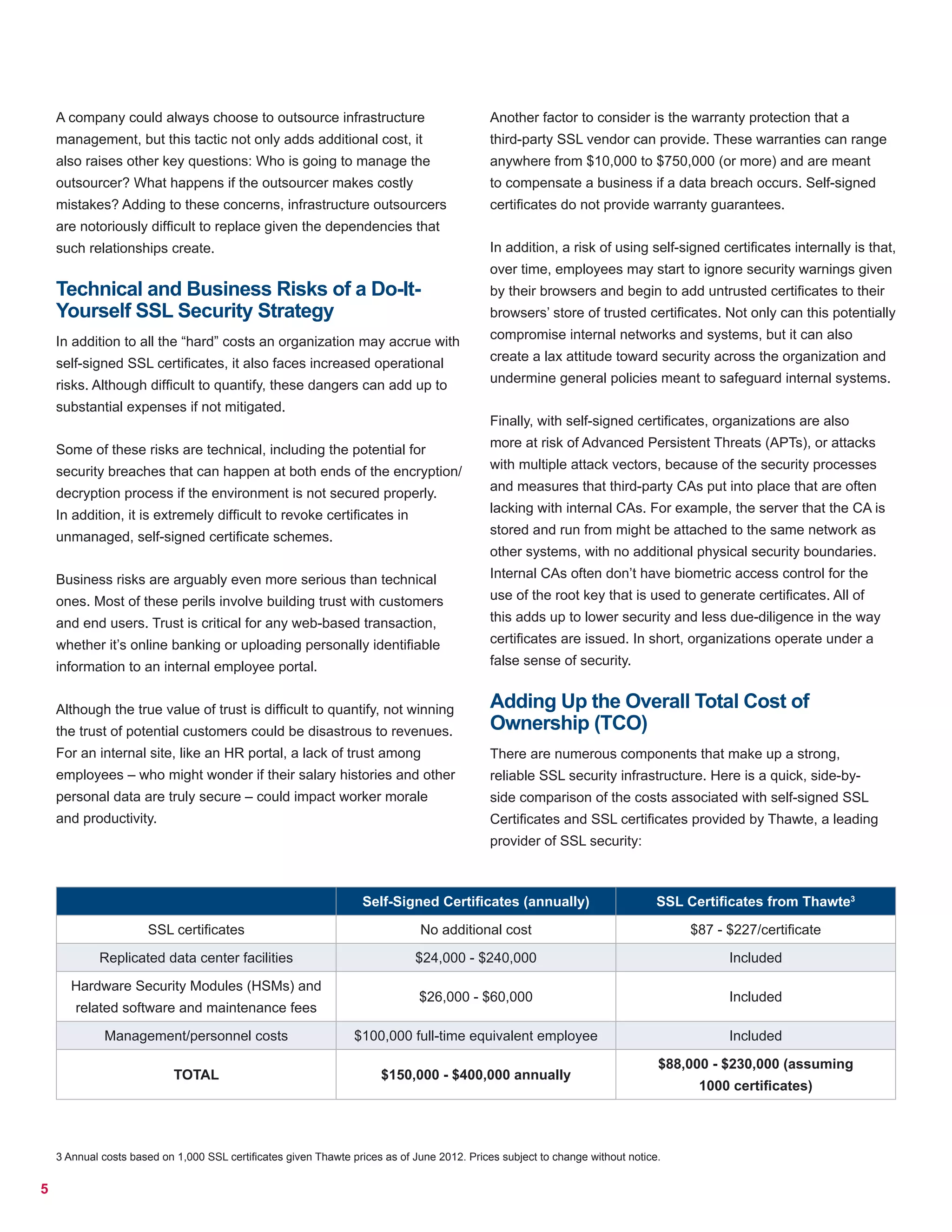
The document discusses the hidden costs and risks associated with self-signed SSL certificates compared to those obtained from trusted third-party vendors. It emphasizes that while self-signed certificates might appear cheaper, the total cost of ownership, including infrastructure, personnel, and inherent security risks, can lead to significantly higher expenses. Ultimately, partnering with a reputable certificate authority is recommended for effective and reliable SSL security.