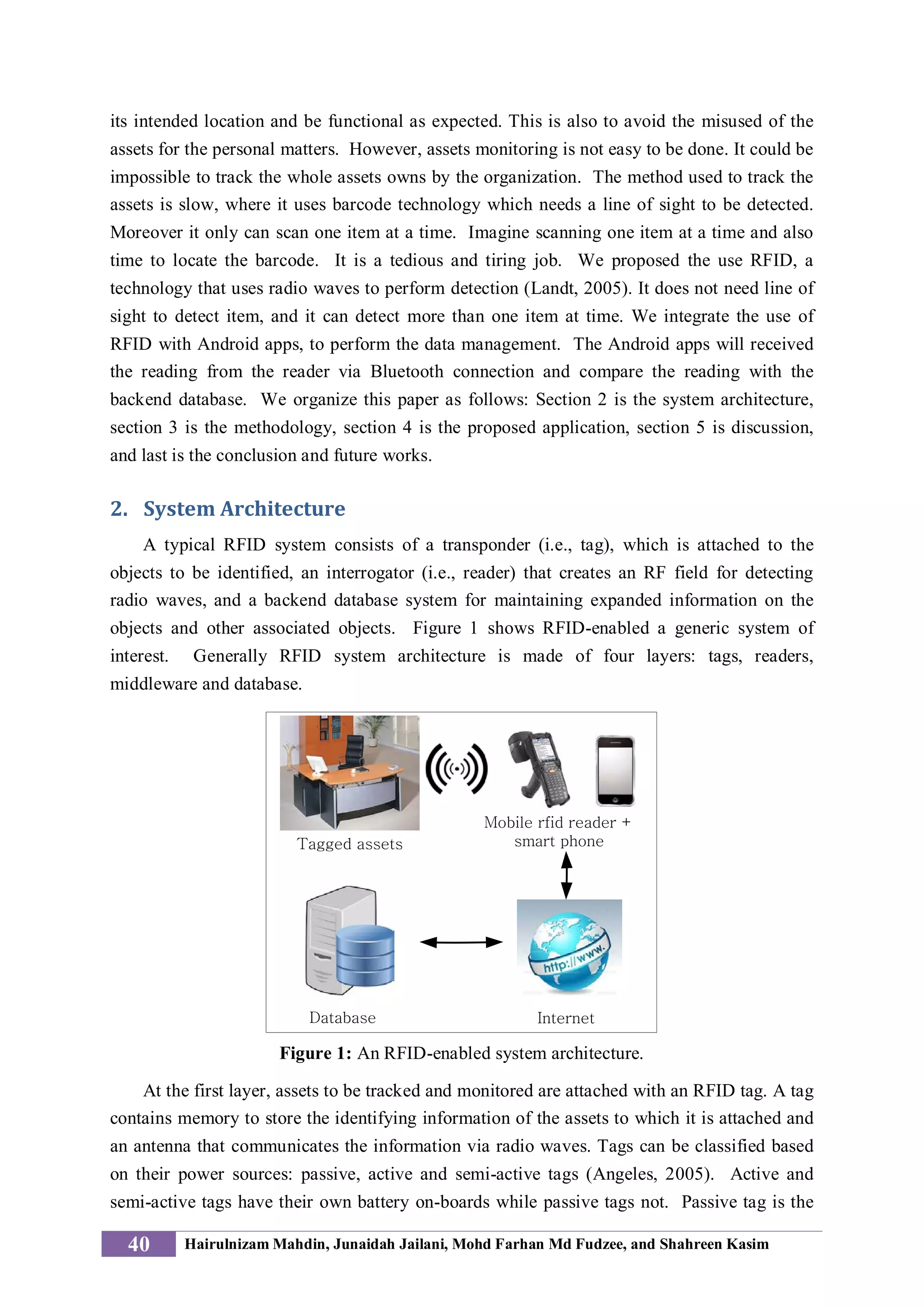
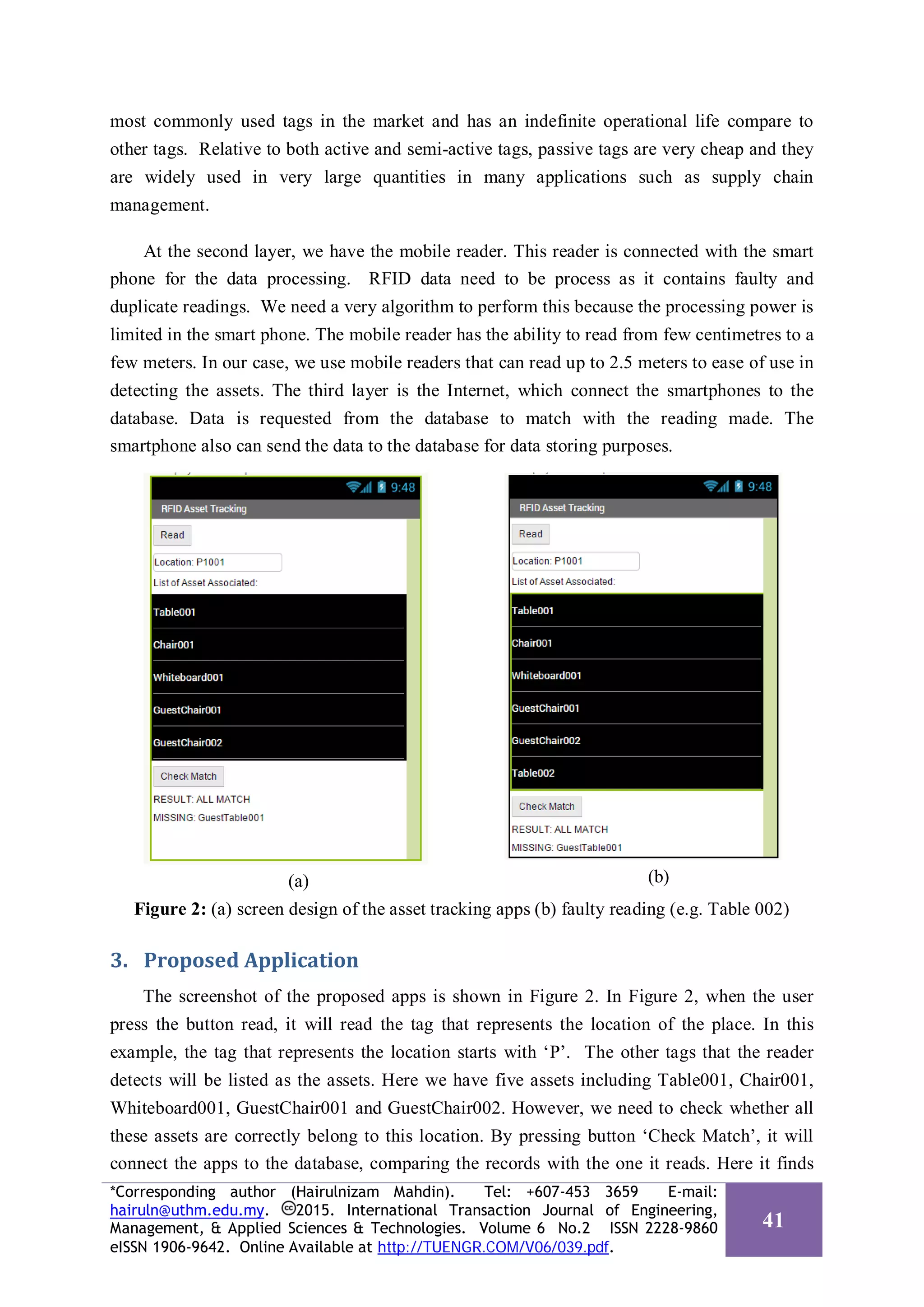
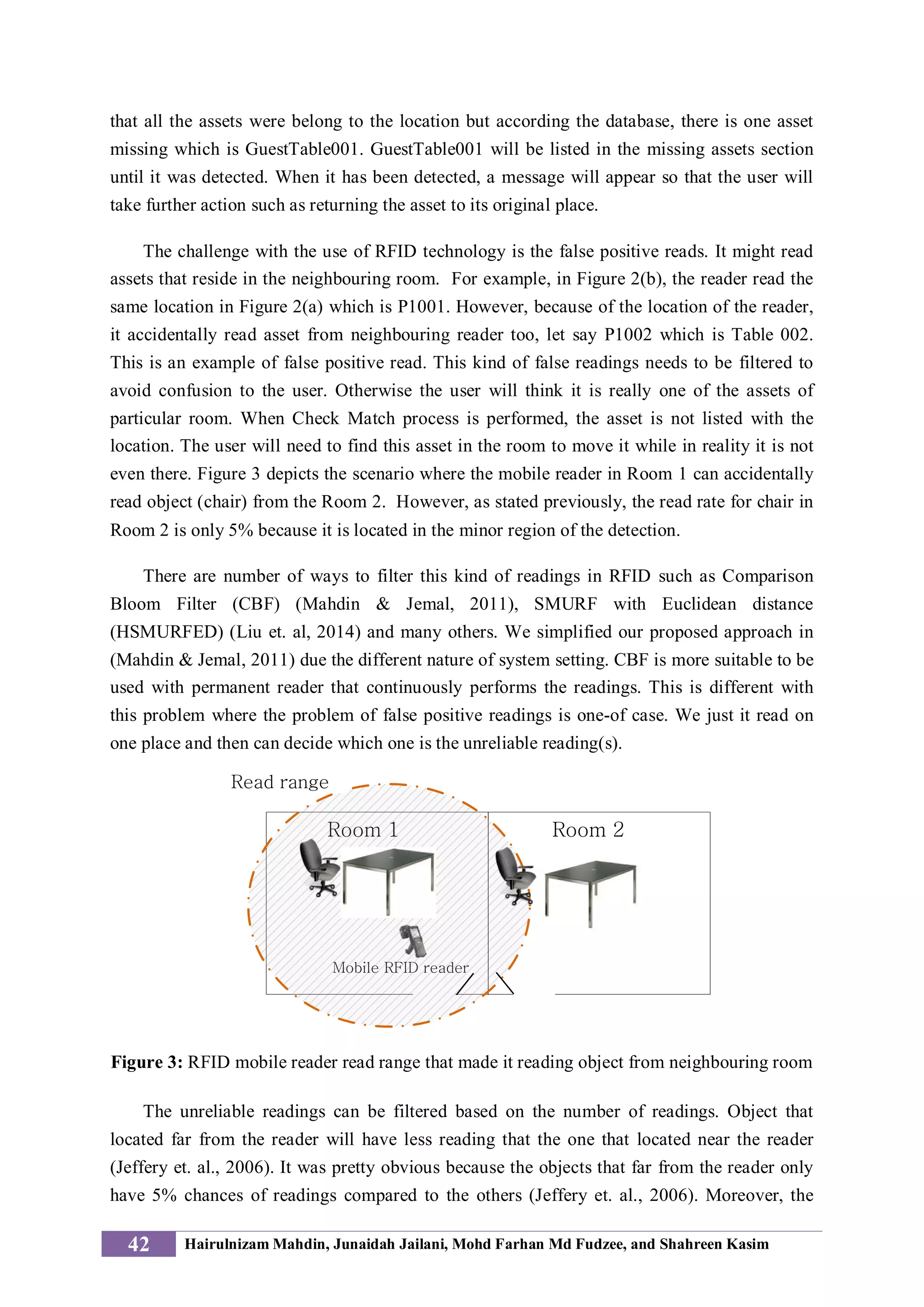
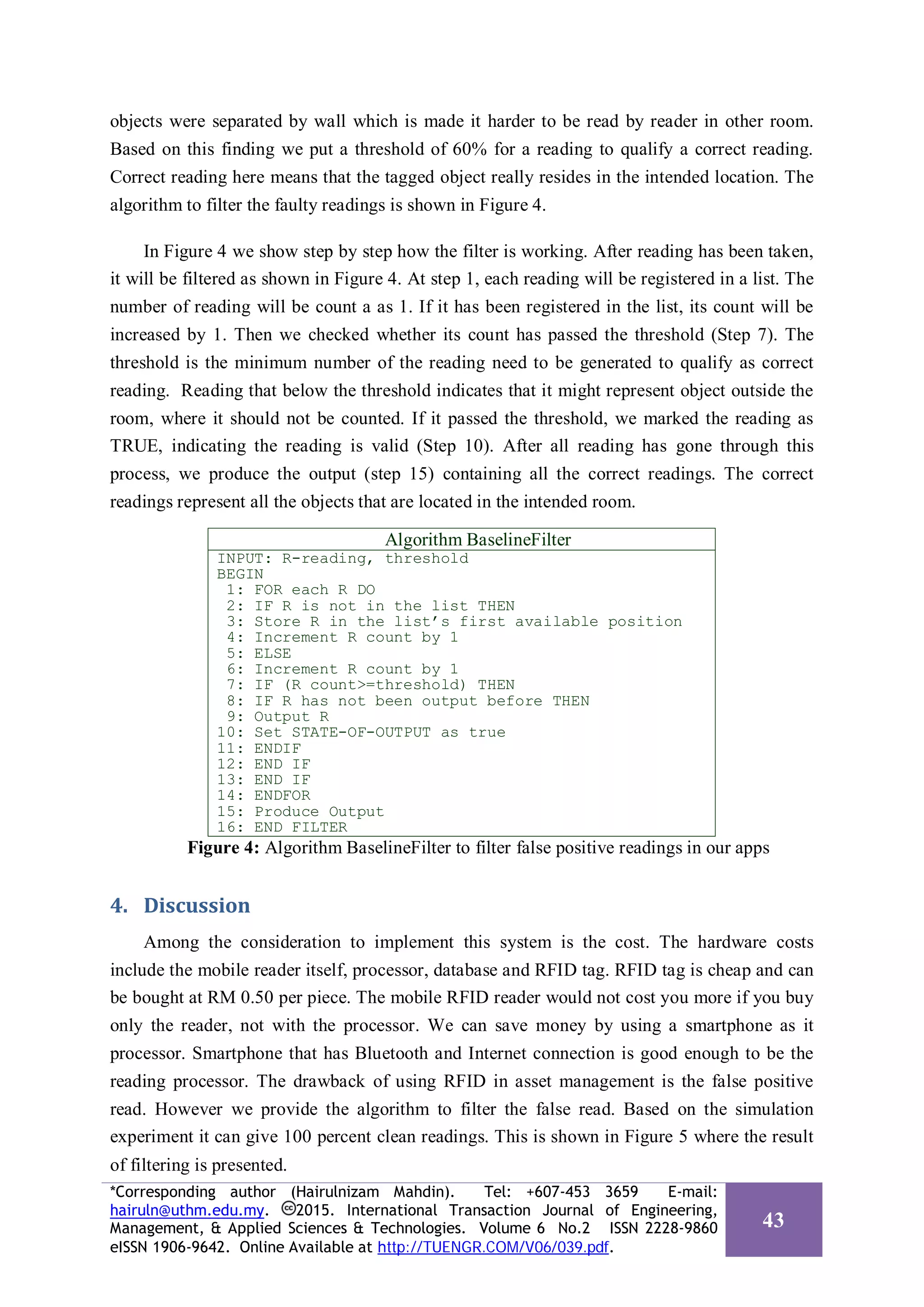
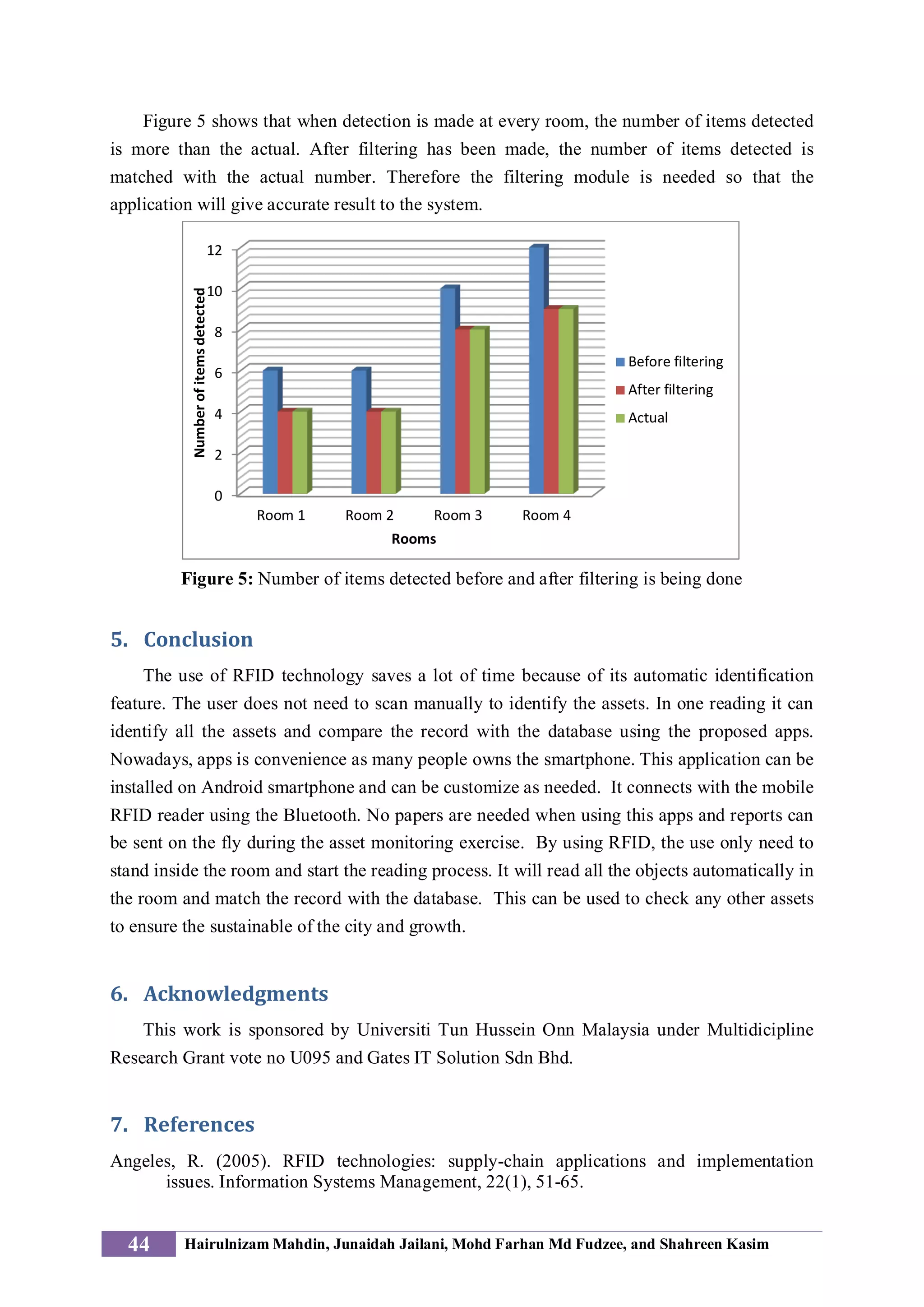
The document discusses the development of a mobile RFID-based asset management system using Android applications, which improves the efficiency of asset tracking in organizations by automating the identification process. It outlines the architecture of the system, including RFID tags, mobile readers, and backend databases, while addressing challenges such as false positive readings. The proposed solution features an algorithm to filter these erroneous readings, ultimately achieving accurate asset location reporting and enhancing overall data management.