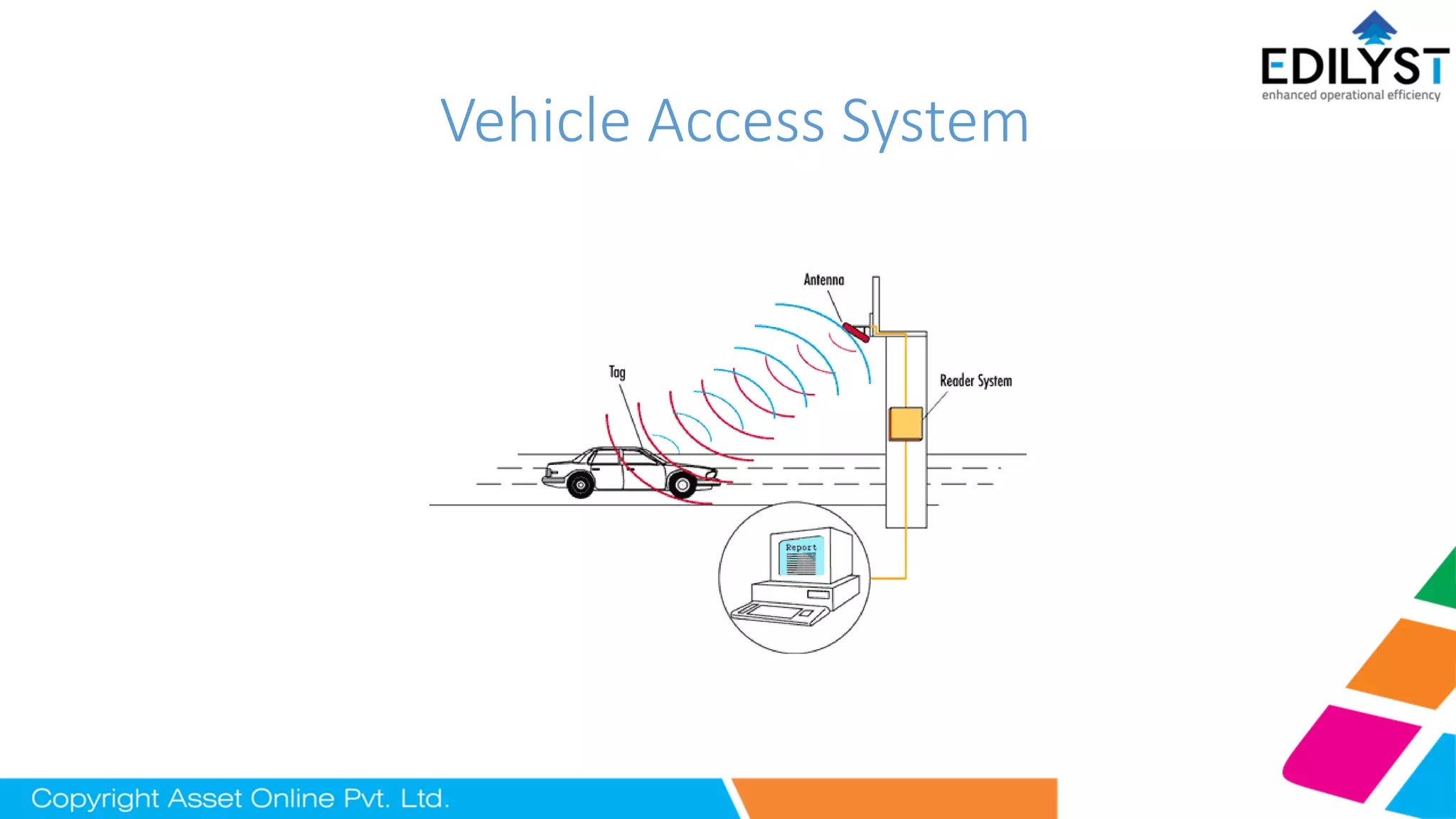
The document outlines the components and functioning of a vehicle access system using RFID technology, detailing how authorized and visitor vehicles are managed through fixed and desktop readers alongside window and web applications. Key features include automated barrier control, real-time tracking of entry and exit, visitor pass issuance, and integration capabilities with third-party ERP systems. The system aims to enhance security, efficiency, and user experience at entry points with benefits including reduced queue times and comprehensive vehicle data tracking.