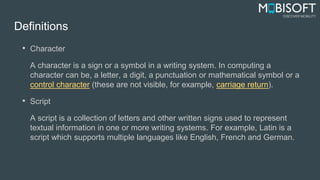
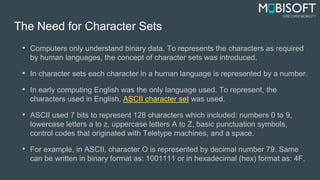
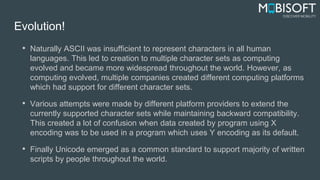
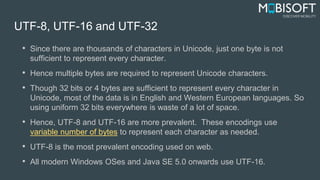
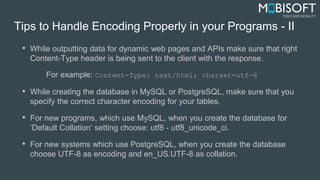
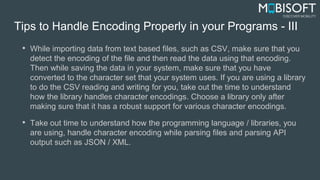
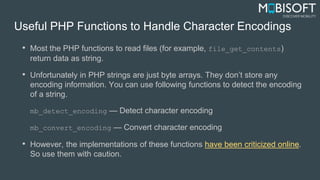
This document discusses character encodings and provides tips for properly handling encodings in programming. It begins with definitions of characters, scripts, and the need for character sets. It then discusses commonly used character sets like ASCII and Unicode. UTF-8, UTF-16, and UTF-32 encodings are explained as they allow representing all Unicode characters using variable number of bytes. The document concludes with programming language-specific tips and functions for detecting, parsing, and writing encodings in languages like PHP, Java, Objective-C, and C#.

![How to Handle Character Encoding in Java
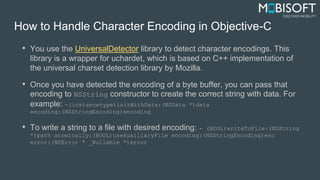
• In Java, you can use InputStreamReader.getEncoding()to detect encoding.
• The juniversalchardet library which is a Java port of universalchardet library
from Mozilla can also be used to detect character encodings in Java.
• Once you have a byte array of data and you have detected the character
encoding for it, you can use the following String constructor to create a string
with proper encoding: public String(byte[] bytes, Charset charset)
• To save a file with desired character encoding, you need to pass the proper
character set to the OutputStreamWriter class. Here is an example of how to
do it.](https://image.slidesharecdn.com/mipl-understanding-character-encoding-160127045731/85/Understanding-Character-Encodings-14-320.jpg)