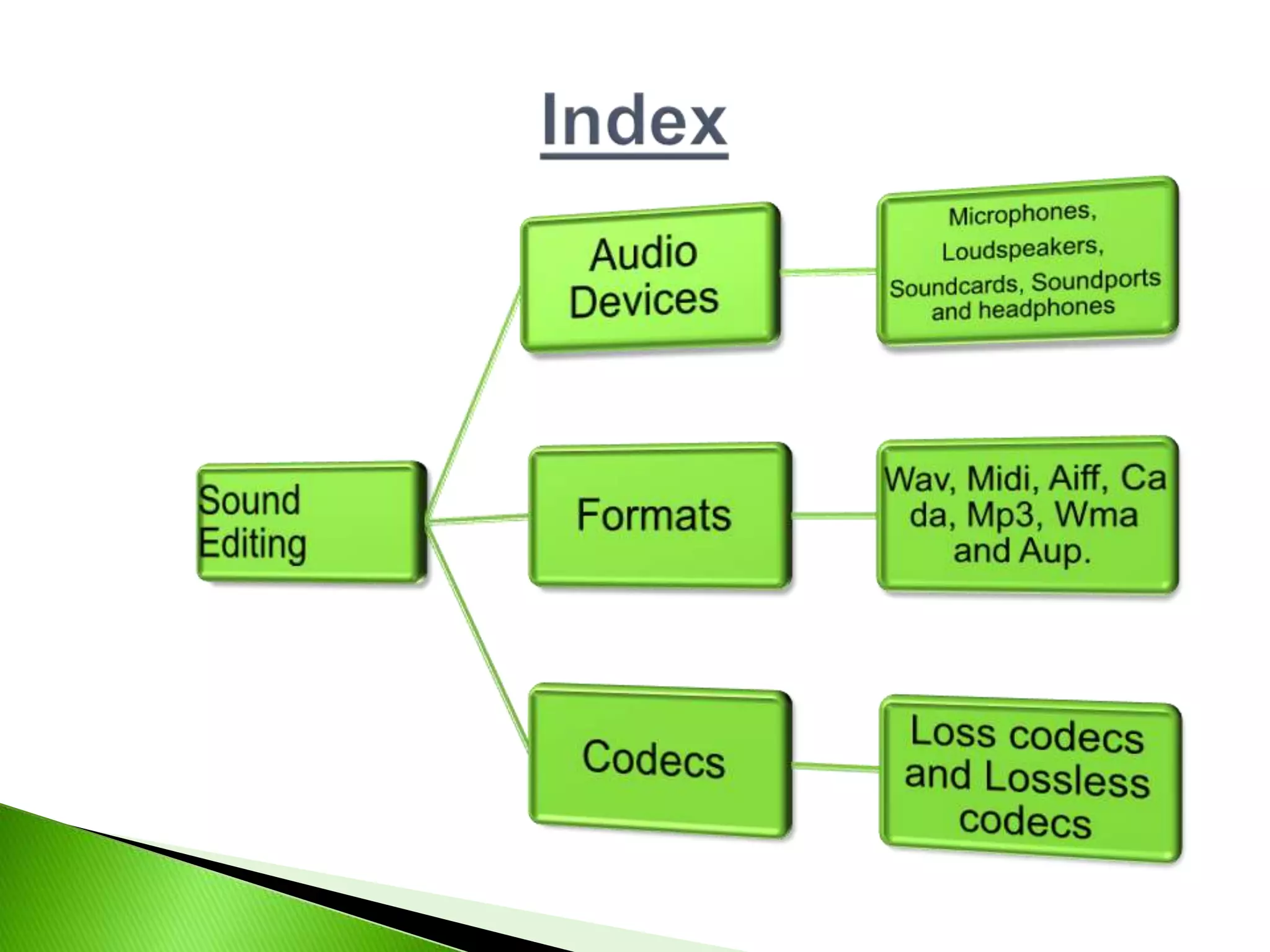
Audio devices allow you to play or record audio and come in two types: input and output. Audio formats store digital audio data using different file types like MP3, WAV, and WMA. Codecs encode or decode audio streams and can be either lossy, which reduces quality for more compression, or lossless, which retains all original audio information. Common input devices are microphones while output devices include speakers and headphones.