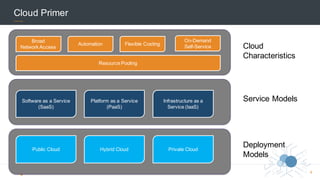
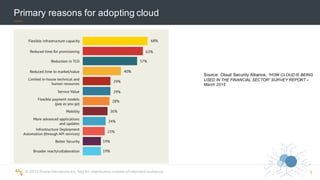
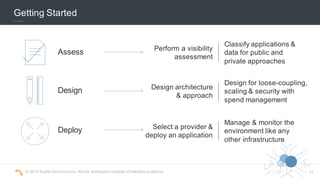
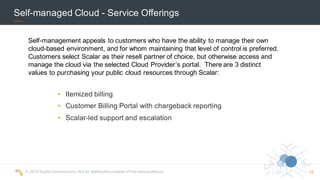
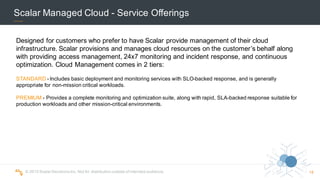
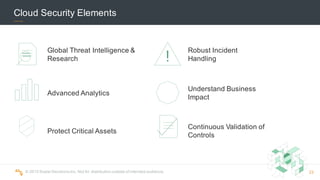
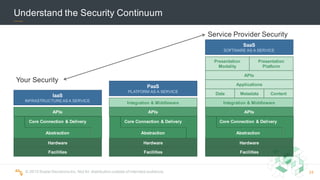
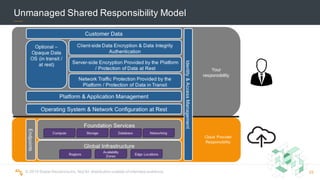
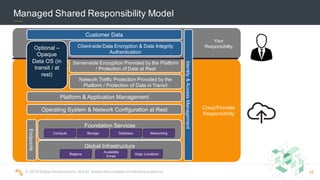
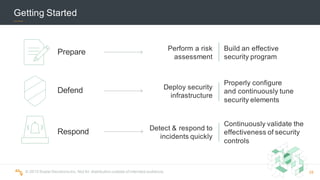
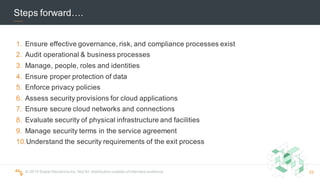
The document provides an overview of cloud computing perspectives from Scalar Decisions. It defines cloud computing based on NIST's definition and discusses pragmatic industry changes like automation, elasticity, and pay-as-you-go models. It outlines cloud characteristics, service models, and deployment models. It also discusses Scalar's approach to cloud including strategic partnerships, consulting offerings, self-managed cloud, and managed cloud services. Finally, it covers cloud security elements and an approach to security by design.