Embed presentation
Downloaded 12 times
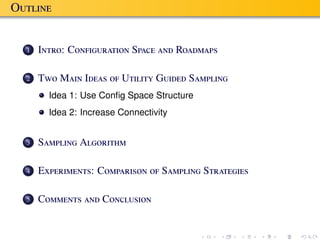

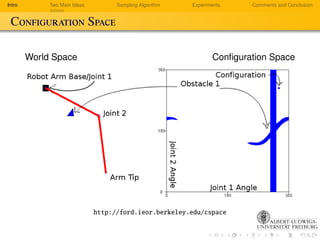
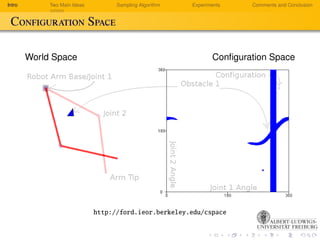







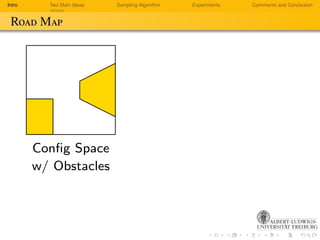


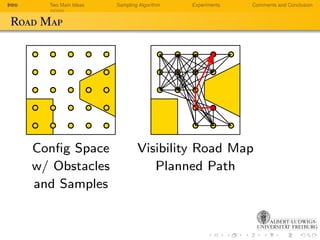



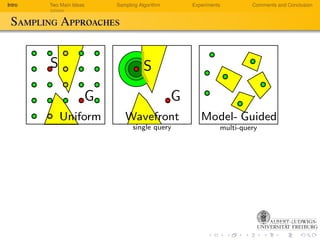
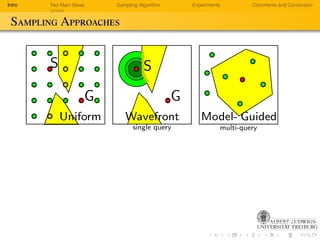
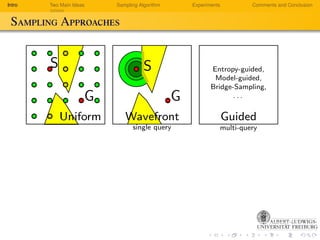




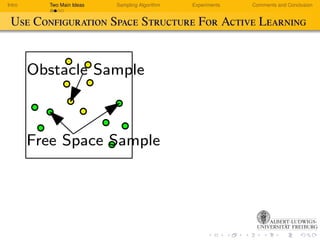













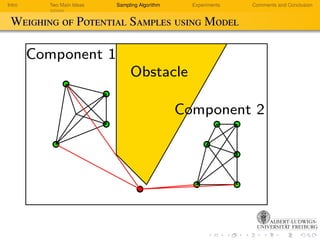








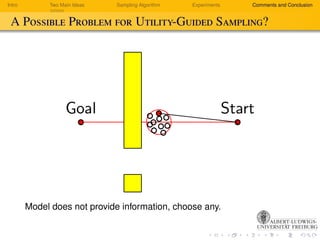





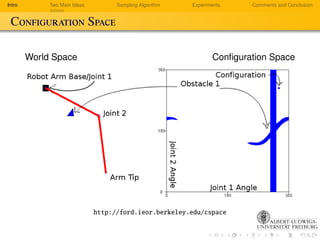
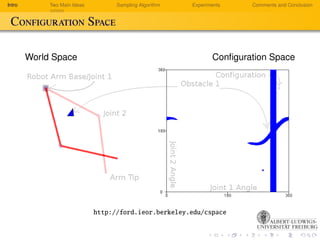
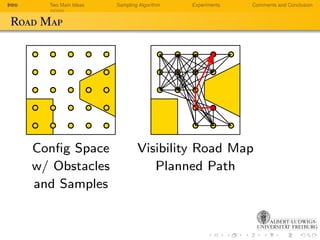
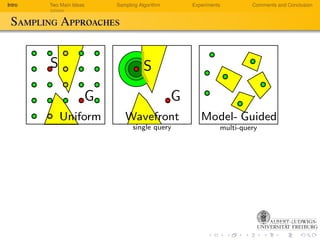
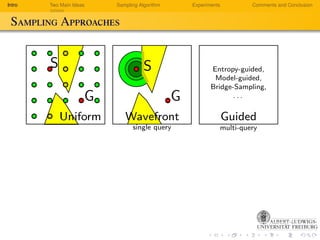
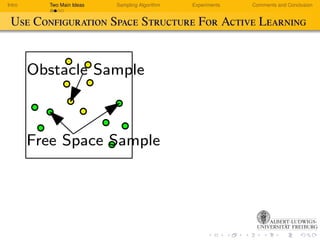
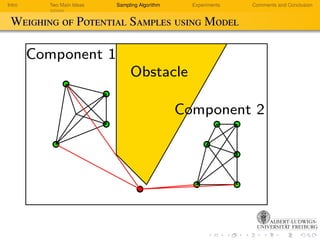
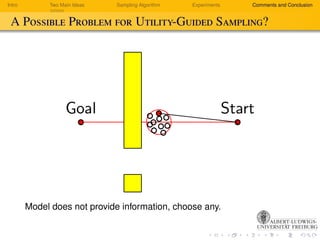
This document discusses sampling algorithms for quickly sampling in high-dimensional configuration spaces. It introduces configuration space and roadmaps, describes two main ideas for improving sampling, and presents a utility-guided multi-query sampling algorithm evaluated in experiments.