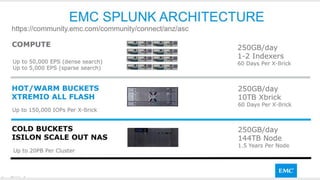
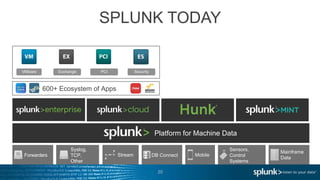
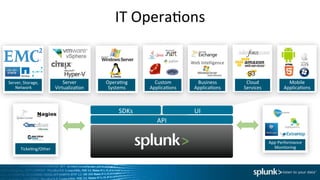
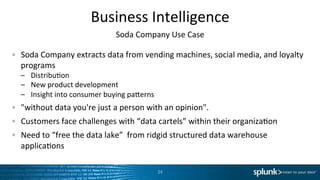
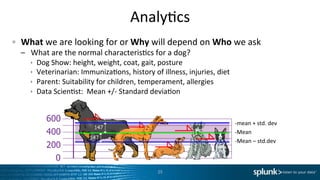
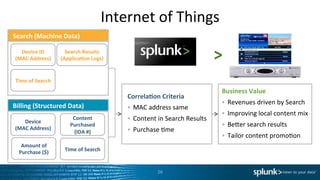
The document discusses how Scalar, EMC, and Splunk can help optimize IT infrastructure for Canadian businesses through innovation, expertise, and services. It provides an overview of Scalar's client solutions in areas like security, cloud, and integrating emerging technologies. Use cases for Splunk analytics in IT operations, security, and IoT are also examined. The document explores consulting services around solution design, deployment, and customization.