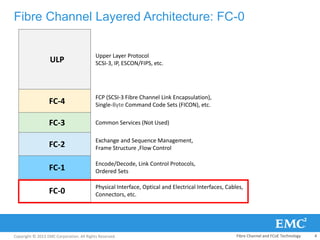
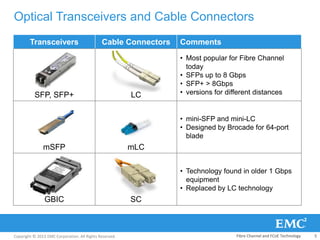
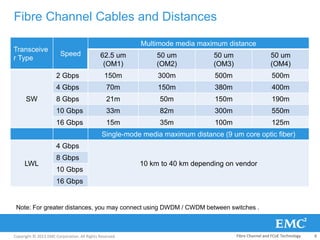
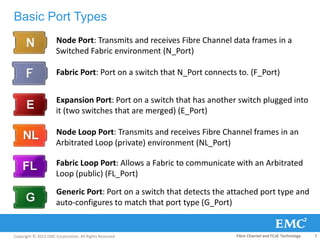
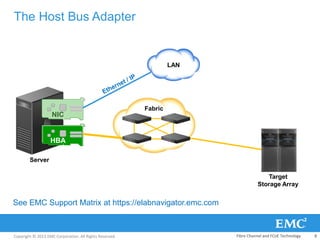
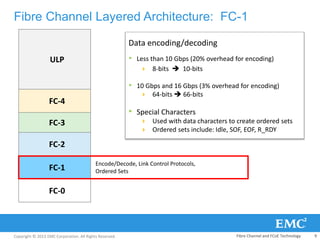
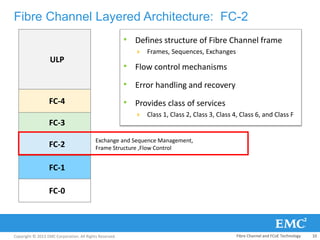
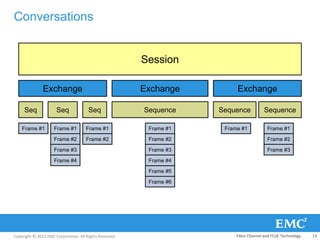
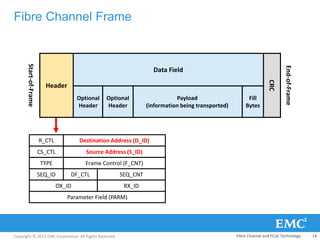
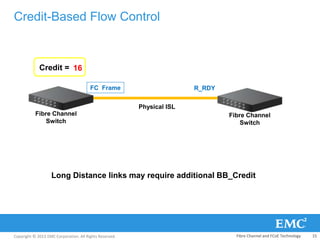
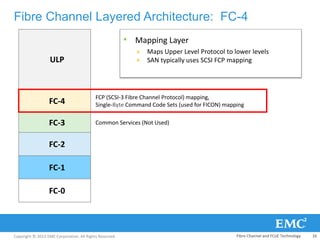
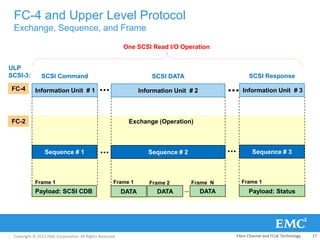
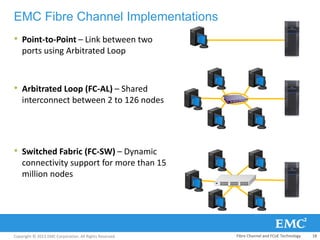
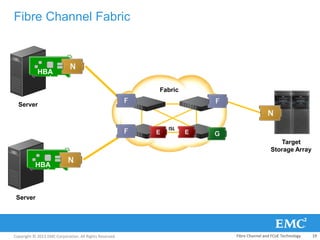
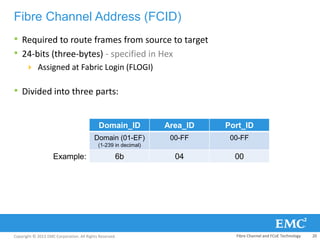
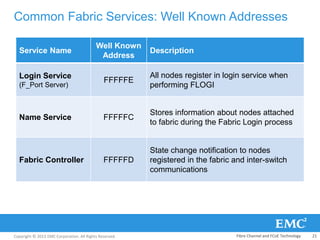
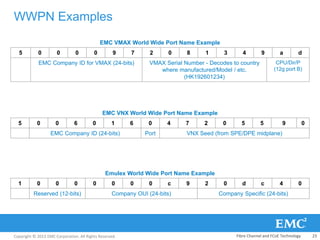
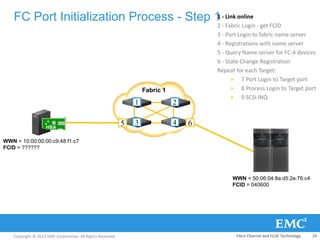
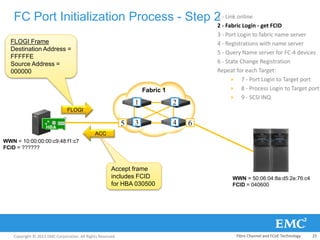
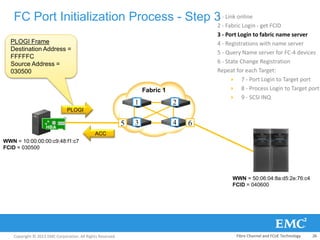
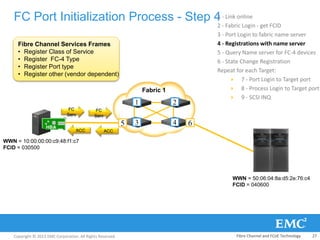
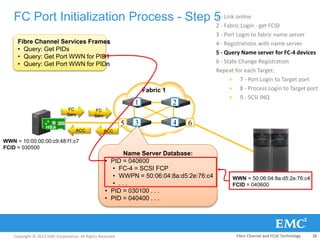
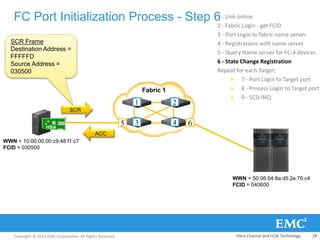
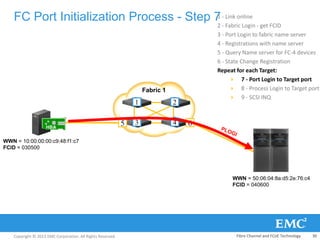
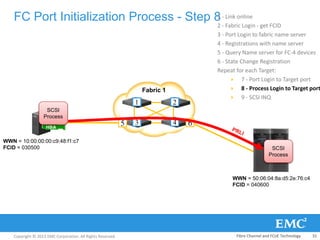
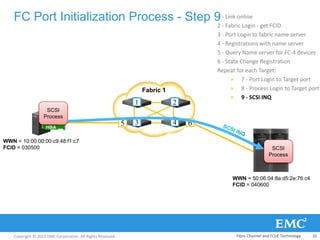
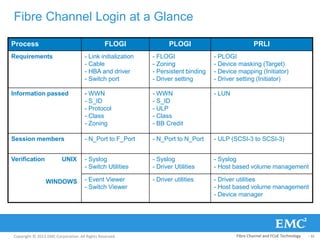
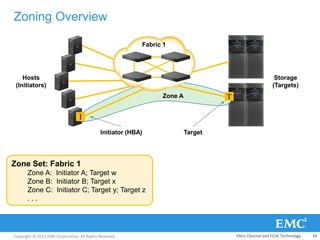
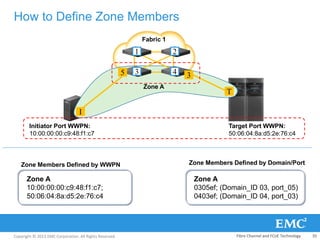
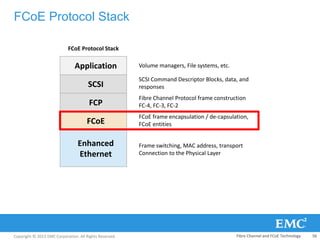
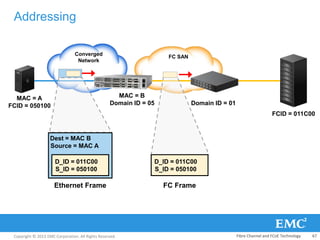
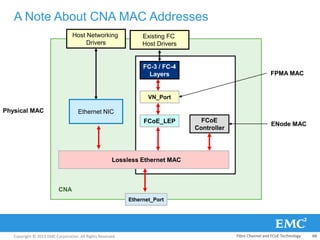
This document provides an overview of Fibre Channel protocol and components. It describes the Fibre Channel layered architecture including FC-0 through FC-4 layers. It covers Fibre Channel frames, exchanges, sequences, flow control, addresses, port initialization process and common fabric services. Key topics include Fibre Channel protocol makeup, components, transceivers, cables, switches, host bus adapters, world wide names, and fabric login process.