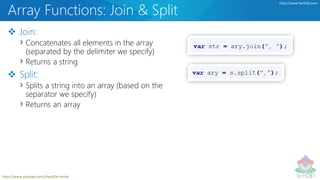
The document provides an in-depth overview of JavaScript arrays, covering topics such as different types of declarations, initialization methods, associative arrays, and nested arrays. It includes demonstrations of various array functions such as push, pop, shift, unshift, join, and splice, along with the potential pitfalls of using array.length. Overall, it serves as a comprehensive resource for understanding and manipulating arrays in JavaScript.