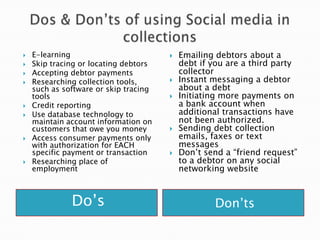
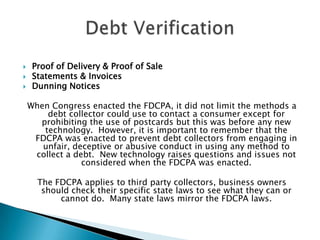
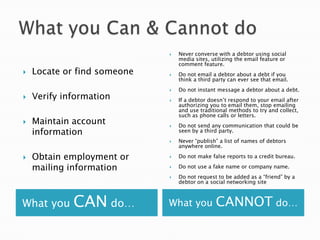
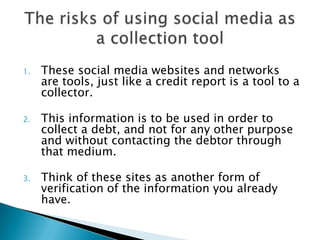
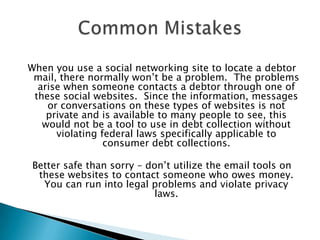
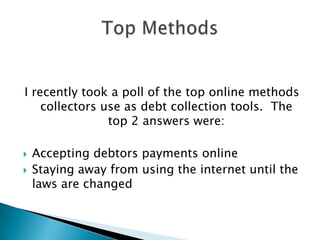
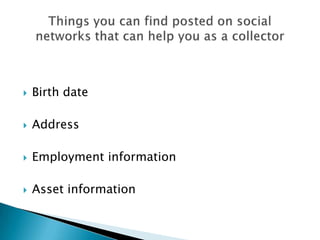
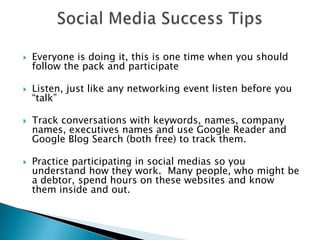
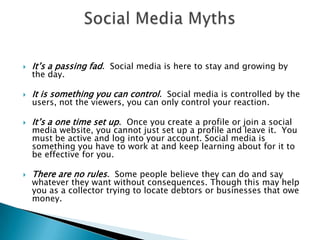
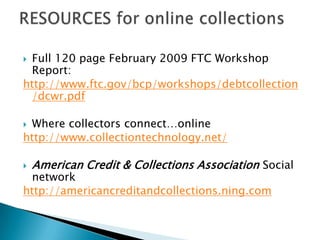
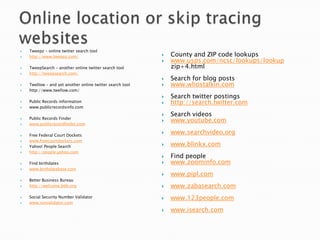
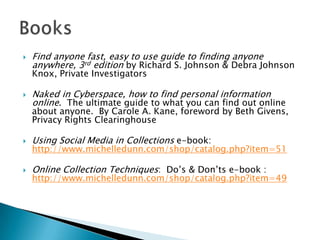
The presentation by Michelle Dunn focuses on the use of social media in debt collection, highlighting the risks, laws, and common mistakes that collectors face when navigating this new communication landscape. It discusses how collectors can utilize social networking sites to locate debtors while adhering to regulations such as the Fair Debt Collection Practices Act (FDCPA). Key takeaways include the importance of knowing what communication methods are permissible, the potential legal pitfalls of using social media, and the necessity for ongoing engagement with these platforms to achieve effective collections.