Embed presentation
Download as PDF, PPTX
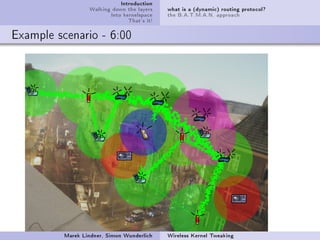
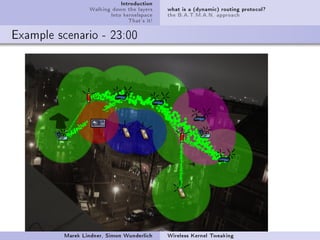
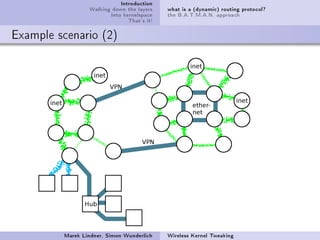
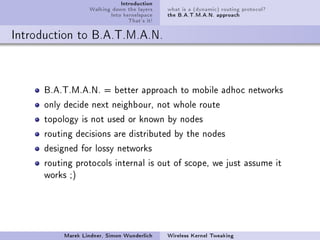
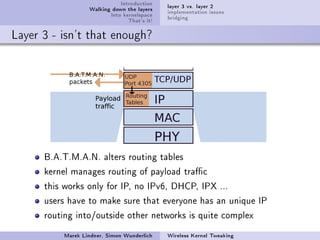
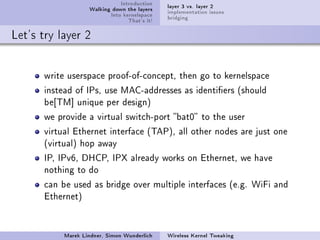
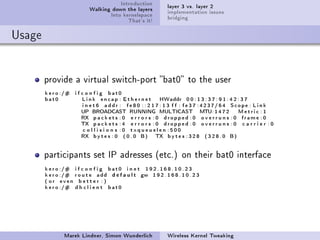
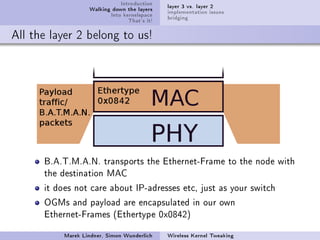
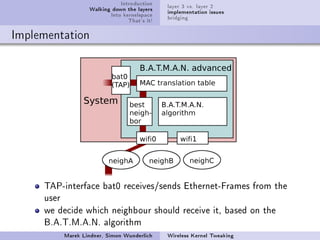
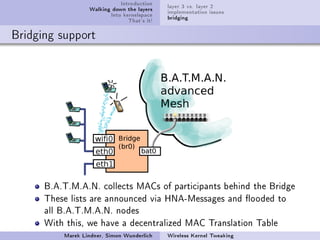
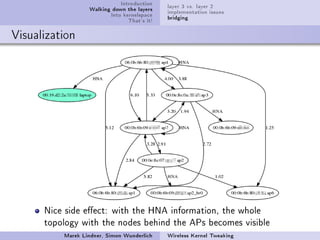
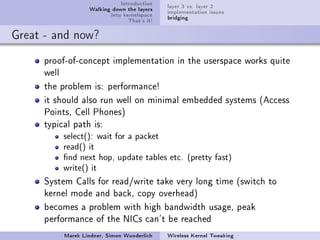

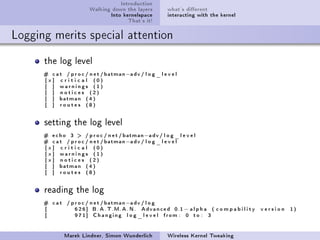
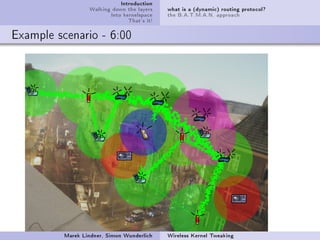
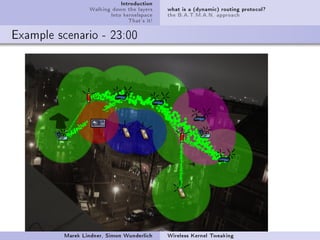
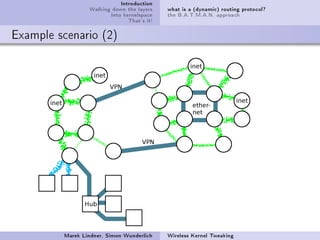
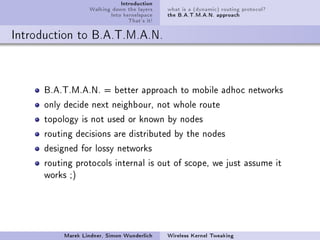
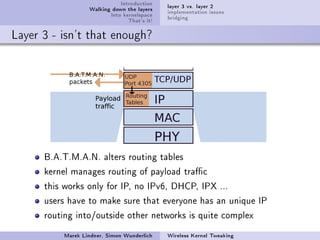
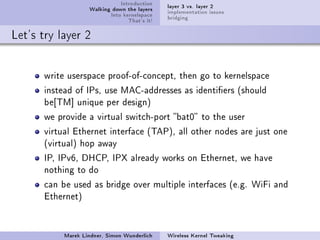
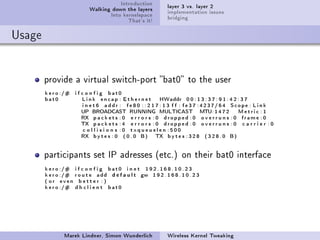
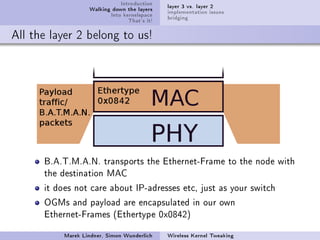
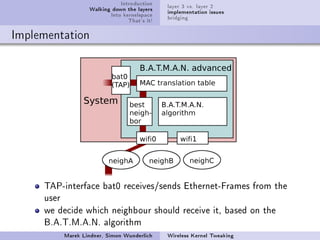
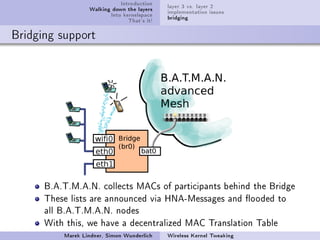
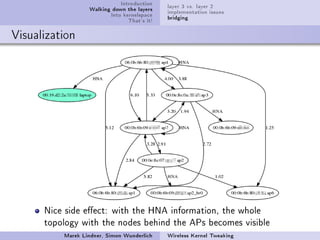
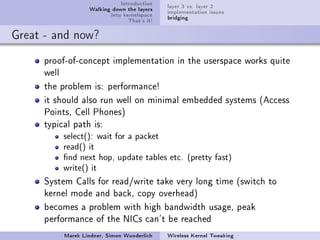
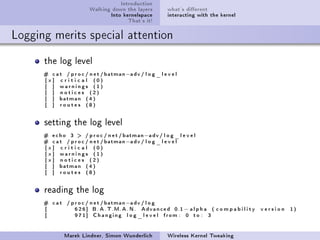
The document discusses the b.a.t.m.a.n. (Better Approach to Mobile Adhoc Networks) routing protocol, focusing on its implementation in wireless kernel space for optimized performance. It outlines the differences between Layer 2 and Layer 3 implementations, highlighting the need for effective routing in lossy networks and the use of MAC addresses for identification. The text emphasizes the advantages of kernelspace interaction, including reduced message copying and improved asynchronous packet handling.