The document discusses various topics related to web mining and data mining including:
- Web mining techniques like web content mining, web usage mining, and web structure mining.
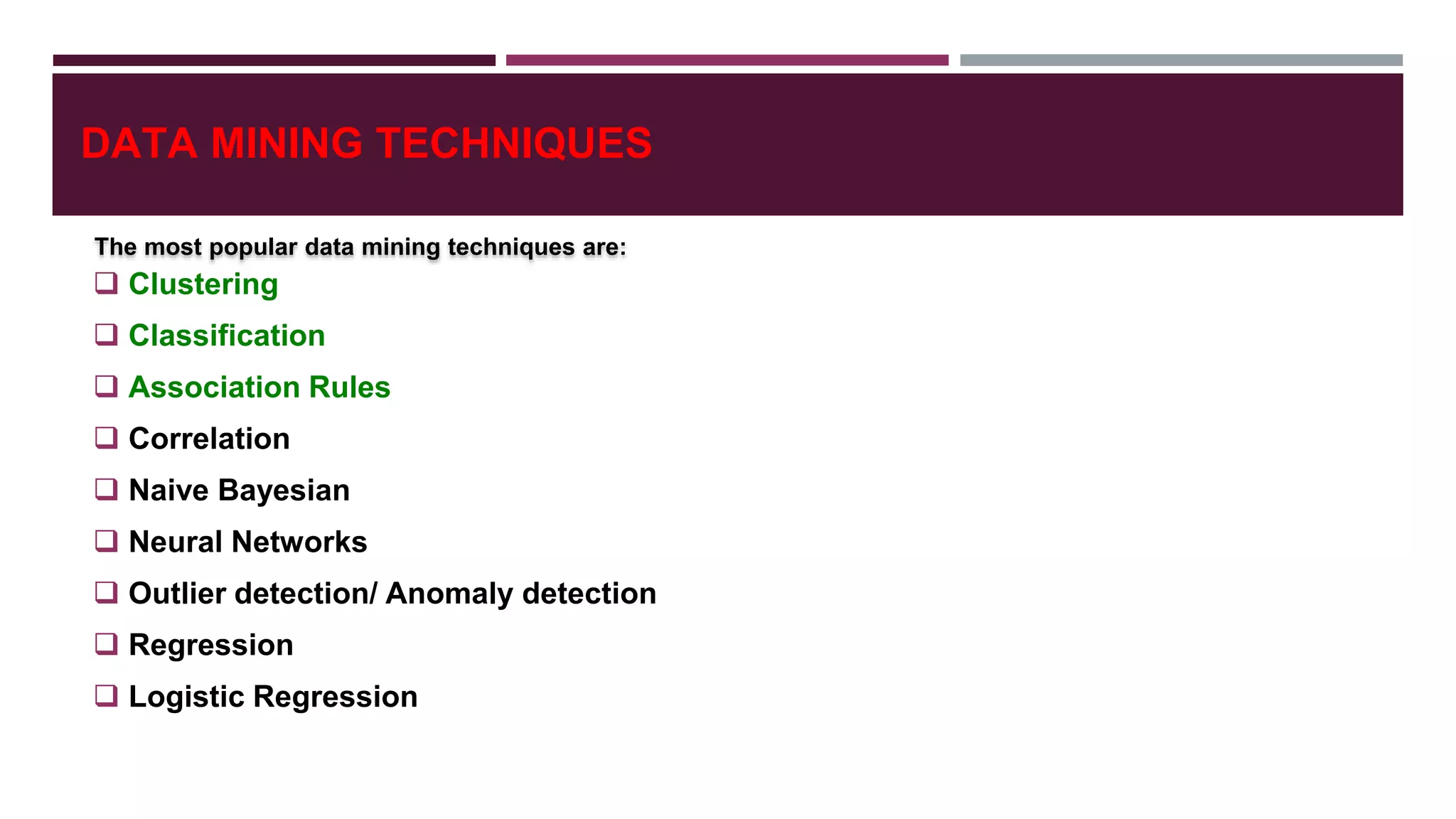
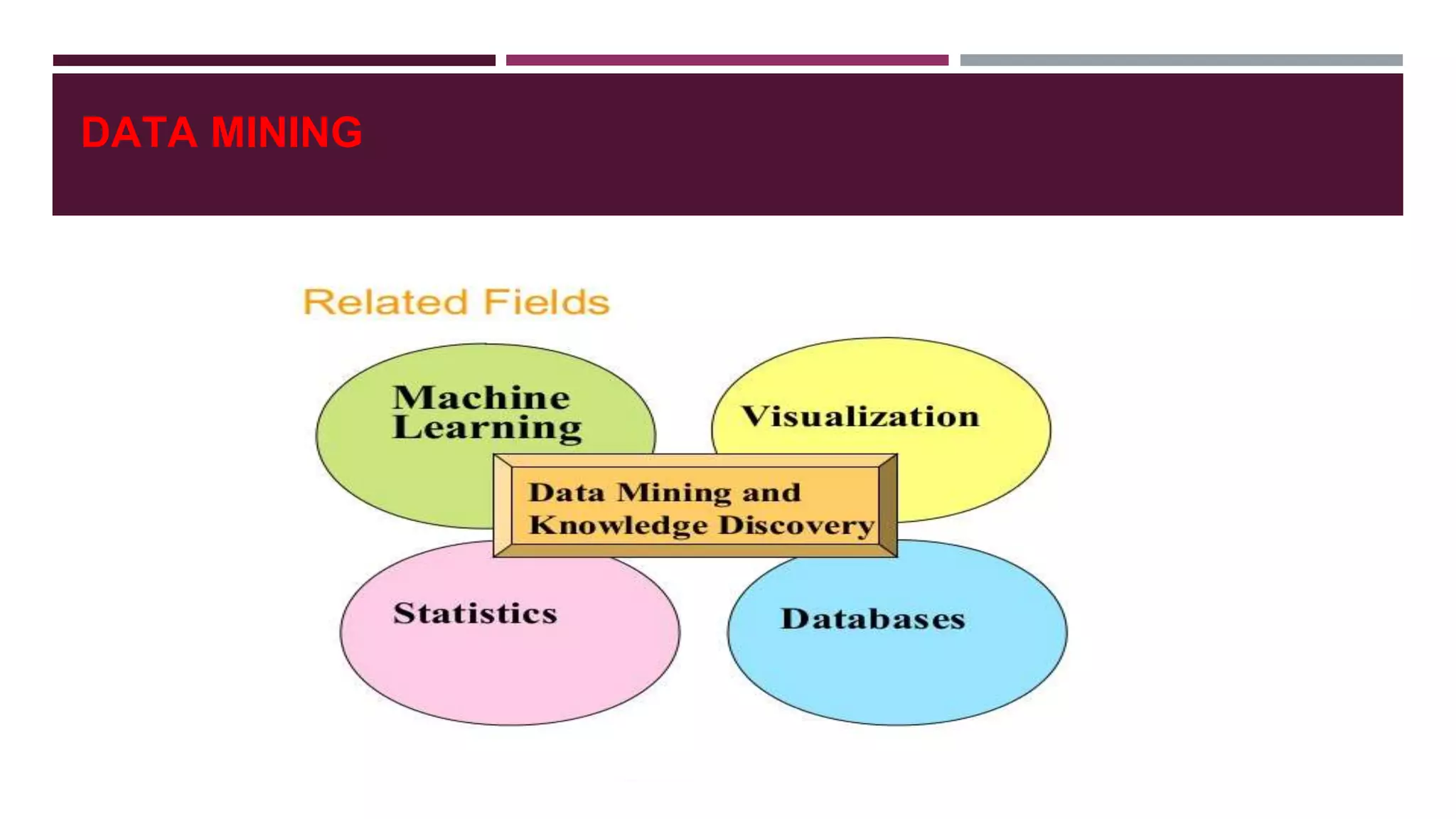
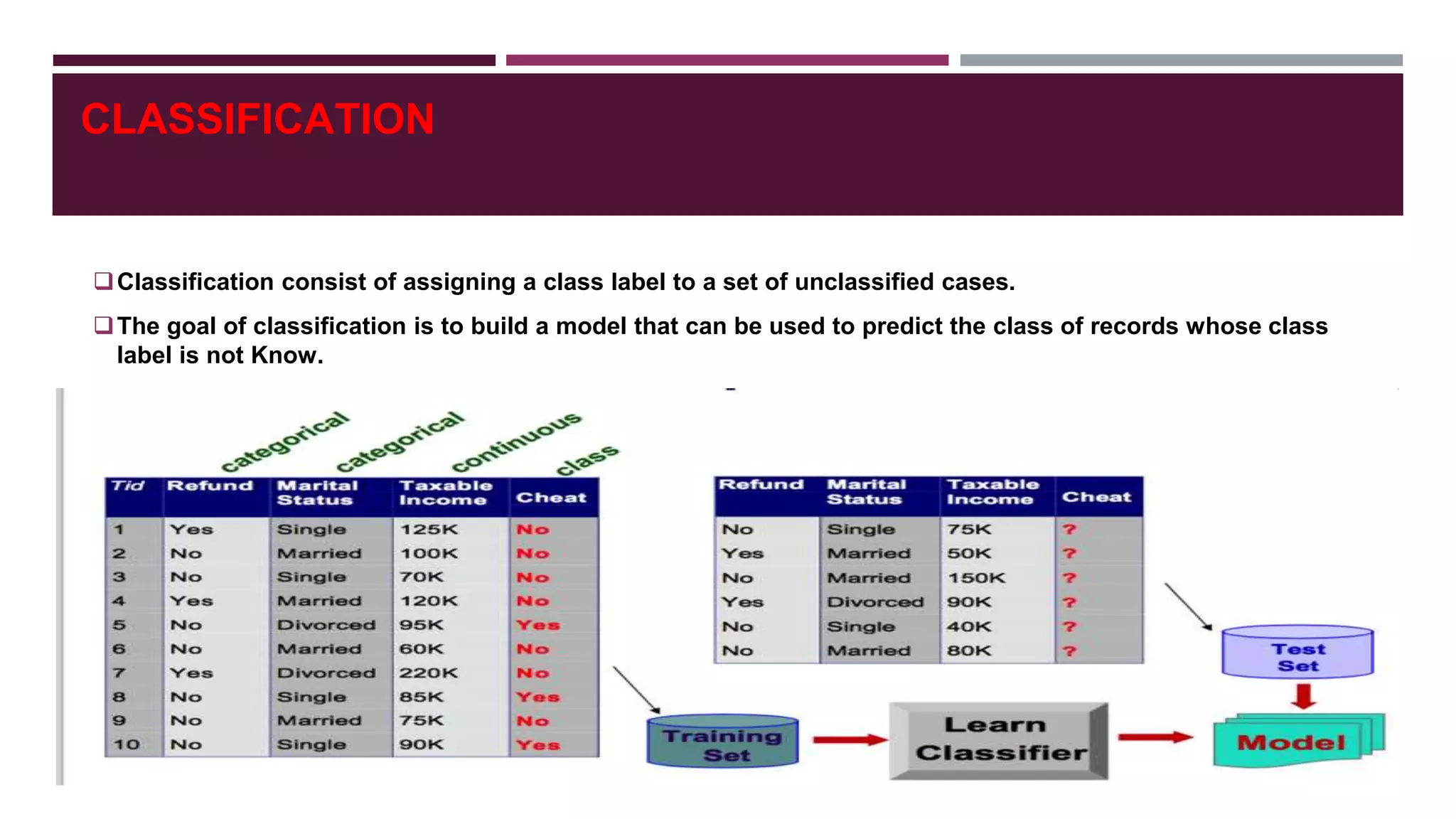
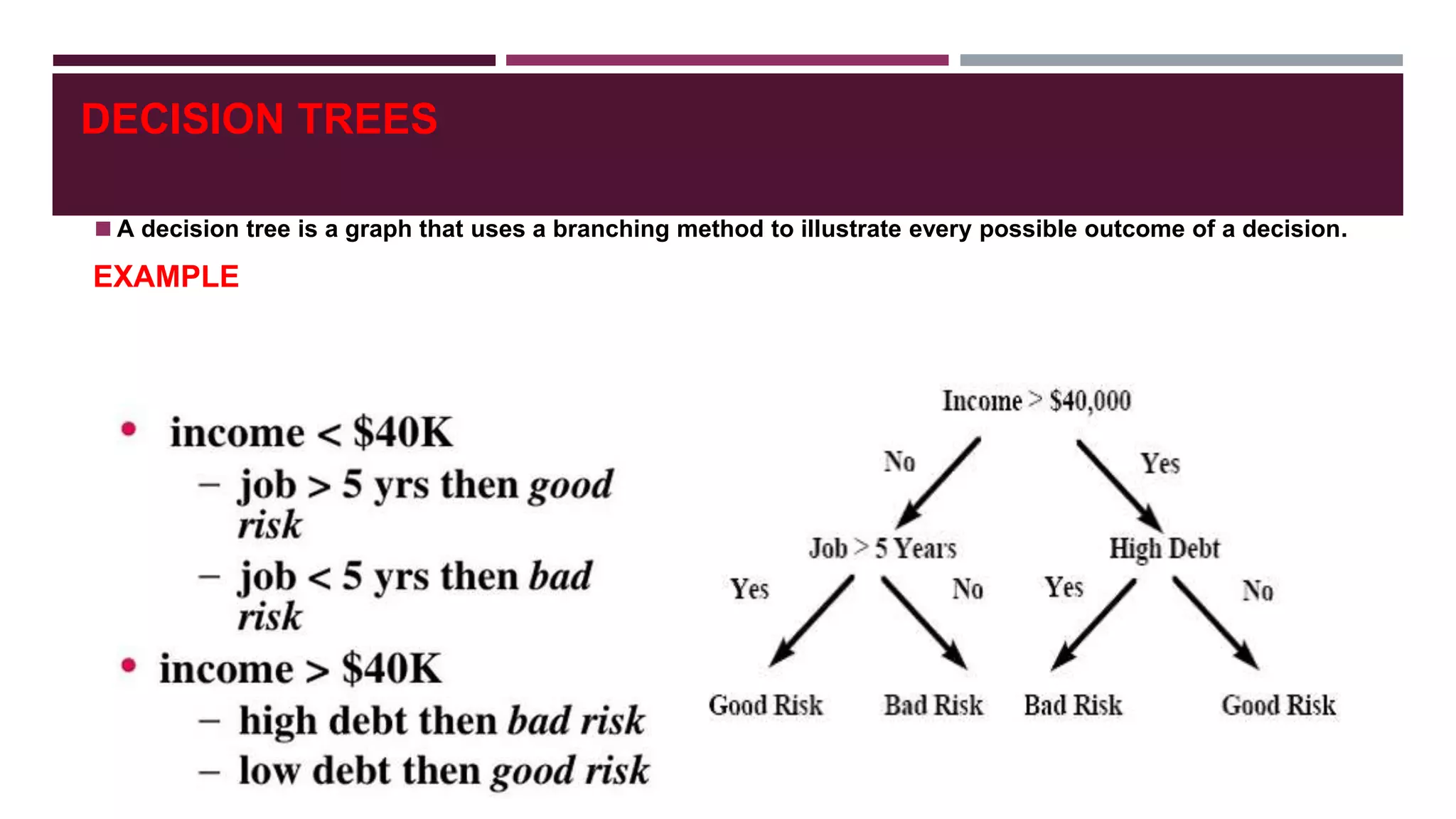
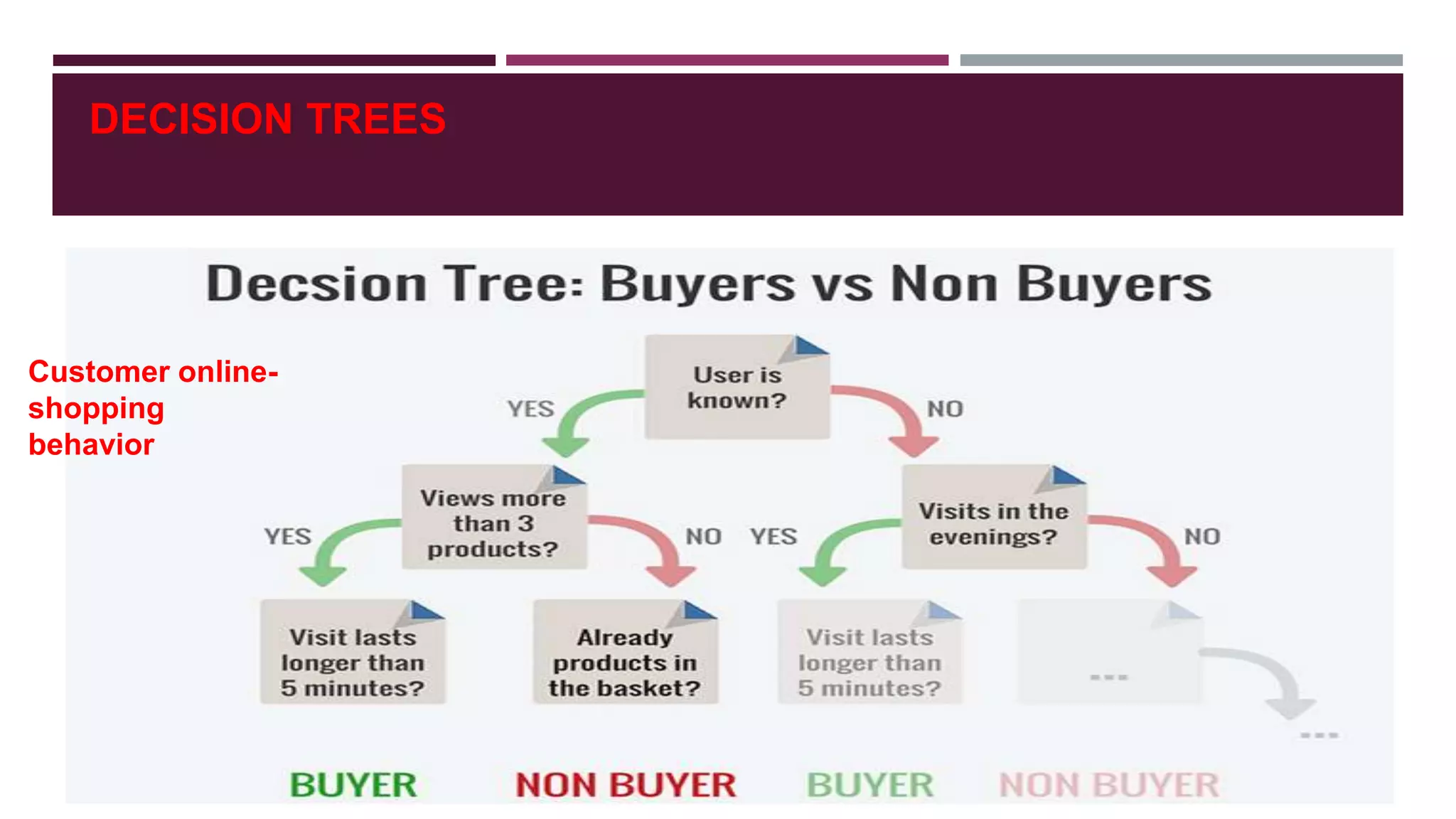
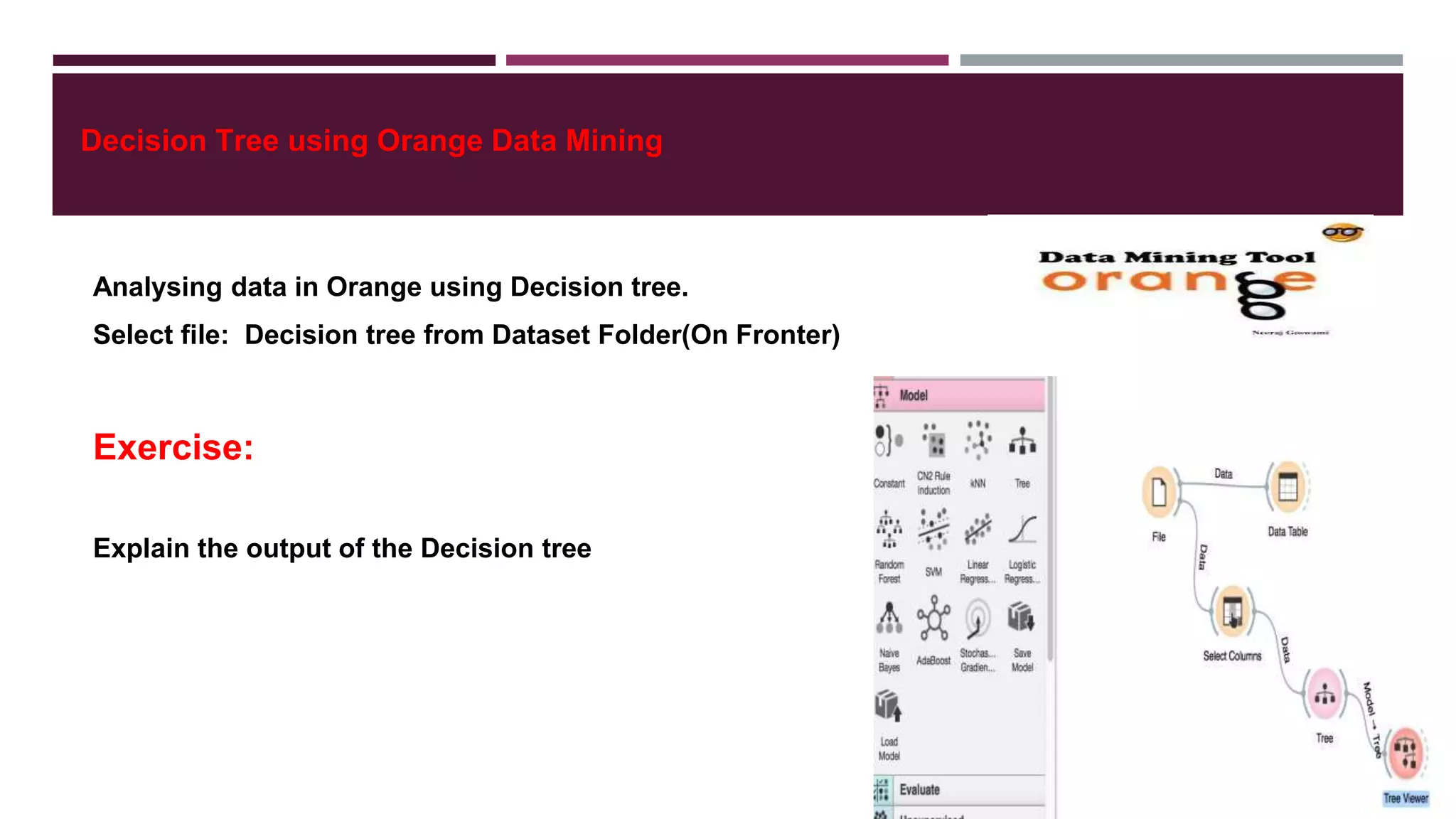
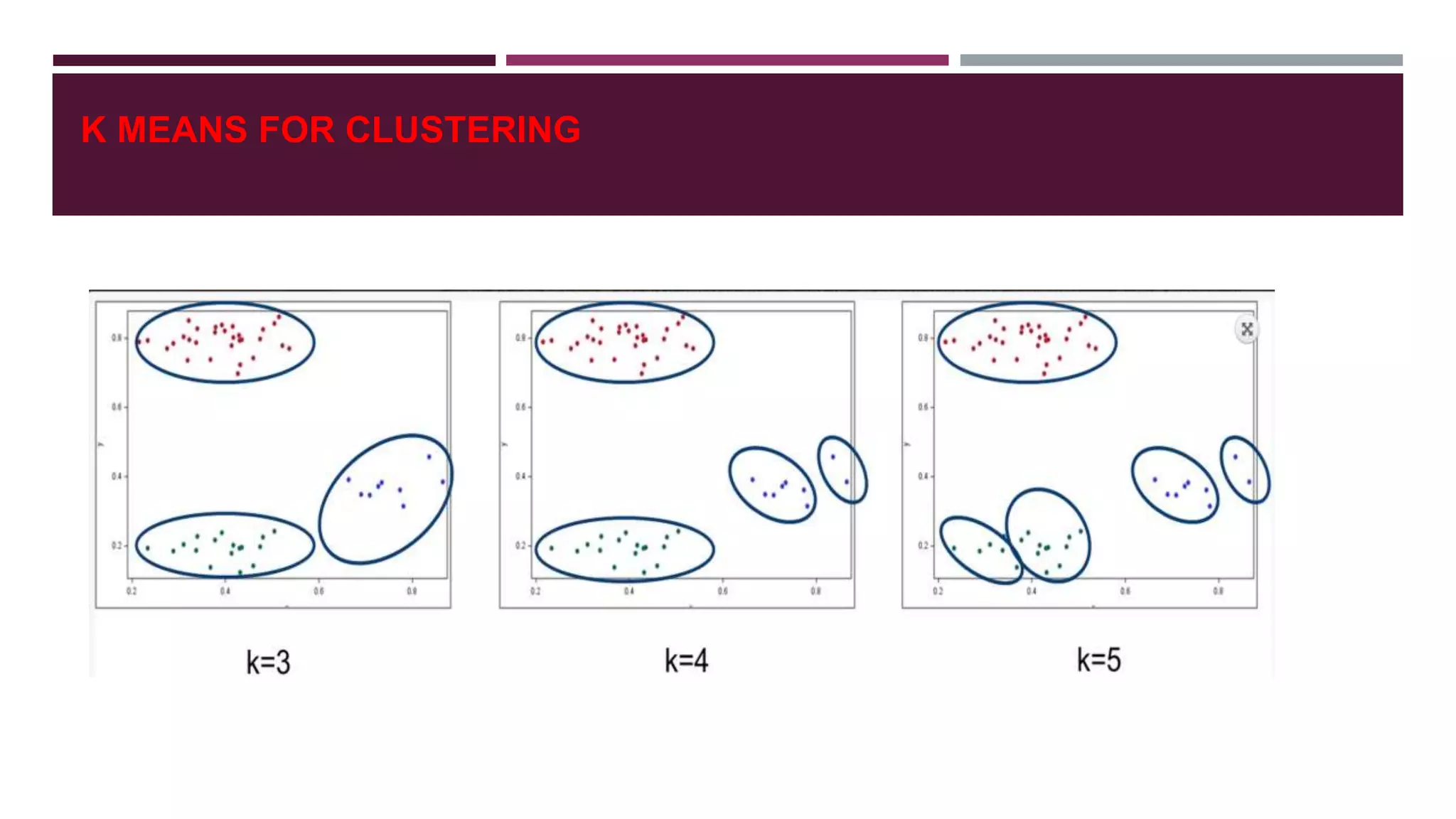
- Common data mining techniques like classification, clustering, association rule mining etc. and how they are applied in web content mining.
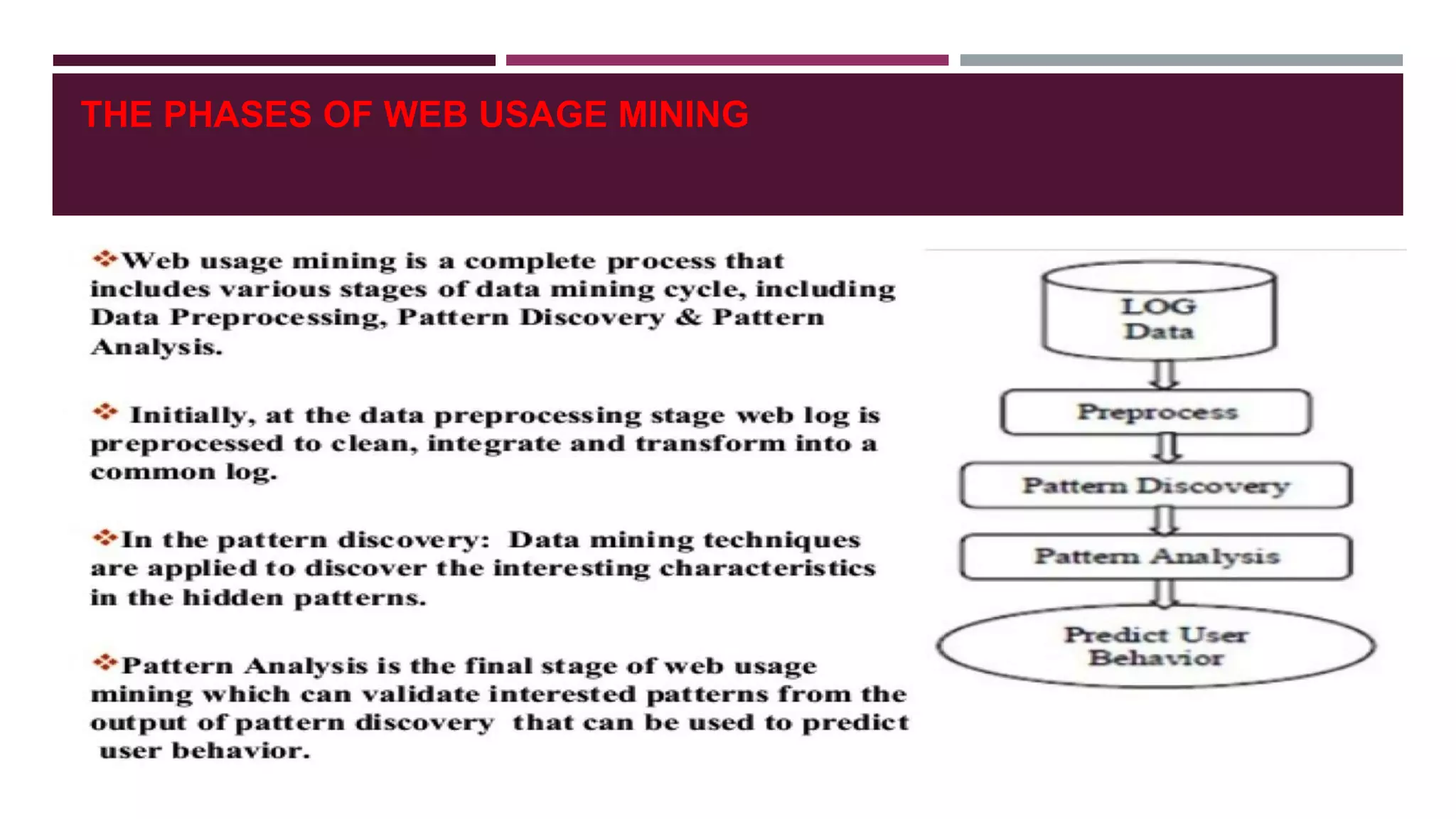
- How web usage mining analyzes server log files to understand user browsing behavior and patterns.
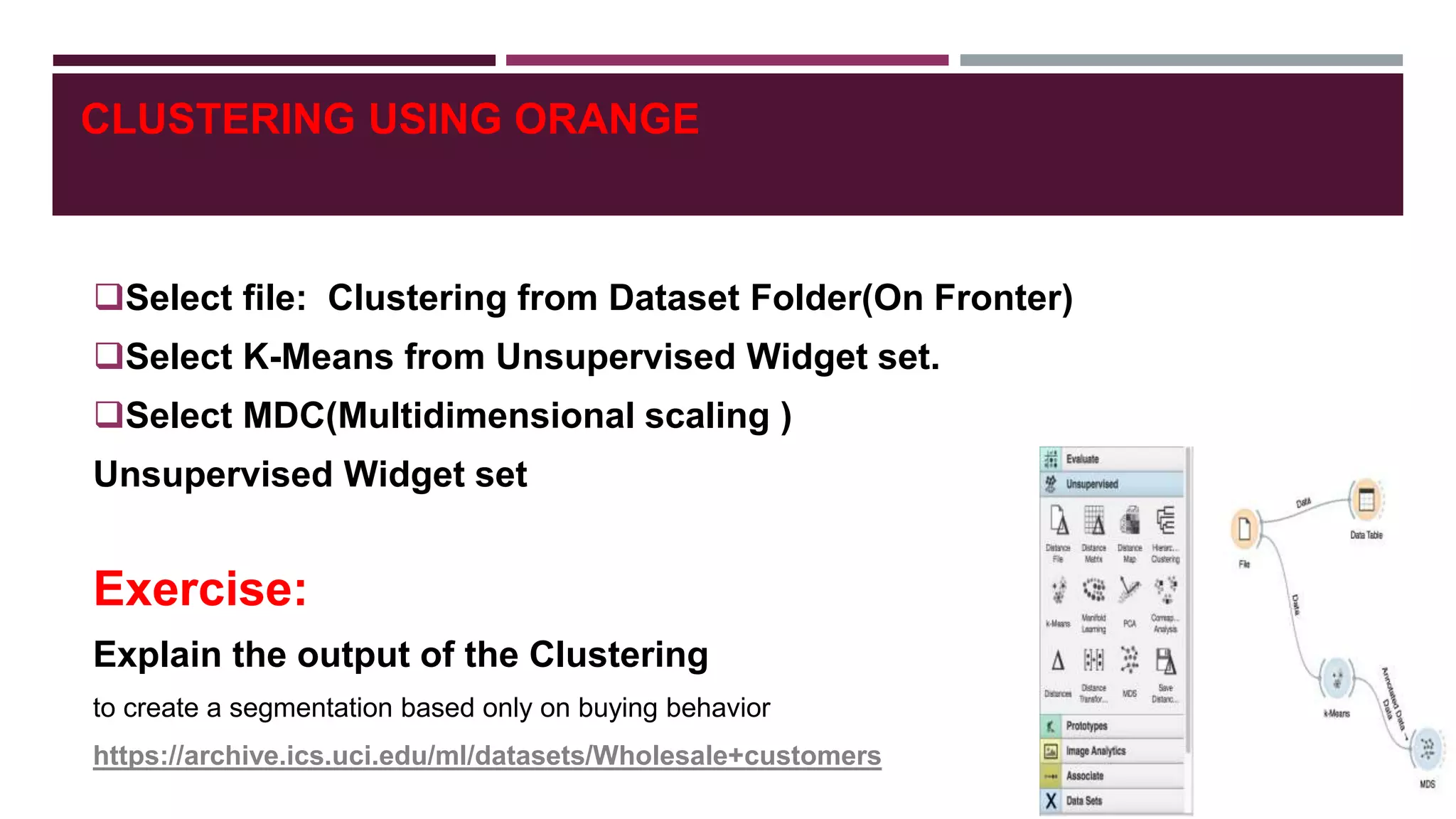
- Classification and clustering are two popular techniques used in web usage mining, with decision trees and k-means clustering provided as examples.










![SOCIAL NETWORK ANALYSIS
Social network analysis [SNA] is the mapping and measuring of relationships and flows between
people, groups, organizations, computers, and other connected information/knowledge entities.
The nodes in the network are the people and groups while the links show relationships or flows
between the nodes.
SNA provides both a visual and a mathematical analysis of human relationships.
EXAMPLE:
Who knows whom and who shares what information
and knowledge with whom through what media.](https://image.slidesharecdn.com/webminingsocialmediamining-190604083351/75/Web-mining-and-social-media-mining-44-2048.jpg)