMENT </xsl:element> percent = char xsl:namespace-alias § 7.1 per-mille = char xsl:output § 16 zero-digit = char <xsl:namespace-alias digit = char <xsl:output stylesheet-prefix = prefix | quot;#defaultquot; pattern-separator = char /> method = quot;xmlquot; | quot;htmlquot; | quot;textquot; | qname-but-not-ncname result-prefix = prefix | quot;#defaultquot; /> version = nmtoken xsl:key § 12.2 xsl:number § 7.7 encoding = string <xsl:key omit-xml-declaration = quot;yesquot; | quot;noquot; <xsl:number name = qname standalone = quot;yesquot; | quot;noquot; level = quot;singlequot; | quot;multiplequot; | quot;anyquot; match = pattern doctype-public = string count = pattern use = expression /> doctype-system = string from = pattern cdata-section-elements = qnames value = number-expression CONDITIONAL PROCESSING ELEMENTS indent = quot;yesquot; | quot;noquot; format = { string } media-type = string /> lang = { nmtoken } xsl:choose § 9.2 letter-value = { quot;alphabeticquot; | quot;traditionalquot; } REPETITON ELEMENT <xsl:choose> grouping-separator = { char } <!-- Content: (xsl:when+, xsl:otherwise?) --> grouping-size = { number } /> xsl:for-each §8 </xsl:choose> xsl:processing-instruction § 7.3 <xsl:for-each xsl:if § 9.1 <xsl:processing-instruction select = node-set-expression> <xsl:if name = { ncname }> <!-- Content: (xsl:sort*, template) --> test = boolean-expression> <!-- Content: template --> </xsl:for-each> <!-- Content: template --> </xsl:processing-instruction> SORTING ELEMENT </xsl:if> xsl:text § 7.2 xsl:otherwise § 9.2 xsl:sort § 10 <xsl:text <xsl:otherwise> disable-output-escaping = quot;yesquot; | quot;noquot;> <xsl:sort <!-- Content: template --> <!-- Content: #PCDATA --> select = string-expression </xsl:otherwise> </xsl:text> lang = { nmtoken } xsl:when § 9.2 xsl:value-of § 7.6.1 data-type = { quot;textquot; | quot;numberquot; | qname-but-not-ncname } order = { quot;ascendingquot; | quot;descendingquot; } <xsl:when <xsl:value-of case-order = { quot;upper-firstquot; | quot;lower-firstquot; } /> test = boolean-expression> select = string-expression <!-- Content: template --> STYLESHEET STRUCTURE ELEMENTS disable-output-escaping = quot;yesquot; | quot;noquot; /> </xsl:when> DATA MODEL ELEMENTS xsl:import § 2.6.2 CREATING RESULT-TREE ELEMENTS xsl:preserve-space § 3.3 <xsl:import xsl:attribute § 7.1.3 href = uri-reference /> <xsl:preserve-space xsl:include § 2.6.1 <xsl:attribute elements = tokens /> name = { qname } xsl:strip-space § 3.3 <xsl:include namespace = { uri-reference }> href = uri-reference /> <!-- Content: template --> <xsl:strip-space xsl:stylesheet § 2.2 </xsl:attribute> elements = tokens /> xsl:attribute-set § 7.1.4 <xsl:stylesheet FALLBACK ELEMENT id = id <xsl:attribute-set extension-element-prefixes = tokens xsl:fallback § 15 name = qname exclude-result-prefixes = tokens use-attribute-sets = qnames> <xsl:fallback> version = number> <!-- Content: xsl:attribute* --> <!-- Content: template --> <!-- Content: (xsl:import*, top-level-elements) --> </xsl:attribute-set> </xsl:fallback> </xsl:stylesheet> xsl:comment § 7.4 xsl:transform § 2.2 MESSAGE ELEMENT <xsl:comment> <xsl:transform xsl:message § 13 <!-- Content: template --> id = id </xsl:comment> extension-element-prefixes = tokens <xsl:message xsl:copy § 7.5 exclude-result-prefixes = tokens terminate = quot;yesquot; | quot;noquot;> version = number> <!-- Content: template --> <xsl:copy
- 2. string format-number(number, string, string?) § 12.3 <!-- Content: (xsl:import*, top-level-elements) --> </xsl:transform> The format-number function converts its first argument to a string using the TEMPLATE RULE ELEMENTS format pattern string specified by the second argument and the decimal- format named by the third argument, or the default decimal-format, if there xsl:apply-imports § 5.6 is no third argument. The format pattern string is in the syntax specified by the JDK 1.1 DecimalFormat class. <xsl:apply-imports /> xsl:apply-templates § 5.4 boolean function-available(string) § 15 <xsl:apply-templates The function-available function returns true if and only if the expanded- Quick Reference select = node-set-expression name is the name of a function in the function library. mode = qname> string generate-id(node-set?) § 12.4 <!-- Content: (xsl:sort | xsl:with-param)* --> </xsl:apply-templates> The generate-id function returns a string that uniquely identifies the node in xsl:template § 5.3 the argument node-set that is first in document order. XSL Transformations node-set key(string, object) § 12.2 <xsl:template match = pattern The key function does for keys what the id function does for IDs. name = qname (XSLT) priority = number object system-property(string) § 12.4 mode = qname> The system-property function returns an object representing the value of the Version 1.0 <!-- Content: (xsl:param*, template) --> </xsl:template> system property identified by the name. If there is no such system property, the empty string should be returned. VARIABLE/PARAMETER ELEMENTS string unparsed-entity-uri(string) § 12.4 W3C Recommendation xsl:copy-of § 11.3 The unparsed-entity-uri returns the URI of the unparsed entity with the 16 November 1999 <xsl:copy-of specified name in the same document as the context node. select = expression /> NOTATION xsl:param § 11 http://www.w3.org/TR/xslt/ | separator for alternative values <xsl:param , separator for consecutive values name = qname select = expression> ? zero-or-more repetitions <!-- Content: template --> * zero-or-more repetitions Table of Contents: </xsl:param> + one-or-more repetitions xsl:variable § 11 #PCDATA Elements parsable character data boolean-expression expression returning a Boolean · Additional Function Elements <xsl:variable char represents a single character · Conditional Processing Elements name = qname expression XPath production expression select = expression> · Creating Result-Tree Elements <!-- Content: template --> id XML name used as unique identifier within · Data Model Elements </xsl:variable> the document, special attribute type · Fallback Element xsl:with-param § 11.6 ncname non-colon-name - XML Name without · Message Element colon (see also qname) <xsl:with-param · Named Template Element nmtoken name token – mixture of XML name name = qname · Output Element characters select = expression> · Repetition Element <!-- Content: template --> node-set-expression expression returning a node-set · Sorting Element </xsl:with-param> number represents a number · Stylesheet Structure Elements number-expression expression retuning a number FUNCTIONS · Template Rule Elements pattern XPath pattern · Variable/Parameter Elements node-set current() § 12.4 prefix XML namespace prefix qname qualified name – XML name with local part The current function returns a node-set that has the current node as its only Functions and optional XML namespace prefix, member. separated by a colon note-set document(object, node-set?) § 12.1 string represents a string string-expression expression returning a string The document function allows access to XML documents other than the token attribute type main source document. uri-reference Universal Resource Identifier reference deepX Ltd. boolean element-available(string) § 15 XML name XML name is a string beginning with a The element-available function returns true if and only if the expanded-name letter or one of a few punctuation characters, Dublin, Ireland is the name of an instruction. If the expanded-name has a namespace URI and continuing with letters, digits, hyphens, equal to the XSLT namespace URI, then it refers to an element defined by underscores, colons, or full stops, together info@deepX.com XSLT. known as name characters. http://www.deepX.com/
