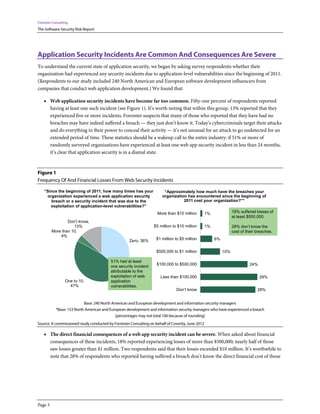
This document summarizes the results of a survey about application security. It finds that 51% of respondents had experienced at least one web application security incident since 2011, with 18% reporting losses of at least $500,000. While many organizations employ security measures, few take a holistic strategic approach. There is also often a disconnect between development and security teams. To improve, companies need to integrate security into development from the start and better align development and security goals.
![Forrester Consulting
The Software Security Risk Report
Table Of Contents
Executive Summary ................................................................................................................................................................................. 2
Application Security Incidents Are Common And Consequences Are Severe ........................................................................... 3
Organizations Must Take A Holistic Approach To Application Security .................................................................................... 7
App Development And Security Must Better Align For Optimized Results ............................................................................. 12
Key Recommendations ......................................................................................................................................................................... 16
Appendix A: Methodology................................................................................................................................................................... 17
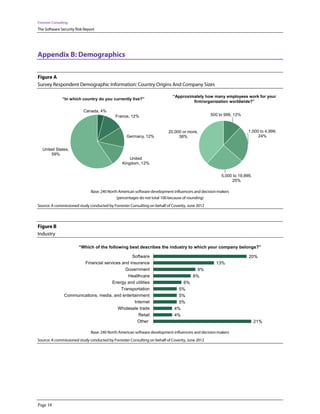
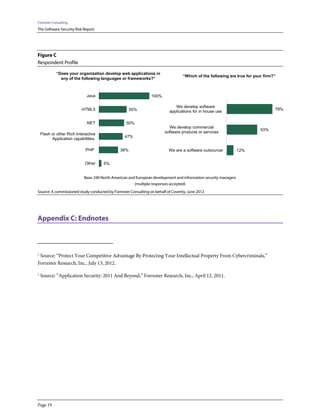
Appendix B: Demographics ................................................................................................................................................................. 18
Appendix C: Endnotes .......................................................................................................................................................................... 19
© 2012, Forrester Research, Inc. All rights reserved. Unauthorized reproduction is strictly prohibited. Information is based on best available resources.
Opinions reflect judgment at the time and are subject to change. Forrester®, Technographics®, Forrester Wave, RoleView, TechRadar, and Total
Economic Impact are trademarks of Forrester Research, Inc. All other trademarks are the property of their respective companies. For additional
information, go to www.forrester.com. [1-HMGX0Z]
About Forrester Consulting
Forrester Consulting provides independent and objective research-based consulting to help leaders succeed in their organizations. Ranging in
scope from a short strategy session to custom projects, Forrester’s Consulting services connect you directly with research analysts who apply
expert insight to your specific business challenges. For more information, visit www.forrester.com/consulting.
Page 1](https://image.slidesharecdn.com/the-software-security-risk-report-120920004737-phpapp01/85/The-software-security-risk-report-2-320.jpg)