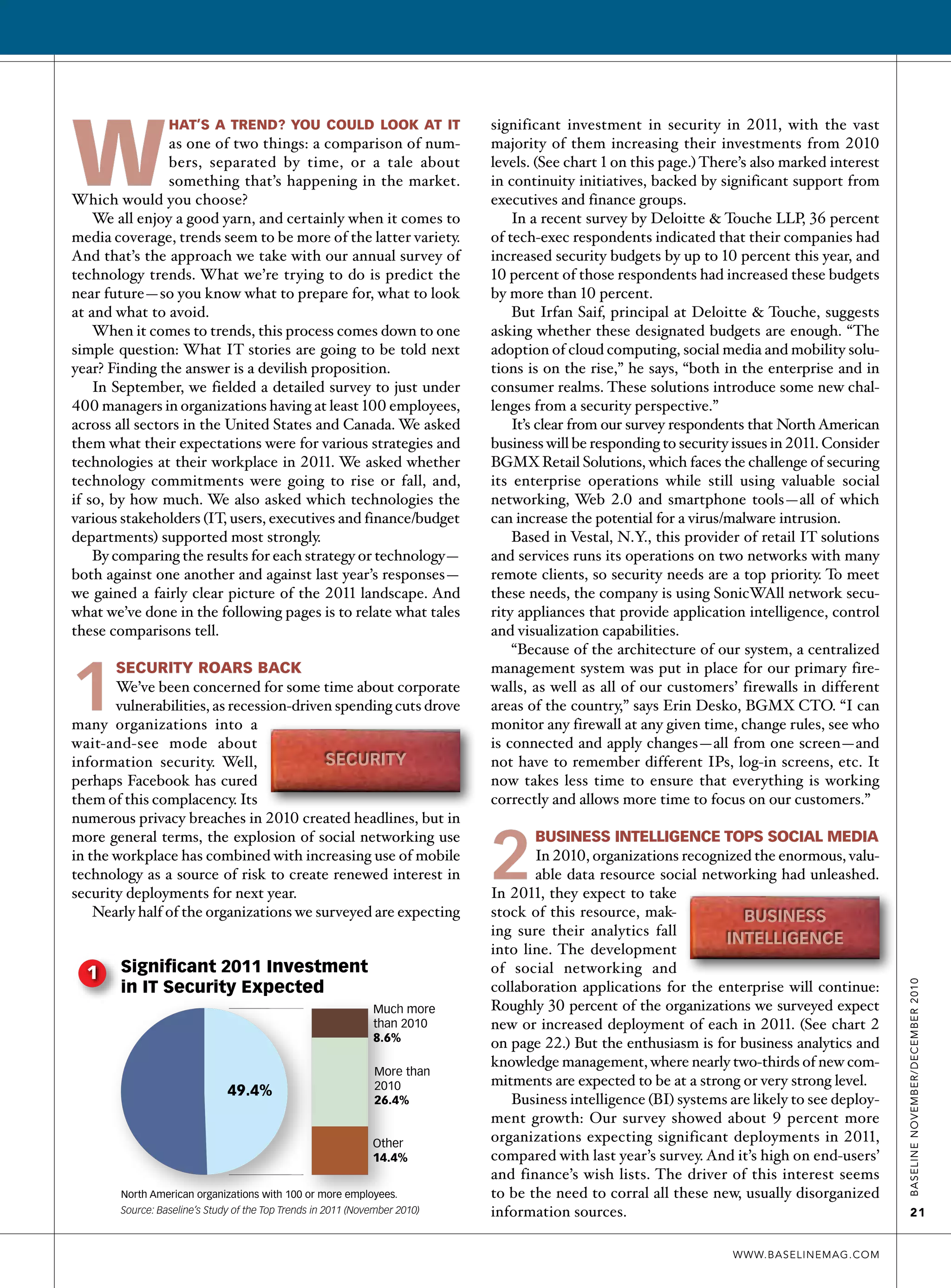
1. Security enjoys a revival as organizations significantly increase security budgets and prioritize continuity initiatives in response to increased risks from social networking, mobile technologies, and cloud computing. Nearly half of surveyed organizations expect significantly higher security spending in 2011.
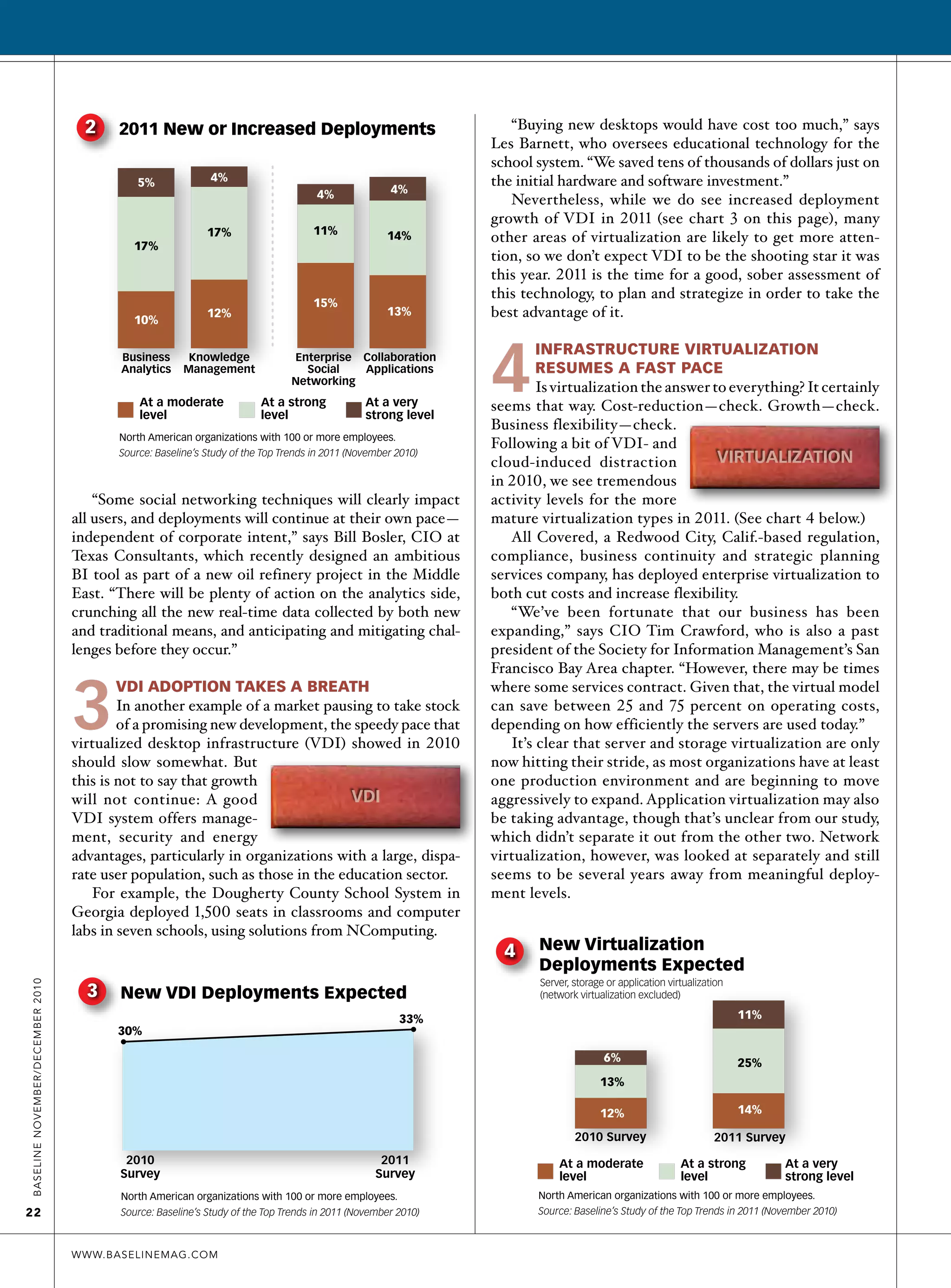
2. While interest remains in social media and collaboration tools, organizations are more focused on deploying business intelligence systems to analyze large amounts of new data from these sources. Two-thirds expect strong commitment to business analytics and knowledge management in 2011.
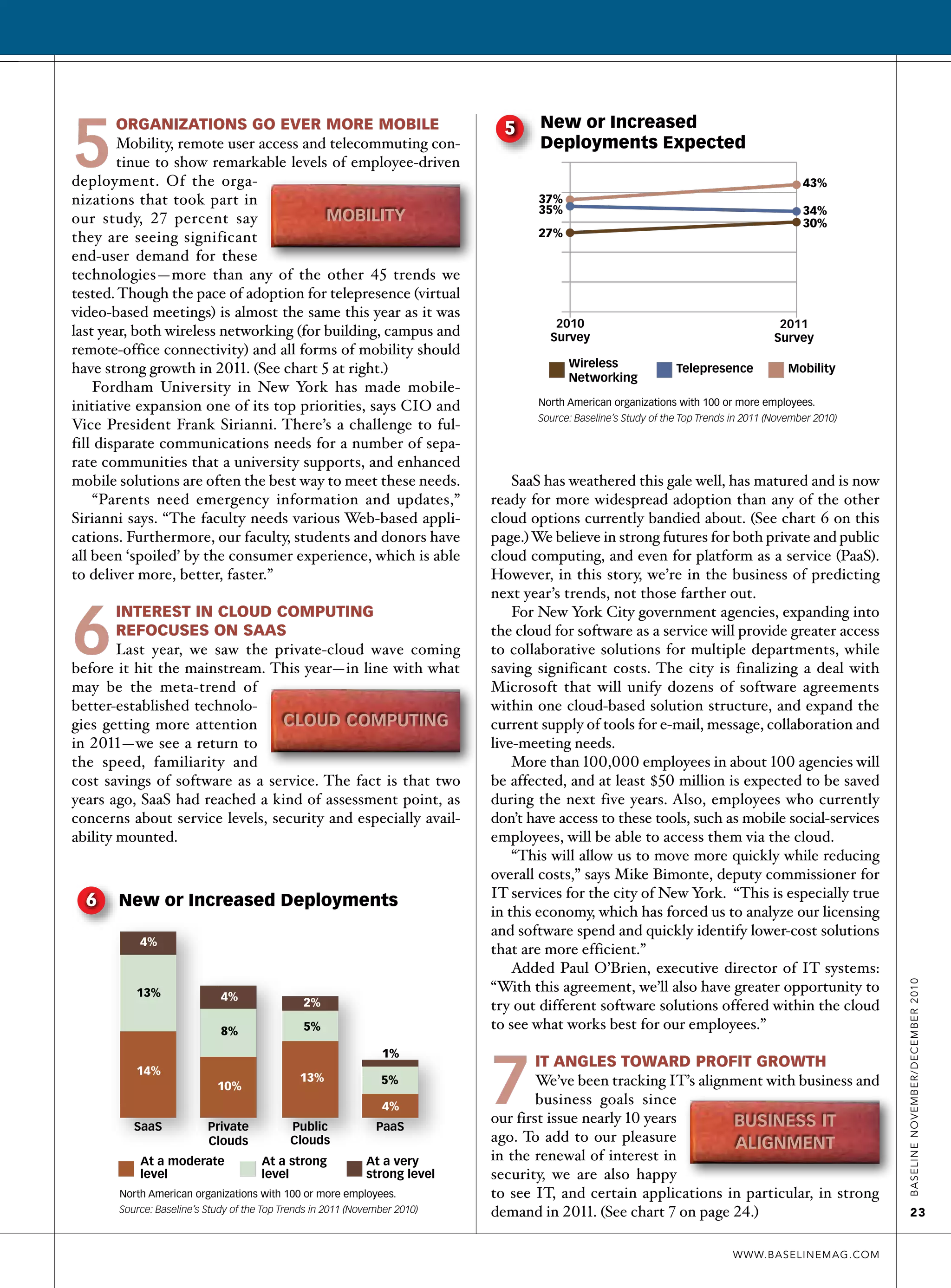
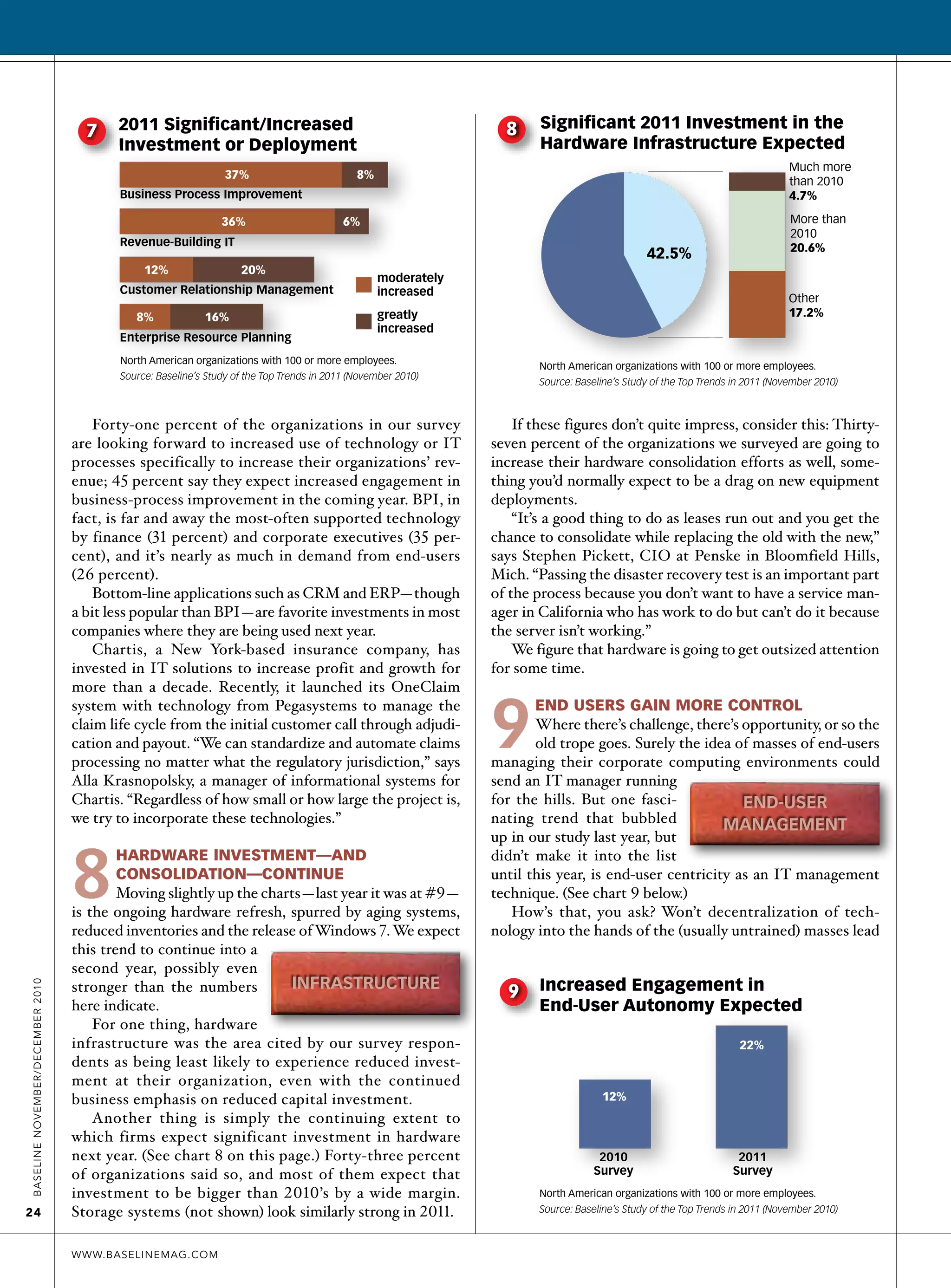
3. Virtual desktop infrastructure (VDI) adoption grew rapidly in 2010 but is expected to slow somewhat as organizations take time to evaluate the technology's advantages and strategize its use. Server, storage, and application virtualization deployments are anticipated