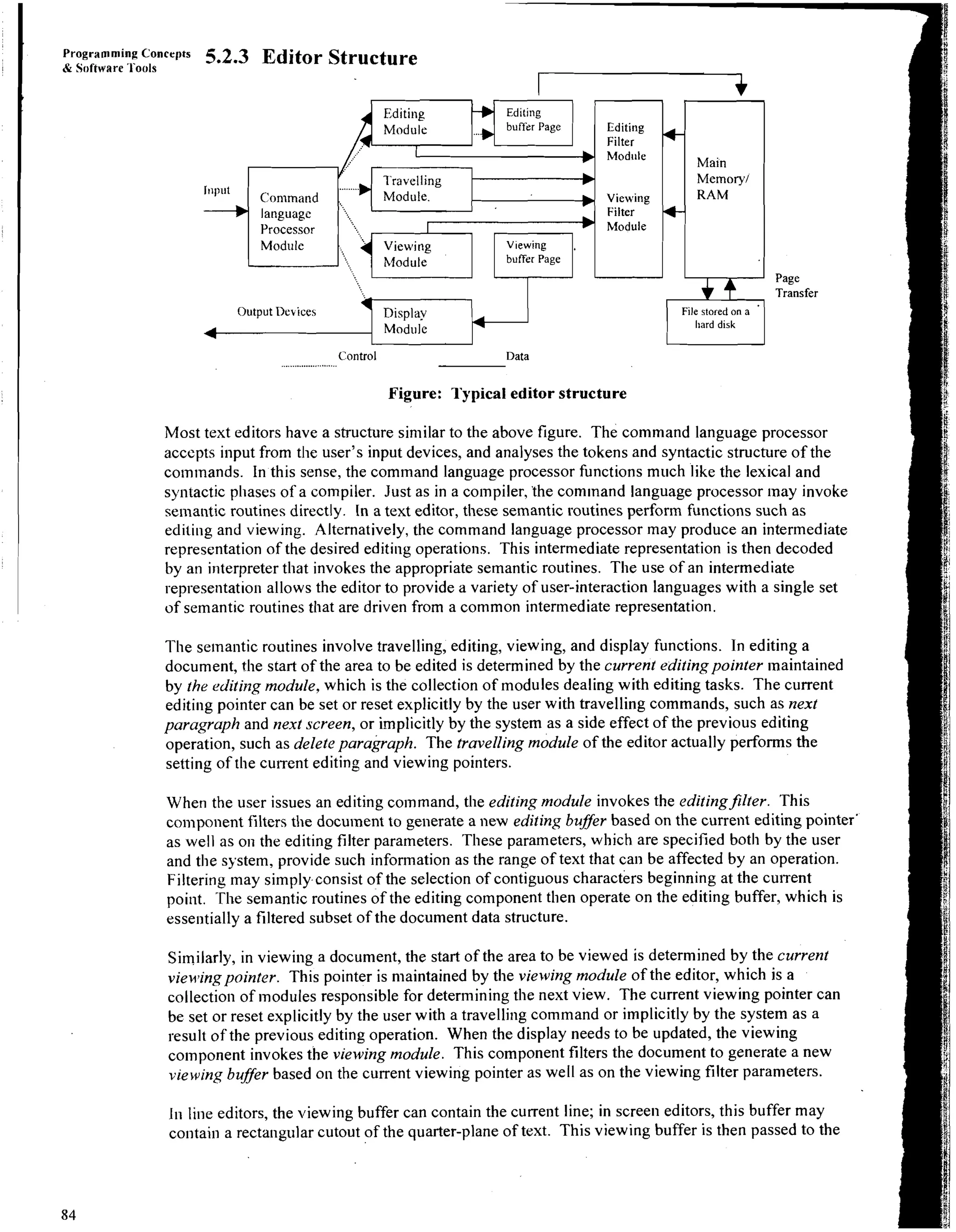
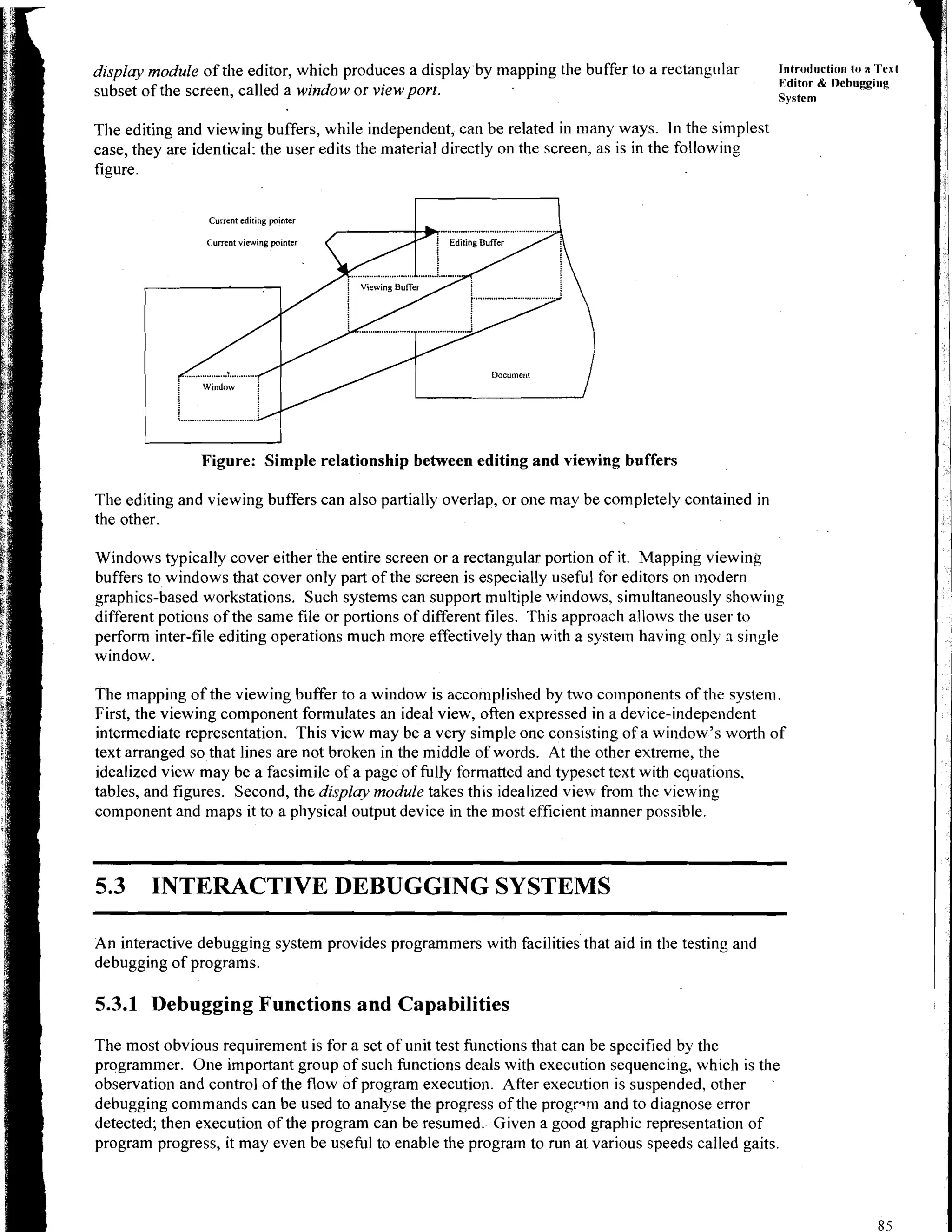
This document section introduces a text editor and debugging system. It defines a text editor as a program that enables creating and editing text files, and notes the distinction from word processors. An interactive debugging system provides programmers tools to test and debug programs. The objectives are to define these concepts and discuss important functions and characteristics of future debugging systems.