Technology Certificates at KSU
•
1 like•81 views
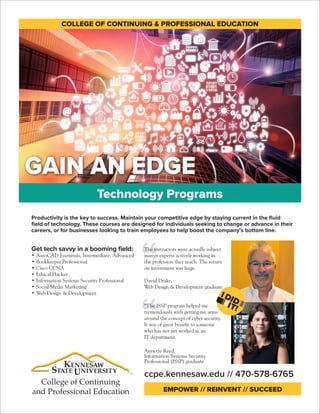
From AutoCAD to web design, these professional certificates from the College of Continuing and Professional Education at Kennesaw State University will help you reach your tech training goals.
Report
Share
Report
Share
Download to read offline
Recommended
Mendix - Cloud PAAS App Platform

Tarandeep Singh Presentation on Mendix - Cloud PAAS App Platform. This PPT Contains basic information about Mendix and How really you can start developing on Mendix.
Thanks.
------------------------------------------------------------
About Me
Myself Tarandeep Singh from Delhi, India working as a Software Engineer with more than 3 years of Experience on Java, Android, Salesforce, Mendix and CMS Tools. I have started this youtube channel with the aim to share my knowledge and experience with you guys. I will add Videos on Android, Java, Salesforce, Mendix, Wordpress, Opencart etc. Also i am going to Answer your Questions through my videos.
Follow me on Twitter : http://twitter.com/tdssaini
Connect with me on Linkedin : http://linkedin.com/in/tdssaini
Follow my Blog : http://Blog.ErTarandeep.com
Follw me on Medium : http://medium.com/@tdssaini
Visit My Website : http://ErTarandeep.com
Email me at : tarandeep.s.saini@gmail.com
NetIQ advertisement for their Security Solutions

Advertisement for NetIQ security solutions. We've developed a series of marketing initiatives for each of their core solutions. Each solution group has it's own imagery and messaging.
DevOps Night - Shifting Security to the Left - SCTV Tower - 19 September 2018

Presentation for DevOps Night talk in SCTV Tower in Jakarta on 19 September 2018. Sharing on how to bring security to DevOps environment on Development side.
Tech in Sustainability | YfS India

This is a talk taken by me on 19th Nov 2021 (7:30 PM IST) for the YfS India Organization to boost participants of a Hackathon to learn about implementation of Technology in Sustainability Grounds.
To know more about me, explore at: https://ramneekkalra.in/
From Zero to DevSecOps: How to Implement Security at the Speed of DevOps 

Your organization has already embraced the DevOps methodology? That’s a great start. But what about security?
It’s a fact - many organizations fear that adding security to their DevOps practices will severely slow down their development processes. But this doesn’t need to be the case.
Tune in to hear Jeff Martin, Senior Director of Product at WhiteSource and Anders Wallgren, VP of Technology Strategy at Cloudbees, as they discuss:
- Why traditional DevOps has shifted, and what this will mean
- Who should own security in the age of DevOps
- Which tools and strategies are needed to implement continuous security throughout the DevOps pipeline
LaunchTech Named Agency of the Year at Global Excellence Awards

Drawing on two decades of experience in the cybersecurity industry, Wayne Schepens is an entrepreneur that continues to contribute to organizations like SINET, Mach 37, and other accelerator programs since launching LaunchTech in 2014. Wayne Schepens is the founder and CEO of LaunchTech Communications, which he grew to an industry leader generating over $2.5 million in revenue after just a few years in operation.
The organization has recently been named Cyber and Info Security Agency of the Year 2020 at the Global Excellence Awards, having been judged by a panel of 35 industry experts from around the world. LaunchTech's senior vice president of operations, Kate D. Shapiro, noted that it validates the team’s efforts while also highlighting their creative finesse and technical acumen.
The awards, which were presented by the Info Security Products Guide, recognize the efforts of security firms across the globe, with a focus on those that have made a large impact on the industry.
Embedding Security in IT Projects

Security is an important factor in IT project management. This presentation highlights security implications in delivering IT projects by focusing on project management processes, and Software Development Life Cycle. This also highlights how to implement security in Waterfall and Agile delivery methods. In addition, this presentation details delivering quality software by aligning project level strategies with organization’s security strategy and process.
Presented on June 2015 at ISSA, Durham, NC, USA.
Recommended
Mendix - Cloud PAAS App Platform

Tarandeep Singh Presentation on Mendix - Cloud PAAS App Platform. This PPT Contains basic information about Mendix and How really you can start developing on Mendix.
Thanks.
------------------------------------------------------------
About Me
Myself Tarandeep Singh from Delhi, India working as a Software Engineer with more than 3 years of Experience on Java, Android, Salesforce, Mendix and CMS Tools. I have started this youtube channel with the aim to share my knowledge and experience with you guys. I will add Videos on Android, Java, Salesforce, Mendix, Wordpress, Opencart etc. Also i am going to Answer your Questions through my videos.
Follow me on Twitter : http://twitter.com/tdssaini
Connect with me on Linkedin : http://linkedin.com/in/tdssaini
Follow my Blog : http://Blog.ErTarandeep.com
Follw me on Medium : http://medium.com/@tdssaini
Visit My Website : http://ErTarandeep.com
Email me at : tarandeep.s.saini@gmail.com
NetIQ advertisement for their Security Solutions

Advertisement for NetIQ security solutions. We've developed a series of marketing initiatives for each of their core solutions. Each solution group has it's own imagery and messaging.
DevOps Night - Shifting Security to the Left - SCTV Tower - 19 September 2018

Presentation for DevOps Night talk in SCTV Tower in Jakarta on 19 September 2018. Sharing on how to bring security to DevOps environment on Development side.
Tech in Sustainability | YfS India

This is a talk taken by me on 19th Nov 2021 (7:30 PM IST) for the YfS India Organization to boost participants of a Hackathon to learn about implementation of Technology in Sustainability Grounds.
To know more about me, explore at: https://ramneekkalra.in/
From Zero to DevSecOps: How to Implement Security at the Speed of DevOps 

Your organization has already embraced the DevOps methodology? That’s a great start. But what about security?
It’s a fact - many organizations fear that adding security to their DevOps practices will severely slow down their development processes. But this doesn’t need to be the case.
Tune in to hear Jeff Martin, Senior Director of Product at WhiteSource and Anders Wallgren, VP of Technology Strategy at Cloudbees, as they discuss:
- Why traditional DevOps has shifted, and what this will mean
- Who should own security in the age of DevOps
- Which tools and strategies are needed to implement continuous security throughout the DevOps pipeline
LaunchTech Named Agency of the Year at Global Excellence Awards

Drawing on two decades of experience in the cybersecurity industry, Wayne Schepens is an entrepreneur that continues to contribute to organizations like SINET, Mach 37, and other accelerator programs since launching LaunchTech in 2014. Wayne Schepens is the founder and CEO of LaunchTech Communications, which he grew to an industry leader generating over $2.5 million in revenue after just a few years in operation.
The organization has recently been named Cyber and Info Security Agency of the Year 2020 at the Global Excellence Awards, having been judged by a panel of 35 industry experts from around the world. LaunchTech's senior vice president of operations, Kate D. Shapiro, noted that it validates the team’s efforts while also highlighting their creative finesse and technical acumen.
The awards, which were presented by the Info Security Products Guide, recognize the efforts of security firms across the globe, with a focus on those that have made a large impact on the industry.
Embedding Security in IT Projects

Security is an important factor in IT project management. This presentation highlights security implications in delivering IT projects by focusing on project management processes, and Software Development Life Cycle. This also highlights how to implement security in Waterfall and Agile delivery methods. In addition, this presentation details delivering quality software by aligning project level strategies with organization’s security strategy and process.
Presented on June 2015 at ISSA, Durham, NC, USA.
NodeJS Application Development services

NodeJS is a platform to build fast, scalable network applications. It allows you to get the best products that are just apt for the application developing process.
CraftTurf Brochure

A general description of the business proposition of CraftTurf as a cloud-based software engineering company.
Container Security: What Enterprises Need to Know

Enterprises and application teams turn to containers to improve agility and increase the scalability of their environments and portability of their applications. But with these benefits come a number of serious security challenges and considerations. While some of the changes containerization brings to security are beneficial, others are a bit thornier. To avoid serious mistakes and data breaches, enterprises must understand how containers affect security and build a strategy to secure them.
From Cybersecurity to Cyber Resilience

The slideshare identifies the six steps to moving beyond cybersecurity to cyber resilience. Ensuring federal agencies maintain continuous operations while under persistent threat. Learn more: https://accntu.re/2Q2cdDj
Mendix learning by Sunil Kumar

A brief discussion on Mendix Platform. It helps you to understand Mendix Platform quickly
Managing Compliance in Container Environments

DevOps, linked with container adoption, is driving digital transformation. Learn cloud native cyber security from the top to bottom of the stack.
Security Everywhere: A Growth Engine for the Digital Economy

Пленарный доклад “Security Everywhere: A Growth Engine for the Digital Economy”, Caspar Herzberg, Vice President Services, Cisco
What is the Goal of Data Center Security

With millions upon millions of new malware variants found every year, protecting the system(s) and the ways a company communicates is a matter of strategy and action of well-matched defenses. The two main defense solution types include physical security and network security.
READ MORE: http://www.42u.com/solutions/security
How to Build a Great Web Application

Successful web and mobile products require a unique combination of enterprise-class aplomb and bold innovation. You have to consider security, scalability, and reliability, but you also need to be familiar with the newest technologies.
You don’t have to compromise. Huge advancements in developer productivity are underway: JavaScript is slowly emerging as the lingua franca of software, and Node.js unlocks unprecedented performance gains in the cloud. Meanwhile, responsive design makes it possible to create amazing, multi-faceted experiences from a single code base.
These technologies make it possible to shave weeks (or months) off your timeline without sacrificing your vision.
NUS-ISS Learning Day 2019-Complying with new IoT cyber security guide

Presented by Mr Ng Kok Leong, Senior Lecturer & Consultant, Digital Strategy & Leadership Practice ,NUS-ISS, at NUS-ISS Learning Day 2019
Cybersecurity PowerPoint Presentation Slides 

Let your team understand the importance of Computer security with the assistance of our Cyber Security PowerPoint Presentation Deck. In today’s time, it is quite essential to pay attention towards the protection of computer systems from theft or damage as there is a every chance of your data being accessed by someone else. Our creative designing team has crafted this PPT Deck with 17 slides for you to share the information related to IT security. Although there are cyber security standards available but still there are people in the market who try to capture your data to either use it for their own purpose or sell it to some other organization. This presentation deck enables you to highlight the information related to cyber attacks that can create concerns such as backdoor, direct-access attacks, eavesdropping, phishing, spoofing, tampering etc. By taking certain security measures you can protect your data. Cyber Security standards attempt to protect the cyber environment of a user or an organization. The PowerPoint deck contains some slides which include information related to tips, initiatives, step to ensure that your data is protected at every step. So, download it and take precautionary steps to secure your IT system. Cater for crazy cravings with our Cybersecurity Powerpoint Presentation Slides. Find a harmless way to fulfill deep desires.
Innovating at speed and scale with implicit security

Growth depends on continuous innovation with emerging technology at speed and scale. How can you do it securely? And why is the timing so vital, as businesses emerge from economic uncertainty?
Technology Trends & The Impact for Software Industry

Technology Trends & The Impact for Software Industry
MT81 Keys to Successful Enterprise IoT Initiatives

Success with enterprise Internet of Things (IoT) initiatives begins with strong partnerships between IT and operations technology (OT) organizations and identifying relevant use cases with measurable ROI. Next, choosing the right IoT architecture and technology requires determining the capabilities are needed at the edge and what are needed in the cloud and datacenter to minimize cost and enable analytics-driven action. This session will discusses the challenges involved with introducing sensors and smart devices into your network, including building infrastructure and analytics capabilities , and securing data and applications. Learn how Dell'S IoT-specific gateways, edge analytics software and infrastructure solutions provide flexible architecture options for multiple IoT use cases.
DevOps Indonesia - DevSecOps - Application Security on Production Environment

This was a presentation for DevOps Indonesia on how can we secure our application production environment by doing automation and tools using RASP and Micro Segmentation to help DevOps organisation to achieve their goals
How to Make New Nonprofit Videos from Old Content Using Adobe Rush

Join Adobe product managers Sirr Less and Jessica Nunez for a quick, instructional webinar showing nonprofit attendees how to bring new life to their organization's content using the Adobe Rush app. Through very simple video editing, learn how to repurpose existing video footage, photos, and audio from your phone and computer to create new media to deliver impactful video communication to your supporters and donors.
The Ultimate Guide To Cyber Security Certifications

Cyber Security is the most important constituent of Information Technology
that protects all kinds of information systems, (personal or professional) against
all the vulnerabilities and potential attacks via the internet.
More Related Content
What's hot
NodeJS Application Development services

NodeJS is a platform to build fast, scalable network applications. It allows you to get the best products that are just apt for the application developing process.
CraftTurf Brochure

A general description of the business proposition of CraftTurf as a cloud-based software engineering company.
Container Security: What Enterprises Need to Know

Enterprises and application teams turn to containers to improve agility and increase the scalability of their environments and portability of their applications. But with these benefits come a number of serious security challenges and considerations. While some of the changes containerization brings to security are beneficial, others are a bit thornier. To avoid serious mistakes and data breaches, enterprises must understand how containers affect security and build a strategy to secure them.
From Cybersecurity to Cyber Resilience

The slideshare identifies the six steps to moving beyond cybersecurity to cyber resilience. Ensuring federal agencies maintain continuous operations while under persistent threat. Learn more: https://accntu.re/2Q2cdDj
Mendix learning by Sunil Kumar

A brief discussion on Mendix Platform. It helps you to understand Mendix Platform quickly
Managing Compliance in Container Environments

DevOps, linked with container adoption, is driving digital transformation. Learn cloud native cyber security from the top to bottom of the stack.
Security Everywhere: A Growth Engine for the Digital Economy

Пленарный доклад “Security Everywhere: A Growth Engine for the Digital Economy”, Caspar Herzberg, Vice President Services, Cisco
What is the Goal of Data Center Security

With millions upon millions of new malware variants found every year, protecting the system(s) and the ways a company communicates is a matter of strategy and action of well-matched defenses. The two main defense solution types include physical security and network security.
READ MORE: http://www.42u.com/solutions/security
How to Build a Great Web Application

Successful web and mobile products require a unique combination of enterprise-class aplomb and bold innovation. You have to consider security, scalability, and reliability, but you also need to be familiar with the newest technologies.
You don’t have to compromise. Huge advancements in developer productivity are underway: JavaScript is slowly emerging as the lingua franca of software, and Node.js unlocks unprecedented performance gains in the cloud. Meanwhile, responsive design makes it possible to create amazing, multi-faceted experiences from a single code base.
These technologies make it possible to shave weeks (or months) off your timeline without sacrificing your vision.
NUS-ISS Learning Day 2019-Complying with new IoT cyber security guide

Presented by Mr Ng Kok Leong, Senior Lecturer & Consultant, Digital Strategy & Leadership Practice ,NUS-ISS, at NUS-ISS Learning Day 2019
Cybersecurity PowerPoint Presentation Slides 

Let your team understand the importance of Computer security with the assistance of our Cyber Security PowerPoint Presentation Deck. In today’s time, it is quite essential to pay attention towards the protection of computer systems from theft or damage as there is a every chance of your data being accessed by someone else. Our creative designing team has crafted this PPT Deck with 17 slides for you to share the information related to IT security. Although there are cyber security standards available but still there are people in the market who try to capture your data to either use it for their own purpose or sell it to some other organization. This presentation deck enables you to highlight the information related to cyber attacks that can create concerns such as backdoor, direct-access attacks, eavesdropping, phishing, spoofing, tampering etc. By taking certain security measures you can protect your data. Cyber Security standards attempt to protect the cyber environment of a user or an organization. The PowerPoint deck contains some slides which include information related to tips, initiatives, step to ensure that your data is protected at every step. So, download it and take precautionary steps to secure your IT system. Cater for crazy cravings with our Cybersecurity Powerpoint Presentation Slides. Find a harmless way to fulfill deep desires.
Innovating at speed and scale with implicit security

Growth depends on continuous innovation with emerging technology at speed and scale. How can you do it securely? And why is the timing so vital, as businesses emerge from economic uncertainty?
Technology Trends & The Impact for Software Industry

Technology Trends & The Impact for Software Industry
MT81 Keys to Successful Enterprise IoT Initiatives

Success with enterprise Internet of Things (IoT) initiatives begins with strong partnerships between IT and operations technology (OT) organizations and identifying relevant use cases with measurable ROI. Next, choosing the right IoT architecture and technology requires determining the capabilities are needed at the edge and what are needed in the cloud and datacenter to minimize cost and enable analytics-driven action. This session will discusses the challenges involved with introducing sensors and smart devices into your network, including building infrastructure and analytics capabilities , and securing data and applications. Learn how Dell'S IoT-specific gateways, edge analytics software and infrastructure solutions provide flexible architecture options for multiple IoT use cases.
DevOps Indonesia - DevSecOps - Application Security on Production Environment

This was a presentation for DevOps Indonesia on how can we secure our application production environment by doing automation and tools using RASP and Micro Segmentation to help DevOps organisation to achieve their goals
How to Make New Nonprofit Videos from Old Content Using Adobe Rush

Join Adobe product managers Sirr Less and Jessica Nunez for a quick, instructional webinar showing nonprofit attendees how to bring new life to their organization's content using the Adobe Rush app. Through very simple video editing, learn how to repurpose existing video footage, photos, and audio from your phone and computer to create new media to deliver impactful video communication to your supporters and donors.
What's hot (20)
Security Everywhere: A Growth Engine for the Digital Economy

Security Everywhere: A Growth Engine for the Digital Economy
Cisco Connect 2018 Vietnam - data center transformation - vn

Cisco Connect 2018 Vietnam - data center transformation - vn
NUS-ISS Learning Day 2019-Complying with new IoT cyber security guide

NUS-ISS Learning Day 2019-Complying with new IoT cyber security guide
Innovating at speed and scale with implicit security

Innovating at speed and scale with implicit security
Cisco Connect 2018 Singapore - Cybersecurity strategy 

Cisco Connect 2018 Singapore - Cybersecurity strategy
Technology Trends & The Impact for Software Industry

Technology Trends & The Impact for Software Industry
MT81 Keys to Successful Enterprise IoT Initiatives

MT81 Keys to Successful Enterprise IoT Initiatives
DevOps Indonesia - DevSecOps - Application Security on Production Environment

DevOps Indonesia - DevSecOps - Application Security on Production Environment
How to Make New Nonprofit Videos from Old Content Using Adobe Rush

How to Make New Nonprofit Videos from Old Content Using Adobe Rush
Similar to Technology Certificates at KSU
The Ultimate Guide To Cyber Security Certifications

Cyber Security is the most important constituent of Information Technology
that protects all kinds of information systems, (personal or professional) against
all the vulnerabilities and potential attacks via the internet.
Top Certification for 2023 Top 10 Certifications Top Professional Certifications

Top certifications for 2022.
Top certification for 2023.
Top professional certifications.
What Cybersecurity Certifications Make You The Most Money Today.pptx

Security is more vital than ever before in today’s digitally interconnected world. The surge in cybercrime has increased the demand for cybersecurity experts.
https://www.infosectrain.com/courses/cissp-certification-training/
CSI Promotional Brochure

Welcome to CSI Technologies - a leading provider of innovative technology solutions for businesses of all sizes. With a focus on delivering high-quality, cost-effective products and services, we help our clients to stay ahead of the curve and unlock the full potential of their technology.
Our team of expert engineers and technologists are dedicated to providing personalized, end-to-end support to ensure that our clients receive the best possible solutions for their unique needs. From custom software development and cloud-based services to data analytics and cybersecurity, we have the expertise and experience to help our clients achieve their goals.
At CSI Technologies, we are committed to delivering exceptional value and support to our clients. Contact us today to learn more about how we can help you to maximize the power of technology in your business.
Secure-Net Technologies

Secure-Net Technologies is a located in Chandigarh an Educational Institute authorized by Pearson, Oracle, Microsoft, Cisco and many more big brands.
The Ultimate Roadmap For CompTIA Training & Certifications

CompTIA is considered one of the leading organizations globally for its technical and cybersecurity certifications. CompTIA certifications are vendor-neutral and are designed to build and validate your teams’ skill sets as per their job roles and help them advance their career path by staying updated with the latest technology, increasing their efficiency, and securing your organization’s security stance.
Obtaining industry-recognized certifications will increase your team’s credibility and establish them as skilled IT professionals. To succeed in an IT job, it is important to keep up with the ever-changing IT industry by upskilling your teams with the best certifications.
CompTIA is the leading training destination for tech-driven teams and tech-engaged organizations. More than 2.5 million CompTIA certifications have been issued in cybersecurity, networking, cloud computing, and technical assistance.
The NICE framework is published by the U.S. National Institute of Standards and Technology (NIST). It provides a common ground for organizations in the public, private, and academic sectors to define professional cybersecurity work requirements. Many CompTIA certifications are mapped to the NIST/NICE frameworks. These certifications are beneficial to government employees to verify their cyber knowledge and skills while fulfilling government directives like FISMA and DoD 8570/8140. Let us explore the advantages of upskilling your IT teams with CompTIA training and certifications.
Top Skills Every Data Center Engineer Should Master.pdf

In the ever-evolving landscape of technology, data center engineers play a crucial role in ensuring the seamless operation of digital infrastructures. Whether you’re a seasoned professional or aspiring to join this dynamic field, mastering key skills is essential for success. Here, we delve into the top skills every data center engineer should prioritize, shedding light on the latest trends and emphasizing the importance of continuous learning.
Innovation Women Speak! Career Pivot - How to Break into Cybersecurity

With so many areas of employment at risk such as retail, travel (airlines 50k job losses) and restaurants (over 40% may not reopen). Many are concerned about their financial futures. For good reasons.
One area that we are seeing explosive growth is cybersecurity. The Bureau of Labor and Statistics have the industry with a median income of 99k per year. And a 31% increase over the next several years with over a million job openings. This is a newer field with a great number of opportunities! Theo will offer a user friendly informational session that will provide you with real ways to get into the field.
You’ll gain:
- A complete overview of all the areas of cyber security for hiring purposes.
- An in-depth conversation about the training/education/experience needed for each area and realistic hiring expectations.
- Insider tips for FREE certification training!
India's Leading Cyber Security Company2022.pdf

Insights Success sheds the spotlight on AKS Information Technology Services, one of the most reliable and trusted cyber security company in India, in its latest edition, ‘India's Leading Cyber Security Company-2022.’
How to choose cybersecurity academy in Kerala

This pdf helps you to boost up your knowledge about cyber security and helps to choose best cyber security academy
Build your career with top cyber security jobs in 2022?

Which cyber security job is right for you? What skills do you need to fill the job? Before we answer these questions, let’s have a glimpse of why there has been an increase in the number of cyber security jobs. According to the University of Maryland, hackers attack an average of 2,244 times a day. Making it a necessity for firms to invest in cyber security, thus opening doors for individuals who want to build a cyber-security career.
DCD INTERNET 2015 BROCHURE

DCD Internet covers the full “mud to cloud” infrastructure stack and eco-system in the internet-facing, web-scale, third-platform, cloud data center.
Driven by all-things 3rd Platform and Web 3.0 – IoT, cloud, mobile, and big data/analytics – the conference program focuses on the movement toward the full-stack – physical and logical. Industry experts will uncover the impact of these next-generation IT foundation technologies and the role of the application optimized software defined infrastructure of SDDC, SDN, cloud, open-source, and hyperconvergence among others.
Hear from visionary thought-leaders and innovators leading the way toward the true “digital enterprise” in the ZettaByte era and discover how to drive costs out of the IT and data center infrastructure, reduce risk, and quicken time-to-market agility and pace.
Do not miss this chance to gain high-value perspectives and learn about the tools and techniques that will accelerate your smart
data center and cloud infrastructure and operations strategy.
How to Monitor Digital Dependencies Across Your Modern IT Stack

How to Monitor Digital Dependencies Across Your Modern IT Stack webinar
OT Security Architecture & Resilience: Designing for Security Success

Resiliency is the new imperative for OT environments. This track provides valuable insights for building a security architecture to meet the business challenge. The discussions are intended to spark conversation and this guide highlights key takeaways on what works, what doesn’t and what’s next. https://accntu.re/36gMaWm
CERTIFIED ARTIFICIAL INTELLIGENCE ENGINEER - CAIE™

The CAIE™ by the United States Artificial Intelligence Institute (USAII™) is explicitly designed to meet this challenging demand of ethical Artificial Intelligence Engineers and providing the right skillsets with the best and ultimate technical knowledge. The CAIE™ is the best qualification to demonstrate your expertise, potential, and promise for managing Artificial Intelligence Engineers' onerous responsibilities.
Similar to Technology Certificates at KSU (20)
The Ultimate Guide To Cyber Security Certifications

The Ultimate Guide To Cyber Security Certifications
Top Certification for 2023 Top 10 Certifications Top Professional Certifications

Top Certification for 2023 Top 10 Certifications Top Professional Certifications
What Cybersecurity Certifications Make You The Most Money Today.pptx

What Cybersecurity Certifications Make You The Most Money Today.pptx
The Ultimate Roadmap For CompTIA Training & Certifications

The Ultimate Roadmap For CompTIA Training & Certifications
Top Skills Every Data Center Engineer Should Master.pdf

Top Skills Every Data Center Engineer Should Master.pdf
Innovation Women Speak! Career Pivot - How to Break into Cybersecurity

Innovation Women Speak! Career Pivot - How to Break into Cybersecurity
Build your career with top cyber security jobs in 2022?

Build your career with top cyber security jobs in 2022?
How to Monitor Digital Dependencies Across Your Modern IT Stack

How to Monitor Digital Dependencies Across Your Modern IT Stack
How to Monitor Digital Dependencies Across Your Modern IT Stack

How to Monitor Digital Dependencies Across Your Modern IT Stack
OT Security Architecture & Resilience: Designing for Security Success

OT Security Architecture & Resilience: Designing for Security Success
CERTIFIED ARTIFICIAL INTELLIGENCE ENGINEER - CAIE™

CERTIFIED ARTIFICIAL INTELLIGENCE ENGINEER - CAIE™
More from College of Continuing and Professional Education
OLLI Director Dick Harp Retirement Recognition

We wish Dick Harp, director of our Osher Lifelong Learning Institute at Kennesaw State University's College of Continuing and Professional Education, the very best as he embarks on his next phase of life. Enjoy your retirement, Dick, and thank you for your generous service to OLLI for the past 20 years. We will miss you!
June 2017 Certificate Program Graduation

Graduation from the College of Continuing and Professional Education at Kennesaw State University (published in the Marietta Daily Journal)
Breanna Schnitger, KSU Phlebotomy Graduate

Breanna Schnitger was inspired by her four young girls to further her education. As a result of her successful completion of our Phlebotomy program, she was hired by WellStar Cobb Hospital.
Spring Break Camps in the Marietta Daily Journal

From cooking to robotics and beyond, our Spring Break Camps at the College of Continuing and Professional Education offer a range of creative, educational and fun camps during spring break and for two months each summer. This feature in the Marietta Daily Journal gives a sneak peek behind the scenes.
A Growing Aging Population

The U.S. Census Bureau released a report in 2014 detailing the growth of the aging population. The senior population, defined as those 65 and older, comprised 13% of the total U.S. population in 2010. That number is expected to rise to nearly 21% by 2050. For the full report, visit http://www.census.gov/content/dam/Census/library/publications/2014/demo/p23-212.pdf. For more about the Professional Development in Gerontology Certificate, visit ccpe.kennesaw.edu/gerontology.
Top Jobs in Georgia

Using data from the Bureau of Labor Statistics, this inforgraphic ranks the top growing jobs in Georgia. Leading the pack at 82% is payroll services. Other top contenders include geriatric care, computers, and healthcare.
Financial Aid Flowchart

We have so many financial aid options, from payment plans and loans to scholarships and VA Education Benefits. Follow this easy flowchart to see what might work for you. Want to know more? Give us a call or visit the financial aid page on our website: http://ccpe.kennesaw.edu/student-resources/financial-aid
CIA — Crime Investigation Adventures Camp (Summer University)

CIA — Crime Investigation Adventures Camp (Summer University)College of Continuing and Professional Education
Children in Grades 6-9 enjoyed hands-on learning in this unique summer camp from Summer University. From finding and lifting fingerprints to creating footwear impressions and analyzing bloodstain, the students used methods from real forensic scientists to step into the role of a crime investigator. It all culminated with a mock crime scene and solving the case! #SummerUFAQs for TESOL: Teaching English to Speakers of Other Languages

FAQs for TESOL: Teaching English to Speakers of Other LanguagesCollege of Continuing and Professional Education
Ever wondered what you need to get started teaching English, either here or overseas? Curious how it might fit in your career? Find out about TESOL options, requirements and benefits with our informative FAQ slideshow.
For more on our TESOL Certificate program, visit http://ksutesolcertificate.com.More from College of Continuing and Professional Education (10)
CIA — Crime Investigation Adventures Camp (Summer University)

CIA — Crime Investigation Adventures Camp (Summer University)
FAQs for TESOL: Teaching English to Speakers of Other Languages

FAQs for TESOL: Teaching English to Speakers of Other Languages
Recently uploaded
Embracing GenAI - A Strategic Imperative

Artificial Intelligence (AI) technologies such as Generative AI, Image Generators and Large Language Models have had a dramatic impact on teaching, learning and assessment over the past 18 months. The most immediate threat AI posed was to Academic Integrity with Higher Education Institutes (HEIs) focusing their efforts on combating the use of GenAI in assessment. Guidelines were developed for staff and students, policies put in place too. Innovative educators have forged paths in the use of Generative AI for teaching, learning and assessments leading to pockets of transformation springing up across HEIs, often with little or no top-down guidance, support or direction.
This Gasta posits a strategic approach to integrating AI into HEIs to prepare staff, students and the curriculum for an evolving world and workplace. We will highlight the advantages of working with these technologies beyond the realm of teaching, learning and assessment by considering prompt engineering skills, industry impact, curriculum changes, and the need for staff upskilling. In contrast, not engaging strategically with Generative AI poses risks, including falling behind peers, missed opportunities and failing to ensure our graduates remain employable. The rapid evolution of AI technologies necessitates a proactive and strategic approach if we are to remain relevant.
Operation Blue Star - Saka Neela Tara

Operation “Blue Star” is the only event in the history of Independent India where the state went into war with its own people. Even after about 40 years it is not clear if it was culmination of states anger over people of the region, a political game of power or start of dictatorial chapter in the democratic setup.
The people of Punjab felt alienated from main stream due to denial of their just demands during a long democratic struggle since independence. As it happen all over the word, it led to militant struggle with great loss of lives of military, police and civilian personnel. Killing of Indira Gandhi and massacre of innocent Sikhs in Delhi and other India cities was also associated with this movement.
TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH A...

TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH ANSWERS.
Overview on Edible Vaccine: Pros & Cons with Mechanism

This ppt include the description of the edible vaccine i.e. a new concept over the traditional vaccine administered by injection.
"Protectable subject matters, Protection in biotechnology, Protection of othe...

Protectable subject matters, Protection in biotechnology, Protection of other biological materials, Ownership and period of protection
Instructions for Submissions thorugh G- Classroom.pptx

This presentation provides a briefing on how to upload submissions and documents in Google Classroom. It was prepared as part of an orientation for new Sainik School in-service teacher trainees. As a training officer, my goal is to ensure that you are comfortable and proficient with this essential tool for managing assignments and fostering student engagement.
CACJapan - GROUP Presentation 1- Wk 4.pdf

Macroeconomics- Movie Location
This will be used as part of your Personal Professional Portfolio once graded.
Objective:
Prepare a presentation or a paper using research, basic comparative analysis, data organization and application of economic information. You will make an informed assessment of an economic climate outside of the United States to accomplish an entertainment industry objective.
Unit 8 - Information and Communication Technology (Paper I).pdf

This slides describes the basic concepts of ICT, basics of Email, Emerging Technology and Digital Initiatives in Education. This presentations aligns with the UGC Paper I syllabus.
Home assignment II on Spectroscopy 2024 Answers.pdf

Answers to Home assignment on UV-Visible spectroscopy: Calculation of wavelength of UV-Visible absorption
Welcome to TechSoup New Member Orientation and Q&A (May 2024).pdf

In this webinar you will learn how your organization can access TechSoup's wide variety of product discount and donation programs. From hardware to software, we'll give you a tour of the tools available to help your nonprofit with productivity, collaboration, financial management, donor tracking, security, and more.
1.4 modern child centered education - mahatma gandhi-2.pptx

Child centred education is an educational approach that priorities the interest, needs and abilities of the child in the learning process.
Acetabularia Information For Class 9 .docx

Acetabularia acetabulum is a single-celled green alga that in its vegetative state is morphologically differentiated into a basal rhizoid and an axially elongated stalk, which bears whorls of branching hairs. The single diploid nucleus resides in the rhizoid.
The approach at University of Liverpool.pptx

How libraries can support authors with open access requirements for UKRI funded books
Wednesday 22 May 2024, 14:00-15:00.
Chapter 3 - Islamic Banking Products and Services.pptx

Chapter 3 - Islamic Banking Products and Services.pptxMohd Adib Abd Muin, Senior Lecturer at Universiti Utara Malaysia
This slide is prepared for master's students (MIFB & MIBS) UUM. May it be useful to all.CLASS 11 CBSE B.St Project AIDS TO TRADE - INSURANCE

Class 11 CBSE Business Studies Project ( AIDS TO TRADE - INSURANCE)
678020731-Sumas-y-Restas-Para-Colorear.pdf

KKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKK
Recently uploaded (20)
TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH A...

TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH A...
Overview on Edible Vaccine: Pros & Cons with Mechanism

Overview on Edible Vaccine: Pros & Cons with Mechanism
"Protectable subject matters, Protection in biotechnology, Protection of othe...

"Protectable subject matters, Protection in biotechnology, Protection of othe...
Instructions for Submissions thorugh G- Classroom.pptx

Instructions for Submissions thorugh G- Classroom.pptx
Unit 8 - Information and Communication Technology (Paper I).pdf

Unit 8 - Information and Communication Technology (Paper I).pdf
Home assignment II on Spectroscopy 2024 Answers.pdf

Home assignment II on Spectroscopy 2024 Answers.pdf
Welcome to TechSoup New Member Orientation and Q&A (May 2024).pdf

Welcome to TechSoup New Member Orientation and Q&A (May 2024).pdf
1.4 modern child centered education - mahatma gandhi-2.pptx

1.4 modern child centered education - mahatma gandhi-2.pptx
Chapter 3 - Islamic Banking Products and Services.pptx

Chapter 3 - Islamic Banking Products and Services.pptx
CLASS 11 CBSE B.St Project AIDS TO TRADE - INSURANCE

CLASS 11 CBSE B.St Project AIDS TO TRADE - INSURANCE
Technology Certificates at KSU
- 1. ” ” Get tech savvy in a booming field: • AutoCAD Essentials; Intermediate; Advanced • Bookkeeper Professional • Cisco CCNA • Ethical Hacker • Information Systems Security Professional • Social Media Marketing • Web Design & Development Technology Programs ccpe.kennesaw.edu // 470-578-6765 EMPOWER // REINVENT // SUCCEED GAIN AN EDGE Productivity is the key to success. Maintain your competitive edge by staying current in the fluid field of technology. These courses are designed for individuals seeking to change or advance in their careers, or for businesses looking to train employees to help boost the company’s bottom line. The instructors were actually subject matter experts actively working in the profession they teach. The return on investment was huge. David Drake, Web Design & Development graduate “The ISSP program helped me tremendously with getting my arms around the concept of cyber security. It was of great benefit to someone who has not yet worked in an IT department. Annette Reed, Information Systems Security Professional (ISSP) graduate COLLEGE OF CONTINUING & PROFESSIONAL EDUCATION
- 2. TECHNOLOGY PROGRAMS AutoCAD Essentials; Intermediate; Advanced Learn the most widely used computer-aided design (CAD) software for producing architectural, engineering and construction drawings. This class benefits individuals in engineering, construction, and architecture industries. Bookkeeper Professional Are you a number cruncher? This unique course will provide you the skills necessary to become savvy with the QuickBooks accounting software package installed on an individually-assigned, remote computer. Cisco CCNA Gain knowledge to earn the necessary credentials to advance your networking career. Cisco certifications are among the top-paying IT certifications (Global Knowledge). Ethical Hacker Become an expert who systematically attempts to penetrate a computer system or network. By identifying weaknesses in target systems, you will use the same methods and tools as a hacker, but in a lawful and ethical manner to evaluate the target system’s security. Information Systems Security Professional Data breaches continue at alarming rates. Be the solution by learning to secure information systems while becoming thoroughly familiar with the domains of the CISSP® Common Body of Knowledge. Social Media Marketing Are you social savvy? Catch up with one of the fastest moving mediums by effectively using social media to market your business, expand brand awareness, and increase exposure and – ultimately – revenue. Web Design & Development Learn the integral design principles and industry tools to put you at the forefront of technology. The Department of Labor projects Web Designer jobs to increase by 20% through 2022. Gain an Edge ccpe.kennesaw.edu // 470-578-6765 REINVENT SUCCEED EMPOWER
