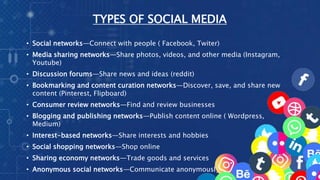
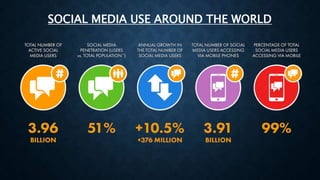
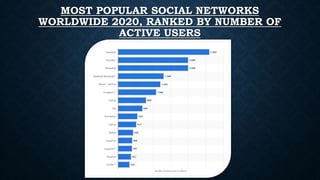
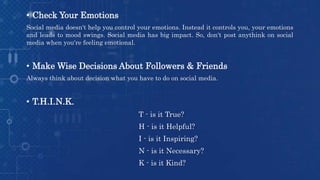
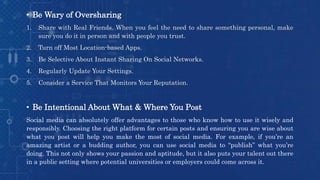
This document discusses responsible use of social media. It defines social media as internet-based technologies that allow sharing of ideas and information through virtual networks. It then lists common social media types like social networks, media sharing, forums, and more. Popular platforms are identified as Facebook, Instagram, Twitter, YouTube, and others. Both advantages like building relationships and disadvantages like addiction and privacy issues are covered. The document concludes by providing tips for using social media responsibly, such as being friends with parents, thinking before posting, and being wary of oversharing personal information.