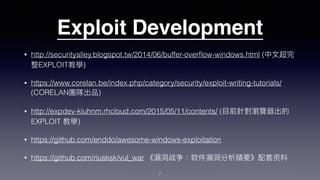
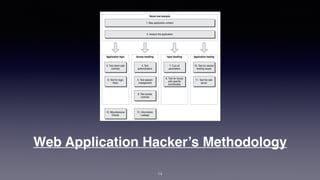
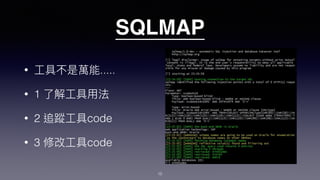
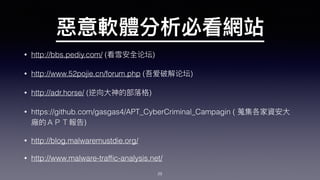
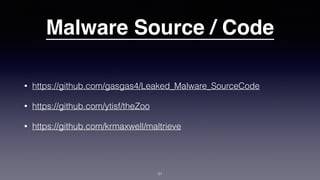
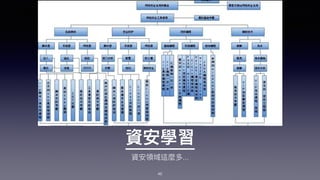
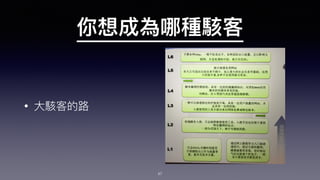
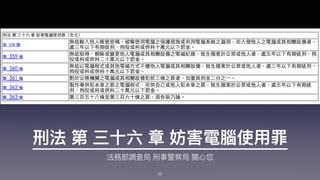
This document contains an agenda for a presentation that includes topics such as exploit development, web application hacking methodology, SQLMap, vulnerability assessment, malware analysis, reverse engineering, and cybersecurity conferences. It also addresses frequently asked questions about capture the flag events, bug bounty programs, and security certifications. Resources like exploit code examples, tool documentation, hacking forums, and malware repositories are listed.