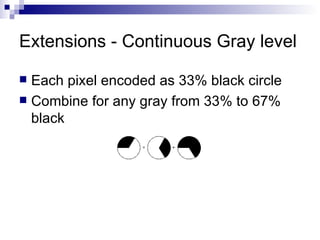
Visual cryptography allows encrypting images such that the decryption can be performed by the human visual system without any computation. It works by splitting an image into shares, such that individual shares reveal no information about the original image but combining a sufficient number of shares reveals the hidden image. The document discusses various schemes for visual cryptography including general k out of n schemes, 2 out of 2 schemes using 2 or 4 subpixels per pixel, 3 out of 3 schemes, and 2 out of 6 schemes. It also covers extensions for color, grayscale, and continuous tone images as well as applications such as voting and banking.



![Model Assume the message consists of a collection of black and white pixels and each pixel is handled separately. Each share is a collection of m black and white subpixels. The resulting picture can be thought as a [ n x m ] Boolean matrix S = [s i,j ] s i,j = 1 if the j-th subpixel in the i-th share is black. s i,j = 0 if the j-th subpixel in the i-th share is white.](https://image.slidesharecdn.com/visual-cryptography-1210753893074072-9/85/Visual-Cryptography-6-320.jpg)