Embed presentation
Download as PDF, PPTX













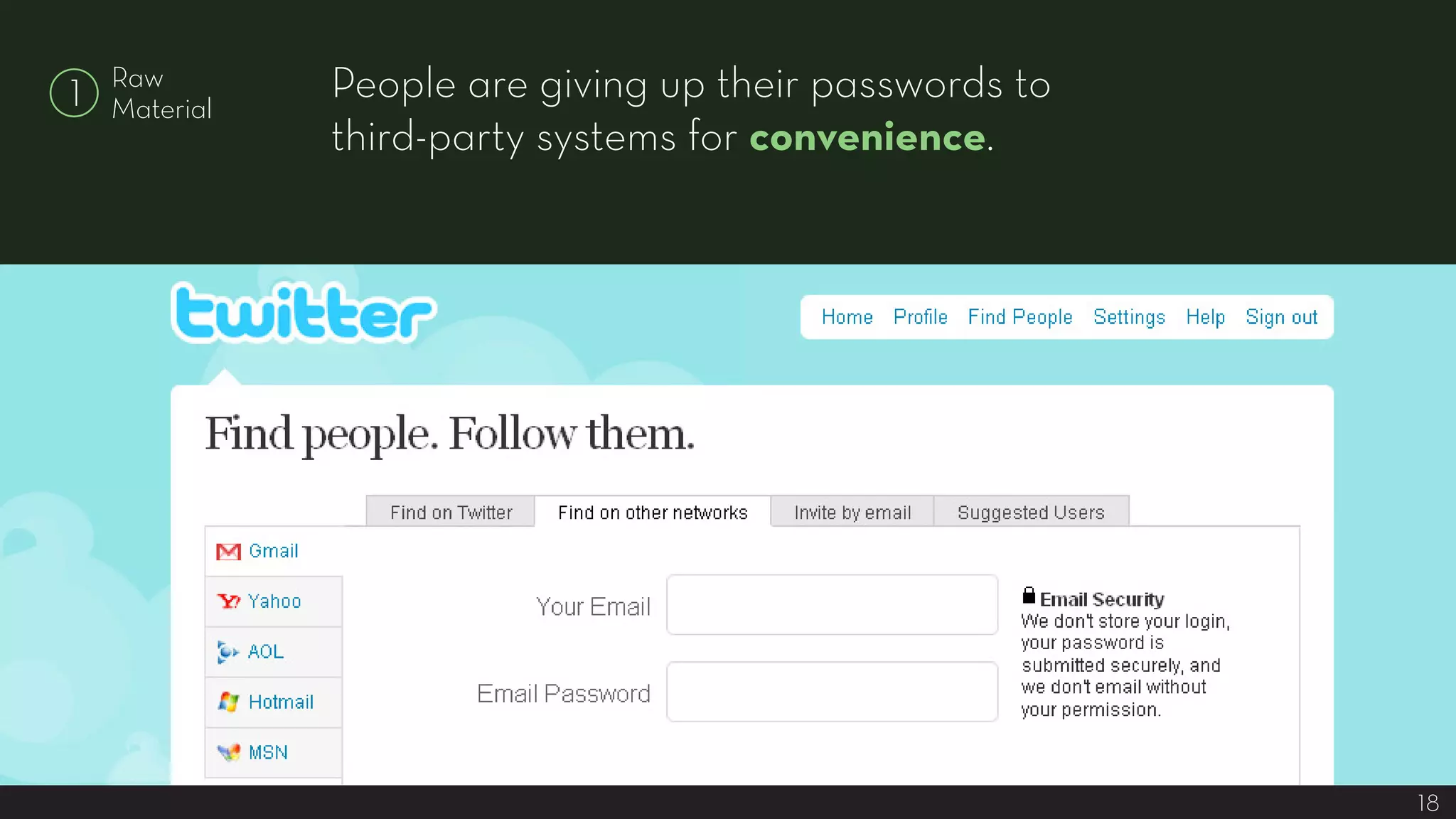










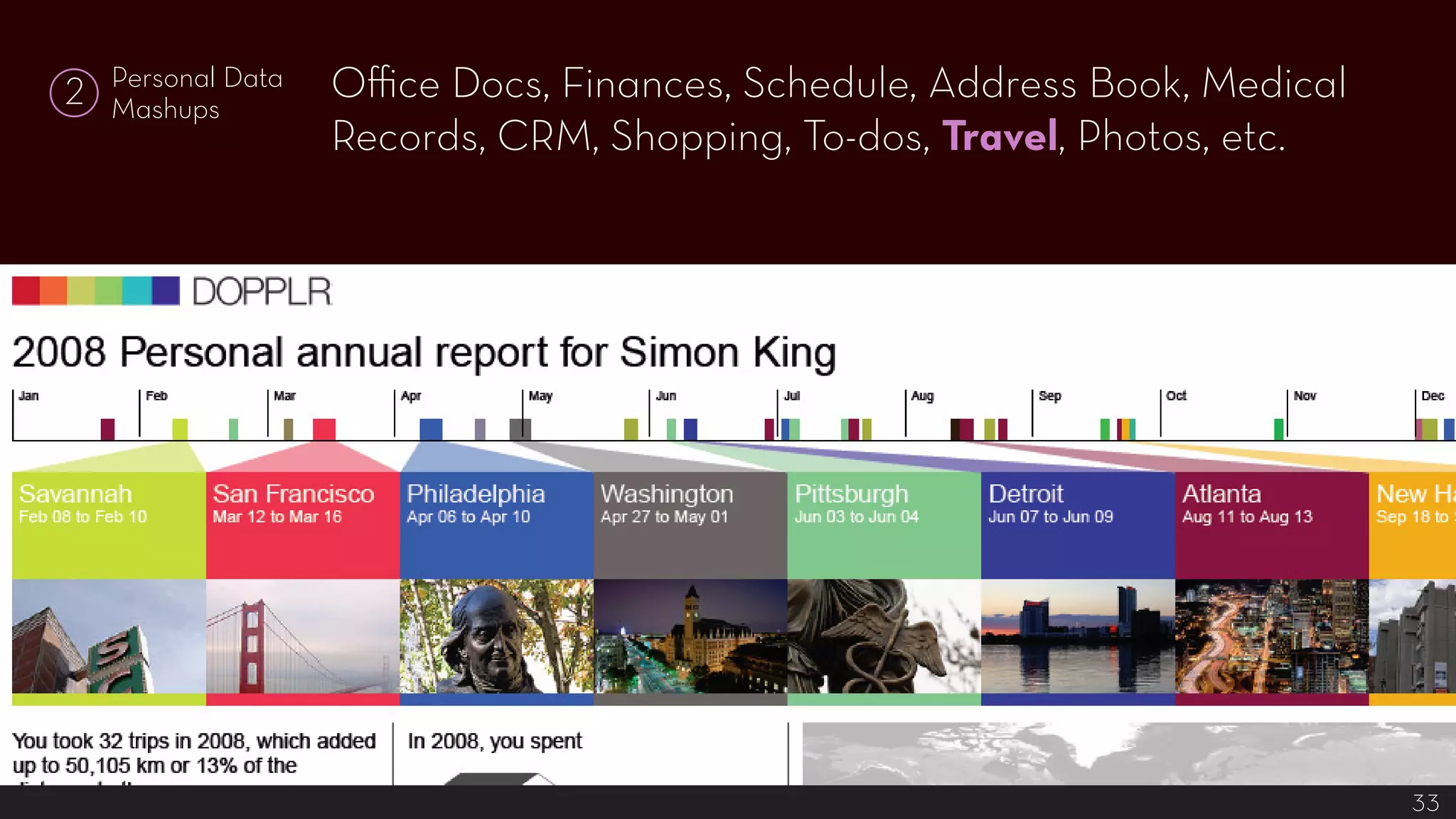
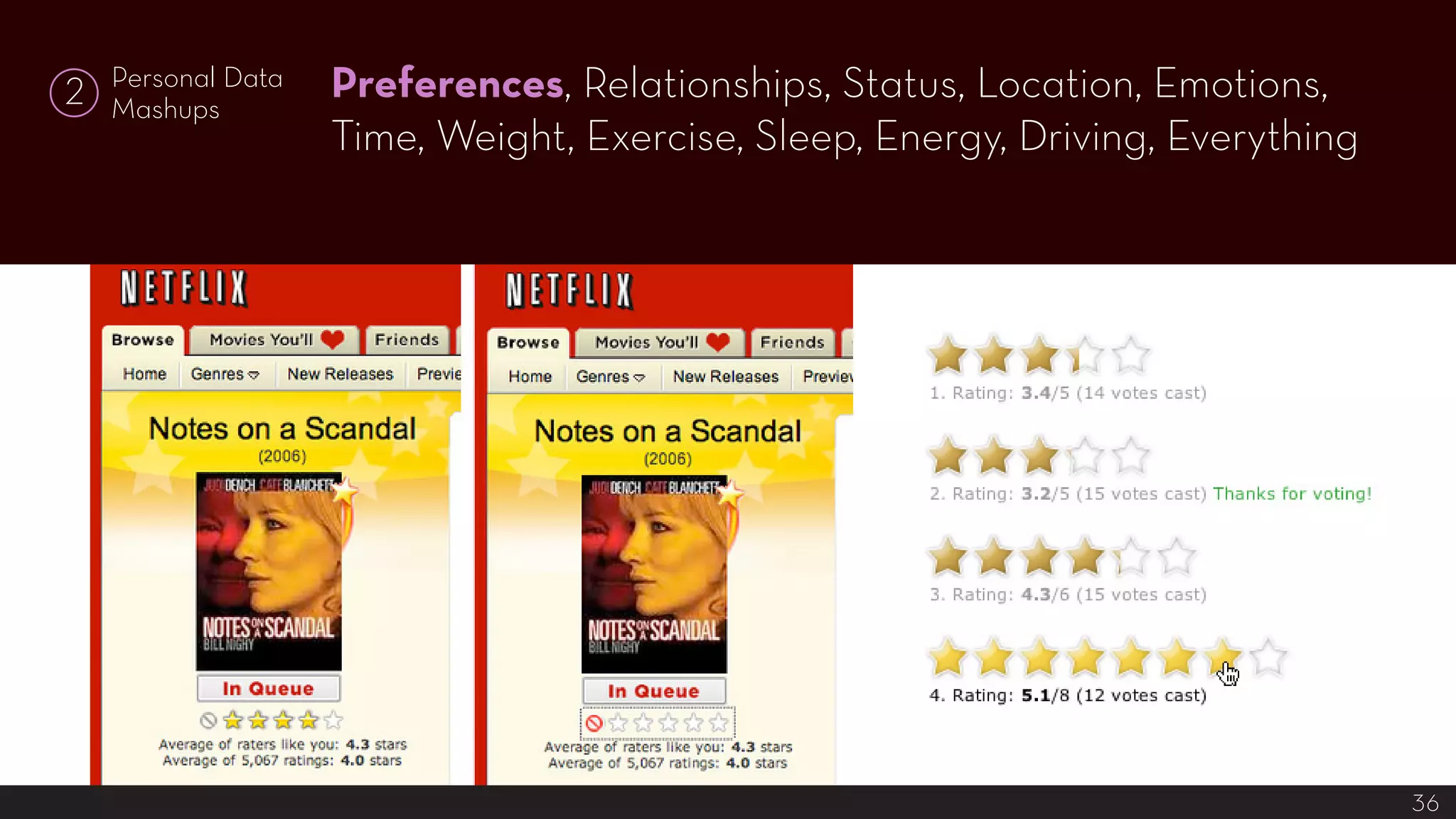




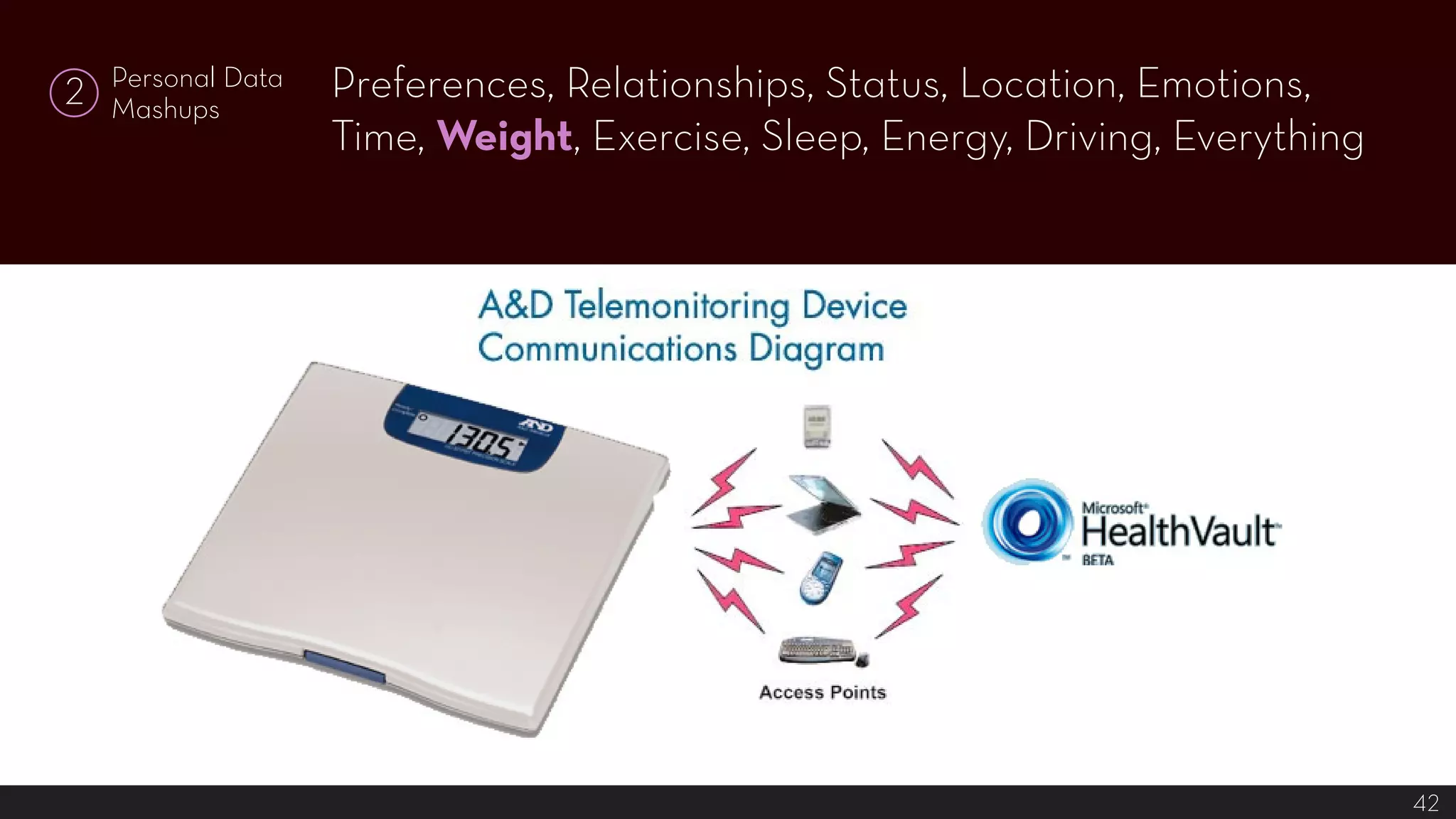
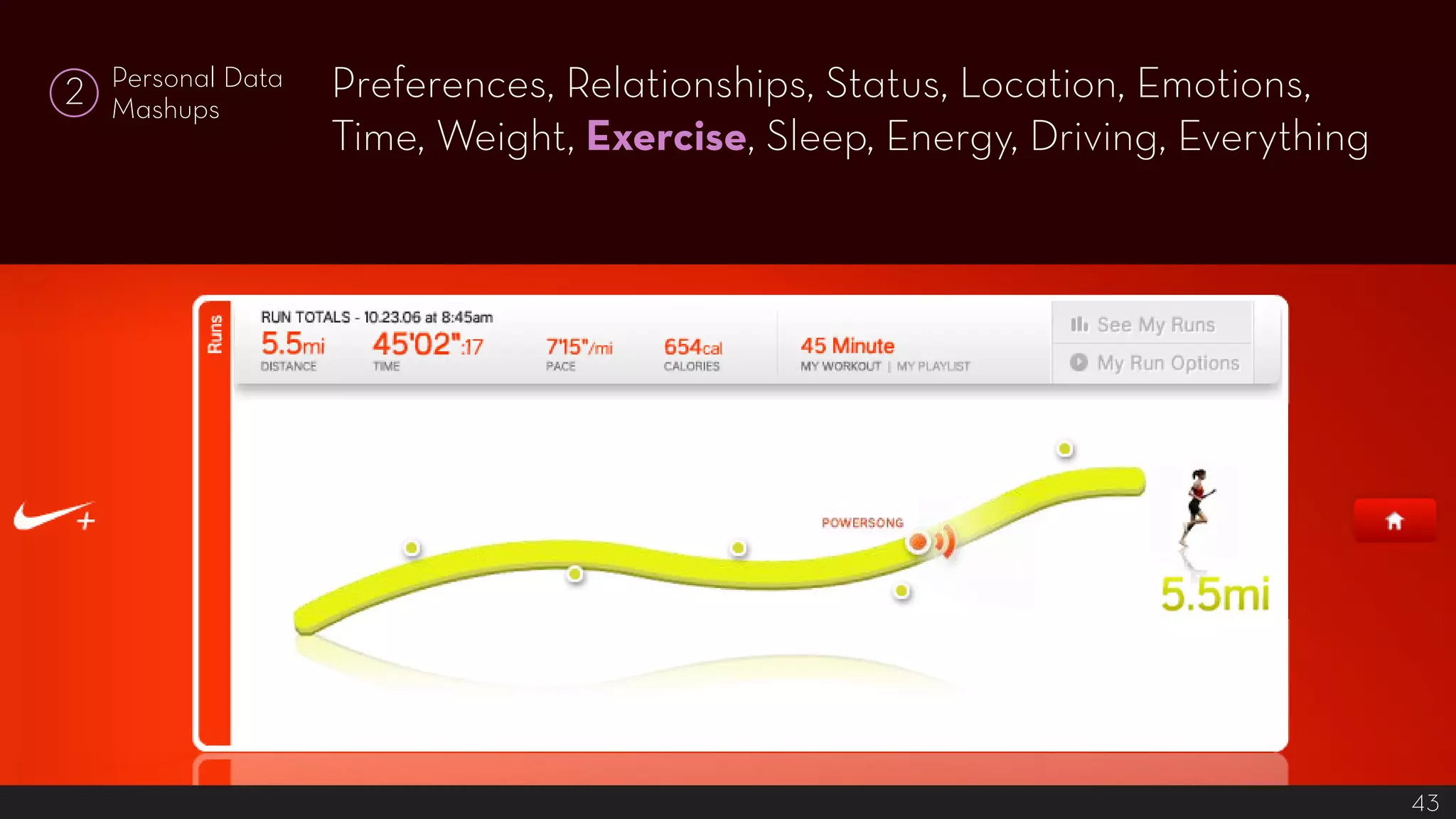










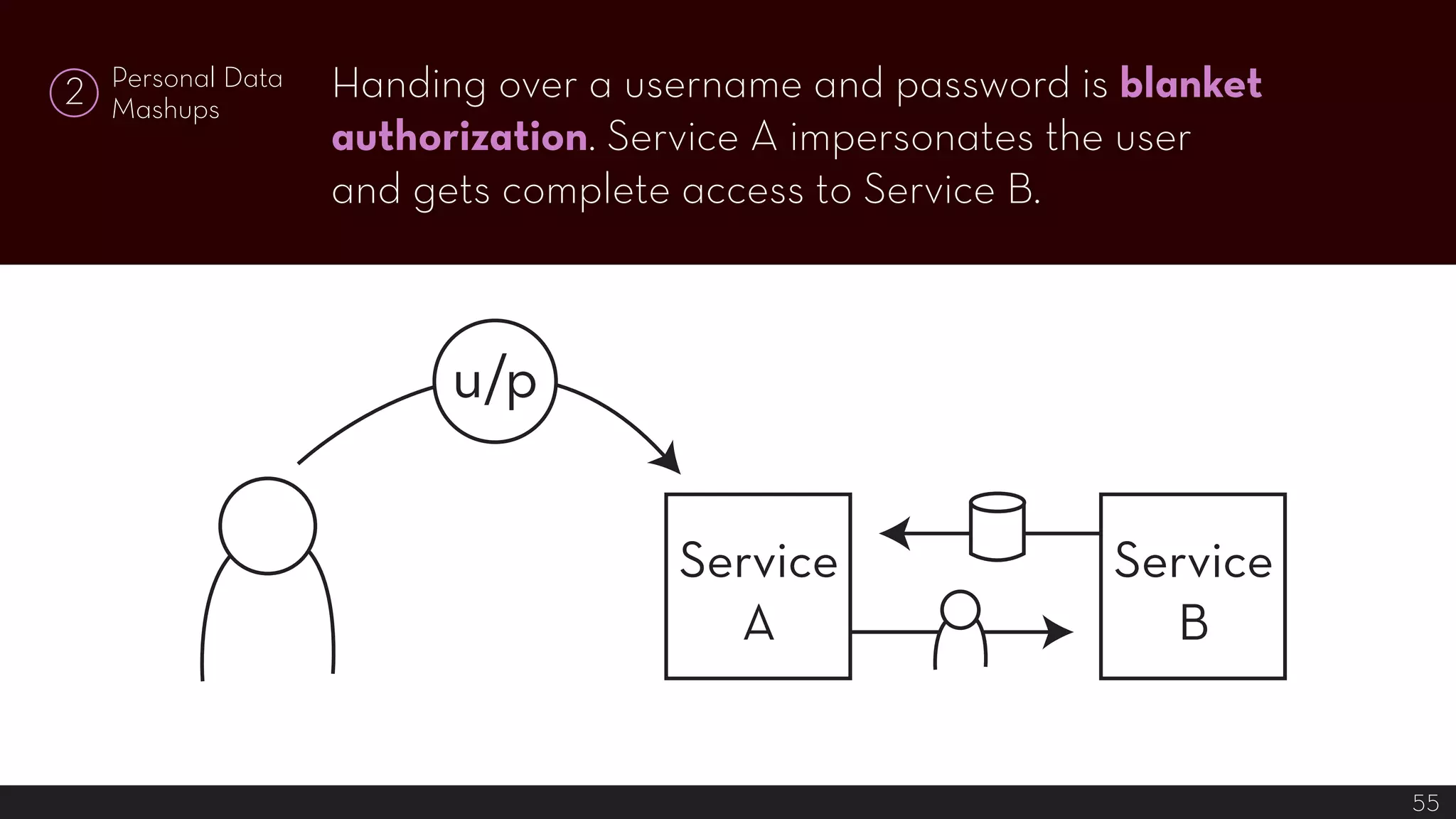



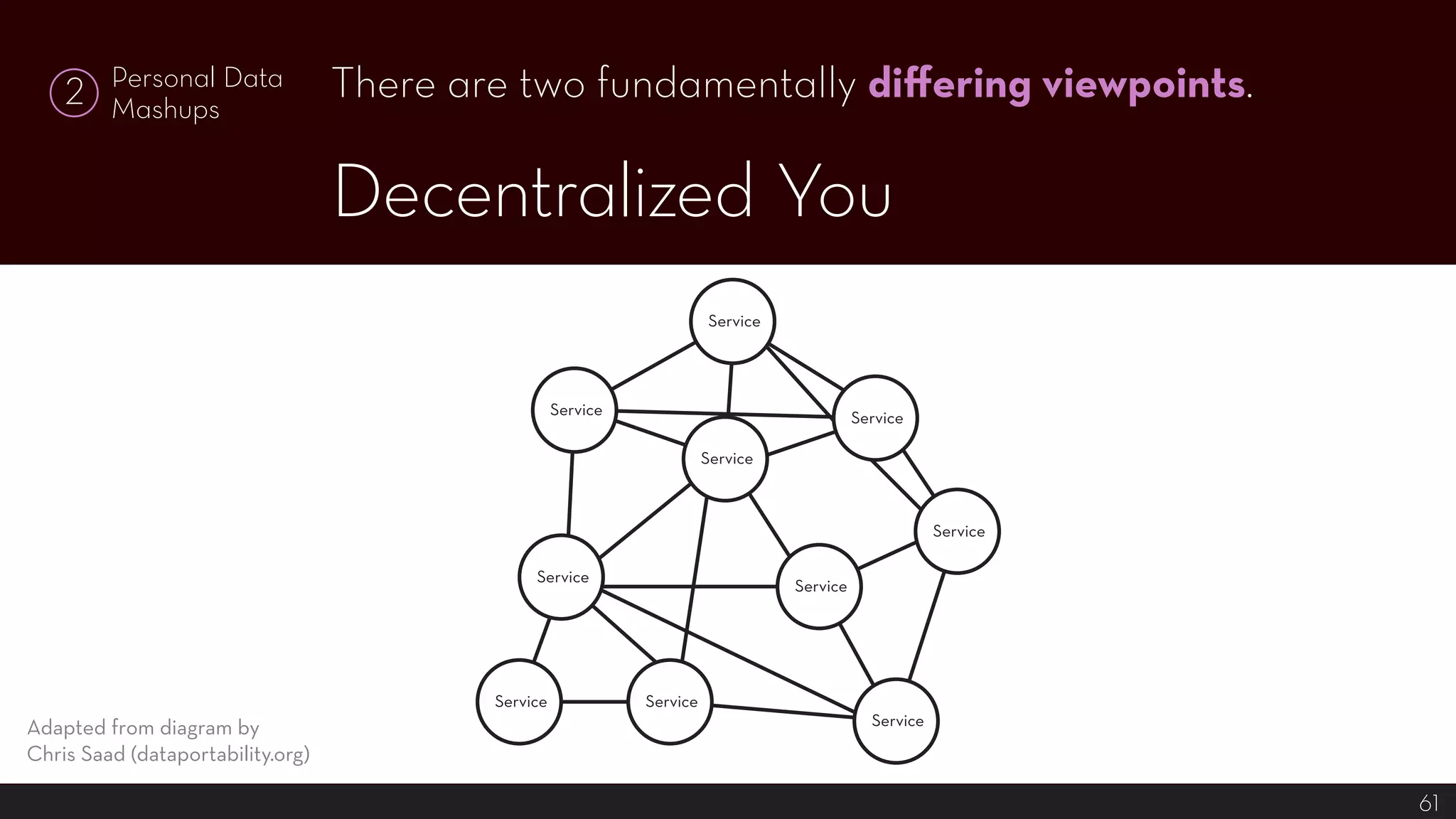


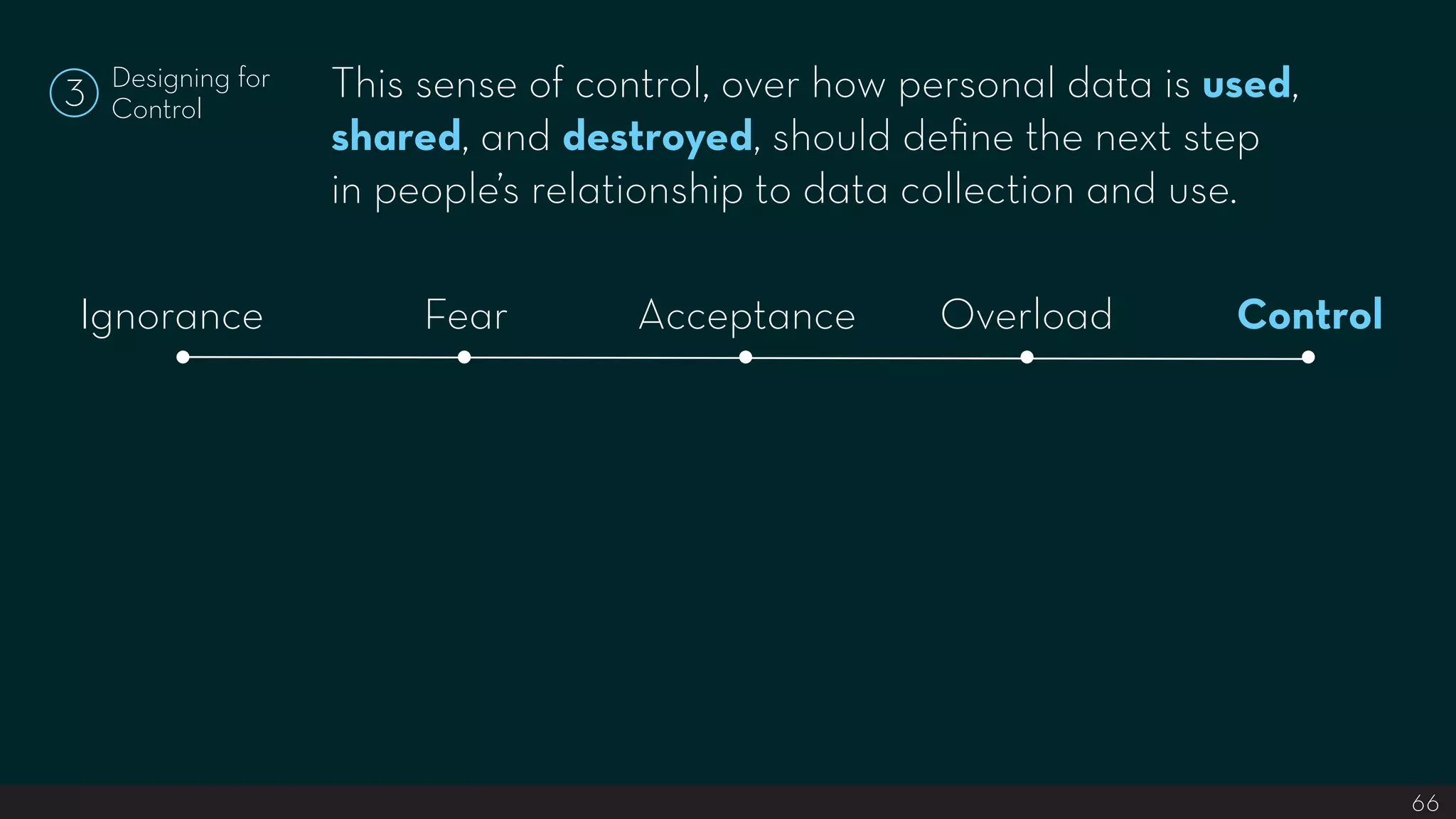
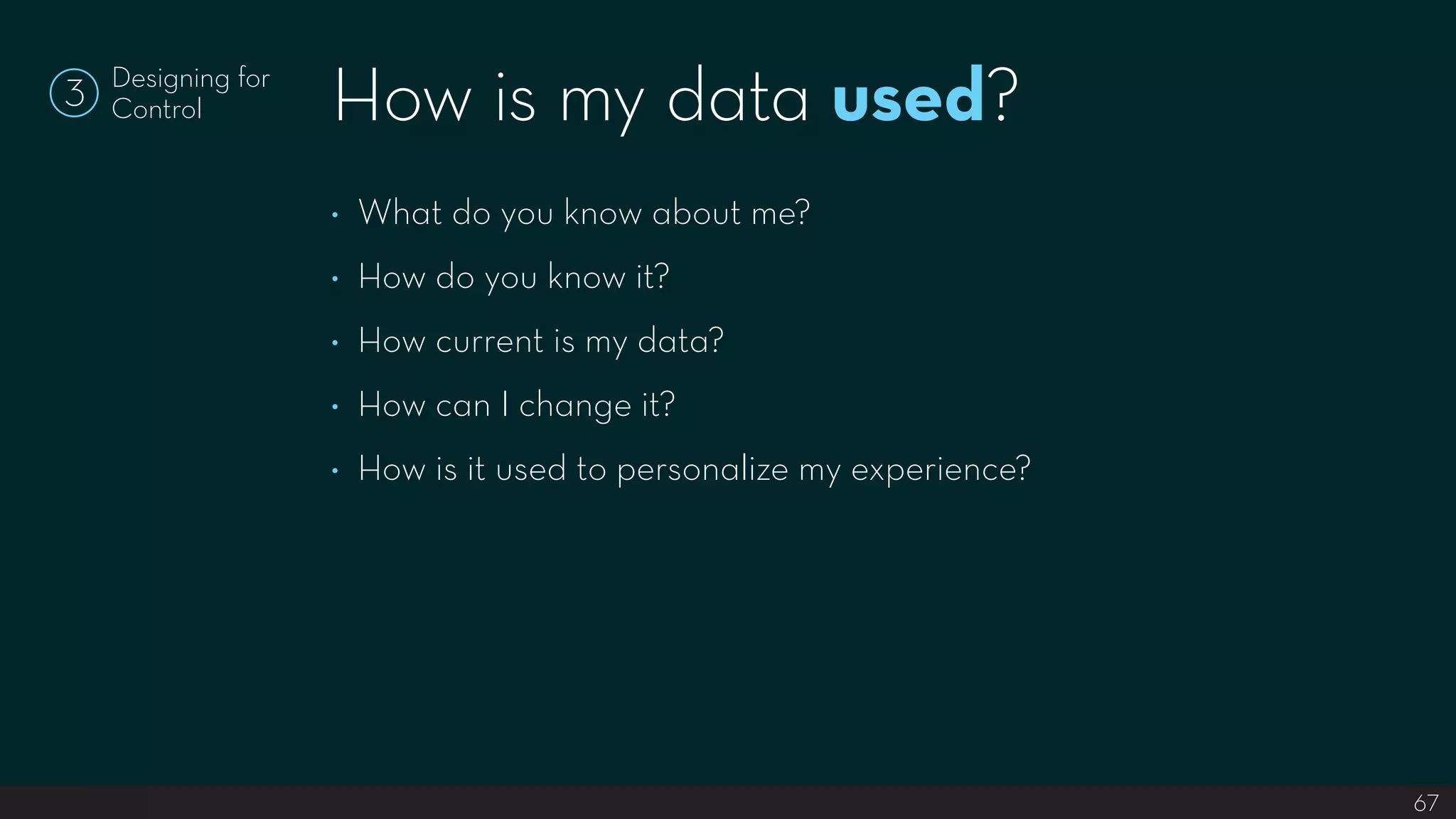
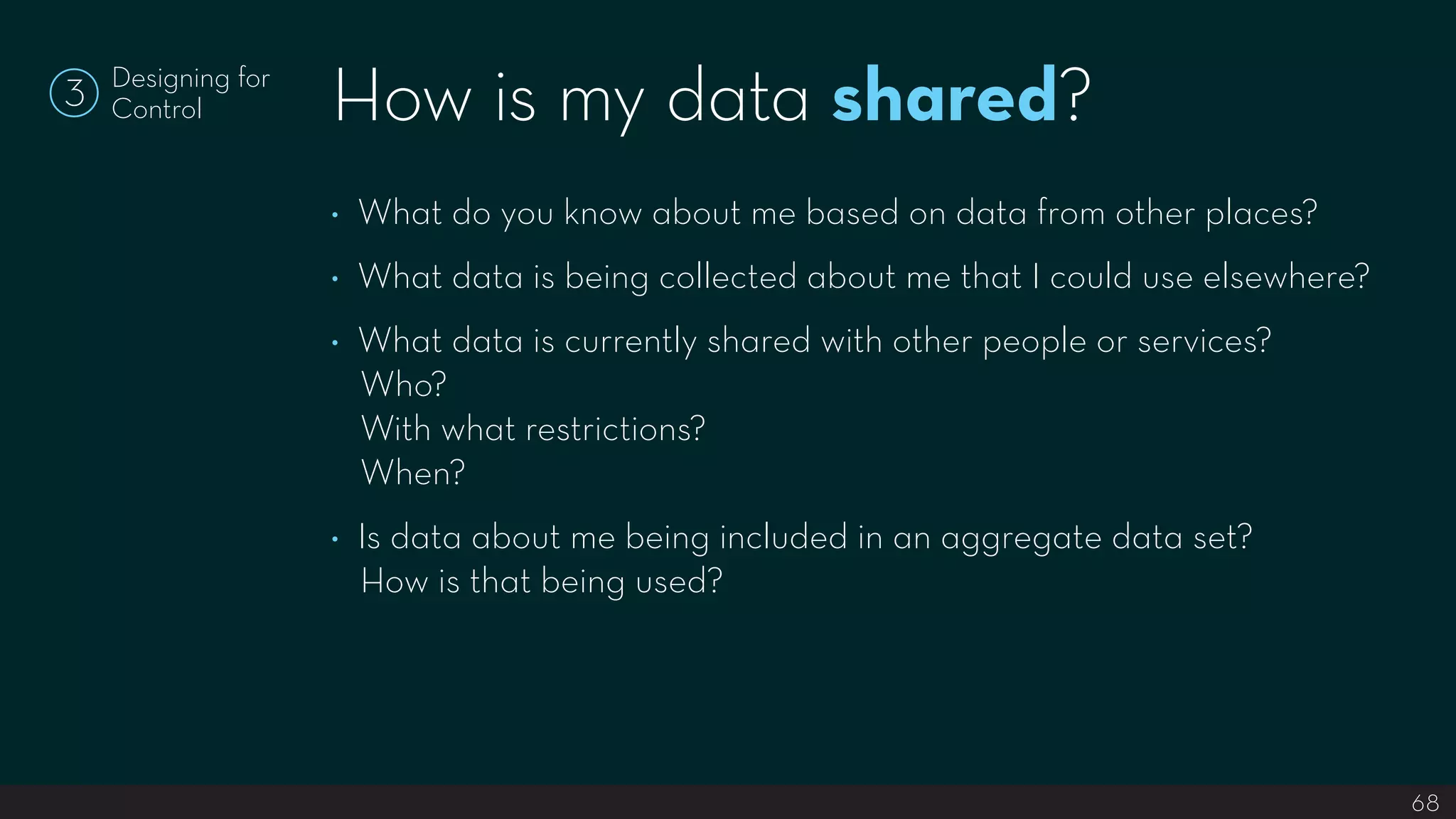




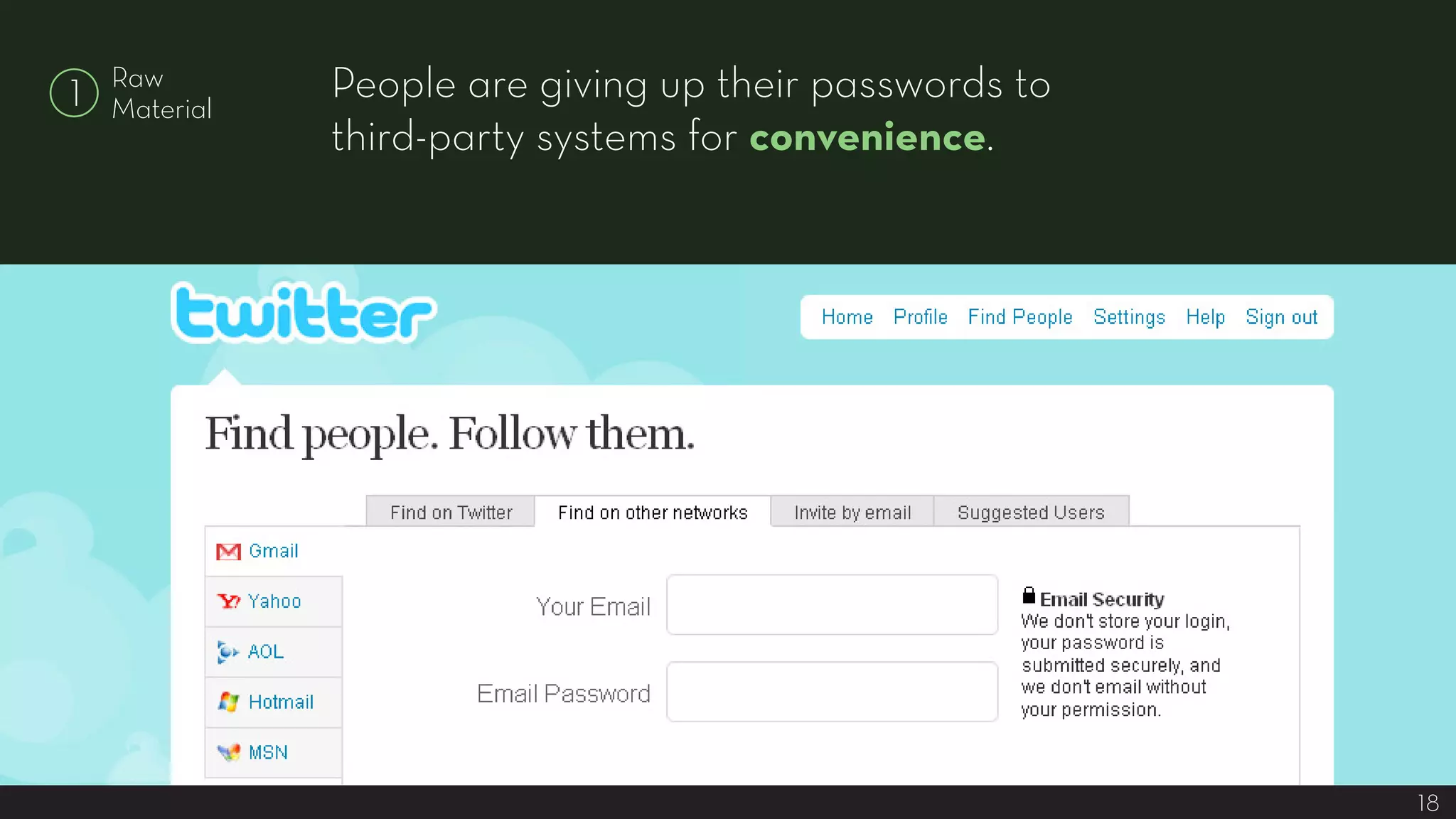
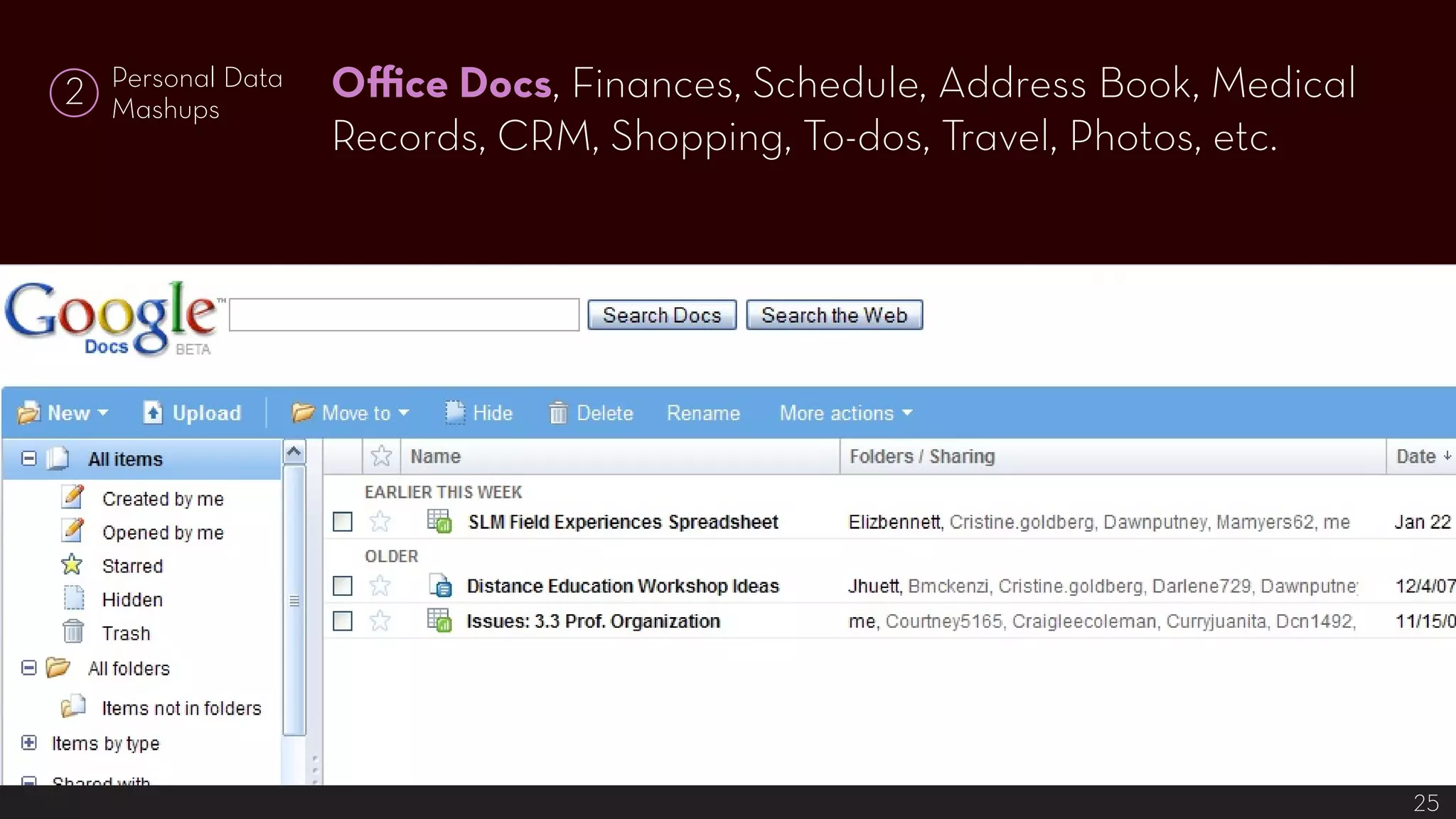
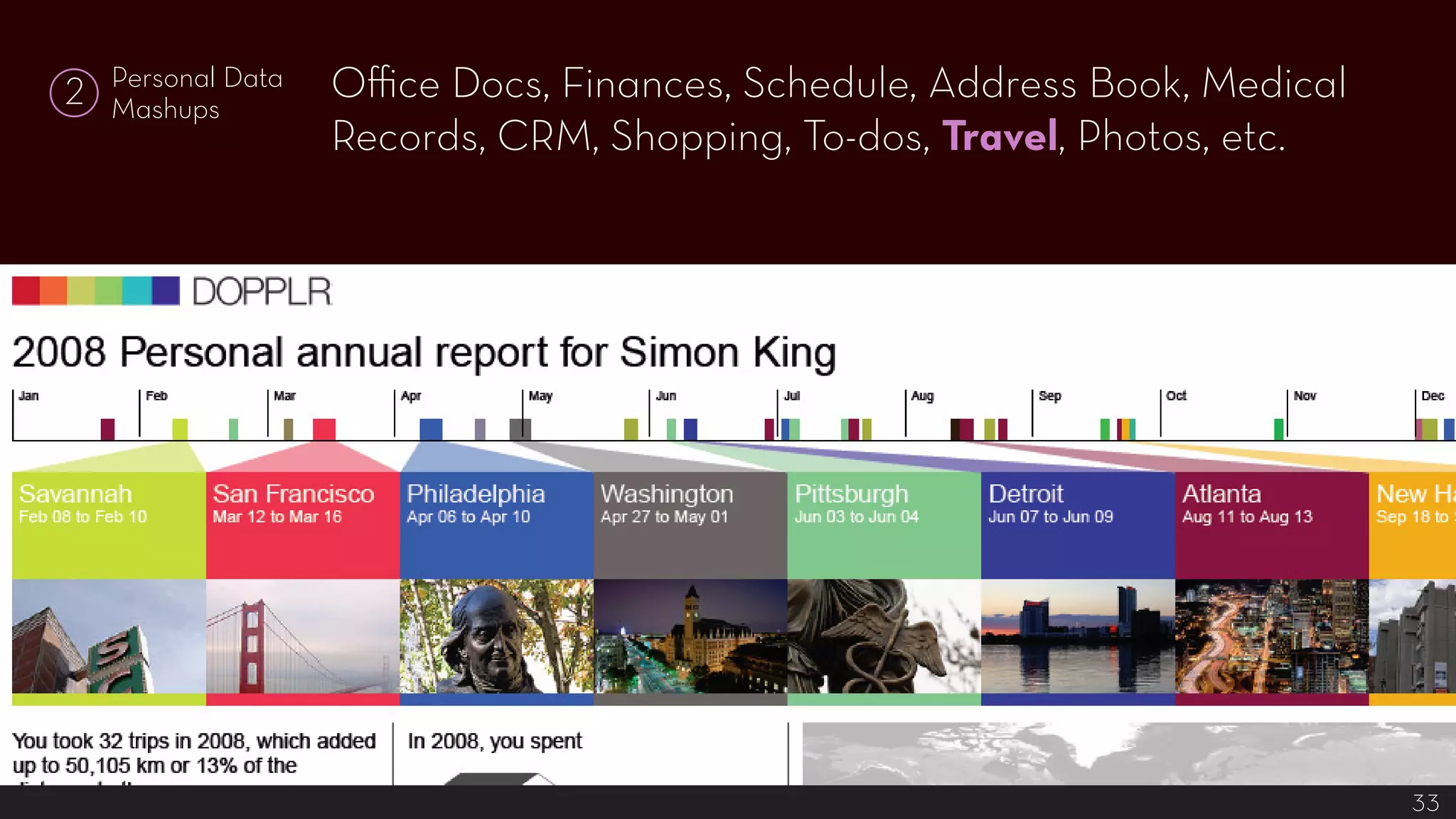
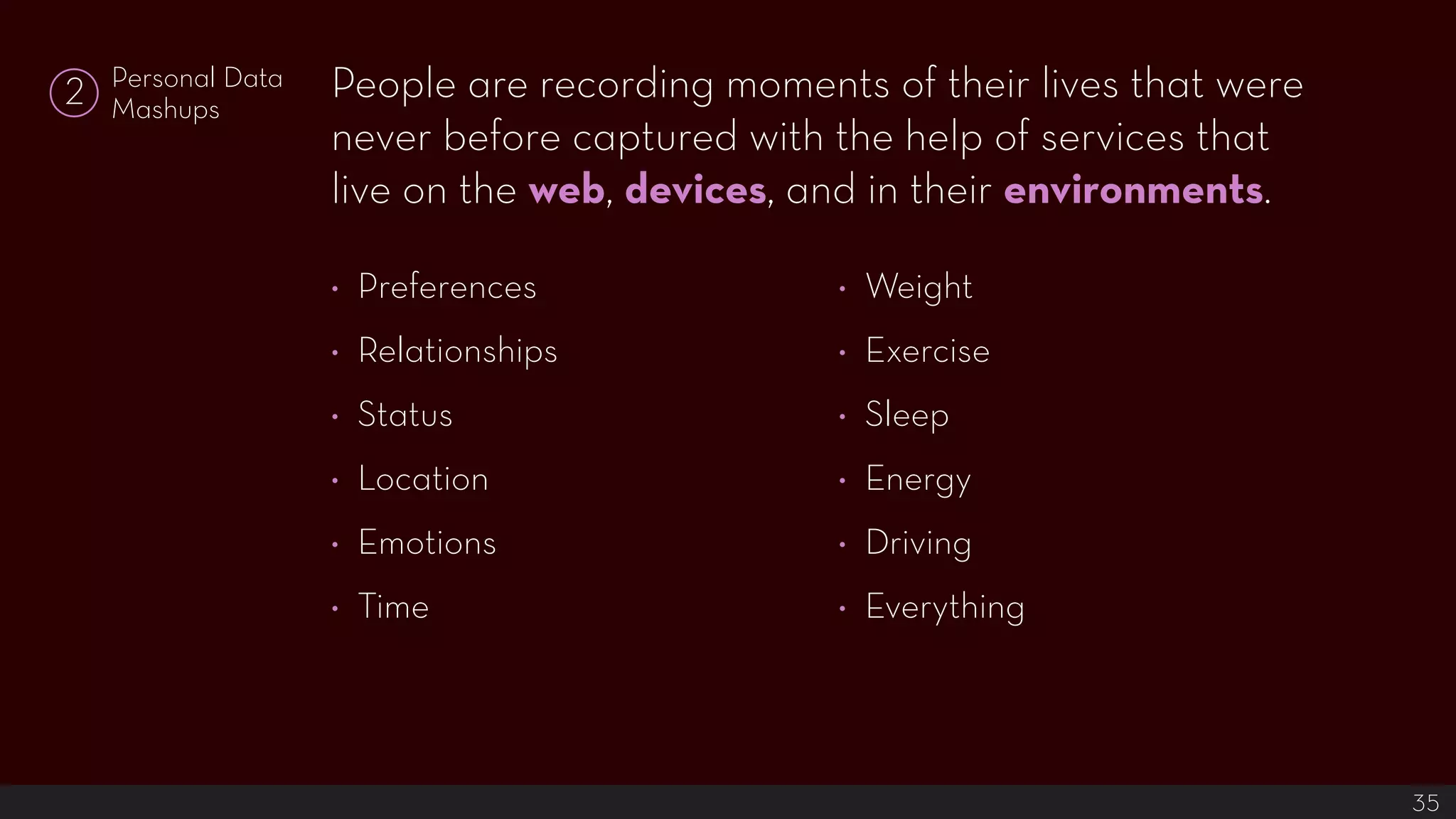
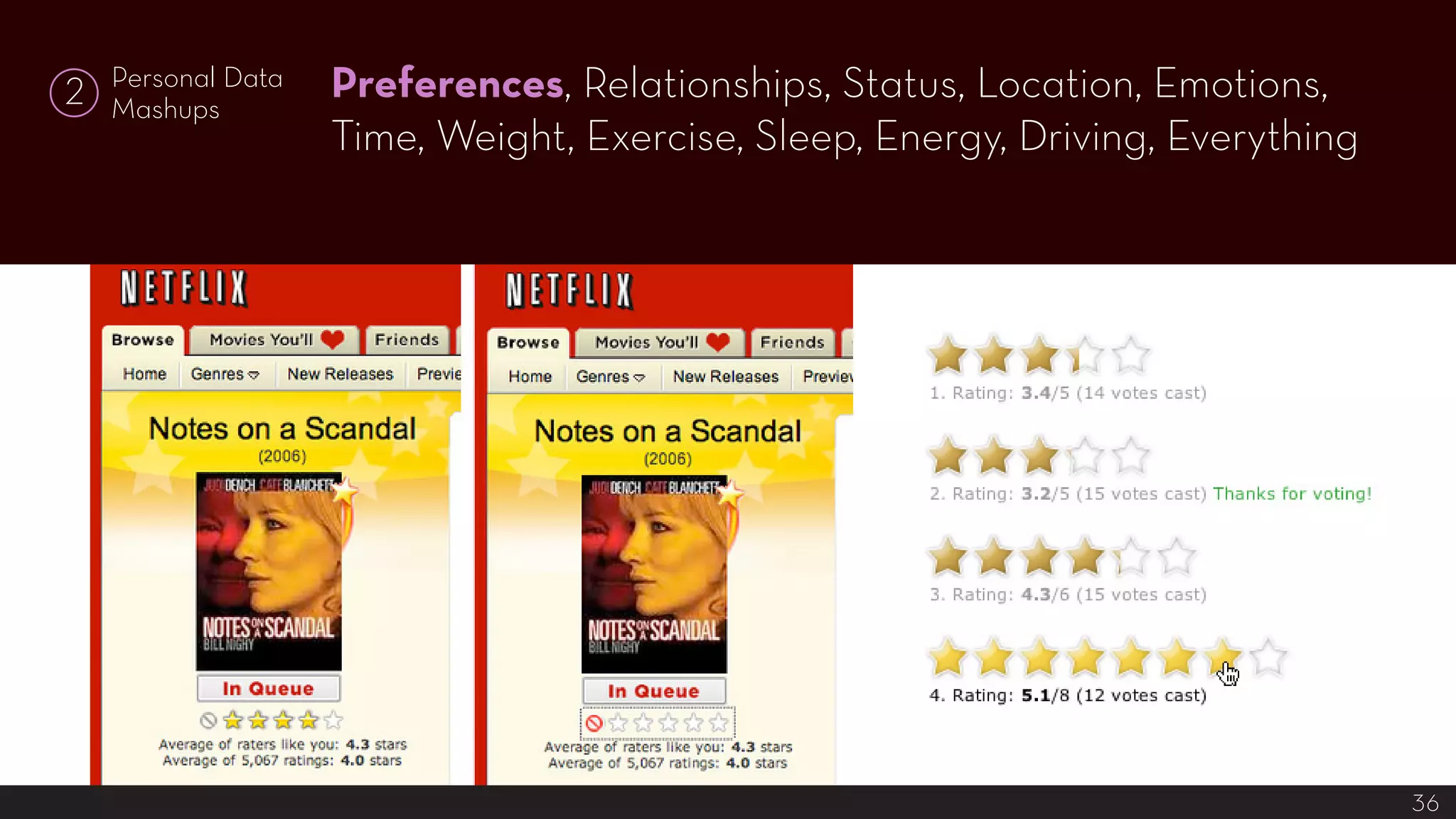
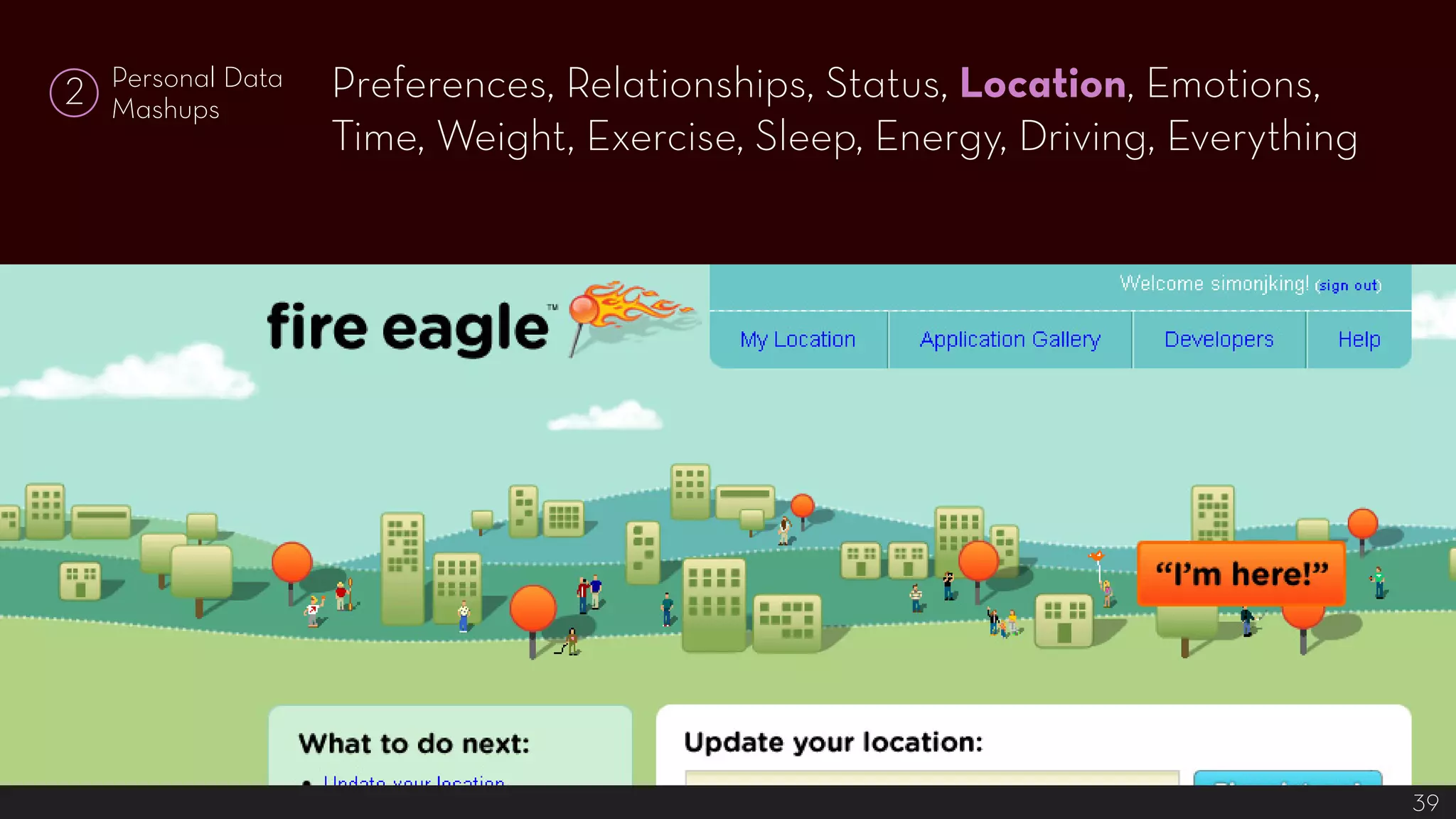
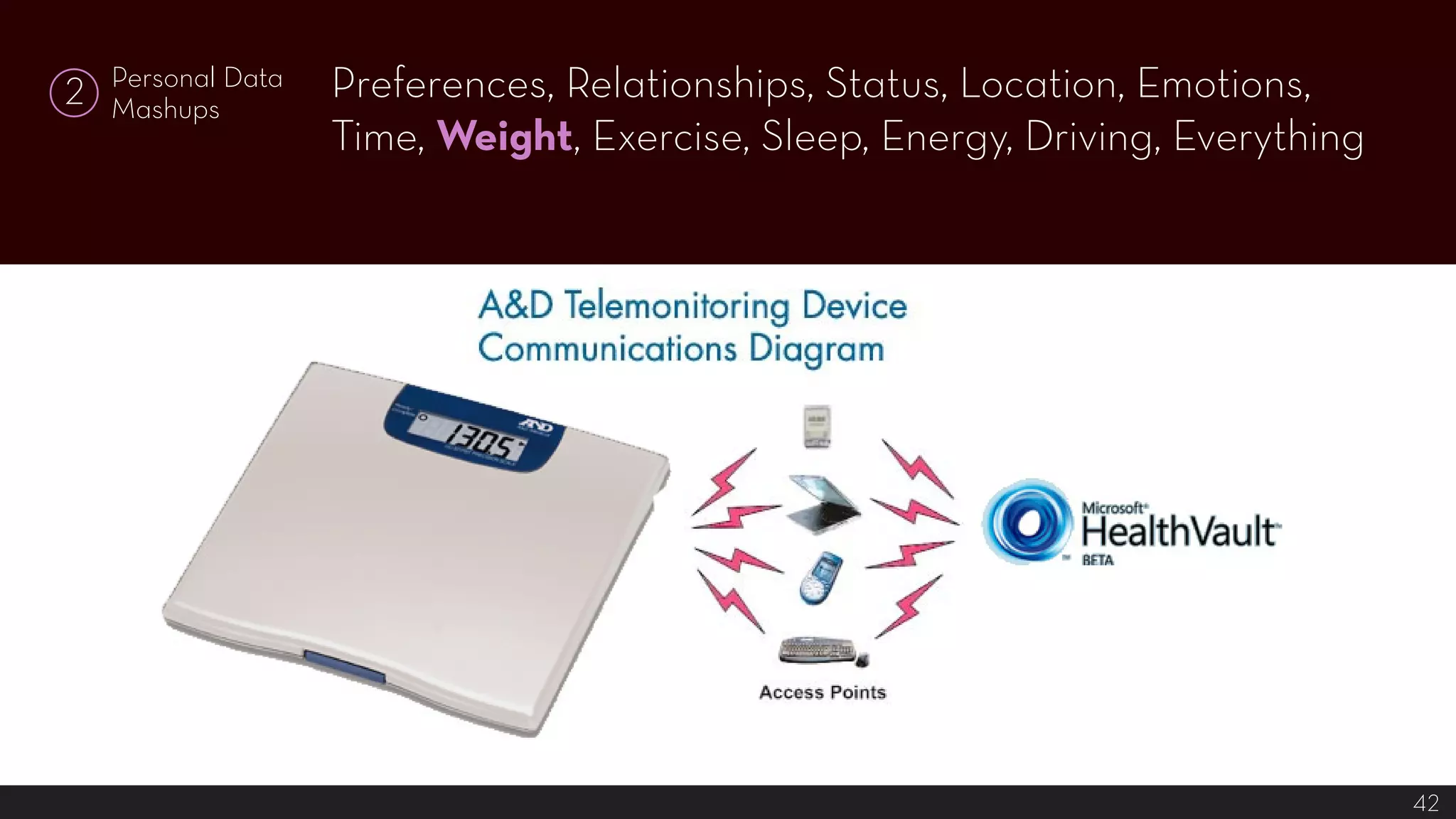
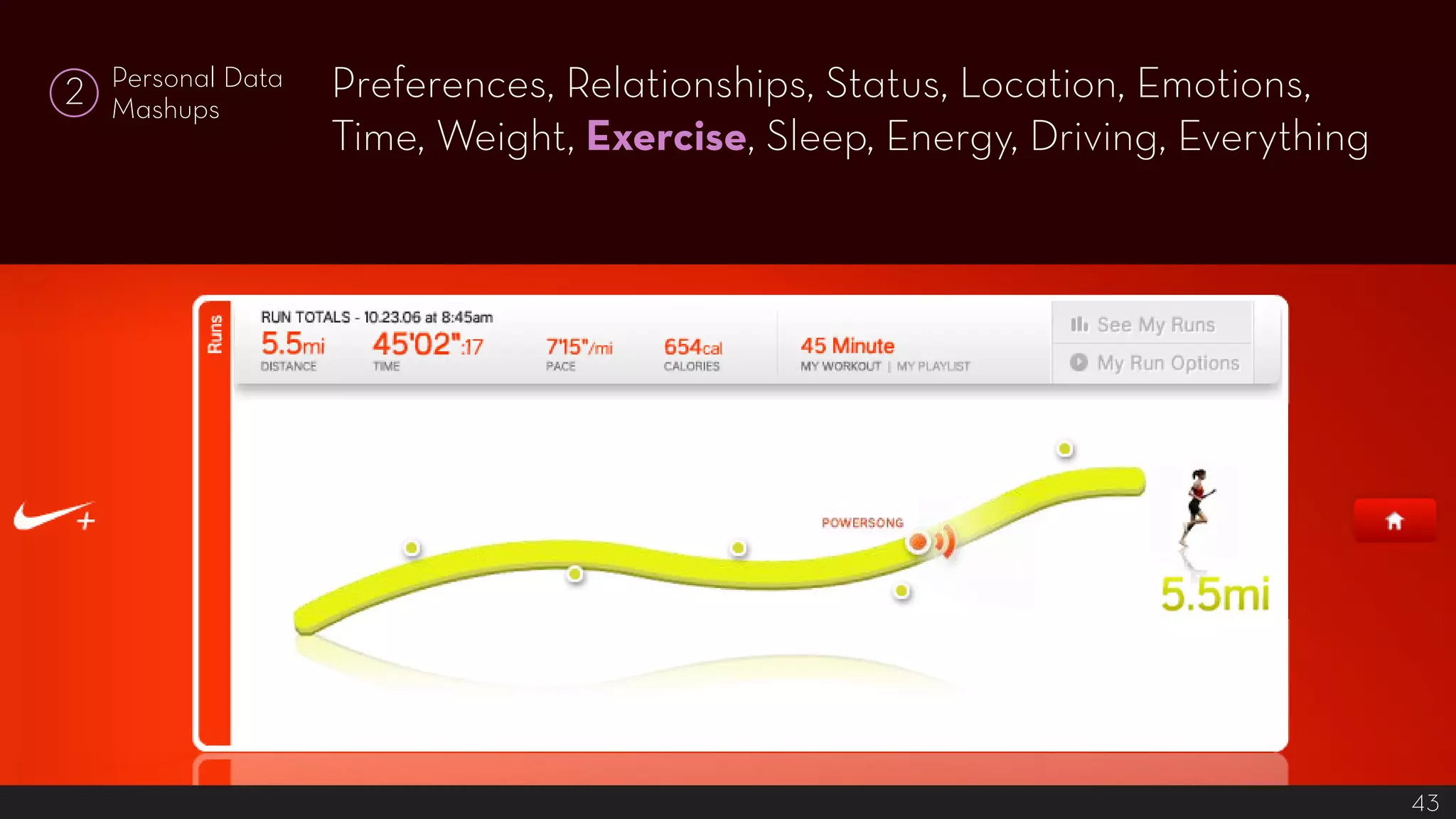
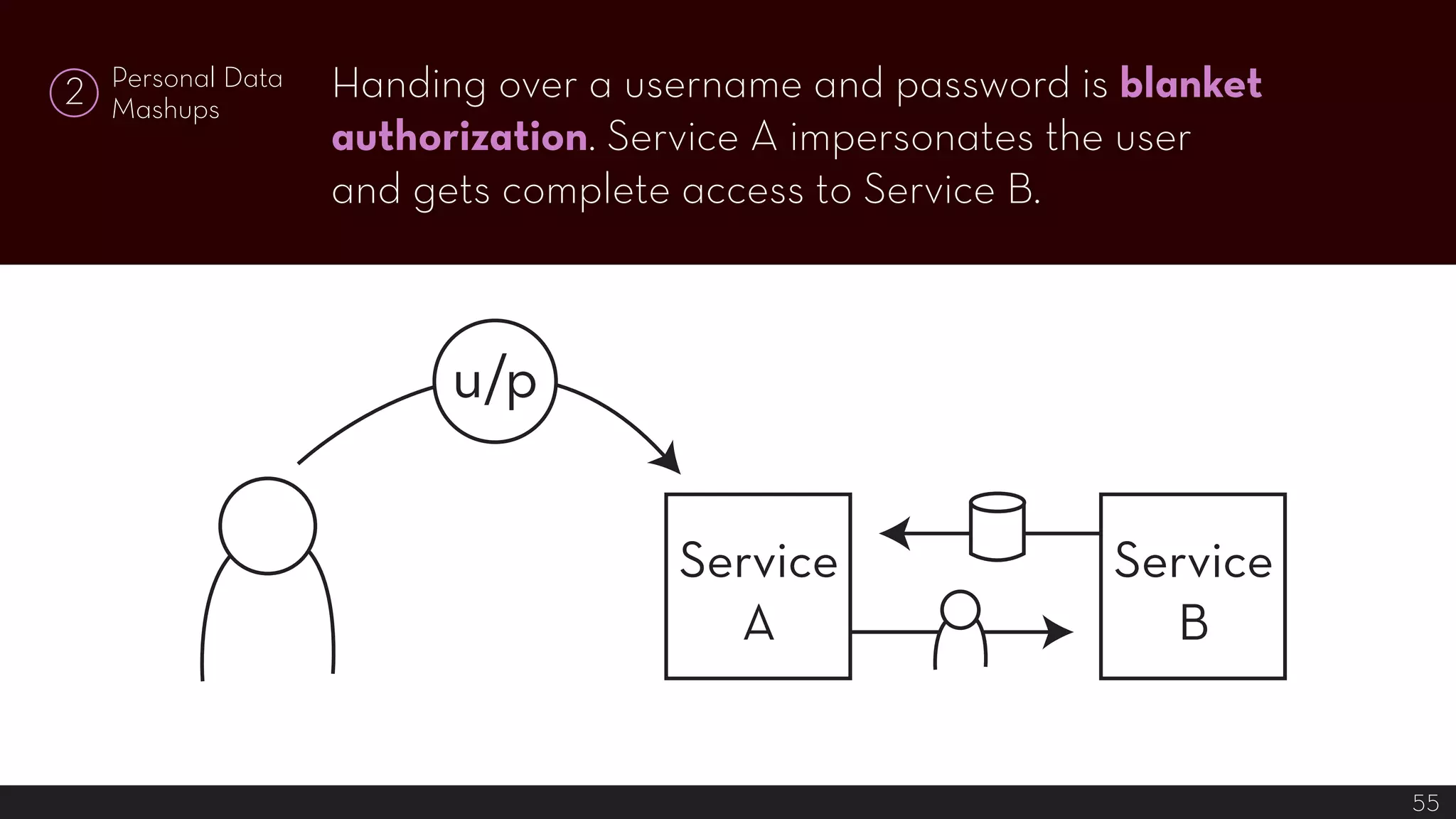
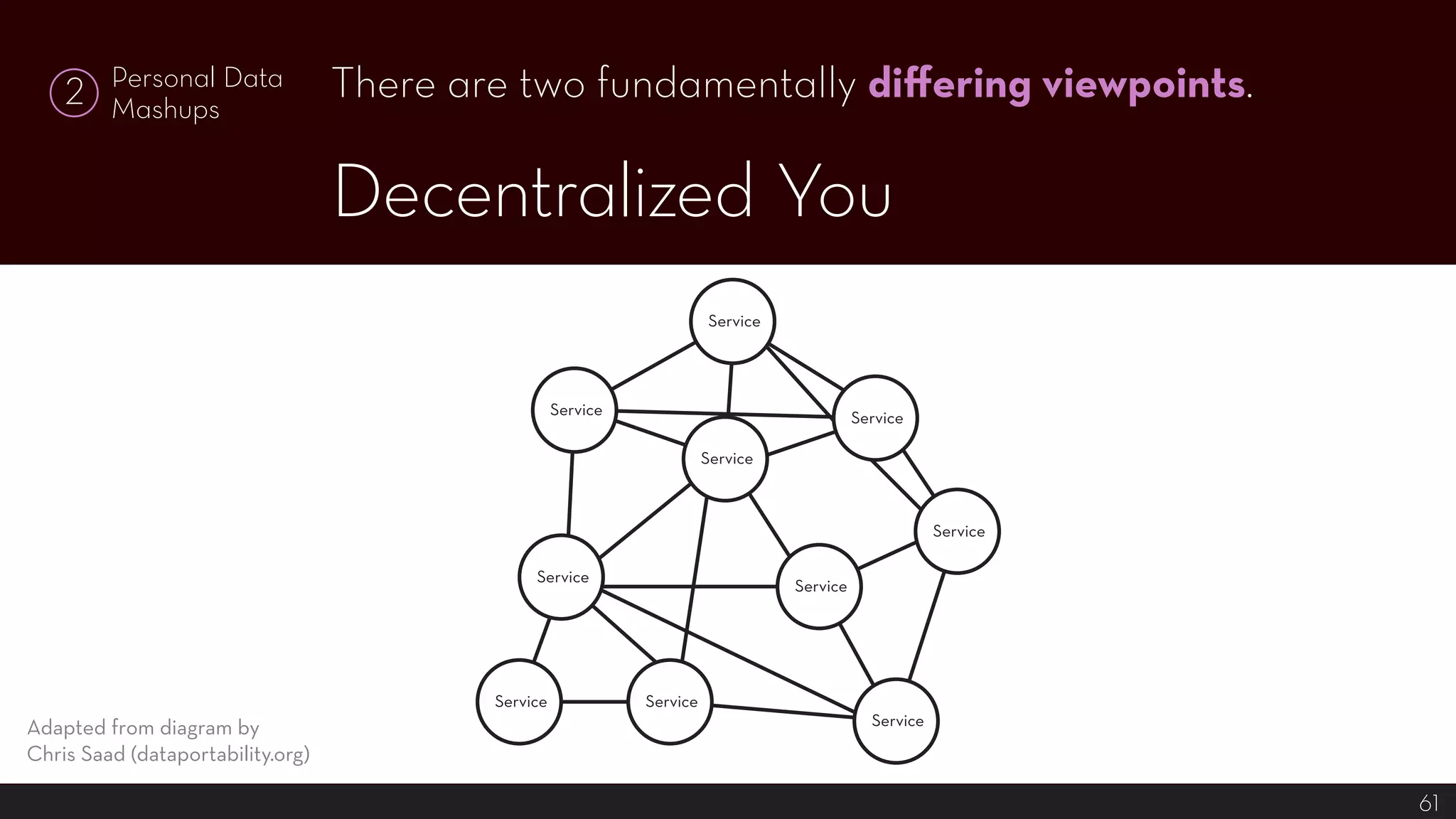
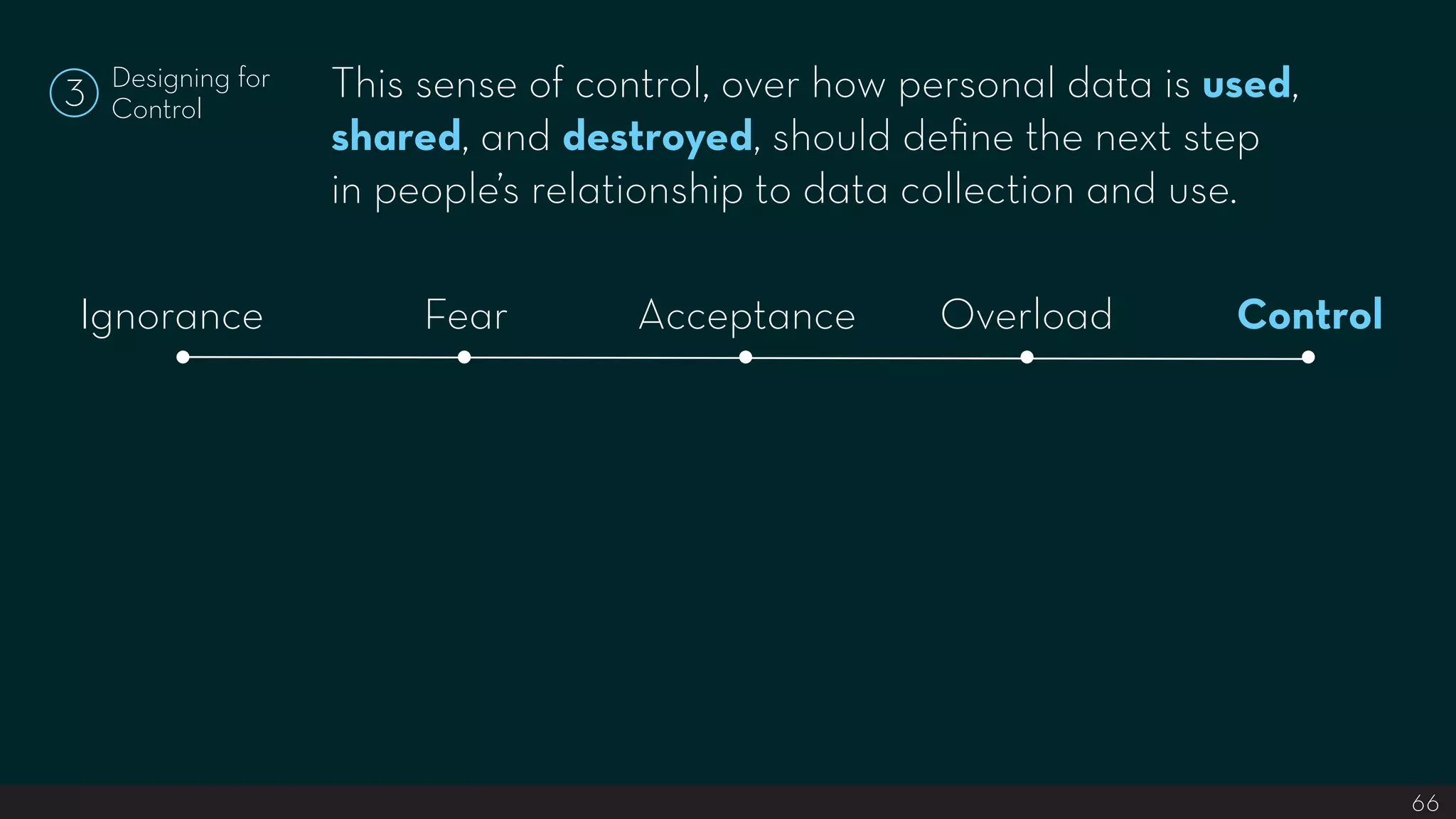
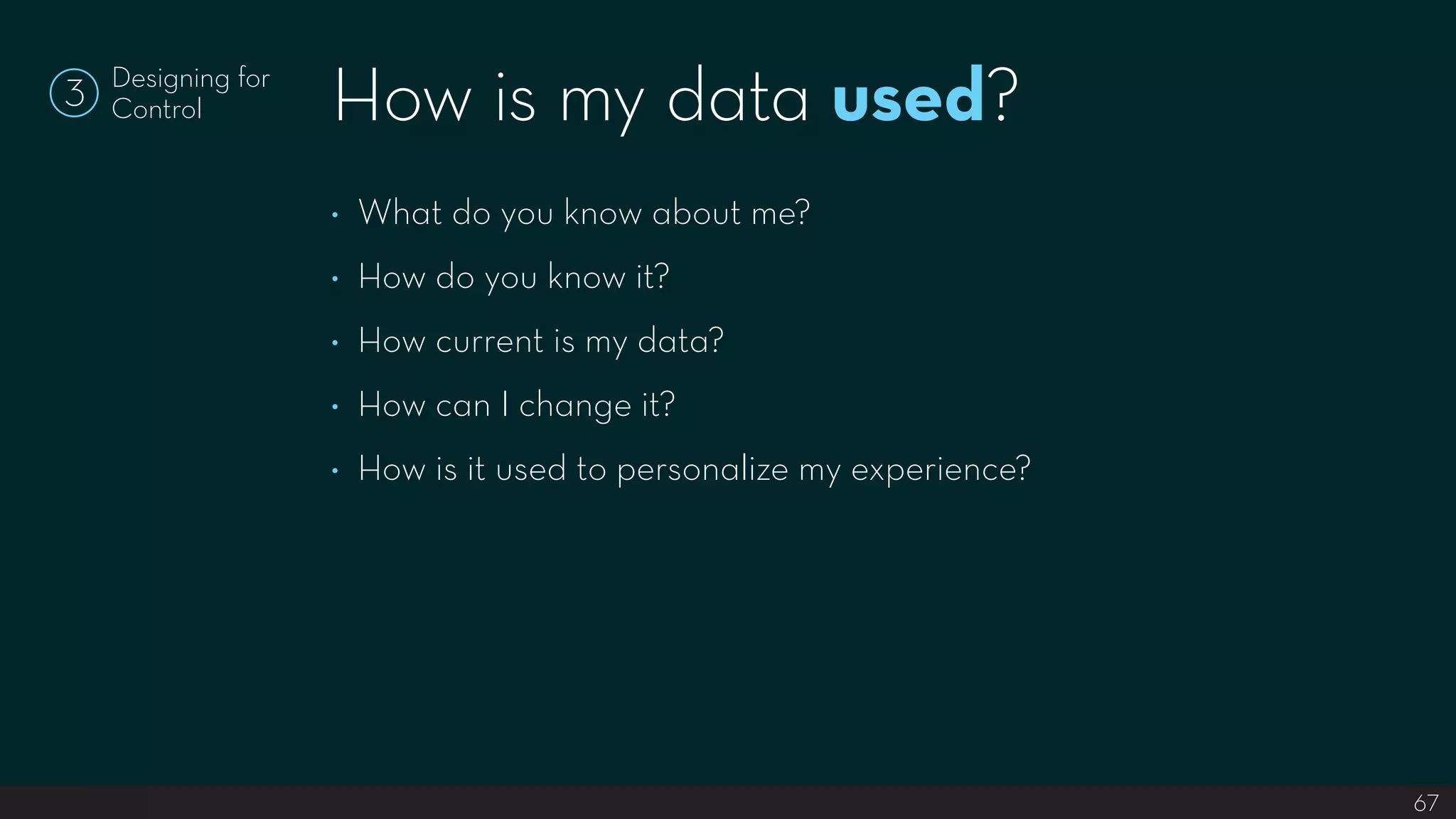
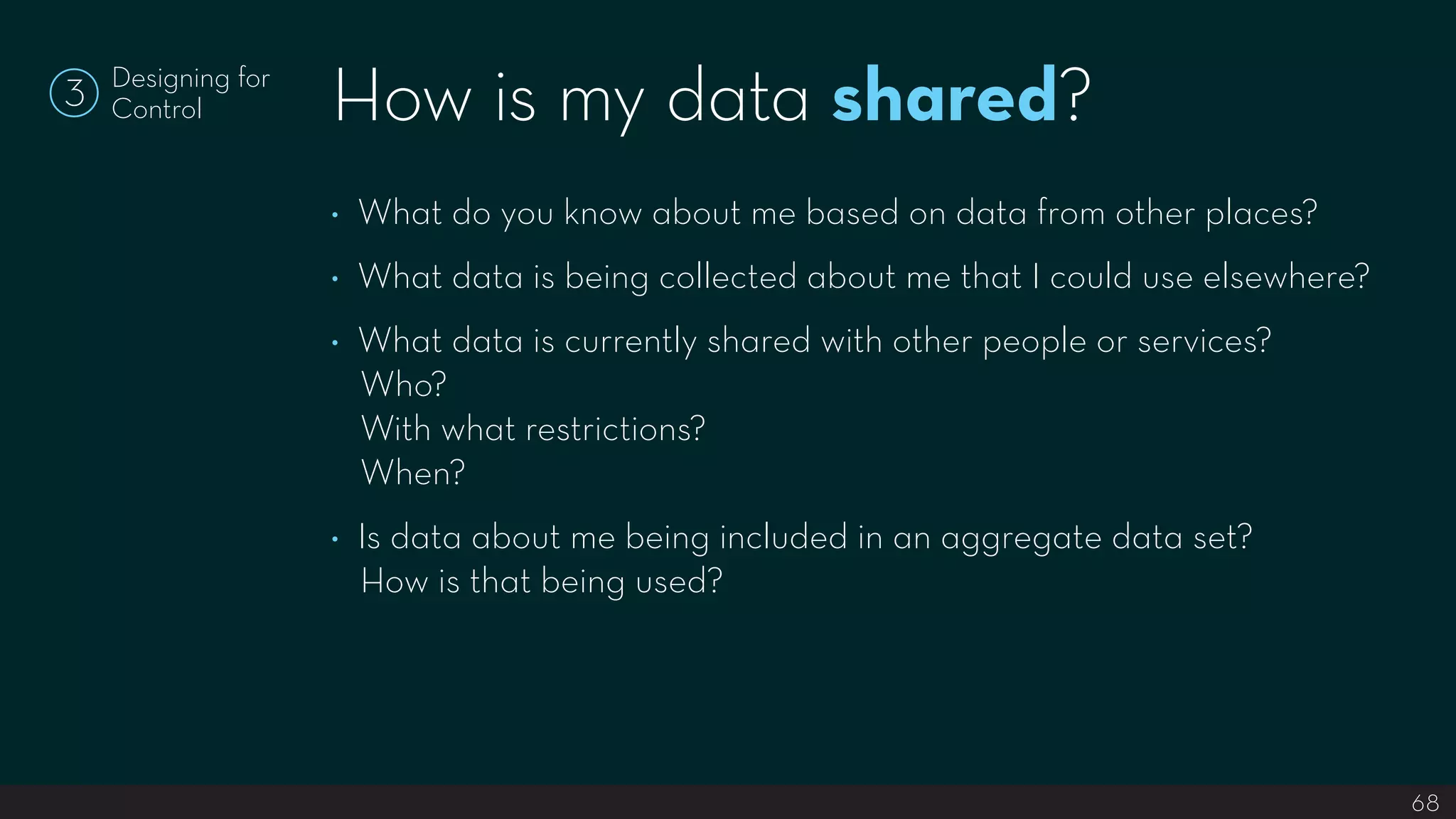
1. The document discusses the rise of tailored interactions, which are personalized experiences based on a person's data and context. As more personal data becomes available online, it enables new possibilities for personalization through "personal data mashups." 2. Technical standards like OpenID and OAuth are emerging that allow for private data to be securely shared, opening opportunities for tailored interactions. However, designers must focus on empowering users with control over their data to avoid privacy and security issues. 3. For tailored interactions to be ethical, users need transparency and control over how their personal data is used, shared, and deleted. The goal should be to allow selective self-revelation rather than total transparency without user consent.