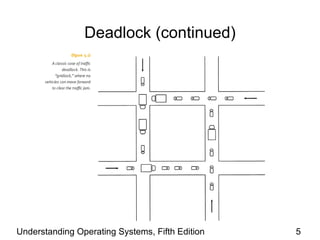
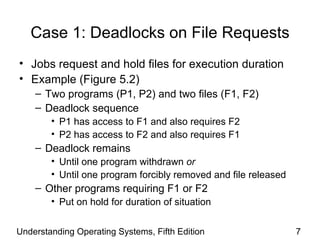
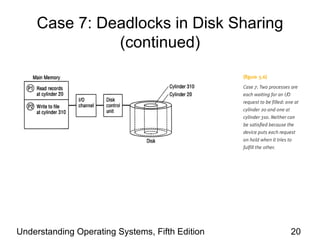
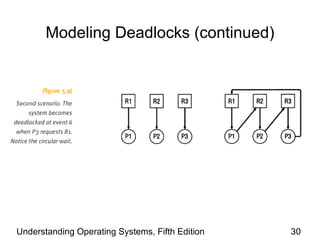
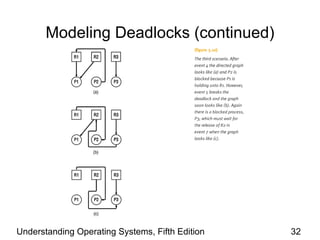
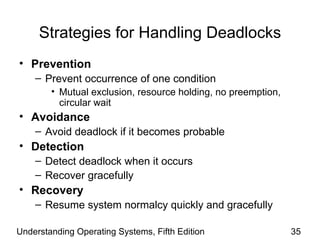
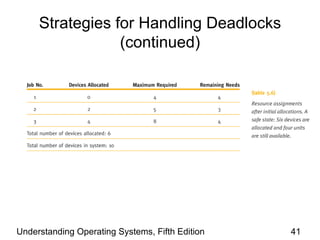
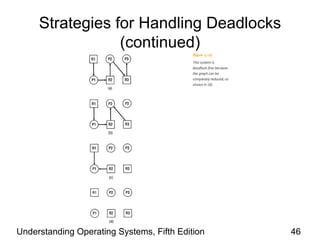
The document discusses deadlocks, which occur when two or more processes are blocked waiting for resources held by each other in a cyclic manner. It describes seven common cases of deadlock involving file requests, databases, dedicated devices, spooling, networks, and disk sharing. It also outlines the four conditions required for deadlock, detection and modeling methods using directed graphs, and strategies for prevention, avoidance, detection, and recovery from deadlocks.