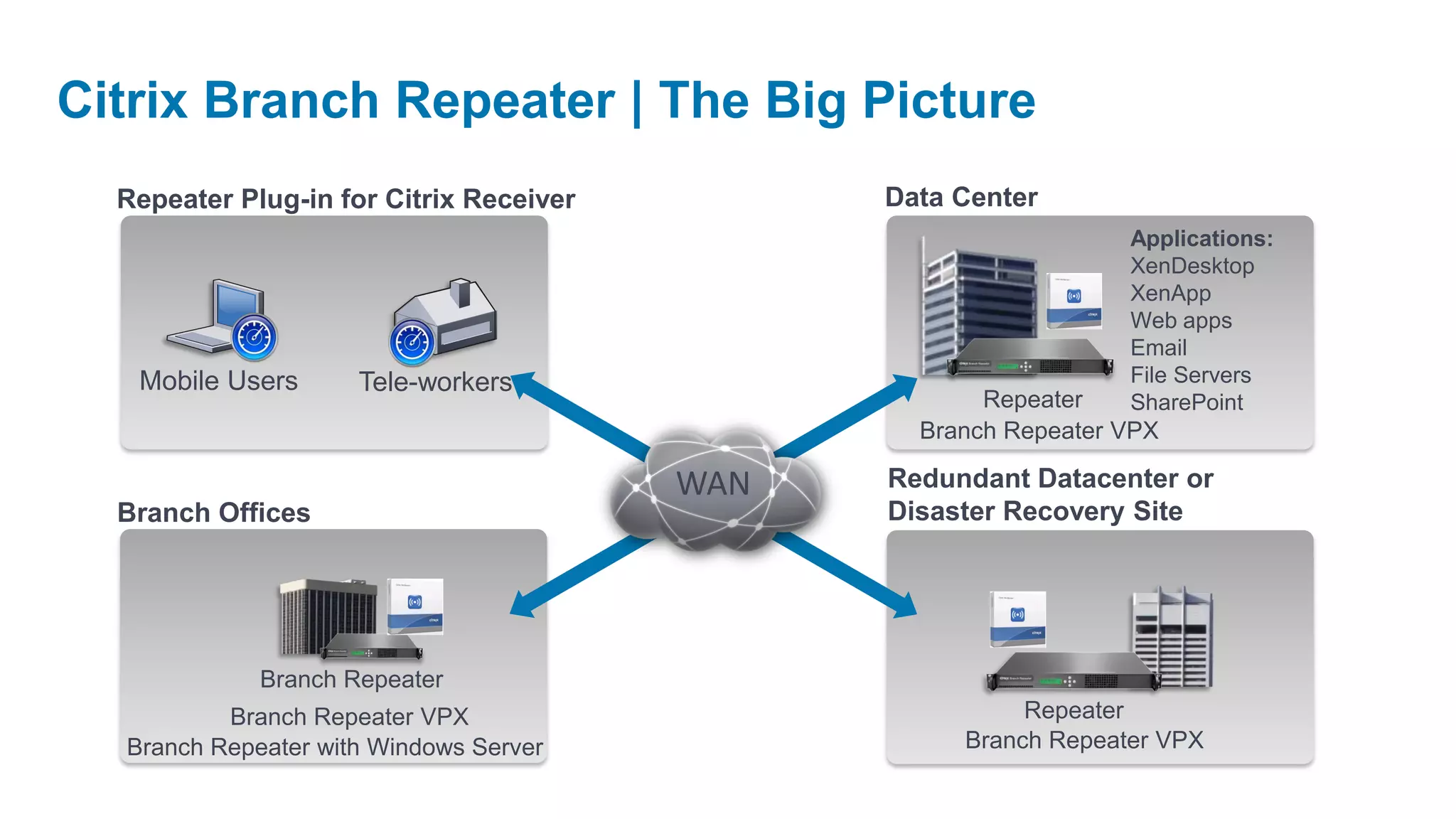
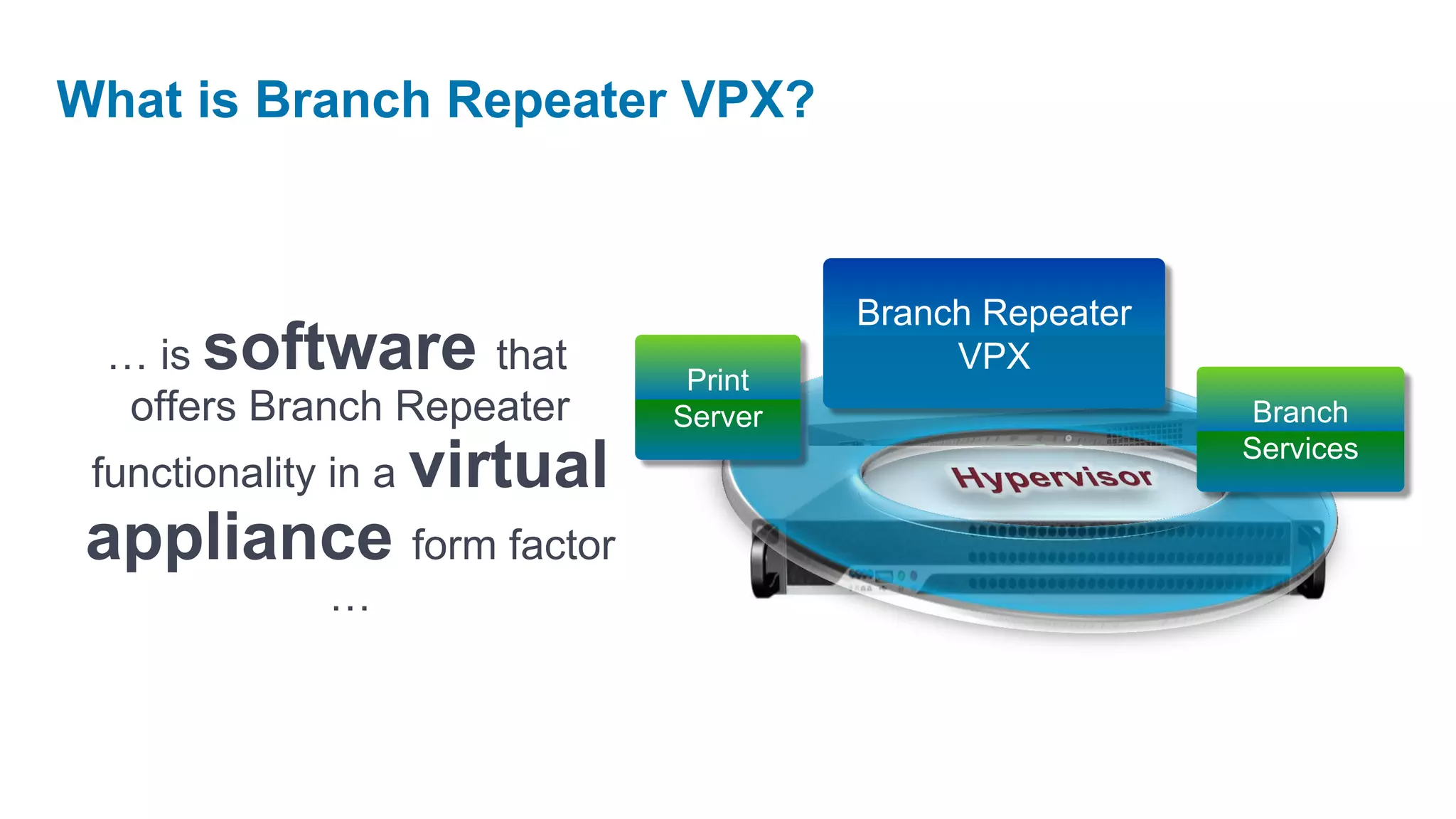
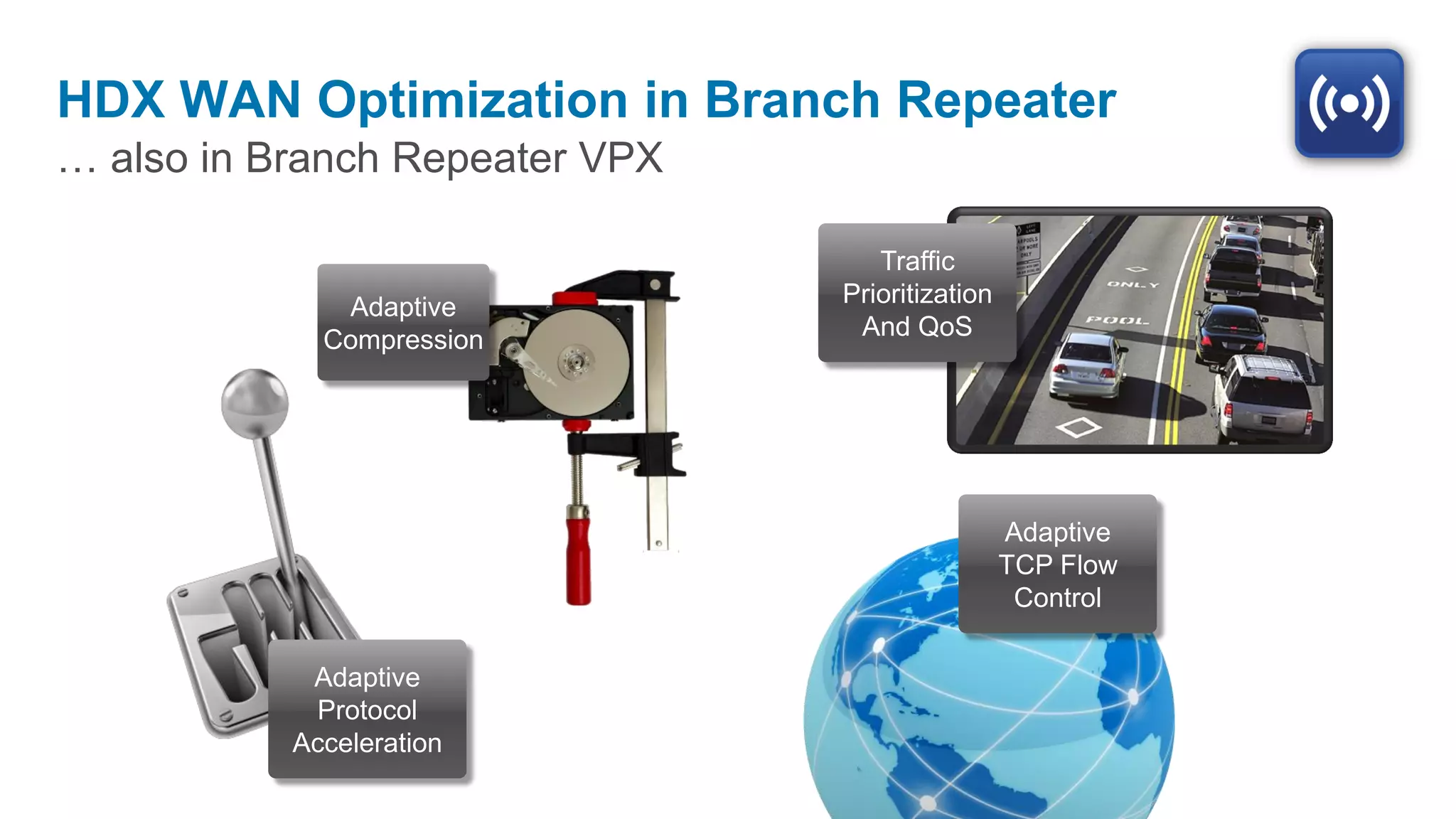
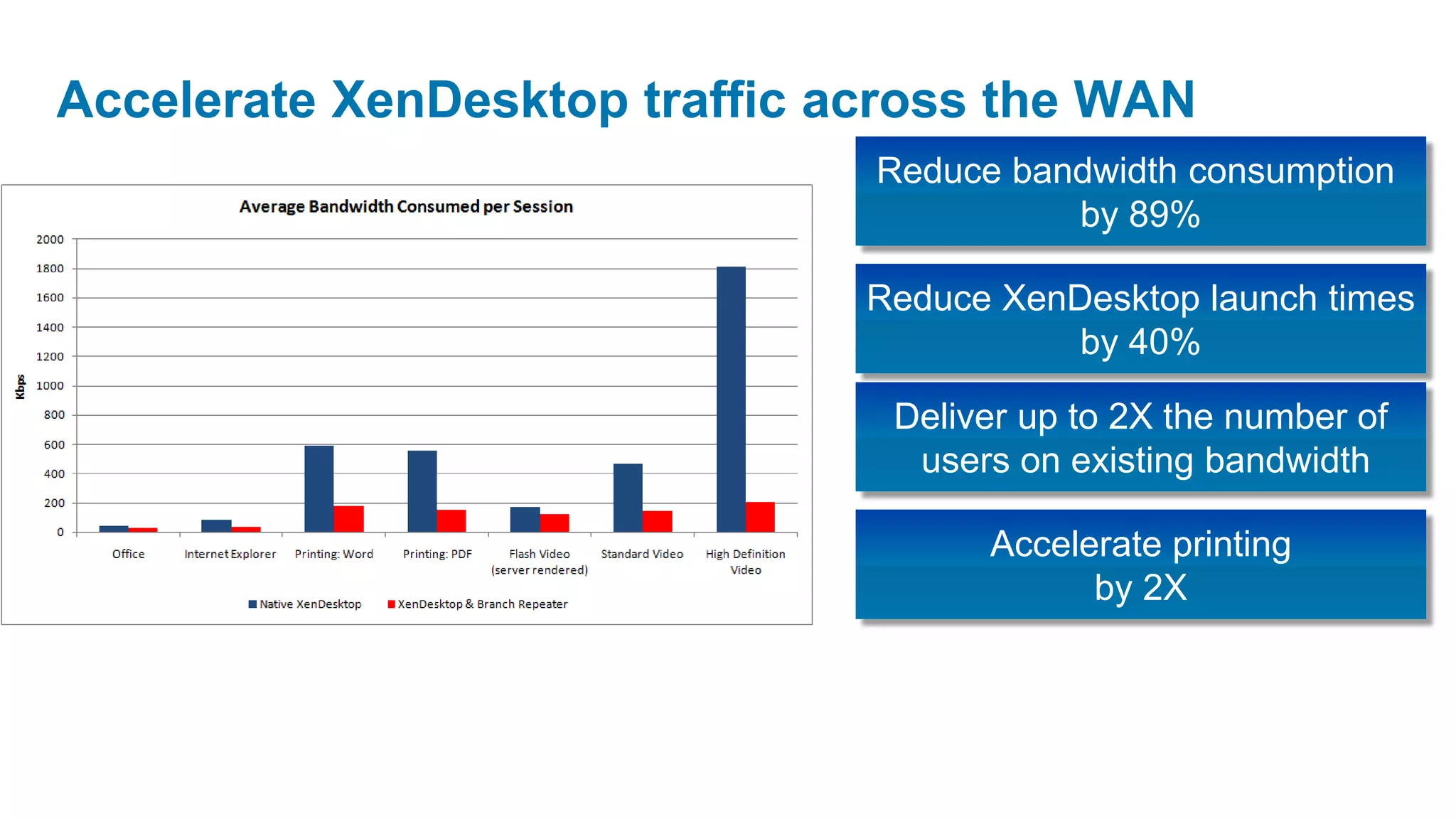
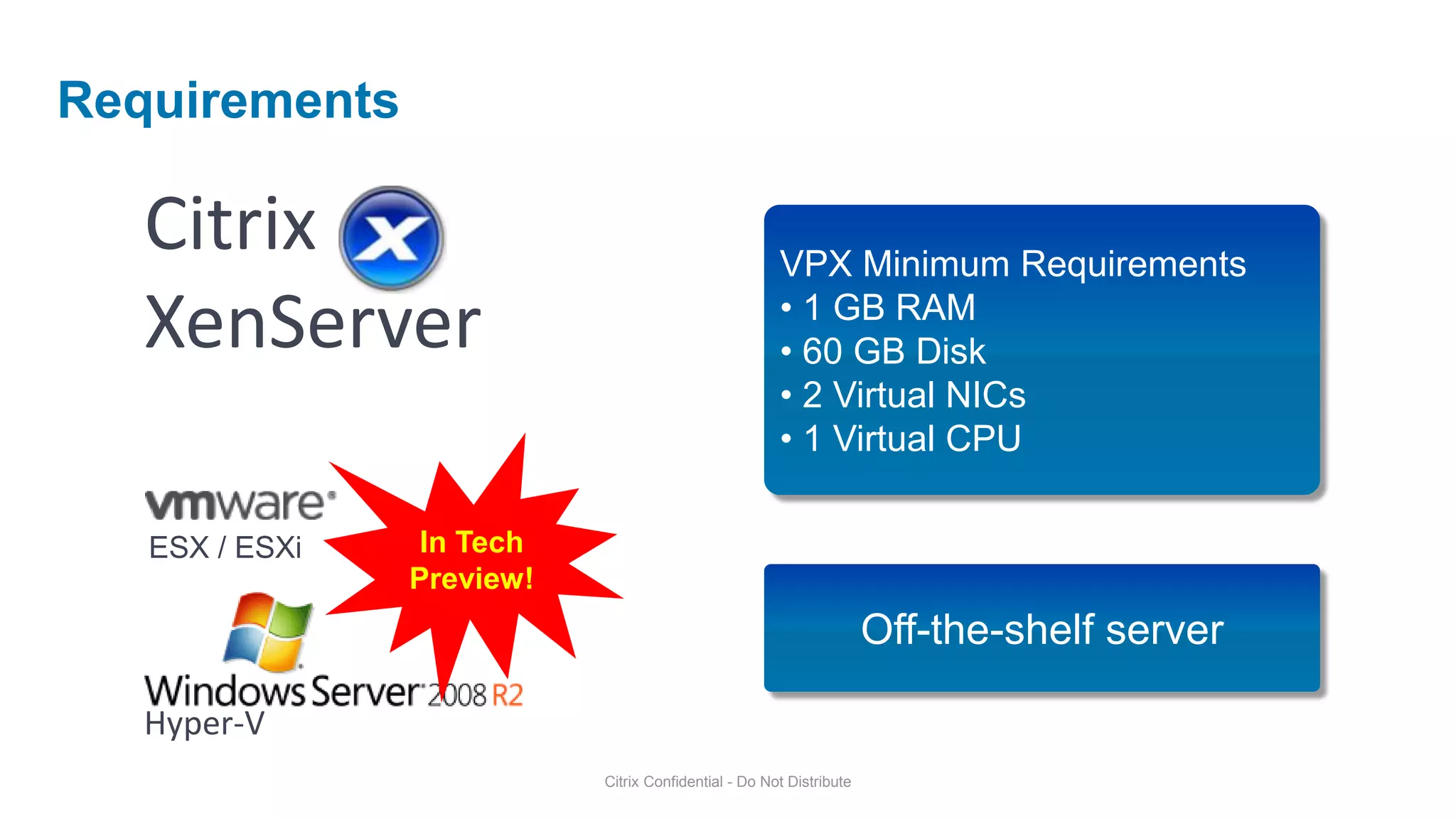
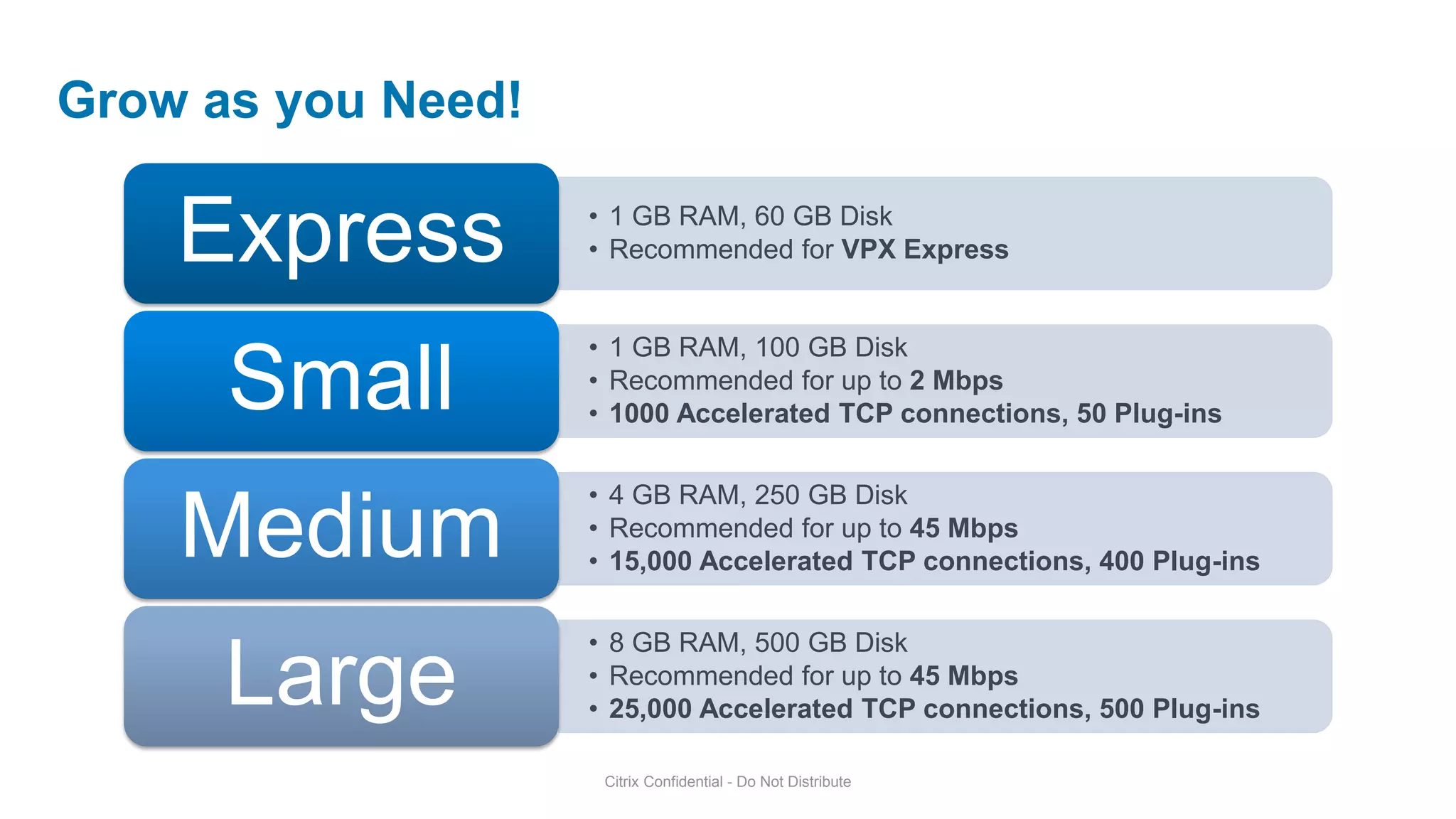
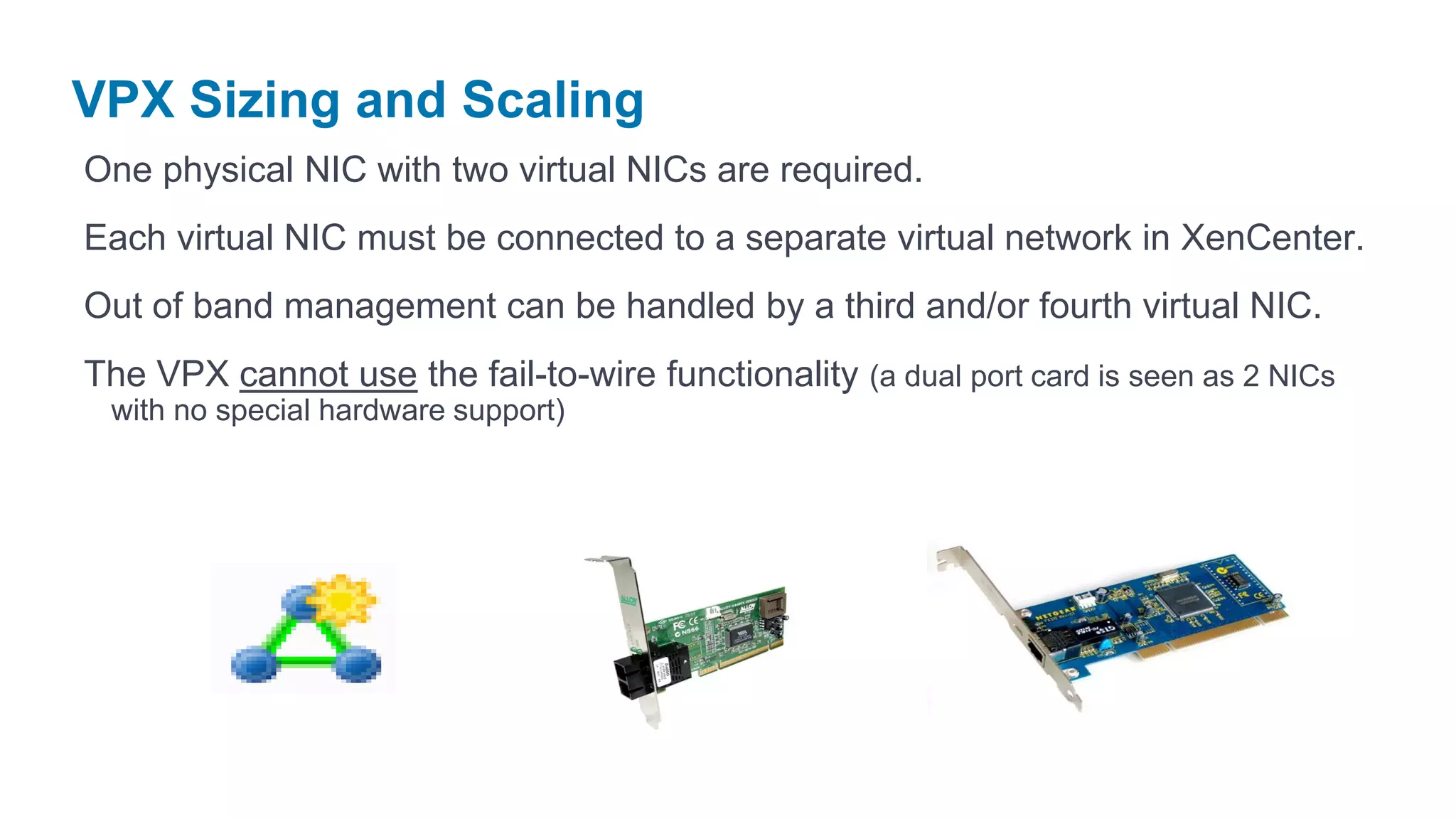
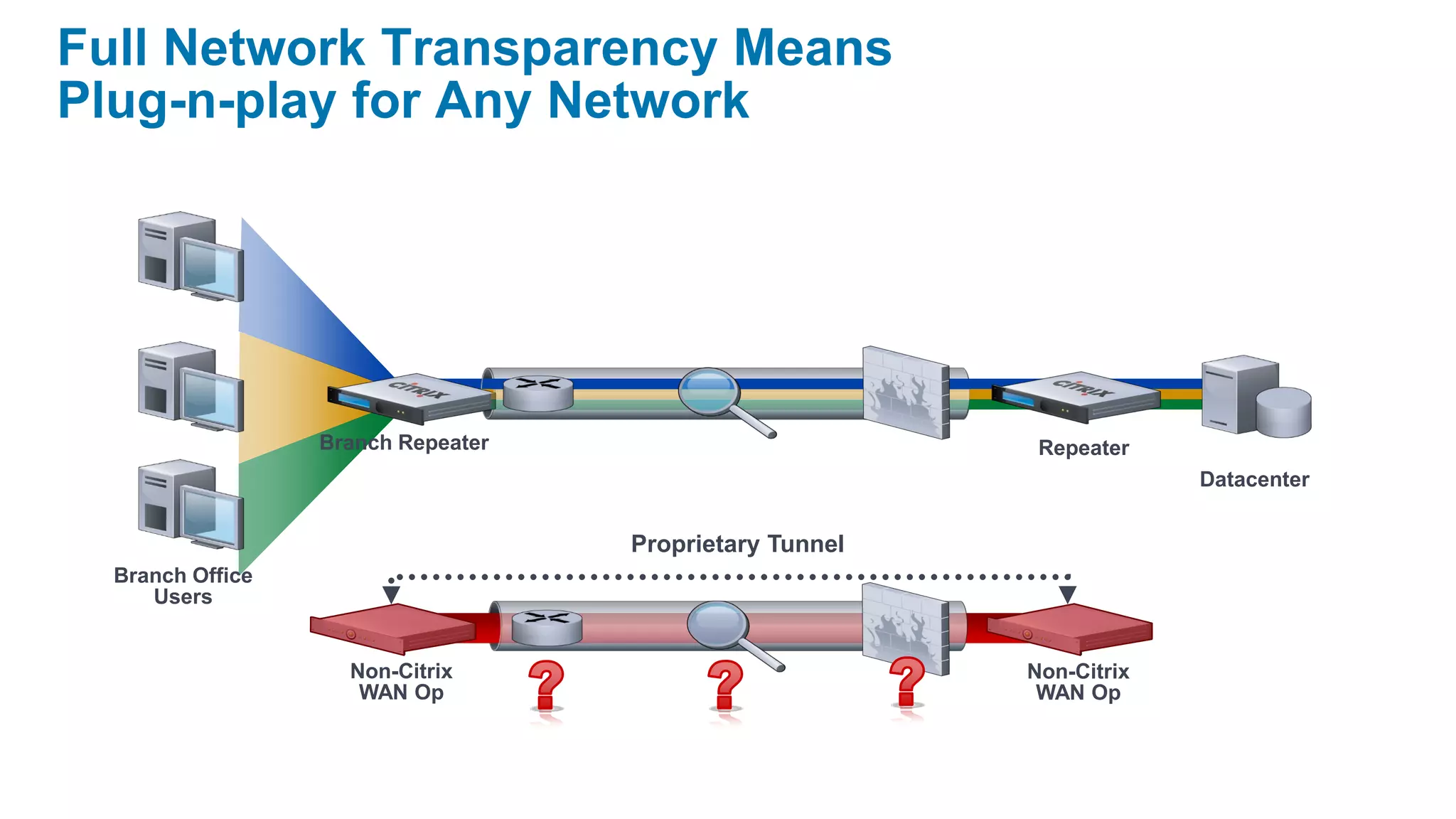
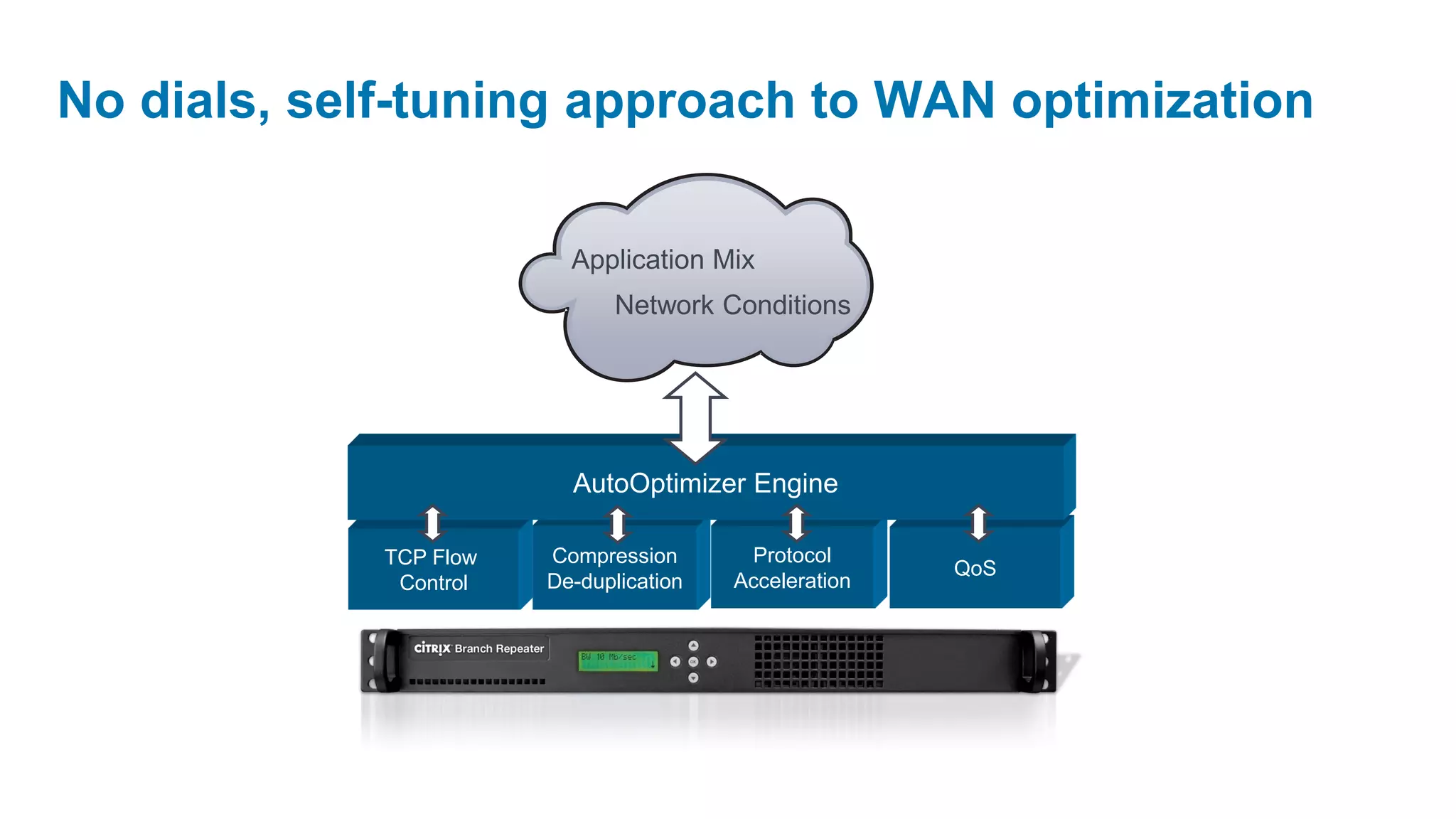
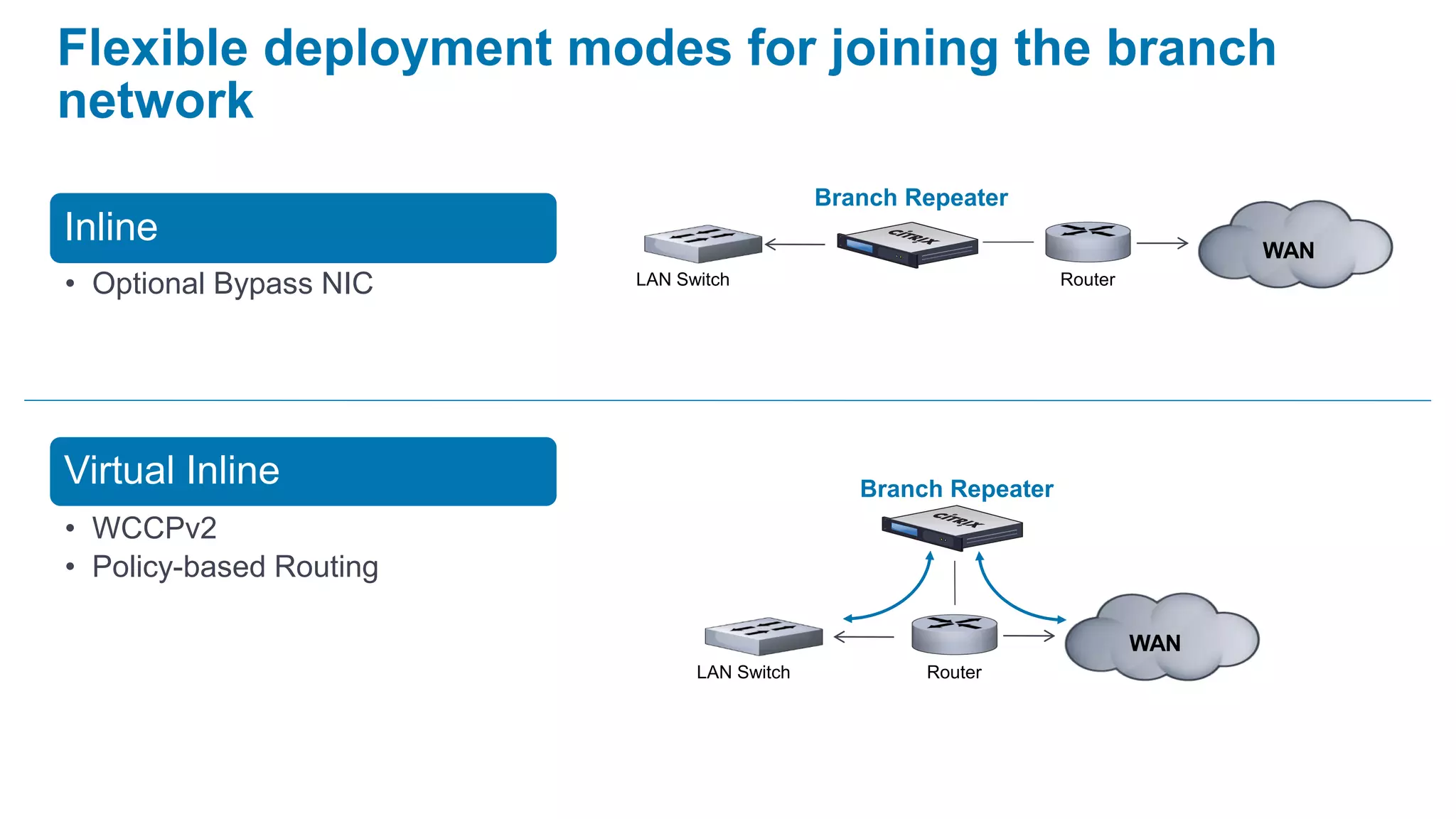
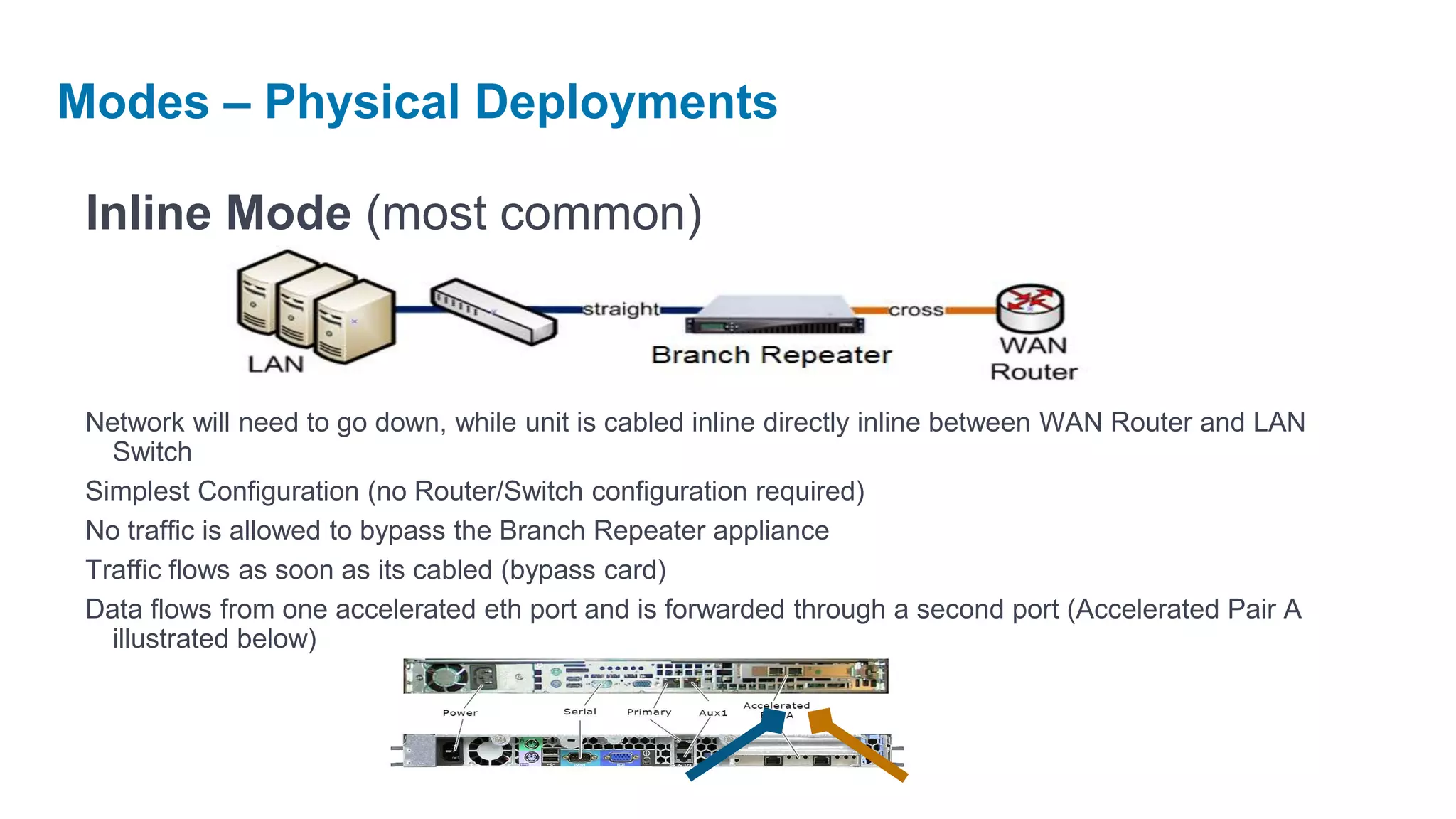
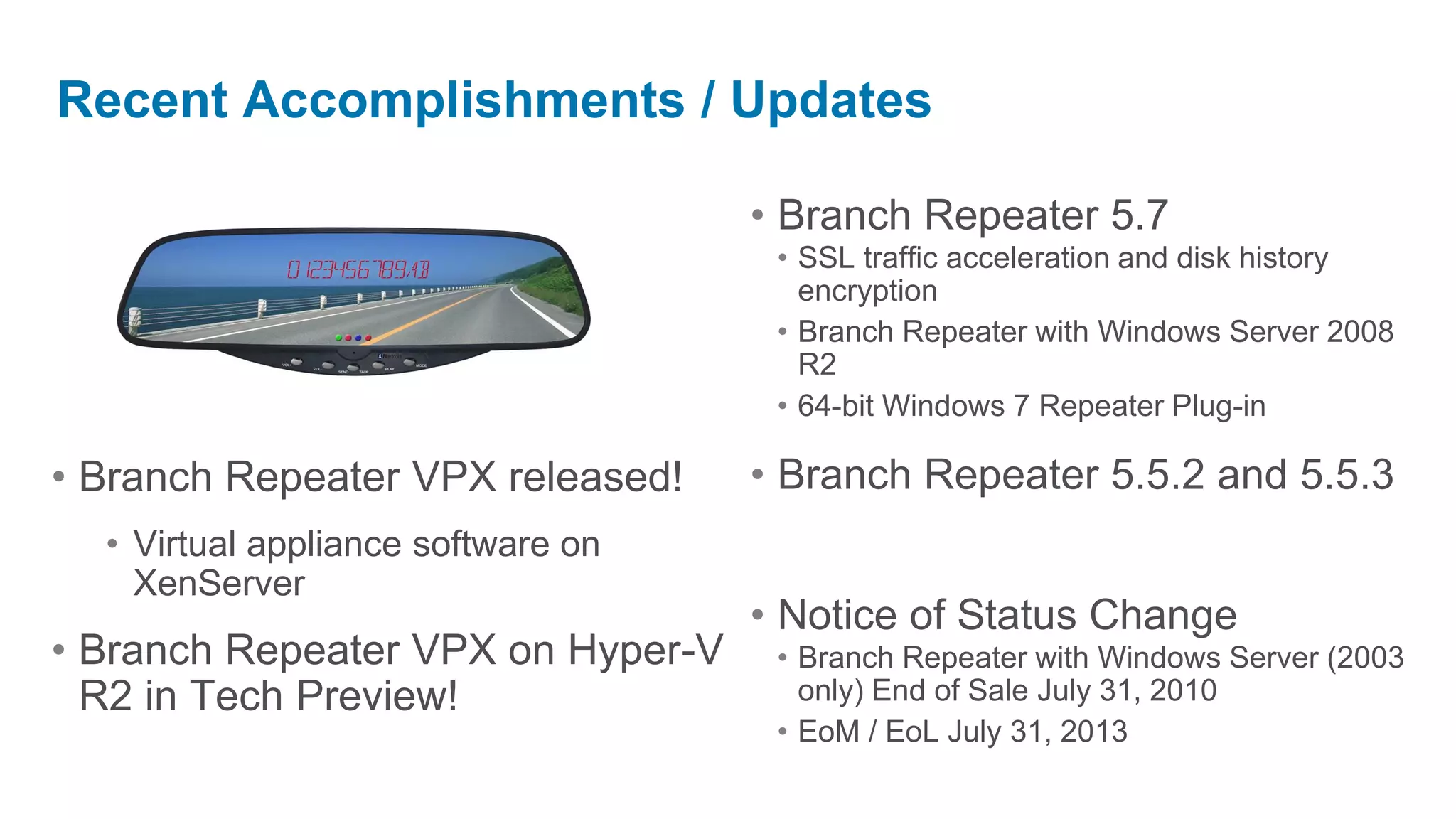
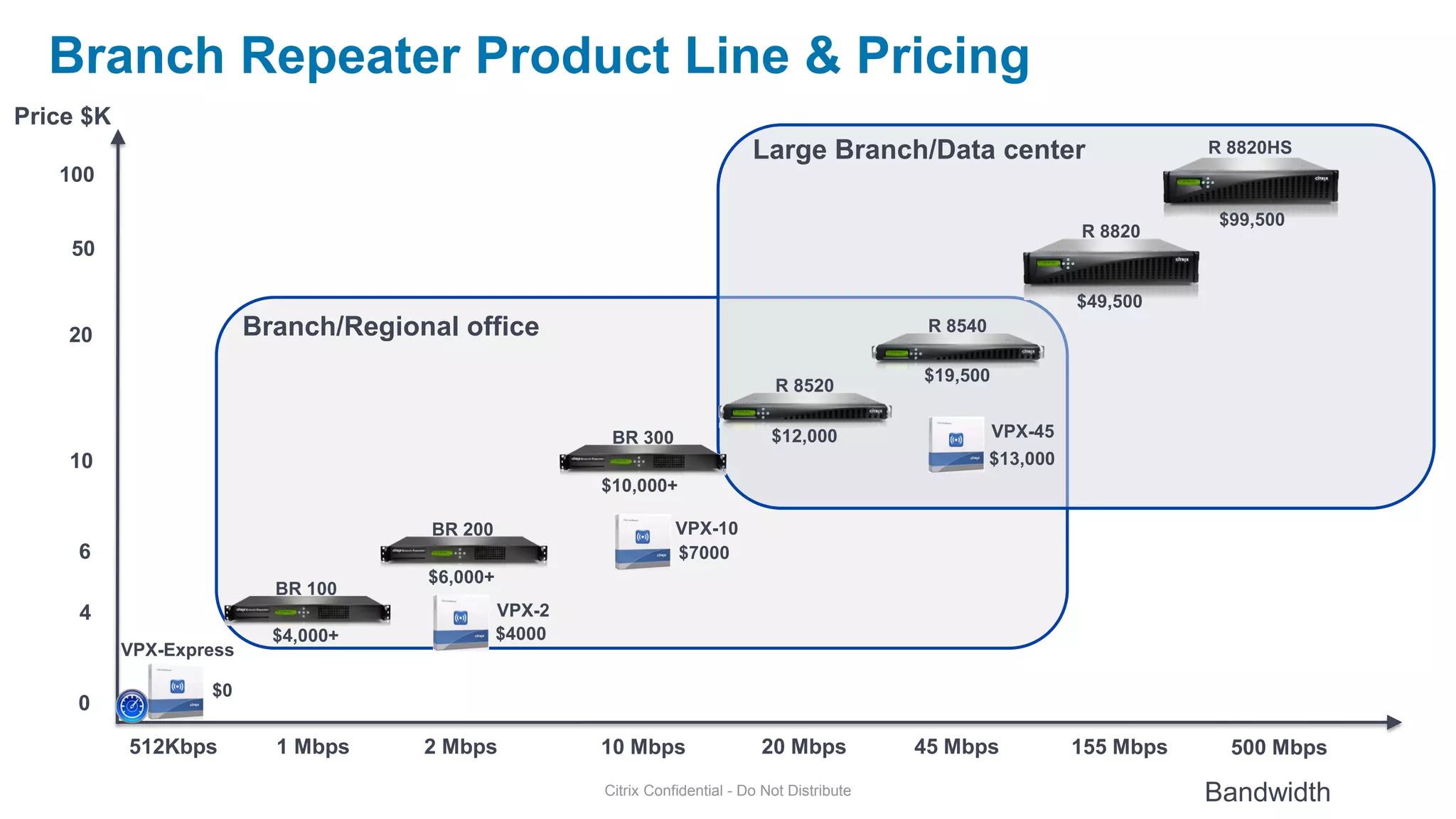
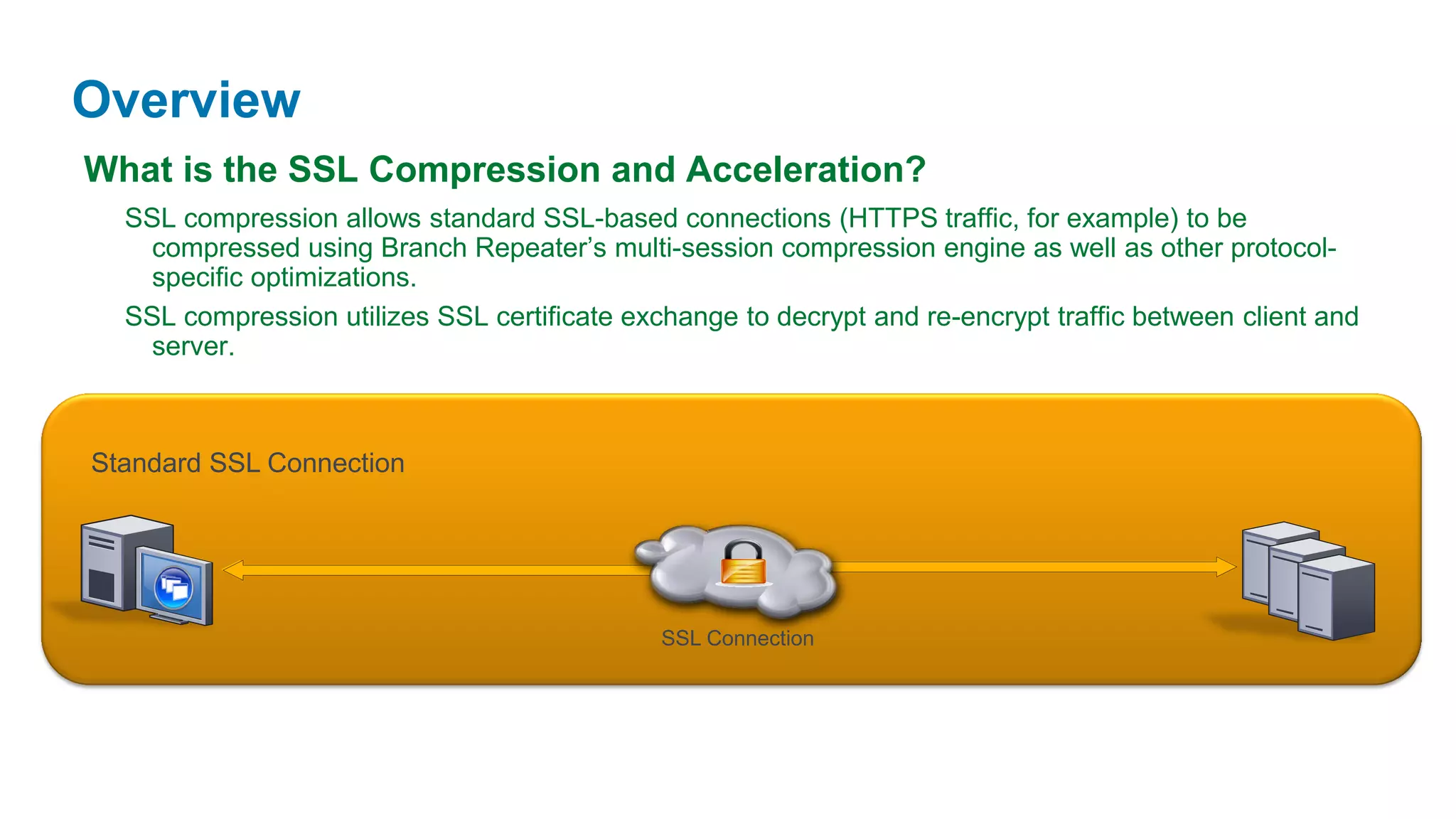
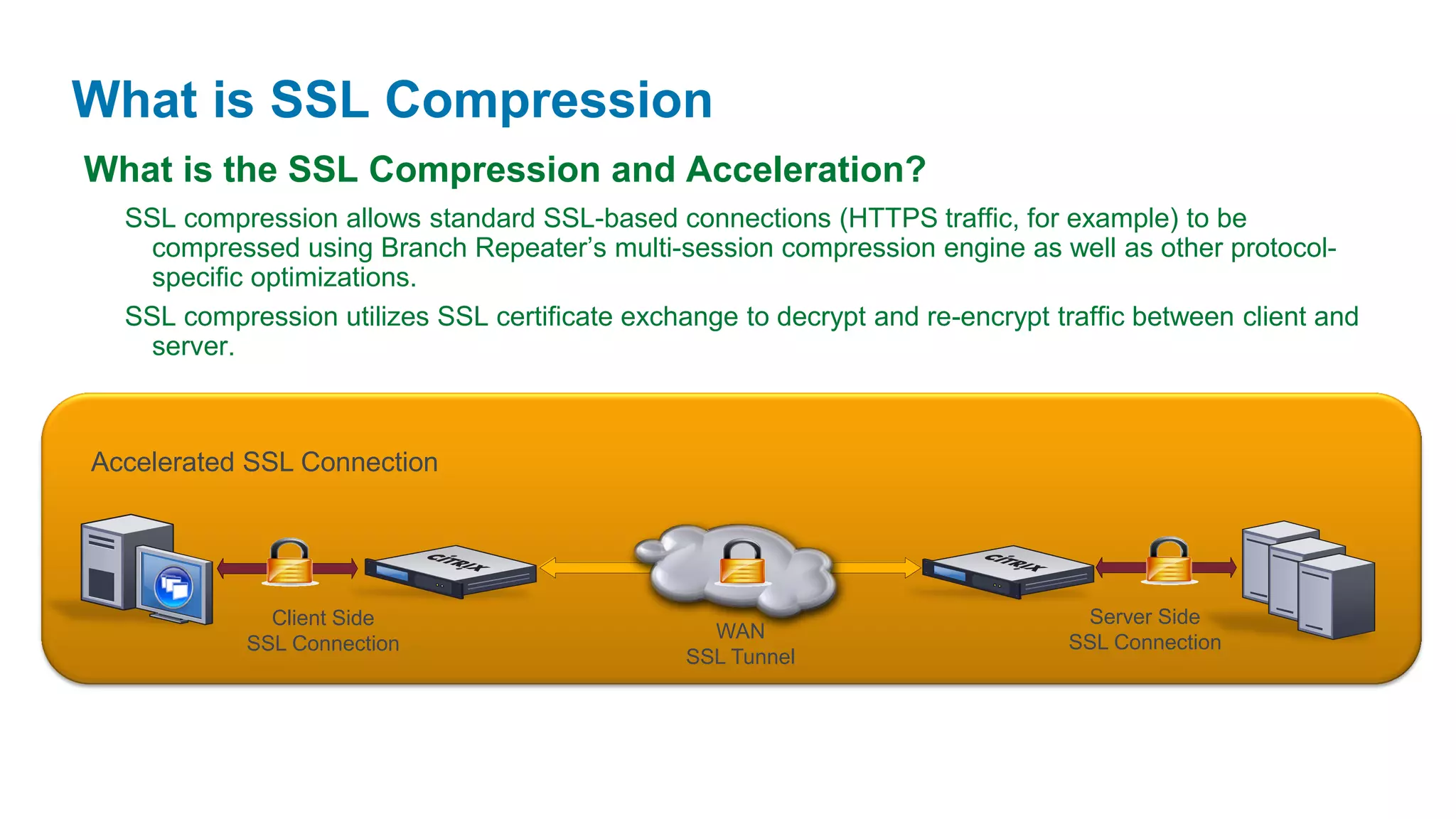
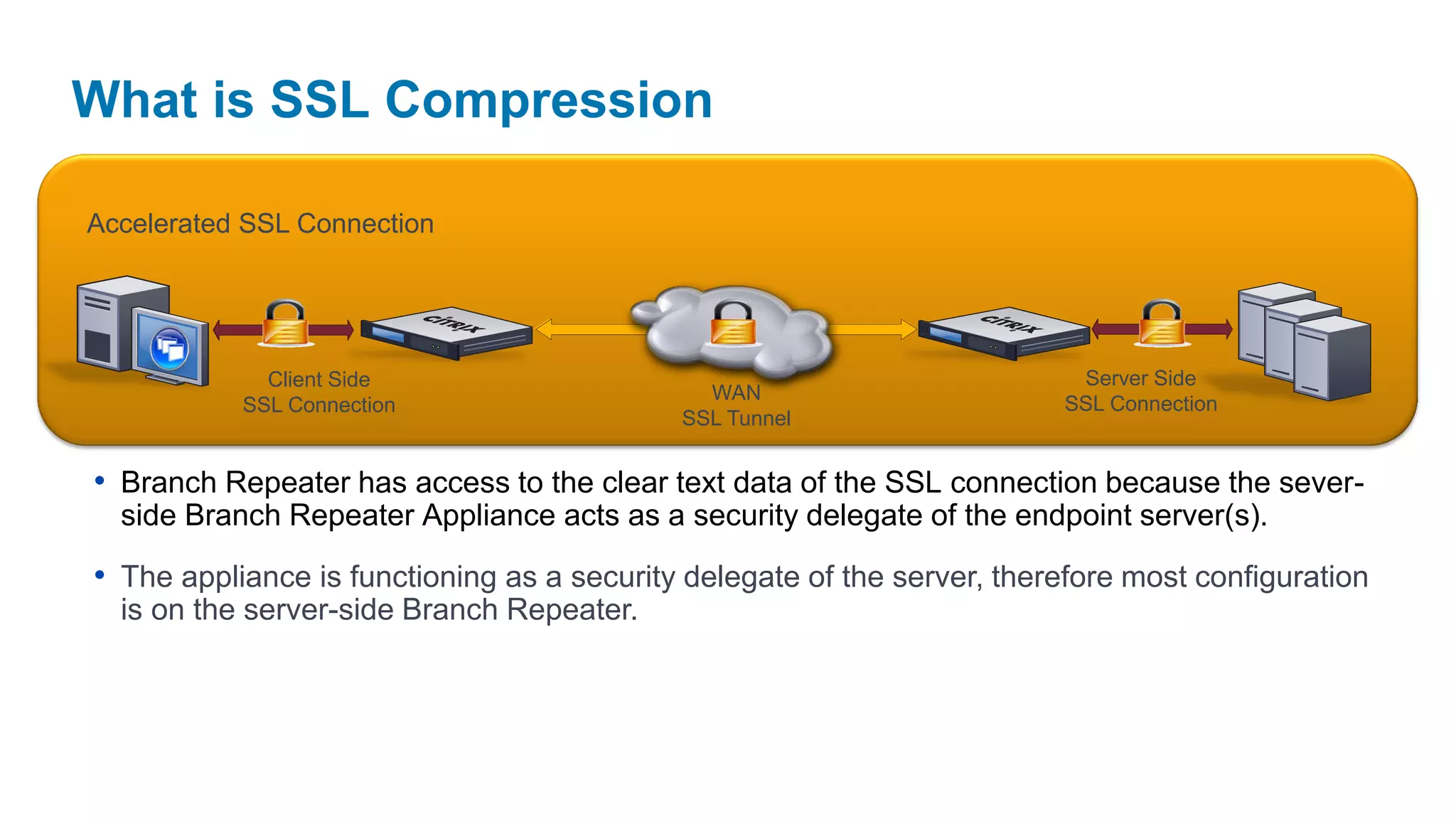
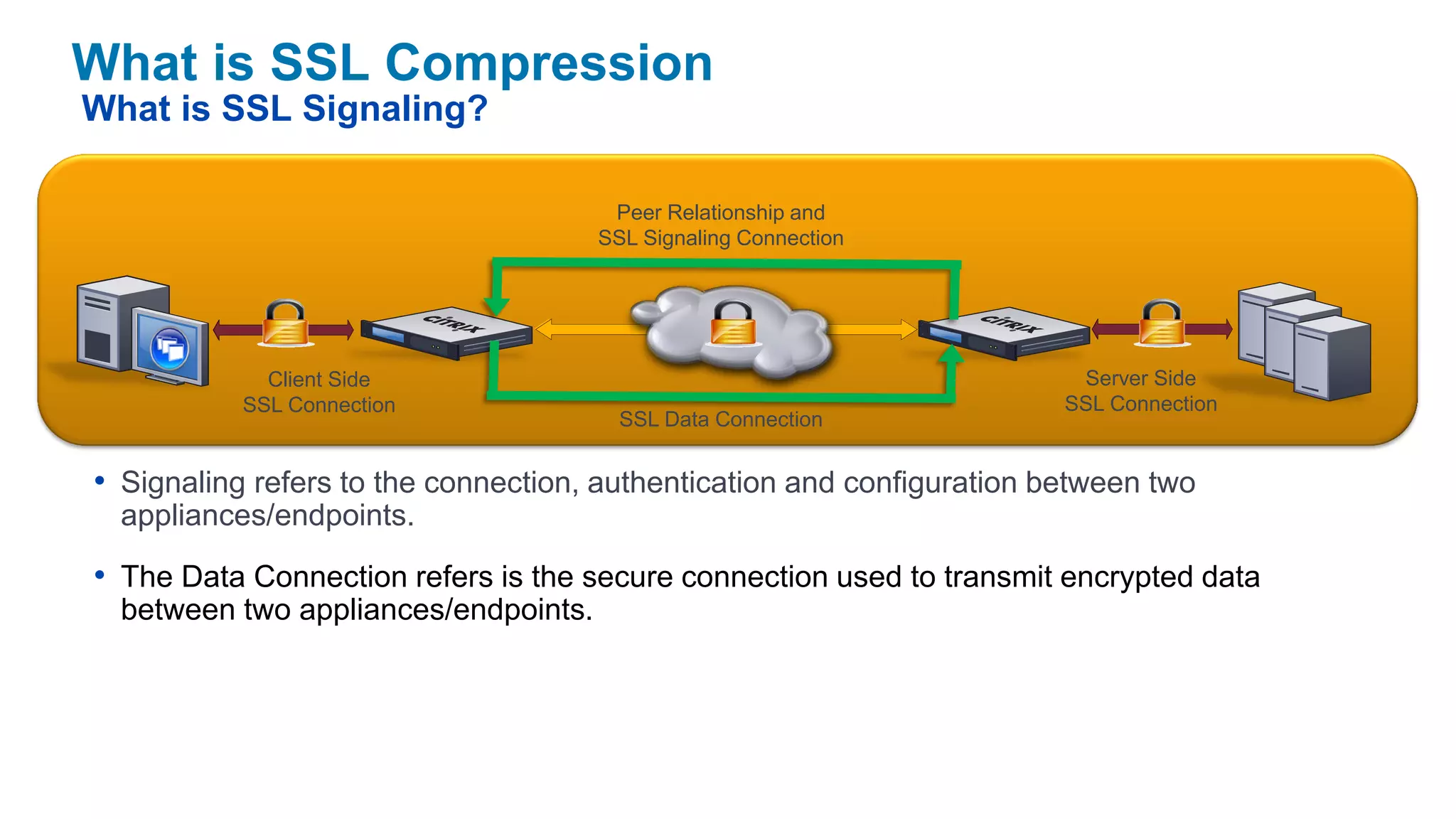
Citrix BranchRepeater provides WAN optimization and acceleration for virtual desktop and application traffic between branch offices and data centers. It uses various techniques like compression, protocol acceleration, and TCP flow control to reduce bandwidth usage and improve performance. The BranchRepeater product family includes physical appliances, a virtual appliance called BranchRepeater VPX, and a software plugin. It provides flexibility in deployment with options for inline, virtual inline, and high availability modes. The latest release added capabilities like SSL traffic acceleration and encryption of appliance disk history.