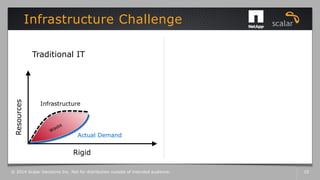
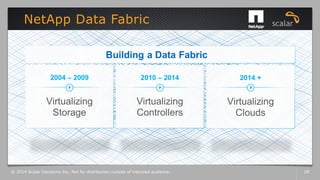
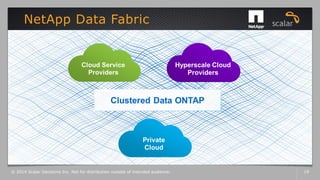
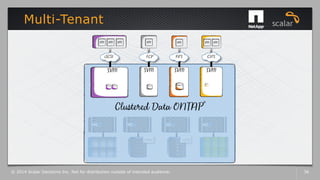
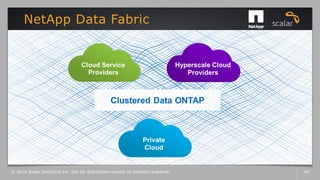
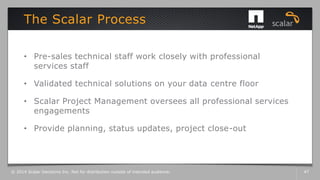
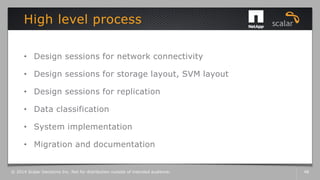
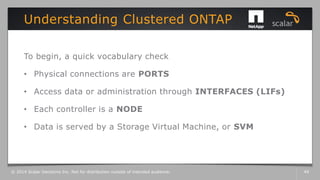
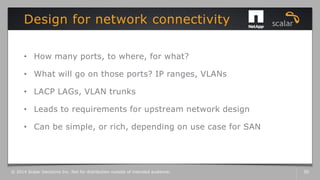
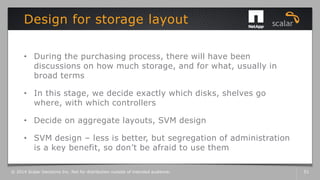
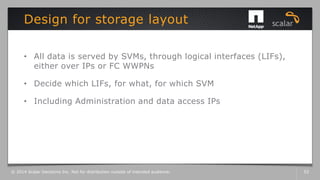
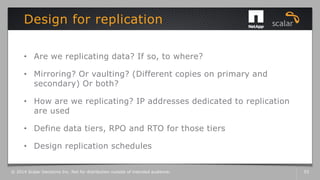
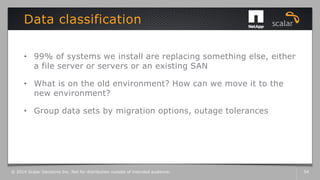
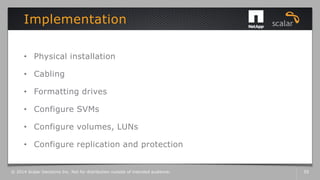
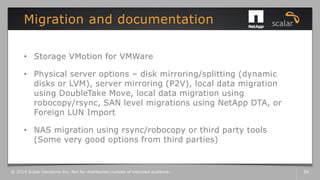
The document discusses the transition to clustered Data ONTAP (CDOT) and its benefits for IT infrastructure, focusing on flexibility, scalability, and data management. It outlines the processes involved in migrating to CDOT, including network design, storage layout, replication strategies, and implementation. The document emphasizes collaboration between technical staff and project management to ensure successful deployment and configuration.