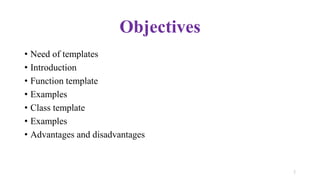
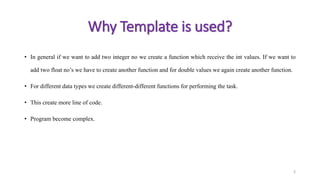
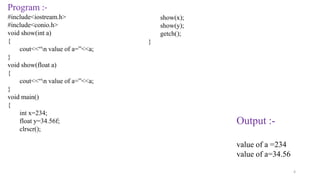
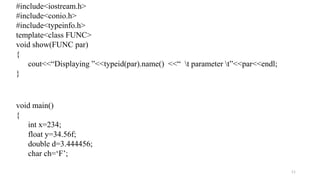
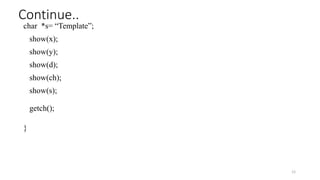
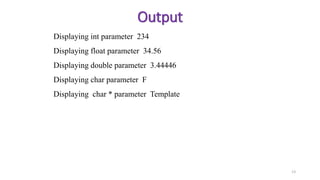
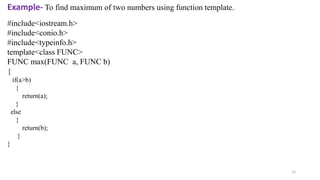
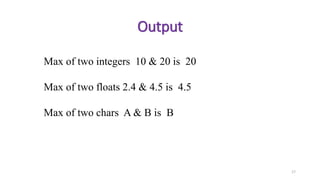
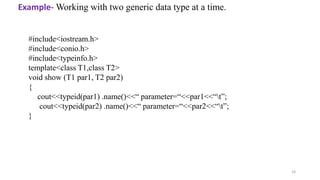
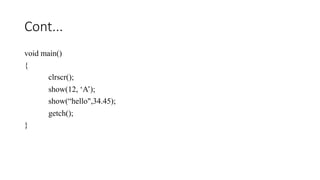
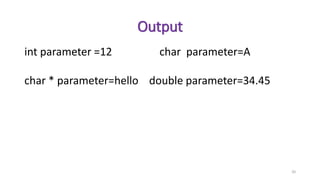
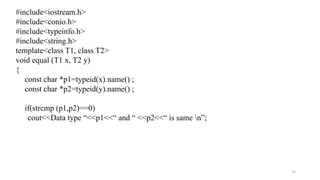
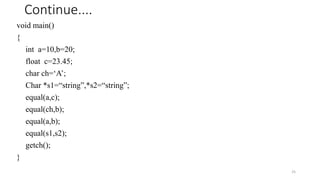
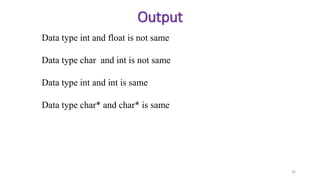
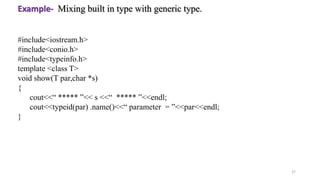
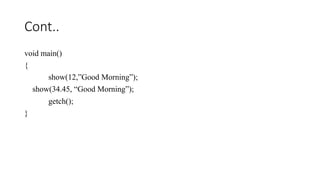
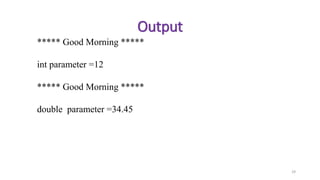
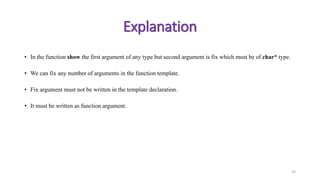
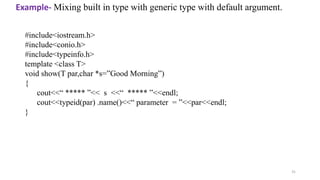
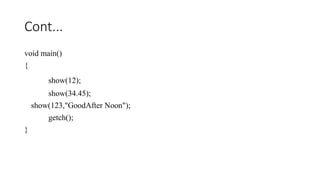
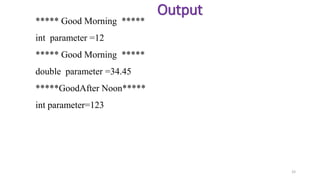
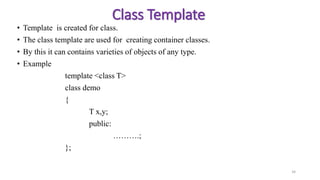
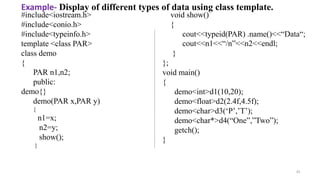
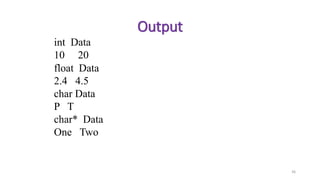
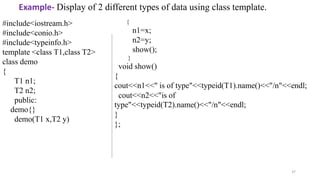
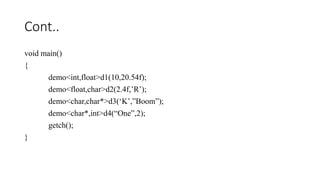
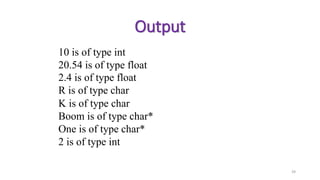
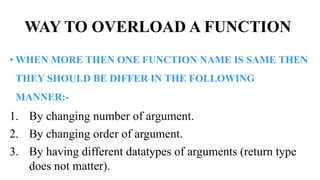
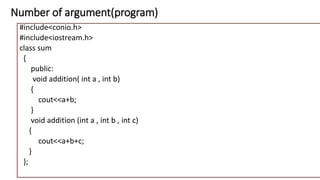
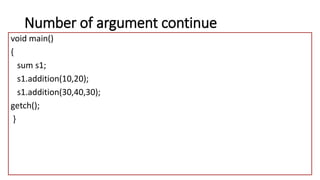
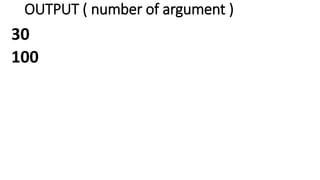
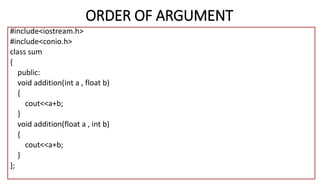
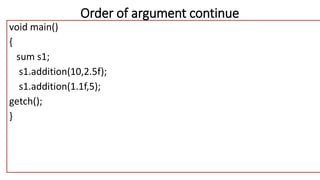
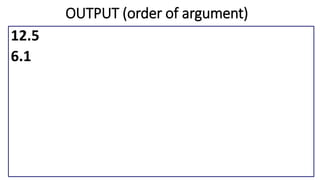
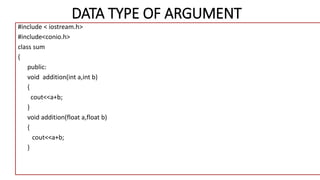
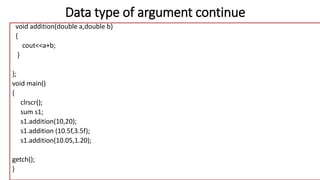
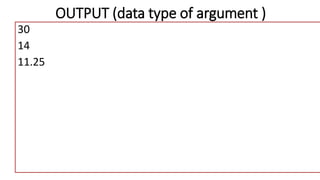
The document discusses function and class templates in C++, highlighting their significance in creating generic functions and classes that can operate with various data types. It provides examples of function templates and class templates, explaining their syntax, advantages, and disadvantages, and illustrating how they simplify code while maintaining type safety. Additionally, the document covers function overloading, explaining how it allows multiple functions with the same name to exist in a class with differing parameters.