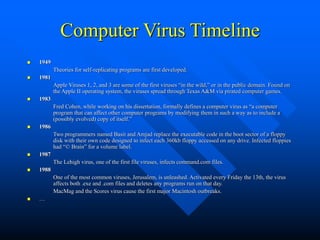
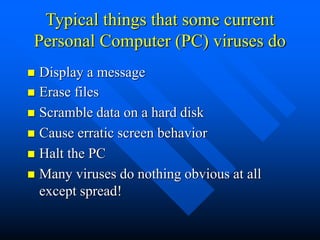
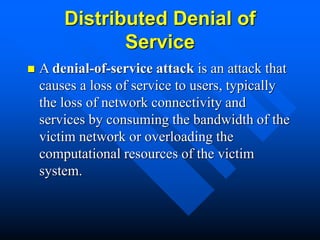
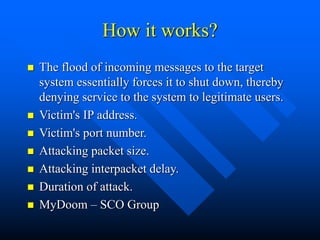
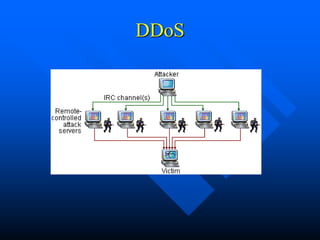
The document discusses the history and nature of computer viruses and worms, defining viruses as programs that attach to legitimate software and replicate themselves. It details significant milestones in the evolution of viruses from the first theories in 1949 to widespread outbreaks like the Melissa virus and MyDoom, highlighting how these malicious programs can disrupt systems. Additionally, it explains the concept of worms as self-replicating programs that exploit network vulnerabilities and emphasizes the importance of prevention measures against such threats.