Temperature measurement machine design
•
0 likes•25 views
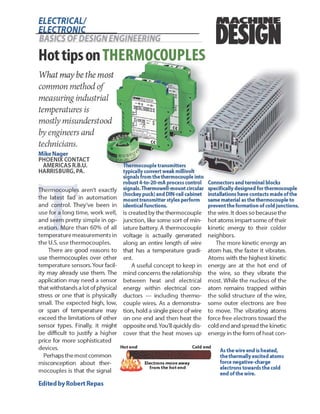
Cover Article in Machine Design discussing temperature measurement with thermocouples
Report
Share
Report
Share
Download to read offline
Recommended
Skills gap

Skills Gap is worldwide and affects many technical and vocational professions. Re-skilling is a responsibility of the individual -- and society as a whole!
Certificate of Appreciation Monmouth County Vocational School District

For helping bring Advanced Manufacturing and Robotics high school program to Monmouth County NJ
Industry 4.0? What the Big Deal? (in 30 seconds please)

Advanced Manufacturing will give suppliers and customers many benefits -- but the benefits aren't the technology. Discover the main reasons Industry 4.0 will be better in the future.
Perceptions of Manufacturing (Misperceptions of Manufacturing)

Negative impressions of manufacturing most in North America that don't reflect the reality of the modern Advanced Manufacturing facility
Industry 4.0 and the Innovation Gap in Advanced Manufacturing

White paper describing the challenges the Industry 4.0 and Advanced Manufacturing will bring to workforce development and training of technicians and engineers.
Redefining White-Collar Jobs in America

Advanced Manufacturing in the USA redefines professional careers and requires new and different skill sets than previous manufacturing jobs. Published in April 2017 in Techniques, the monthly magazine for ACTE members (Association for Career and Technical Education).
Water Treatment Plant Protection

This document discusses methods for protecting water and wastewater treatment plants from lightning strikes and electrical surges. It identifies areas at high risk for lightning strikes, such as pump lift stations and radio antennas. Traditional surge protection methods using MOVs and SADs can be overwhelmed by lightning strikes. Newer triggered arc gap technology provides better protection against high-energy lightning strikes by diverting surge currents to ground. The document describes how triggered arc gaps and additional surge protectors were installed to protect a water treatment plant in Florida that experienced frequent lightning damage.
Recommended
Skills gap

Skills Gap is worldwide and affects many technical and vocational professions. Re-skilling is a responsibility of the individual -- and society as a whole!
Certificate of Appreciation Monmouth County Vocational School District

For helping bring Advanced Manufacturing and Robotics high school program to Monmouth County NJ
Industry 4.0? What the Big Deal? (in 30 seconds please)

Advanced Manufacturing will give suppliers and customers many benefits -- but the benefits aren't the technology. Discover the main reasons Industry 4.0 will be better in the future.
Perceptions of Manufacturing (Misperceptions of Manufacturing)

Negative impressions of manufacturing most in North America that don't reflect the reality of the modern Advanced Manufacturing facility
Industry 4.0 and the Innovation Gap in Advanced Manufacturing

White paper describing the challenges the Industry 4.0 and Advanced Manufacturing will bring to workforce development and training of technicians and engineers.
Redefining White-Collar Jobs in America

Advanced Manufacturing in the USA redefines professional careers and requires new and different skill sets than previous manufacturing jobs. Published in April 2017 in Techniques, the monthly magazine for ACTE members (Association for Career and Technical Education).
Water Treatment Plant Protection

This document discusses methods for protecting water and wastewater treatment plants from lightning strikes and electrical surges. It identifies areas at high risk for lightning strikes, such as pump lift stations and radio antennas. Traditional surge protection methods using MOVs and SADs can be overwhelmed by lightning strikes. Newer triggered arc gap technology provides better protection against high-energy lightning strikes by diverting surge currents to ground. The document describes how triggered arc gaps and additional surge protectors were installed to protect a water treatment plant in Florida that experienced frequent lightning damage.
Smart Grid Overvoltage Protection

This document discusses overvoltage protection for data concentrators used in smart grid applications. It describes the different network levels in smart grids - core, distribution and access networks. For the access network, which provides last mile connectivity between hardware and smart meters, technologies used include power line communication and various wireless standards. Outdoor data concentrator hardware is susceptible to lightning strikes and surges. The document then discusses lightning protection zones and the electrical parameters for surge protection devices used to protect communications ports and power inputs for such outdoor hardware from transient overvoltages.
Power Utility Conference - Wind Turbine Lightning Protection

This document appears to be a presentation on lightning protection for wind turbines. It discusses how lightning strikes can damage wind turbines and cause fires, costing over 1.5 million Euro in one case. It outlines the principles of over-voltage suppression using surge protection components. The presentation covers lightning protection zones, positioning air-termination systems, and surge protection inside the nacelle and down tower panels. It also mentions challenges in protecting rotating equipment and discusses standards for lightning protection.
Four Organic Sales Growth Strategies

Published in ISA Management newsletter, article addresses basic strategies to increase sales organically by expanding into new markets or developing new products. Which combination is right for you? Starting on page 7.
ISA Water and Wastewater Symposium

Technical presentation on lightning protection strategies for water and wastewater treatment plants. Types of voltage surges and equipment protection systems.
ISA 2nd process analytical technology conference

Keynote Presentation on the pharmaceutical industries PAT -- Process Analytical Technology -- Conference
IEEE Conference - Industrial Ethernet

Industrial Ethernet is a specific type of Ethernet used in manufacturing plants and process facilities. It accounts for a large portion of the growing Internet of Things. While based on standard Ethernet, Industrial Ethernet differs in that it must withstand harsh industrial environments and meet real-time control needs. Physical components like connectors and cables must be hardened to withstand vibration, moisture, and other industrial conditions as physical layer failures are common. Standards have evolved to include ruggedized connectors and switches suitable for factory floors and process facilities.
Industrial Housings Paper and Presentation

Delivered at IPC APEX Expo in 2011, details considerations for electronic housing selection for industrial applications.
You're not in kansas anymore - the strange physical world of industrial ether...

Industrial Internet of Things -- Physical Layer Design Considerations from 2014 Annual Conference for Network Professionals. RJ45 and other data connector options.
Null Bangalore | Pentesters Approach to AWS IAM

#Abstract:
- Learn more about the real-world methods for auditing AWS IAM (Identity and Access Management) as a pentester. So let us proceed with a brief discussion of IAM as well as some typical misconfigurations and their potential exploits in order to reinforce the understanding of IAM security best practices.
- Gain actionable insights into AWS IAM policies and roles, using hands on approach.
#Prerequisites:
- Basic understanding of AWS services and architecture
- Familiarity with cloud security concepts
- Experience using the AWS Management Console or AWS CLI.
- For hands on lab create account on [killercoda.com](https://killercoda.com/cloudsecurity-scenario/)
# Scenario Covered:
- Basics of IAM in AWS
- Implementing IAM Policies with Least Privilege to Manage S3 Bucket
- Objective: Create an S3 bucket with least privilege IAM policy and validate access.
- Steps:
- Create S3 bucket.
- Attach least privilege policy to IAM user.
- Validate access.
- Exploiting IAM PassRole Misconfiguration
-Allows a user to pass a specific IAM role to an AWS service (ec2), typically used for service access delegation. Then exploit PassRole Misconfiguration granting unauthorized access to sensitive resources.
- Objective: Demonstrate how a PassRole misconfiguration can grant unauthorized access.
- Steps:
- Allow user to pass IAM role to EC2.
- Exploit misconfiguration for unauthorized access.
- Access sensitive resources.
- Exploiting IAM AssumeRole Misconfiguration with Overly Permissive Role
- An overly permissive IAM role configuration can lead to privilege escalation by creating a role with administrative privileges and allow a user to assume this role.
- Objective: Show how overly permissive IAM roles can lead to privilege escalation.
- Steps:
- Create role with administrative privileges.
- Allow user to assume the role.
- Perform administrative actions.
- Differentiation between PassRole vs AssumeRole
Try at [killercoda.com](https://killercoda.com/cloudsecurity-scenario/)
Data Driven Maintenance | UReason Webinar

Discover the latest insights on Data Driven Maintenance with our comprehensive webinar presentation. Learn about traditional maintenance challenges, the right approach to utilizing data, and the benefits of adopting a Data Driven Maintenance strategy. Explore real-world examples, industry best practices, and innovative solutions like FMECA and the D3M model. This presentation, led by expert Jules Oudmans, is essential for asset owners looking to optimize their maintenance processes and leverage digital technologies for improved efficiency and performance. Download now to stay ahead in the evolving maintenance landscape.
AI assisted telemedicine KIOSK for Rural India.pptx

It gives the overall description of SIH problem statement " AI assisted telemedicine KIOSK for Rural India".
Comparative analysis between traditional aquaponics and reconstructed aquapon...

The aquaponic system of planting is a method that does not require soil usage. It is a method that only needs water, fish, lava rocks (a substitute for soil), and plants. Aquaponic systems are sustainable and environmentally friendly. Its use not only helps to plant in small spaces but also helps reduce artificial chemical use and minimizes excess water use, as aquaponics consumes 90% less water than soil-based gardening. The study applied a descriptive and experimental design to assess and compare conventional and reconstructed aquaponic methods for reproducing tomatoes. The researchers created an observation checklist to determine the significant factors of the study. The study aims to determine the significant difference between traditional aquaponics and reconstructed aquaponics systems propagating tomatoes in terms of height, weight, girth, and number of fruits. The reconstructed aquaponics system’s higher growth yield results in a much more nourished crop than the traditional aquaponics system. It is superior in its number of fruits, height, weight, and girth measurement. Moreover, the reconstructed aquaponics system is proven to eliminate all the hindrances present in the traditional aquaponics system, which are overcrowding of fish, algae growth, pest problems, contaminated water, and dead fish.
Redefining brain tumor segmentation: a cutting-edge convolutional neural netw...

Medical image analysis has witnessed significant advancements with deep learning techniques. In the domain of brain tumor segmentation, the ability to
precisely delineate tumor boundaries from magnetic resonance imaging (MRI)
scans holds profound implications for diagnosis. This study presents an ensemble convolutional neural network (CNN) with transfer learning, integrating
the state-of-the-art Deeplabv3+ architecture with the ResNet18 backbone. The
model is rigorously trained and evaluated, exhibiting remarkable performance
metrics, including an impressive global accuracy of 99.286%, a high-class accuracy of 82.191%, a mean intersection over union (IoU) of 79.900%, a weighted
IoU of 98.620%, and a Boundary F1 (BF) score of 83.303%. Notably, a detailed comparative analysis with existing methods showcases the superiority of
our proposed model. These findings underscore the model’s competence in precise brain tumor localization, underscoring its potential to revolutionize medical
image analysis and enhance healthcare outcomes. This research paves the way
for future exploration and optimization of advanced CNN models in medical
imaging, emphasizing addressing false positives and resource efficiency.
Use PyCharm for remote debugging of WSL on a Windo cf5c162d672e4e58b4dde5d797...

This document serves as a comprehensive step-by-step guide on how to effectively use PyCharm for remote debugging of the Windows Subsystem for Linux (WSL) on a local Windows machine. It meticulously outlines several critical steps in the process, starting with the crucial task of enabling permissions, followed by the installation and configuration of WSL.
The guide then proceeds to explain how to set up the SSH service within the WSL environment, an integral part of the process. Alongside this, it also provides detailed instructions on how to modify the inbound rules of the Windows firewall to facilitate the process, ensuring that there are no connectivity issues that could potentially hinder the debugging process.
The document further emphasizes on the importance of checking the connection between the Windows and WSL environments, providing instructions on how to ensure that the connection is optimal and ready for remote debugging.
It also offers an in-depth guide on how to configure the WSL interpreter and files within the PyCharm environment. This is essential for ensuring that the debugging process is set up correctly and that the program can be run effectively within the WSL terminal.
Additionally, the document provides guidance on how to set up breakpoints for debugging, a fundamental aspect of the debugging process which allows the developer to stop the execution of their code at certain points and inspect their program at those stages.
Finally, the document concludes by providing a link to a reference blog. This blog offers additional information and guidance on configuring the remote Python interpreter in PyCharm, providing the reader with a well-rounded understanding of the process.
官方认证美国密歇根州立大学毕业证学位证书原版一模一样

原版一模一样【微信:741003700 】【美国密歇根州立大学毕业证学位证书】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
More Related Content
More from Mike Nager
Smart Grid Overvoltage Protection

This document discusses overvoltage protection for data concentrators used in smart grid applications. It describes the different network levels in smart grids - core, distribution and access networks. For the access network, which provides last mile connectivity between hardware and smart meters, technologies used include power line communication and various wireless standards. Outdoor data concentrator hardware is susceptible to lightning strikes and surges. The document then discusses lightning protection zones and the electrical parameters for surge protection devices used to protect communications ports and power inputs for such outdoor hardware from transient overvoltages.
Power Utility Conference - Wind Turbine Lightning Protection

This document appears to be a presentation on lightning protection for wind turbines. It discusses how lightning strikes can damage wind turbines and cause fires, costing over 1.5 million Euro in one case. It outlines the principles of over-voltage suppression using surge protection components. The presentation covers lightning protection zones, positioning air-termination systems, and surge protection inside the nacelle and down tower panels. It also mentions challenges in protecting rotating equipment and discusses standards for lightning protection.
Four Organic Sales Growth Strategies

Published in ISA Management newsletter, article addresses basic strategies to increase sales organically by expanding into new markets or developing new products. Which combination is right for you? Starting on page 7.
ISA Water and Wastewater Symposium

Technical presentation on lightning protection strategies for water and wastewater treatment plants. Types of voltage surges and equipment protection systems.
ISA 2nd process analytical technology conference

Keynote Presentation on the pharmaceutical industries PAT -- Process Analytical Technology -- Conference
IEEE Conference - Industrial Ethernet

Industrial Ethernet is a specific type of Ethernet used in manufacturing plants and process facilities. It accounts for a large portion of the growing Internet of Things. While based on standard Ethernet, Industrial Ethernet differs in that it must withstand harsh industrial environments and meet real-time control needs. Physical components like connectors and cables must be hardened to withstand vibration, moisture, and other industrial conditions as physical layer failures are common. Standards have evolved to include ruggedized connectors and switches suitable for factory floors and process facilities.
Industrial Housings Paper and Presentation

Delivered at IPC APEX Expo in 2011, details considerations for electronic housing selection for industrial applications.
You're not in kansas anymore - the strange physical world of industrial ether...

Industrial Internet of Things -- Physical Layer Design Considerations from 2014 Annual Conference for Network Professionals. RJ45 and other data connector options.
More from Mike Nager (8)
Power Utility Conference - Wind Turbine Lightning Protection

Power Utility Conference - Wind Turbine Lightning Protection
You're not in kansas anymore - the strange physical world of industrial ether...

You're not in kansas anymore - the strange physical world of industrial ether...
Recently uploaded
Null Bangalore | Pentesters Approach to AWS IAM

#Abstract:
- Learn more about the real-world methods for auditing AWS IAM (Identity and Access Management) as a pentester. So let us proceed with a brief discussion of IAM as well as some typical misconfigurations and their potential exploits in order to reinforce the understanding of IAM security best practices.
- Gain actionable insights into AWS IAM policies and roles, using hands on approach.
#Prerequisites:
- Basic understanding of AWS services and architecture
- Familiarity with cloud security concepts
- Experience using the AWS Management Console or AWS CLI.
- For hands on lab create account on [killercoda.com](https://killercoda.com/cloudsecurity-scenario/)
# Scenario Covered:
- Basics of IAM in AWS
- Implementing IAM Policies with Least Privilege to Manage S3 Bucket
- Objective: Create an S3 bucket with least privilege IAM policy and validate access.
- Steps:
- Create S3 bucket.
- Attach least privilege policy to IAM user.
- Validate access.
- Exploiting IAM PassRole Misconfiguration
-Allows a user to pass a specific IAM role to an AWS service (ec2), typically used for service access delegation. Then exploit PassRole Misconfiguration granting unauthorized access to sensitive resources.
- Objective: Demonstrate how a PassRole misconfiguration can grant unauthorized access.
- Steps:
- Allow user to pass IAM role to EC2.
- Exploit misconfiguration for unauthorized access.
- Access sensitive resources.
- Exploiting IAM AssumeRole Misconfiguration with Overly Permissive Role
- An overly permissive IAM role configuration can lead to privilege escalation by creating a role with administrative privileges and allow a user to assume this role.
- Objective: Show how overly permissive IAM roles can lead to privilege escalation.
- Steps:
- Create role with administrative privileges.
- Allow user to assume the role.
- Perform administrative actions.
- Differentiation between PassRole vs AssumeRole
Try at [killercoda.com](https://killercoda.com/cloudsecurity-scenario/)
Data Driven Maintenance | UReason Webinar

Discover the latest insights on Data Driven Maintenance with our comprehensive webinar presentation. Learn about traditional maintenance challenges, the right approach to utilizing data, and the benefits of adopting a Data Driven Maintenance strategy. Explore real-world examples, industry best practices, and innovative solutions like FMECA and the D3M model. This presentation, led by expert Jules Oudmans, is essential for asset owners looking to optimize their maintenance processes and leverage digital technologies for improved efficiency and performance. Download now to stay ahead in the evolving maintenance landscape.
AI assisted telemedicine KIOSK for Rural India.pptx

It gives the overall description of SIH problem statement " AI assisted telemedicine KIOSK for Rural India".
Comparative analysis between traditional aquaponics and reconstructed aquapon...

The aquaponic system of planting is a method that does not require soil usage. It is a method that only needs water, fish, lava rocks (a substitute for soil), and plants. Aquaponic systems are sustainable and environmentally friendly. Its use not only helps to plant in small spaces but also helps reduce artificial chemical use and minimizes excess water use, as aquaponics consumes 90% less water than soil-based gardening. The study applied a descriptive and experimental design to assess and compare conventional and reconstructed aquaponic methods for reproducing tomatoes. The researchers created an observation checklist to determine the significant factors of the study. The study aims to determine the significant difference between traditional aquaponics and reconstructed aquaponics systems propagating tomatoes in terms of height, weight, girth, and number of fruits. The reconstructed aquaponics system’s higher growth yield results in a much more nourished crop than the traditional aquaponics system. It is superior in its number of fruits, height, weight, and girth measurement. Moreover, the reconstructed aquaponics system is proven to eliminate all the hindrances present in the traditional aquaponics system, which are overcrowding of fish, algae growth, pest problems, contaminated water, and dead fish.
Redefining brain tumor segmentation: a cutting-edge convolutional neural netw...

Medical image analysis has witnessed significant advancements with deep learning techniques. In the domain of brain tumor segmentation, the ability to
precisely delineate tumor boundaries from magnetic resonance imaging (MRI)
scans holds profound implications for diagnosis. This study presents an ensemble convolutional neural network (CNN) with transfer learning, integrating
the state-of-the-art Deeplabv3+ architecture with the ResNet18 backbone. The
model is rigorously trained and evaluated, exhibiting remarkable performance
metrics, including an impressive global accuracy of 99.286%, a high-class accuracy of 82.191%, a mean intersection over union (IoU) of 79.900%, a weighted
IoU of 98.620%, and a Boundary F1 (BF) score of 83.303%. Notably, a detailed comparative analysis with existing methods showcases the superiority of
our proposed model. These findings underscore the model’s competence in precise brain tumor localization, underscoring its potential to revolutionize medical
image analysis and enhance healthcare outcomes. This research paves the way
for future exploration and optimization of advanced CNN models in medical
imaging, emphasizing addressing false positives and resource efficiency.
Use PyCharm for remote debugging of WSL on a Windo cf5c162d672e4e58b4dde5d797...

This document serves as a comprehensive step-by-step guide on how to effectively use PyCharm for remote debugging of the Windows Subsystem for Linux (WSL) on a local Windows machine. It meticulously outlines several critical steps in the process, starting with the crucial task of enabling permissions, followed by the installation and configuration of WSL.
The guide then proceeds to explain how to set up the SSH service within the WSL environment, an integral part of the process. Alongside this, it also provides detailed instructions on how to modify the inbound rules of the Windows firewall to facilitate the process, ensuring that there are no connectivity issues that could potentially hinder the debugging process.
The document further emphasizes on the importance of checking the connection between the Windows and WSL environments, providing instructions on how to ensure that the connection is optimal and ready for remote debugging.
It also offers an in-depth guide on how to configure the WSL interpreter and files within the PyCharm environment. This is essential for ensuring that the debugging process is set up correctly and that the program can be run effectively within the WSL terminal.
Additionally, the document provides guidance on how to set up breakpoints for debugging, a fundamental aspect of the debugging process which allows the developer to stop the execution of their code at certain points and inspect their program at those stages.
Finally, the document concludes by providing a link to a reference blog. This blog offers additional information and guidance on configuring the remote Python interpreter in PyCharm, providing the reader with a well-rounded understanding of the process.
官方认证美国密歇根州立大学毕业证学位证书原版一模一样

原版一模一样【微信:741003700 】【美国密歇根州立大学毕业证学位证书】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
22CYT12-Unit-V-E Waste and its Management.ppt

Introduction- e - waste – definition - sources of e-waste– hazardous substances in e-waste - effects of e-waste on environment and human health- need for e-waste management– e-waste handling rules - waste minimization techniques for managing e-waste – recycling of e-waste - disposal treatment methods of e- waste – mechanism of extraction of precious metal from leaching solution-global Scenario of E-waste – E-waste in India- case studies.
Unit-III-ELECTROCHEMICAL STORAGE DEVICES.ppt

Batteries -Introduction – Types of Batteries – discharging and charging of battery - characteristics of battery –battery rating- various tests on battery- – Primary battery: silver button cell- Secondary battery :Ni-Cd battery-modern battery: lithium ion battery-maintenance of batteries-choices of batteries for electric vehicle applications.
Fuel Cells: Introduction- importance and classification of fuel cells - description, principle, components, applications of fuel cells: H2-O2 fuel cell, alkaline fuel cell, molten carbonate fuel cell and direct methanol fuel cells.
LLM Fine Tuning with QLoRA Cassandra Lunch 4, presented by Anant

Slides for the 4th Presentation on LLM Fine-Tuning with QLoRA Presented by Anant, featuring DataStax Astra
Recently uploaded (20)
AI assisted telemedicine KIOSK for Rural India.pptx

AI assisted telemedicine KIOSK for Rural India.pptx
Comparative analysis between traditional aquaponics and reconstructed aquapon...

Comparative analysis between traditional aquaponics and reconstructed aquapon...
Redefining brain tumor segmentation: a cutting-edge convolutional neural netw...

Redefining brain tumor segmentation: a cutting-edge convolutional neural netw...
Use PyCharm for remote debugging of WSL on a Windo cf5c162d672e4e58b4dde5d797...

Use PyCharm for remote debugging of WSL on a Windo cf5c162d672e4e58b4dde5d797...
Generative AI leverages algorithms to create various forms of content

Generative AI leverages algorithms to create various forms of content
Data Control Language.pptx Data Control Language.pptx

Data Control Language.pptx Data Control Language.pptx
LLM Fine Tuning with QLoRA Cassandra Lunch 4, presented by Anant

LLM Fine Tuning with QLoRA Cassandra Lunch 4, presented by Anant
