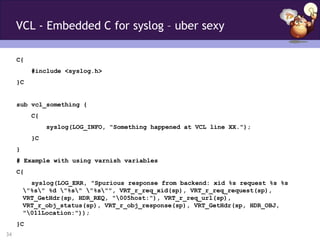
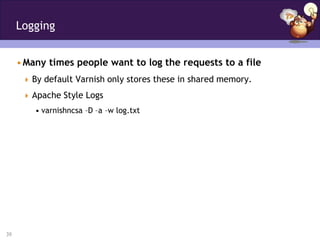
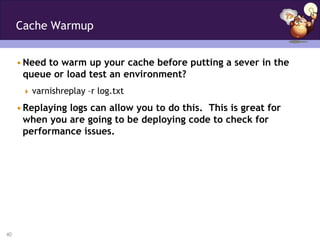
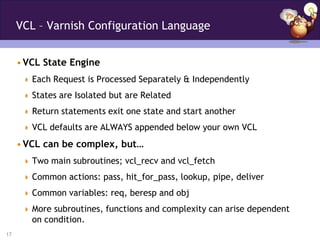
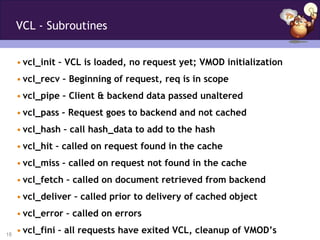
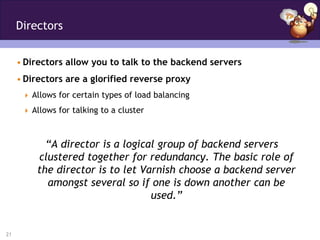
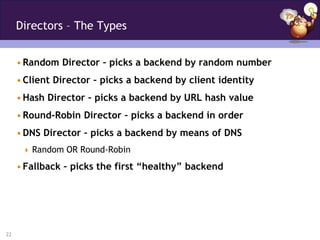
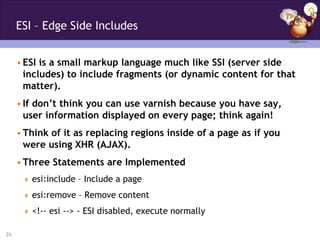
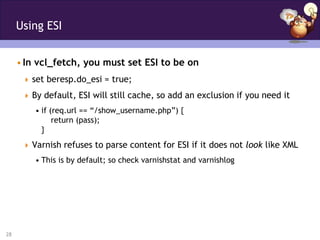
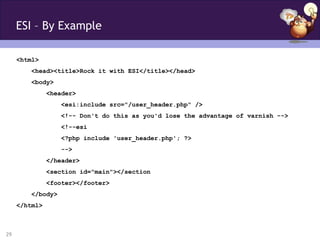
This document summarizes Mike Willbanks' presentation on Varnish to the MinneBar group on April 7, 2012. The presentation covered an introduction to Varnish including what it is and how it works, the benefits of using Varnish to accelerate websites ("The Good"), more advanced Varnish features like VCL and directors ("The Awesome"), and complex Varnish configurations involving ESI, purging, and embedding C code in VCL ("The Crazy"). It also provided overviews of various Varnish command line applications for monitoring and debugging Varnish like varnishtop, varnishstat, and varnishlog.
![Purging Examples
varnishadm -T 127.0.0.1:6082 purge req.url == "/foo/bar“
telnet localhost 6082
purge req.url == "/foo/bar
telnet localhost 80
Response:
Trying 127.0.0.1...
Connected to localhost.
Escape character is '^]'.
PURGE /foo/bar HTTP/1.0
Host: bacon.org
31](https://image.slidesharecdn.com/minnedemovarnish-120407205741-phpapp02/85/Varnish-The-Good-The-Awesome-and-the-Downright-Crazy-31-320.jpg)