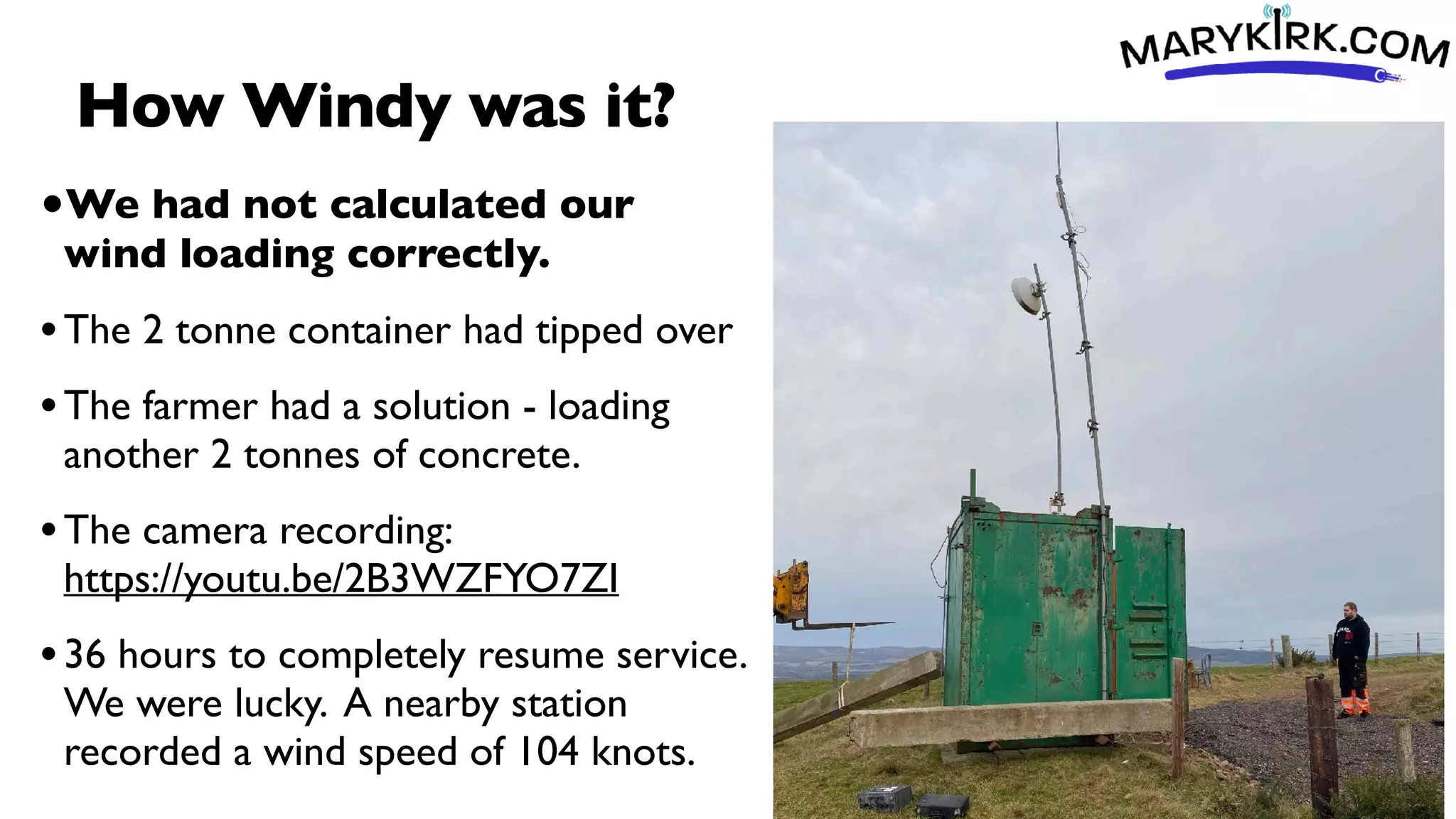
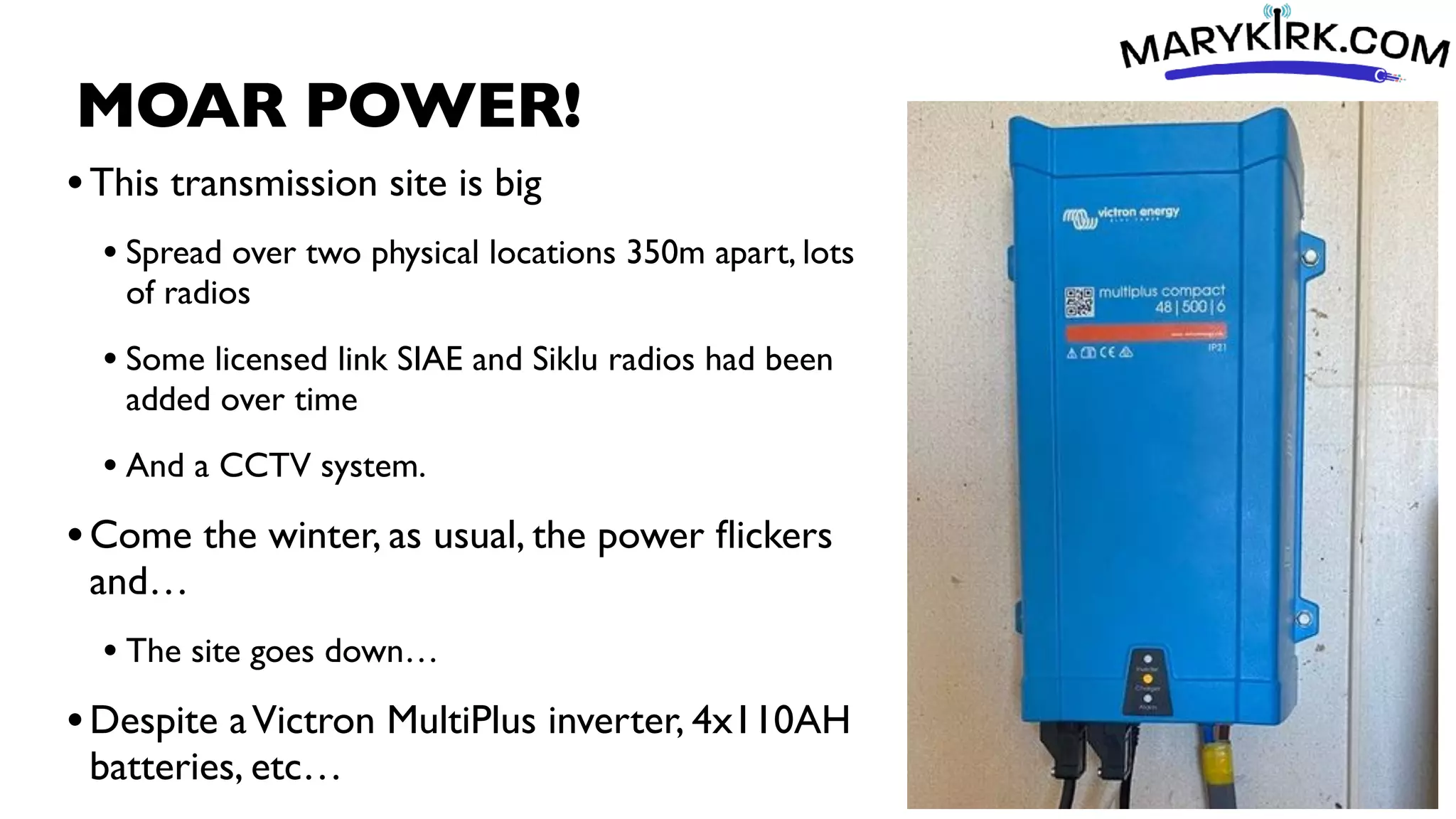
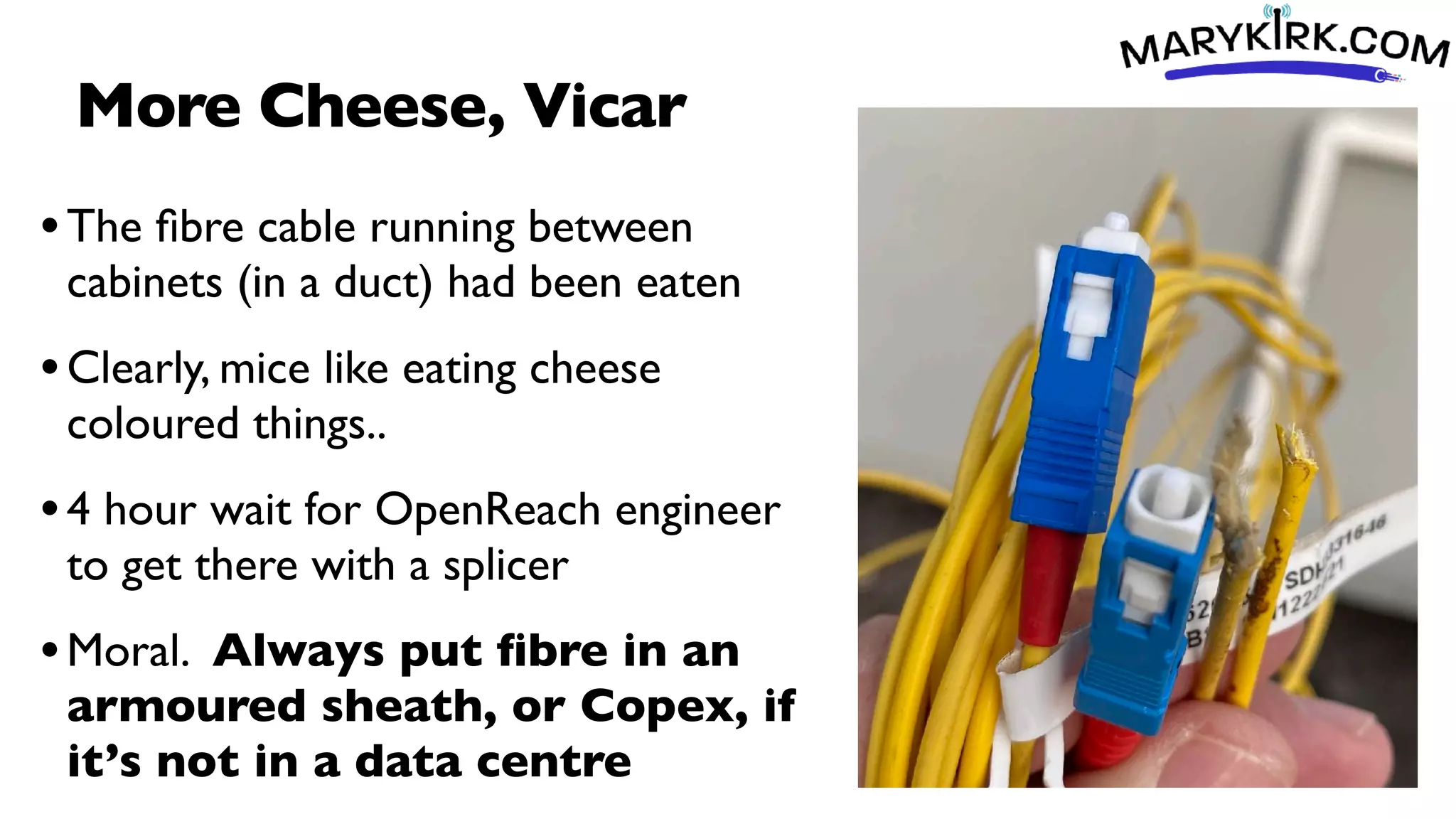
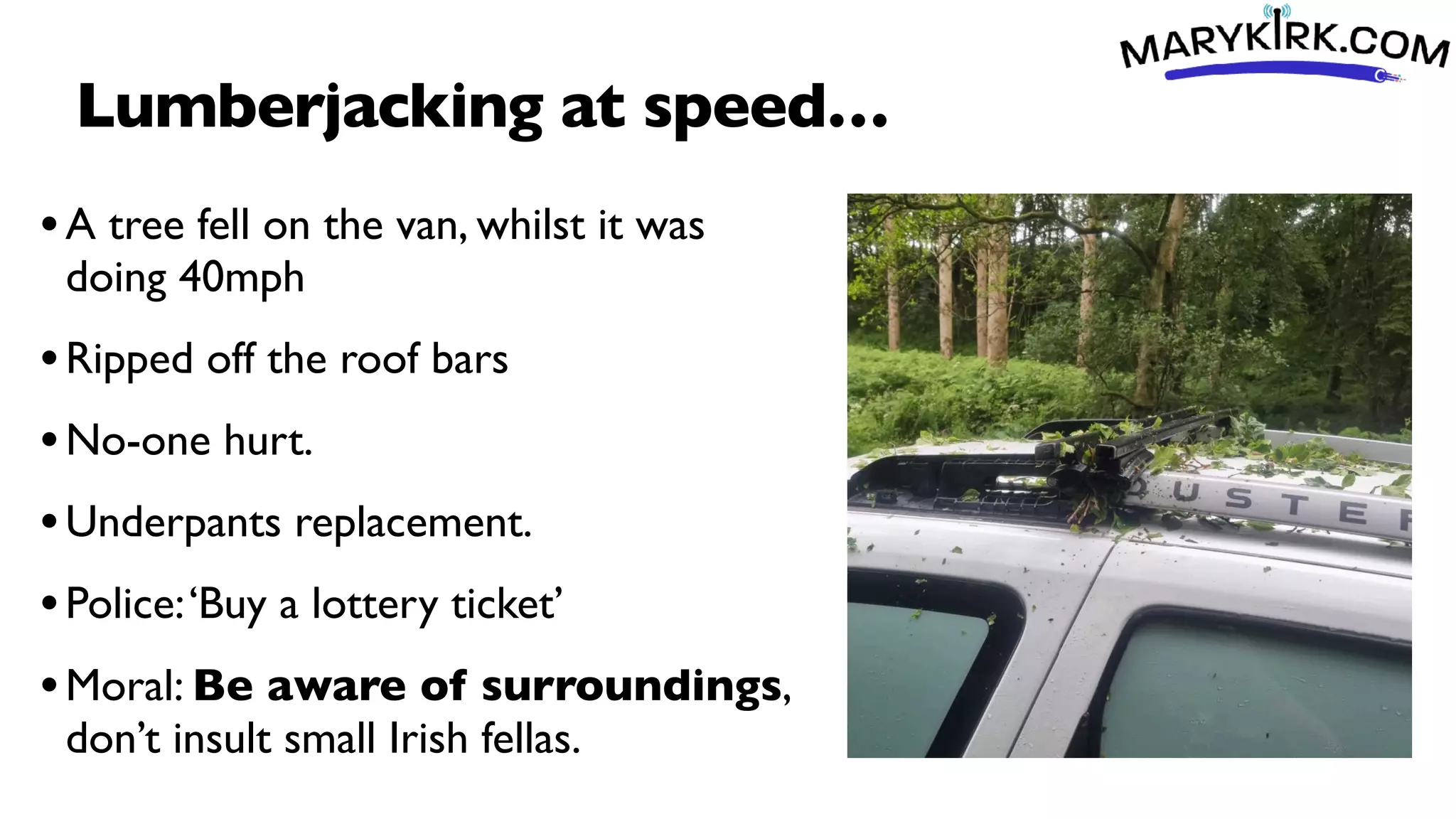
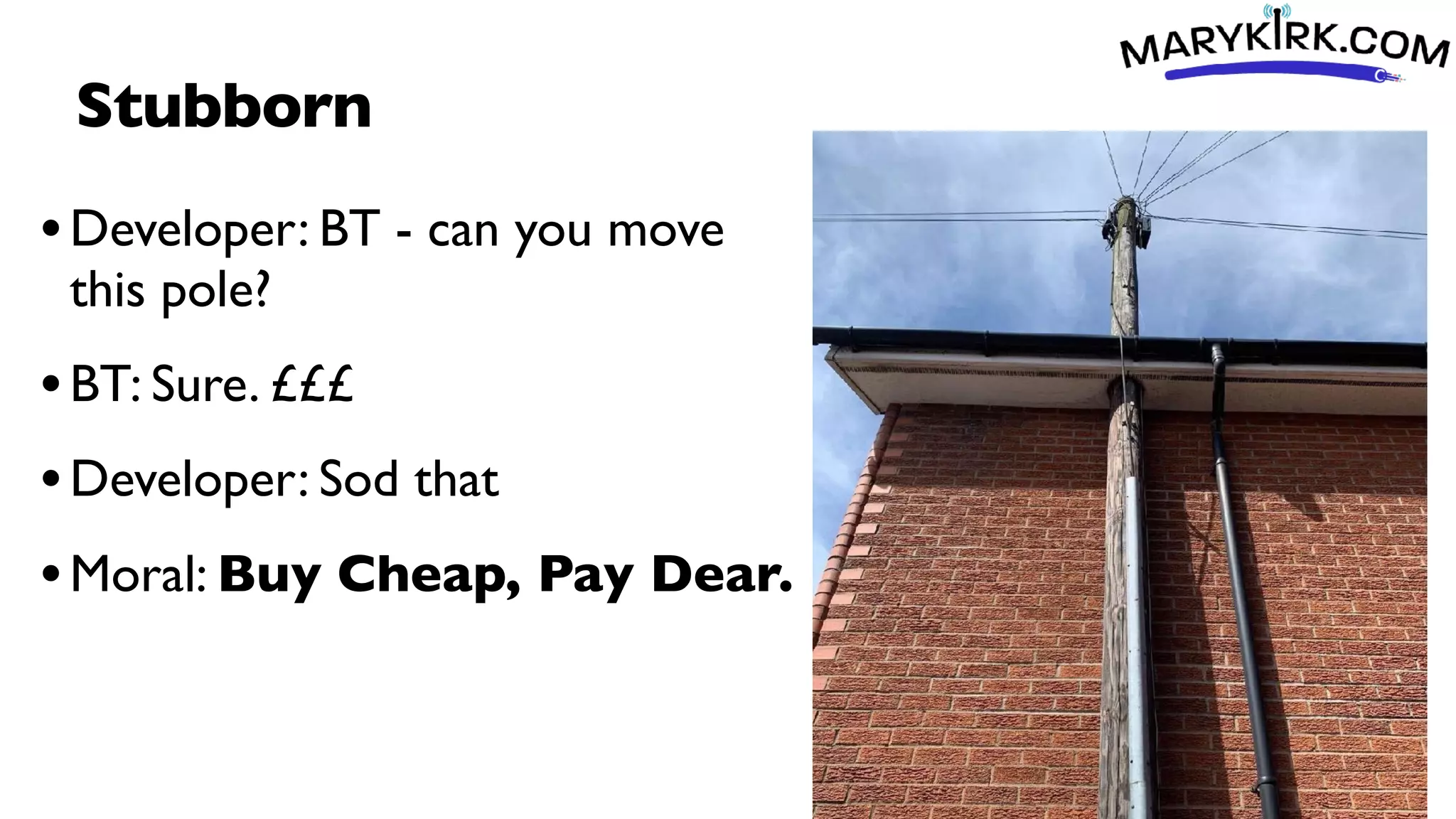
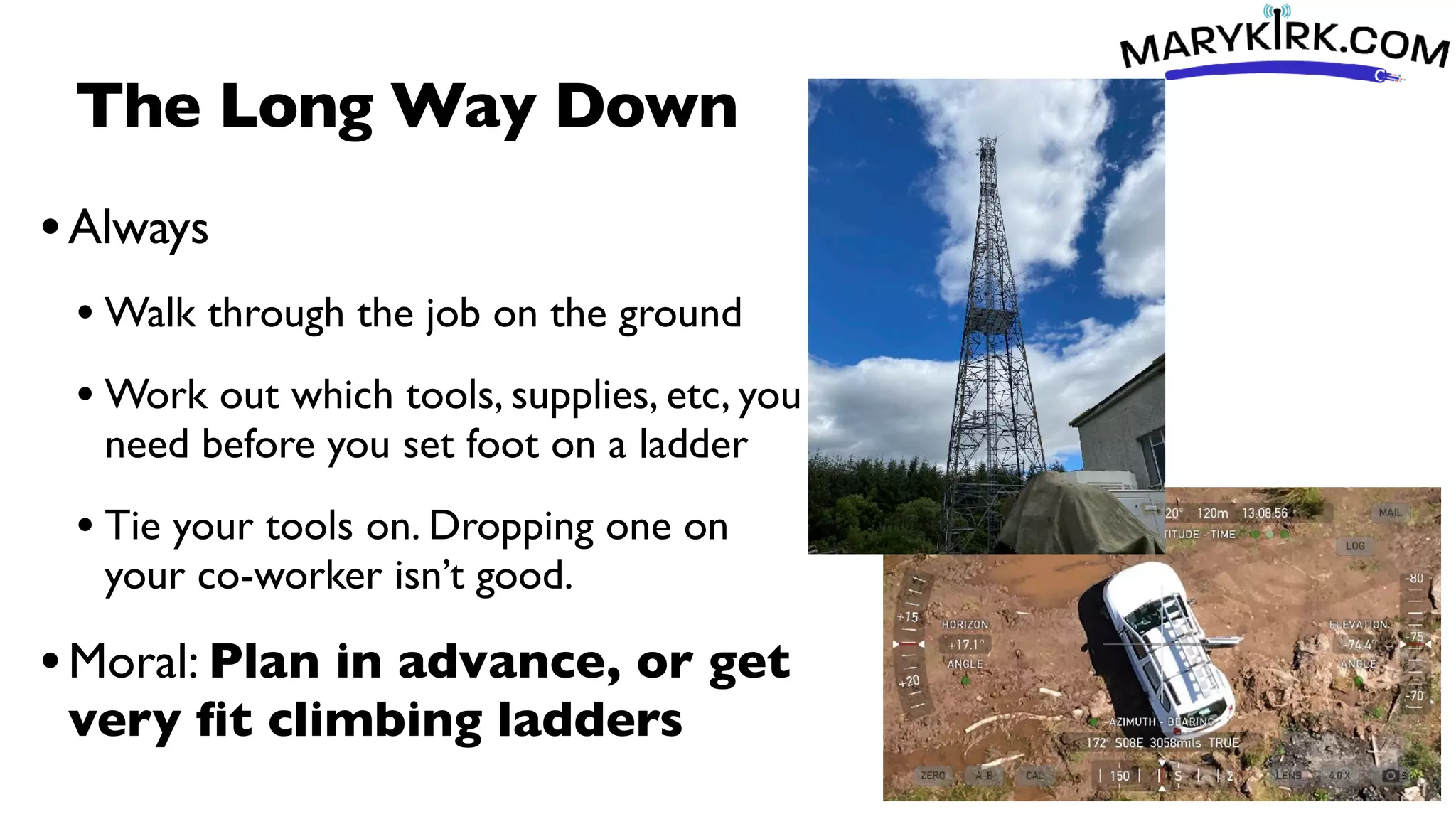
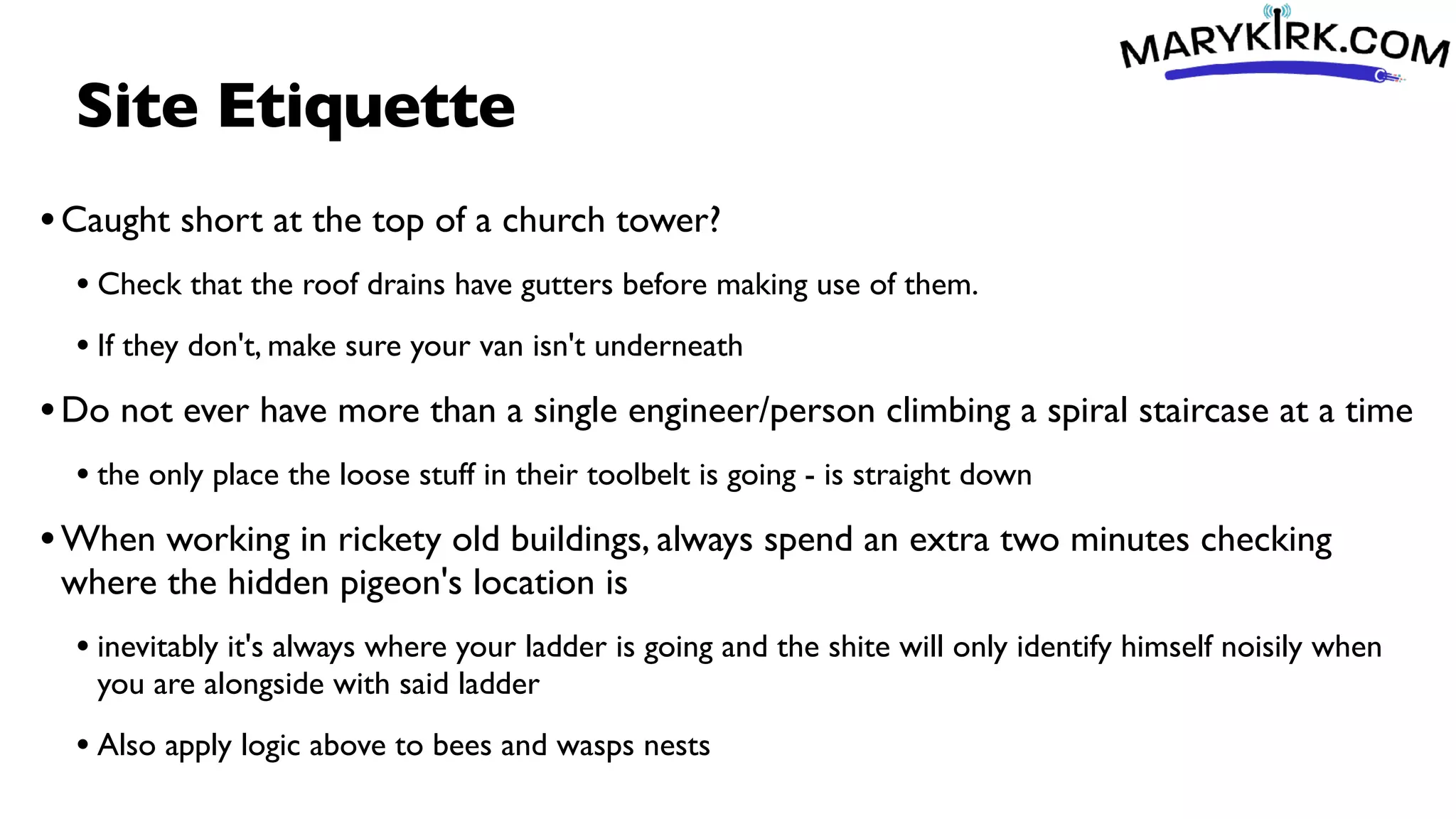
Bill Buchan presented on worst practices in wireless internet service provision to underline best practices. Some examples included: a wireless site container that tipped over during a storm due to incorrect wind loading calculations; overloading an inverter powering multiple radios and cameras; a cable that was damaged by rust allowing water ingress; an antenna mounted upside down allowing water to fill it; fiber cables being chewed by mice; and safety issues like working at heights without harnesses or falling tools. The presentation emphasized planning, maintenance, equipment siting and securing cables and gear to avoid outages and hazards.