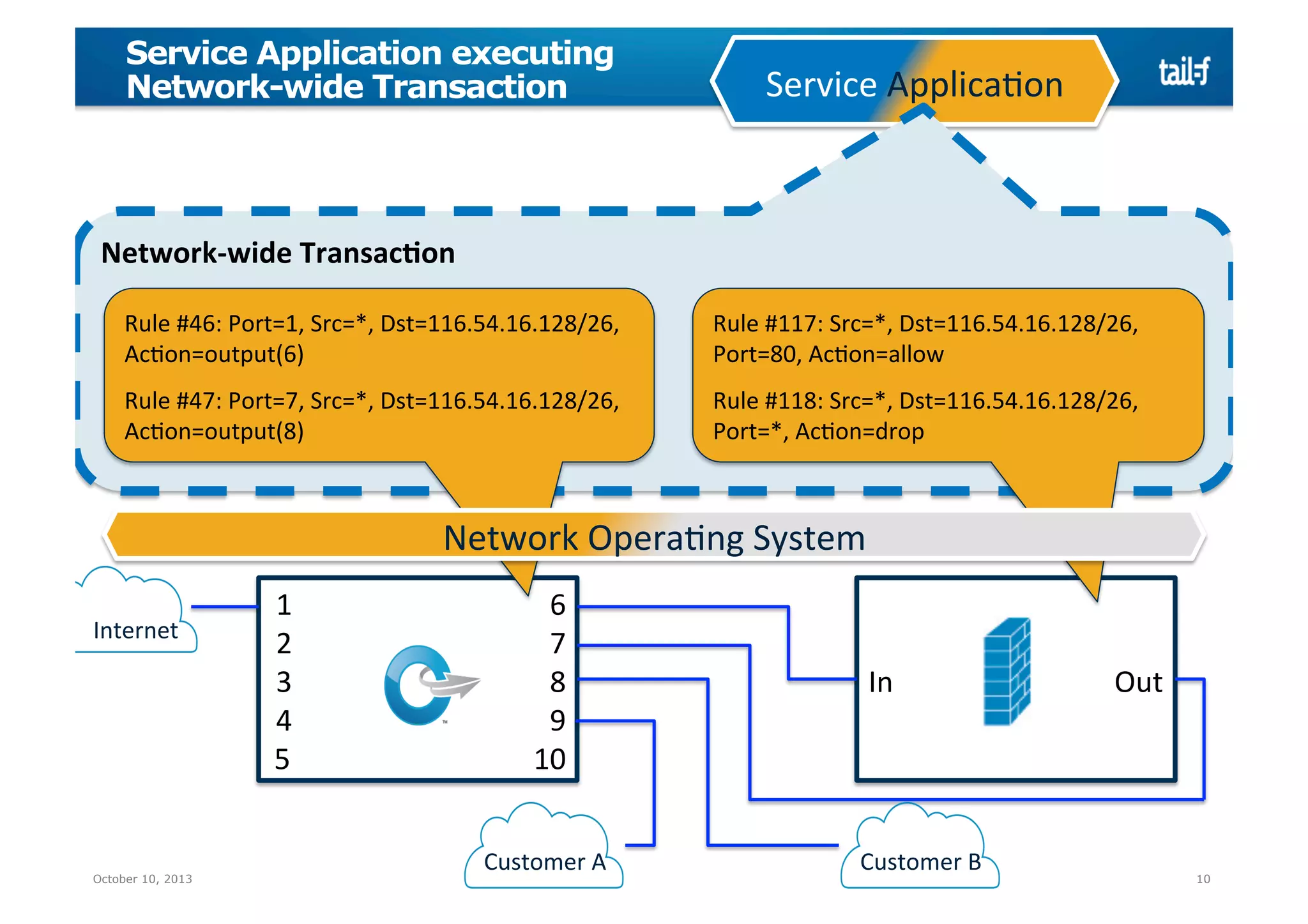
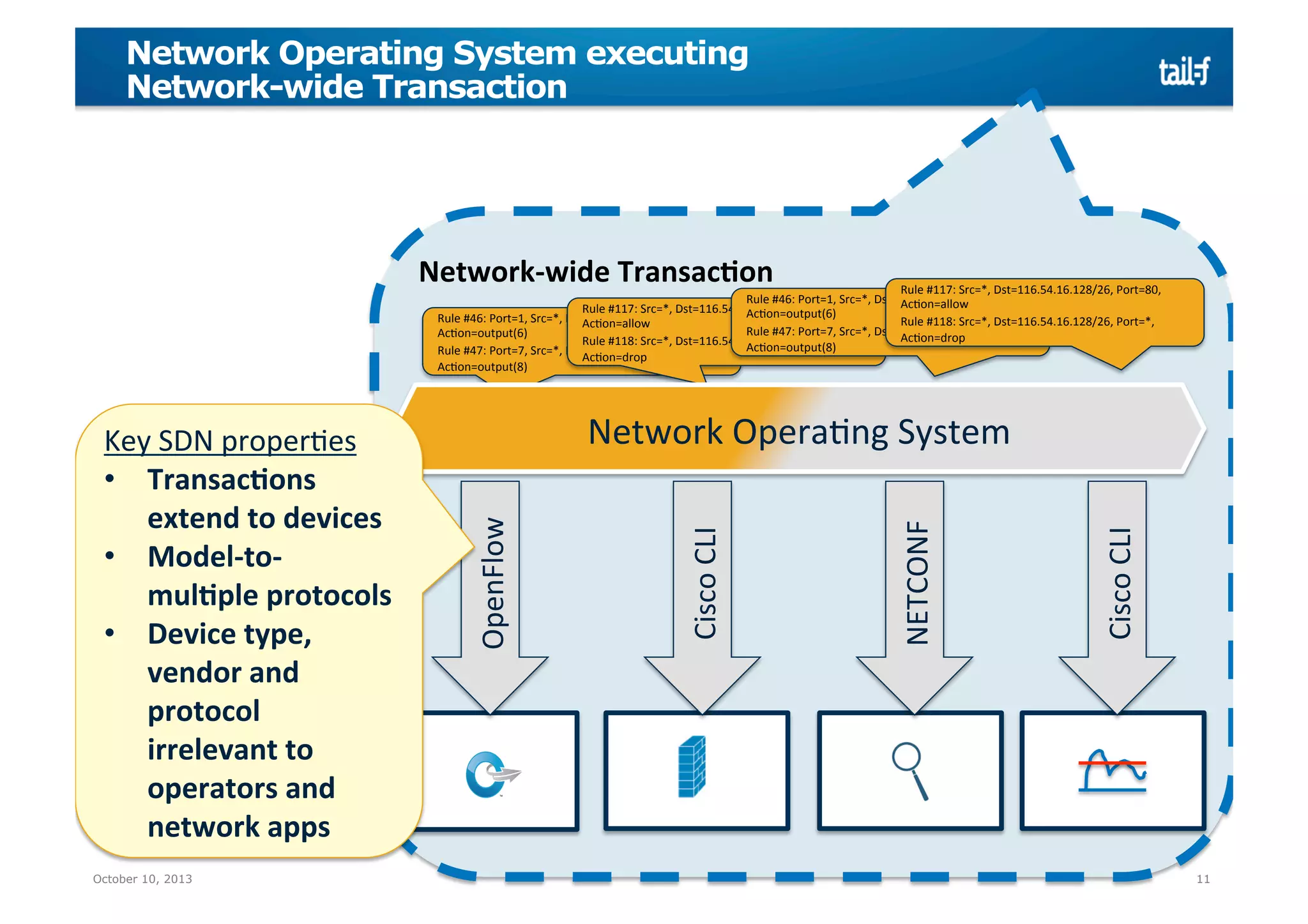
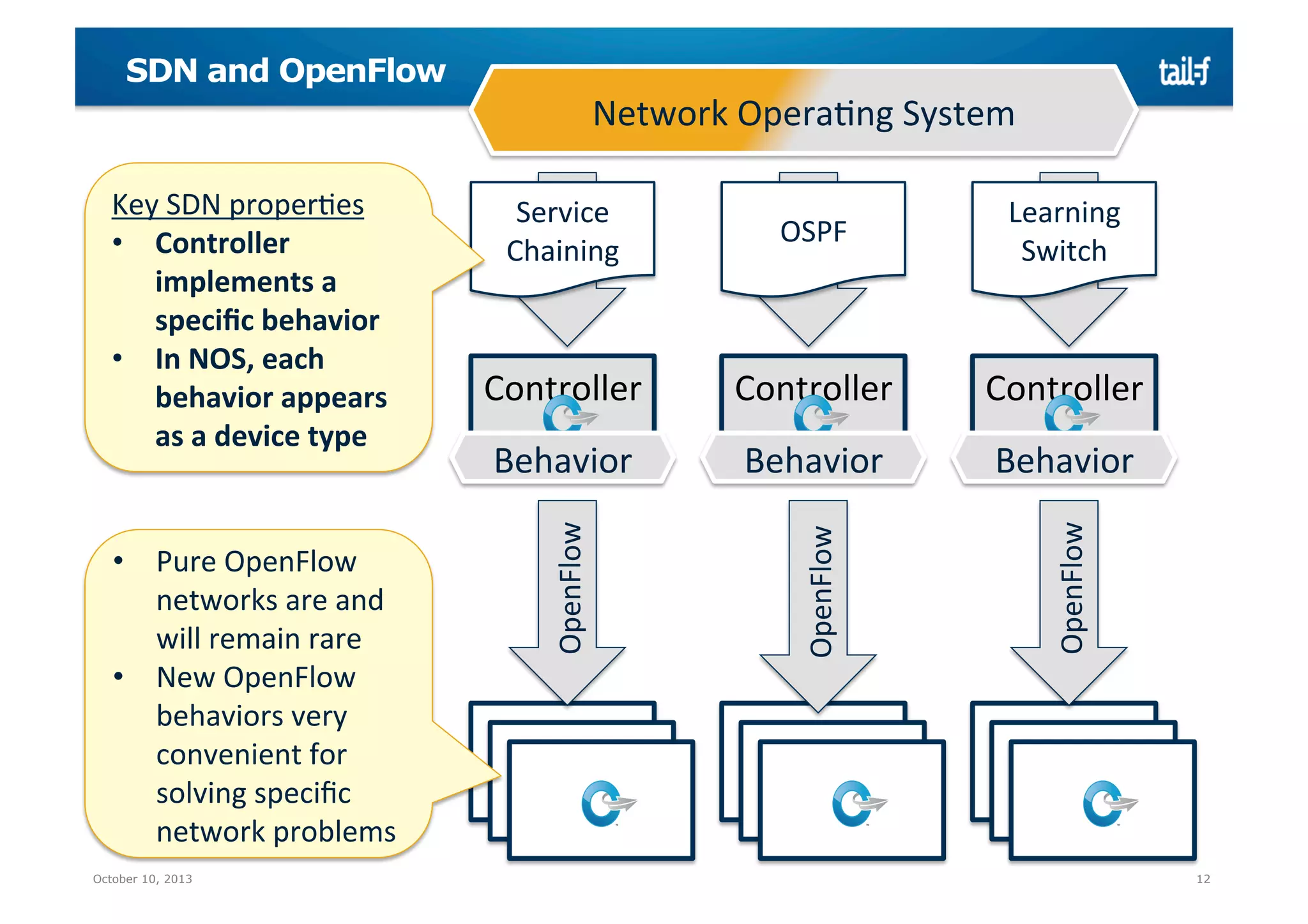
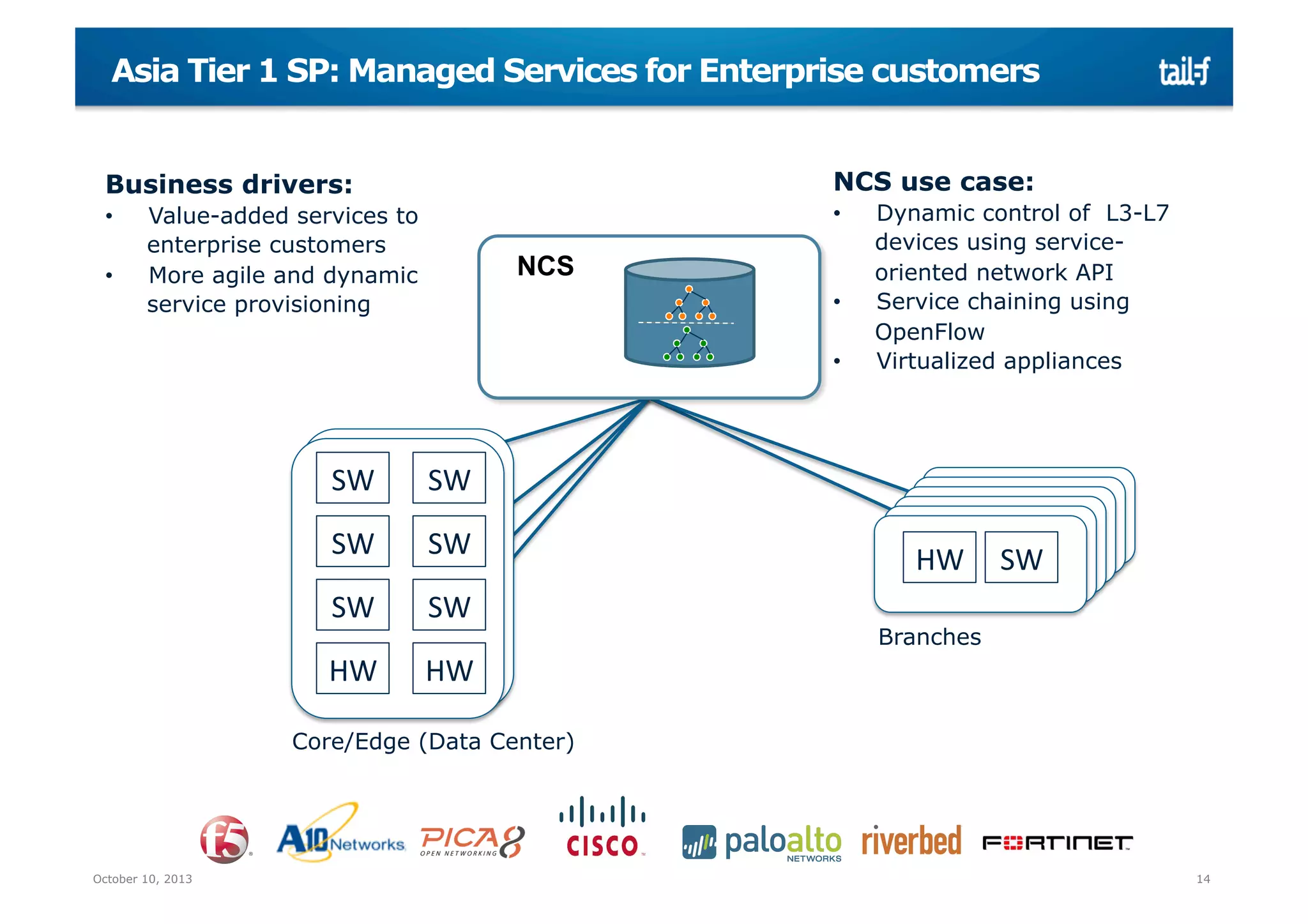
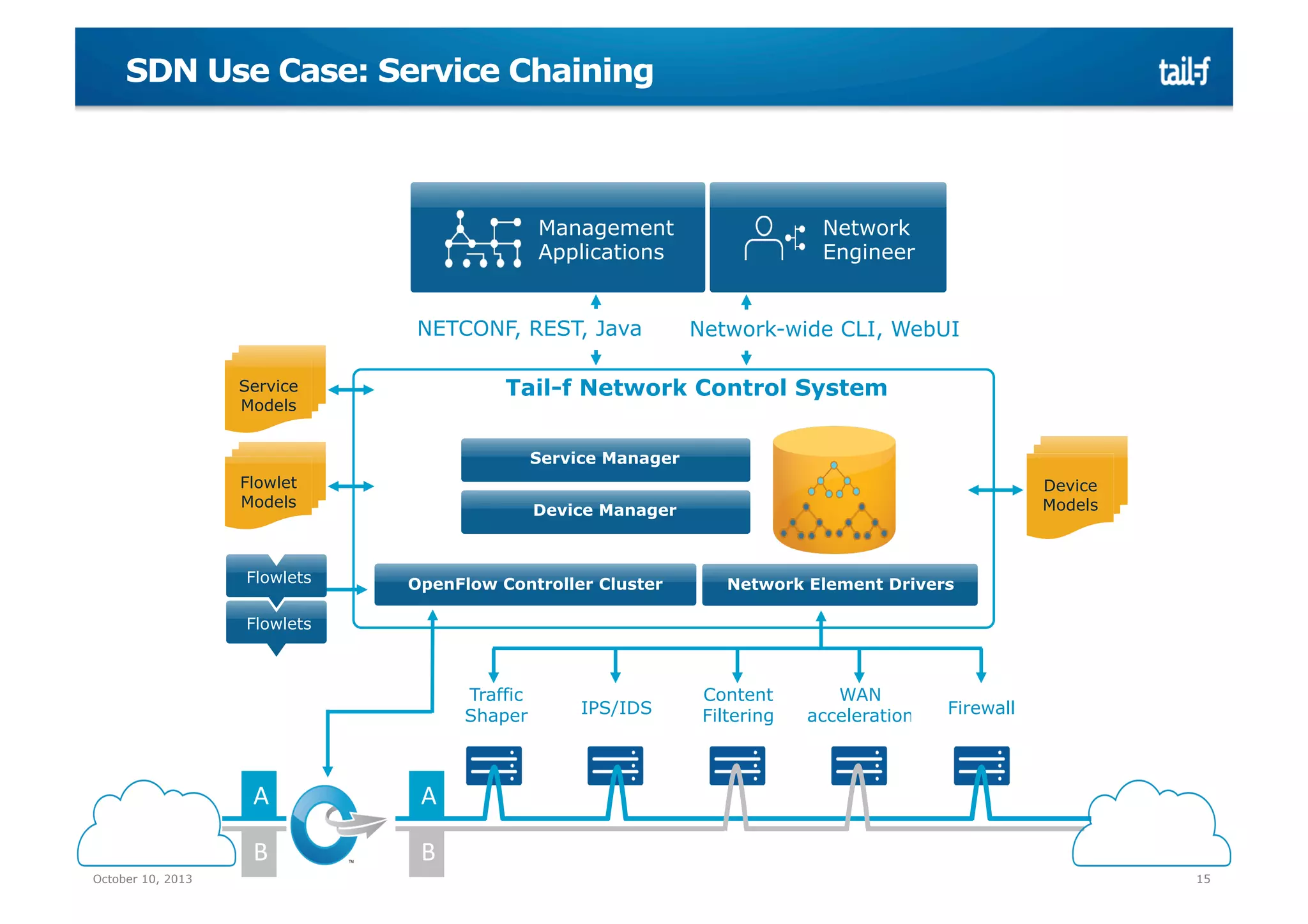
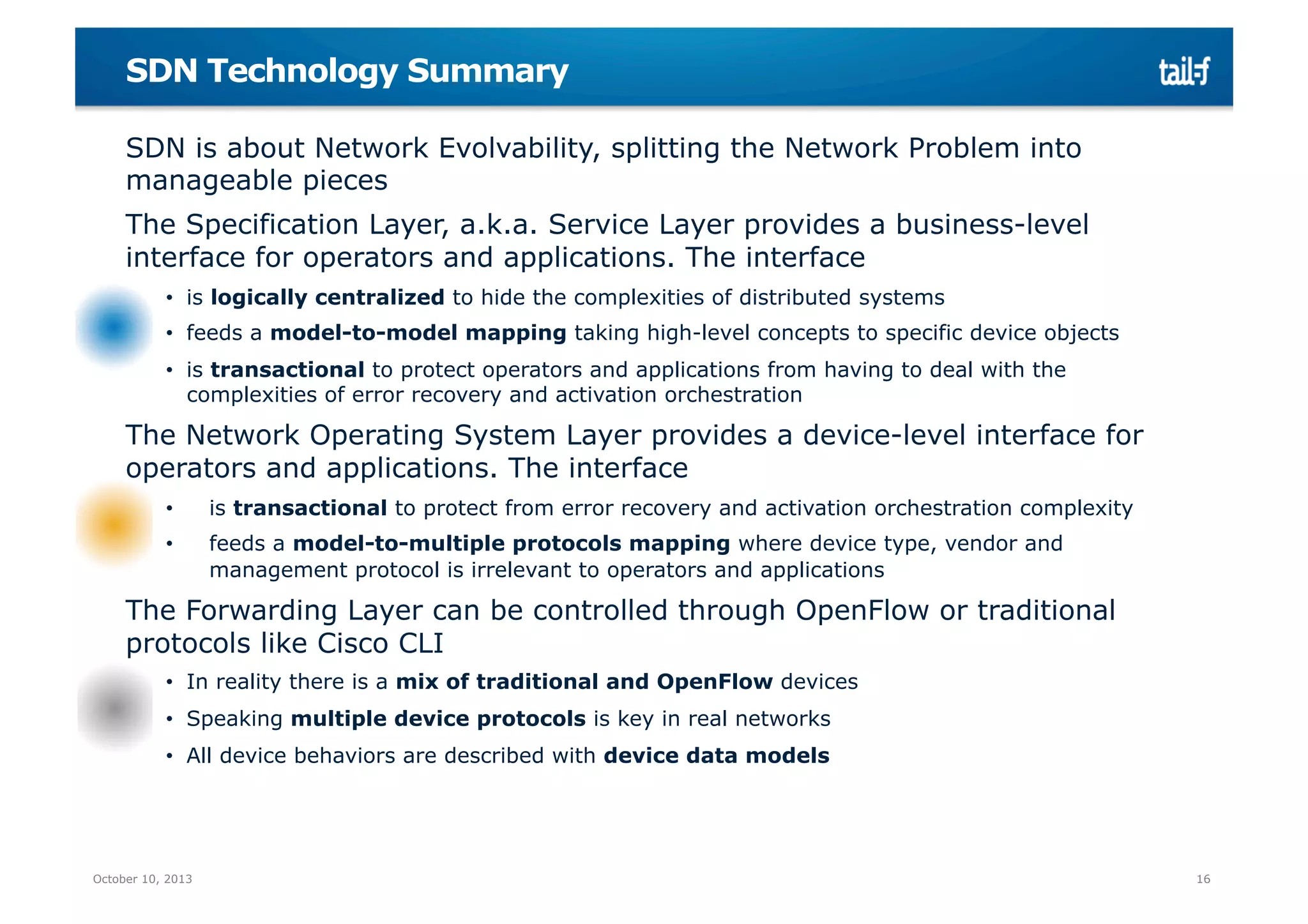
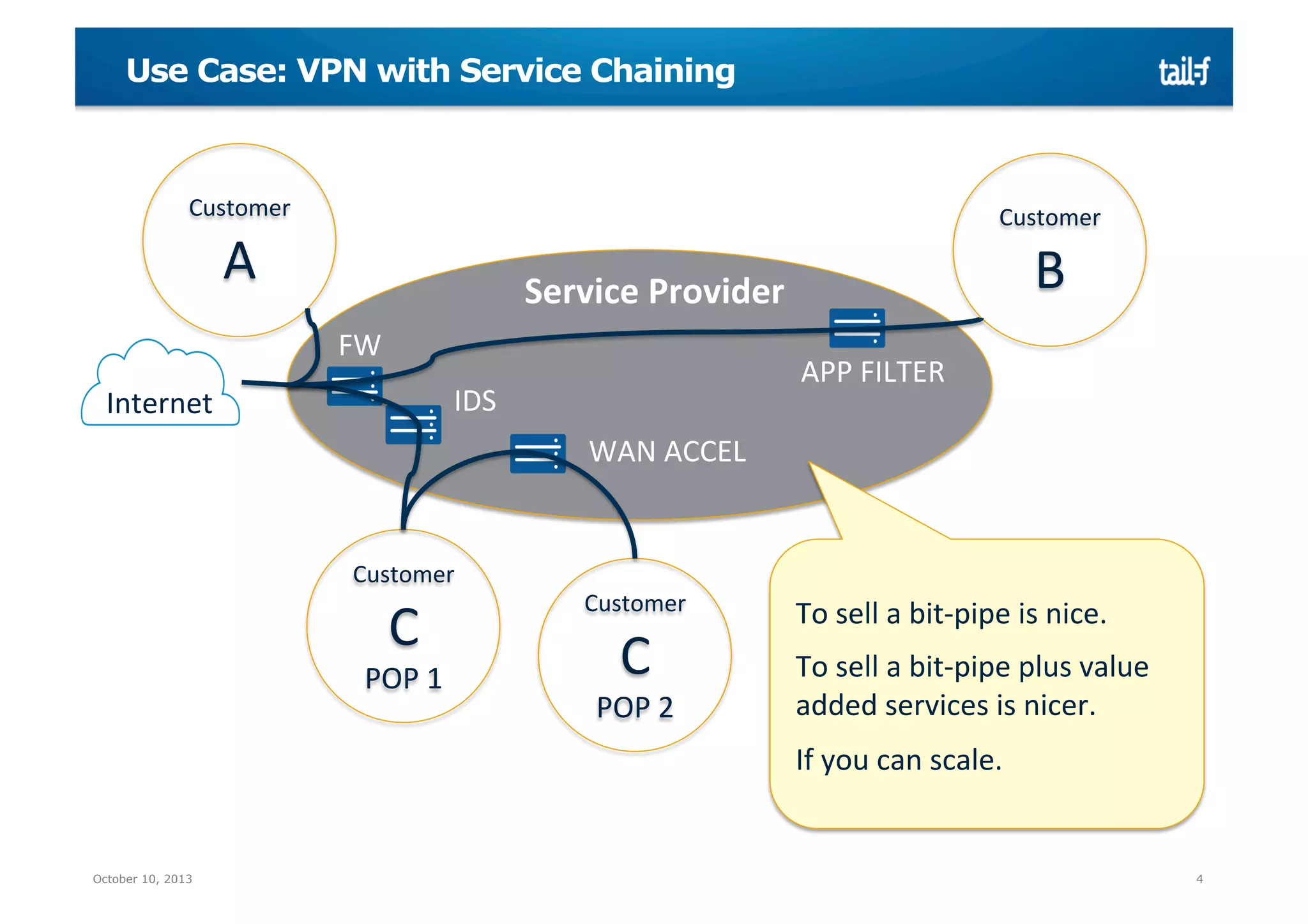
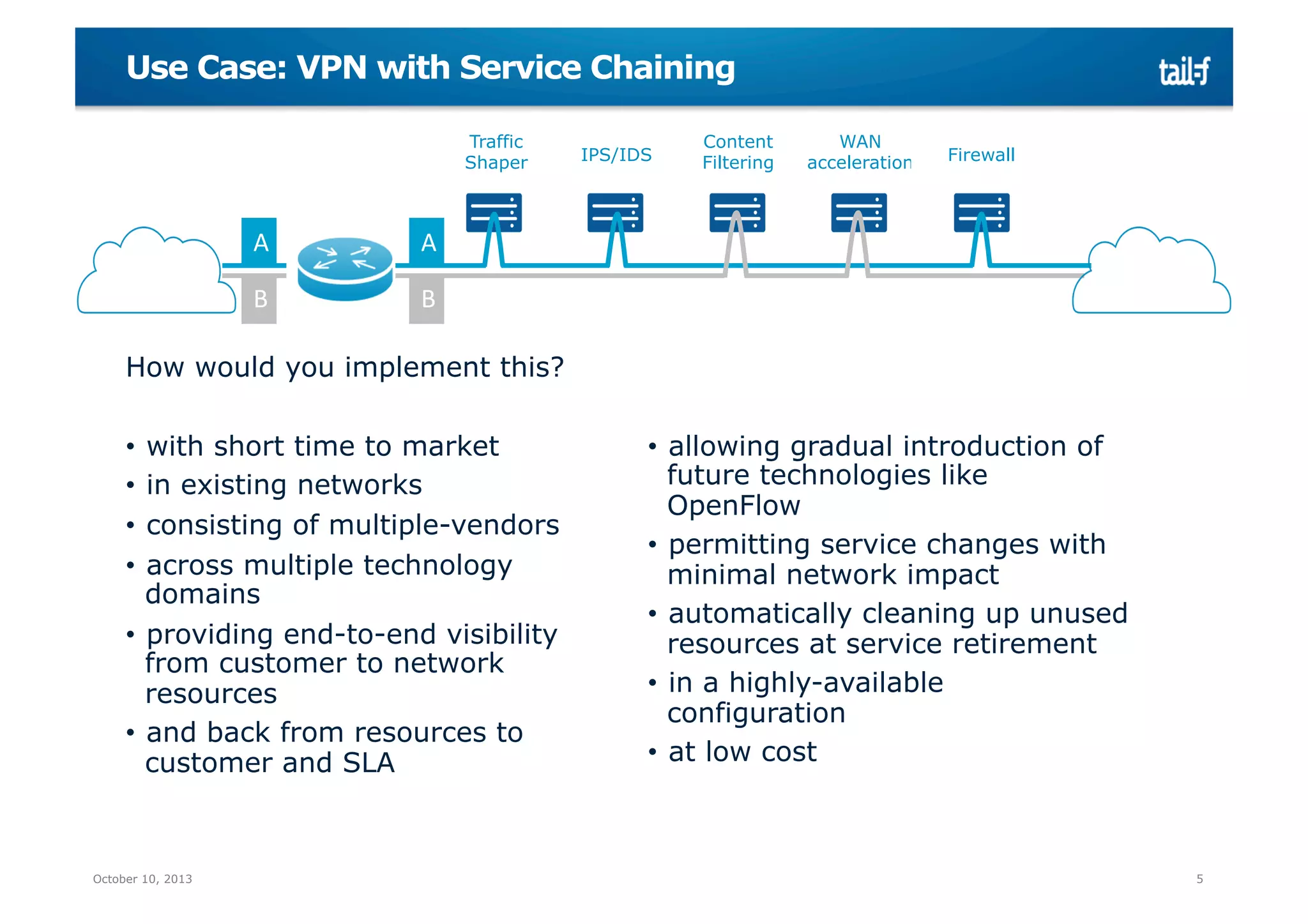
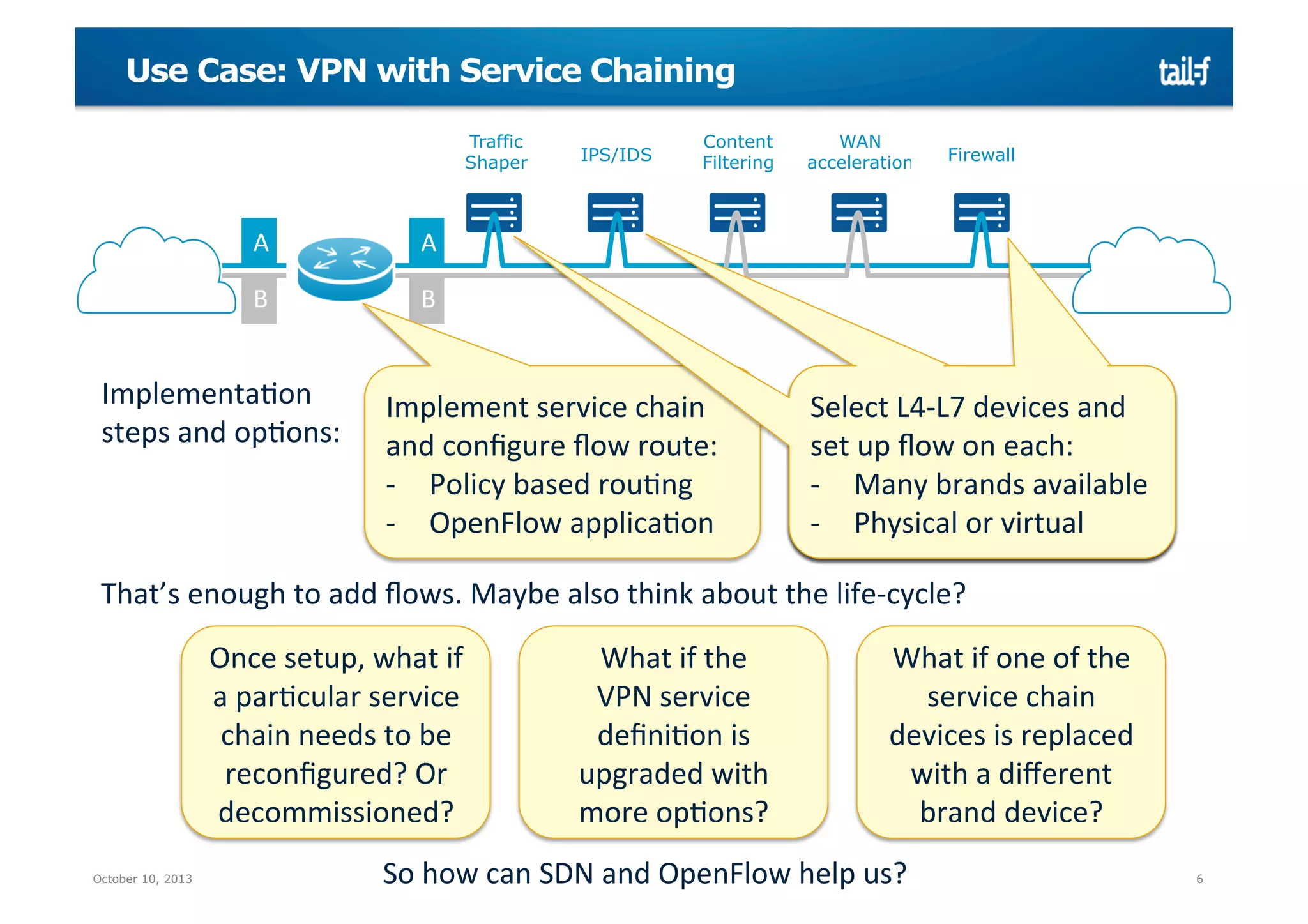
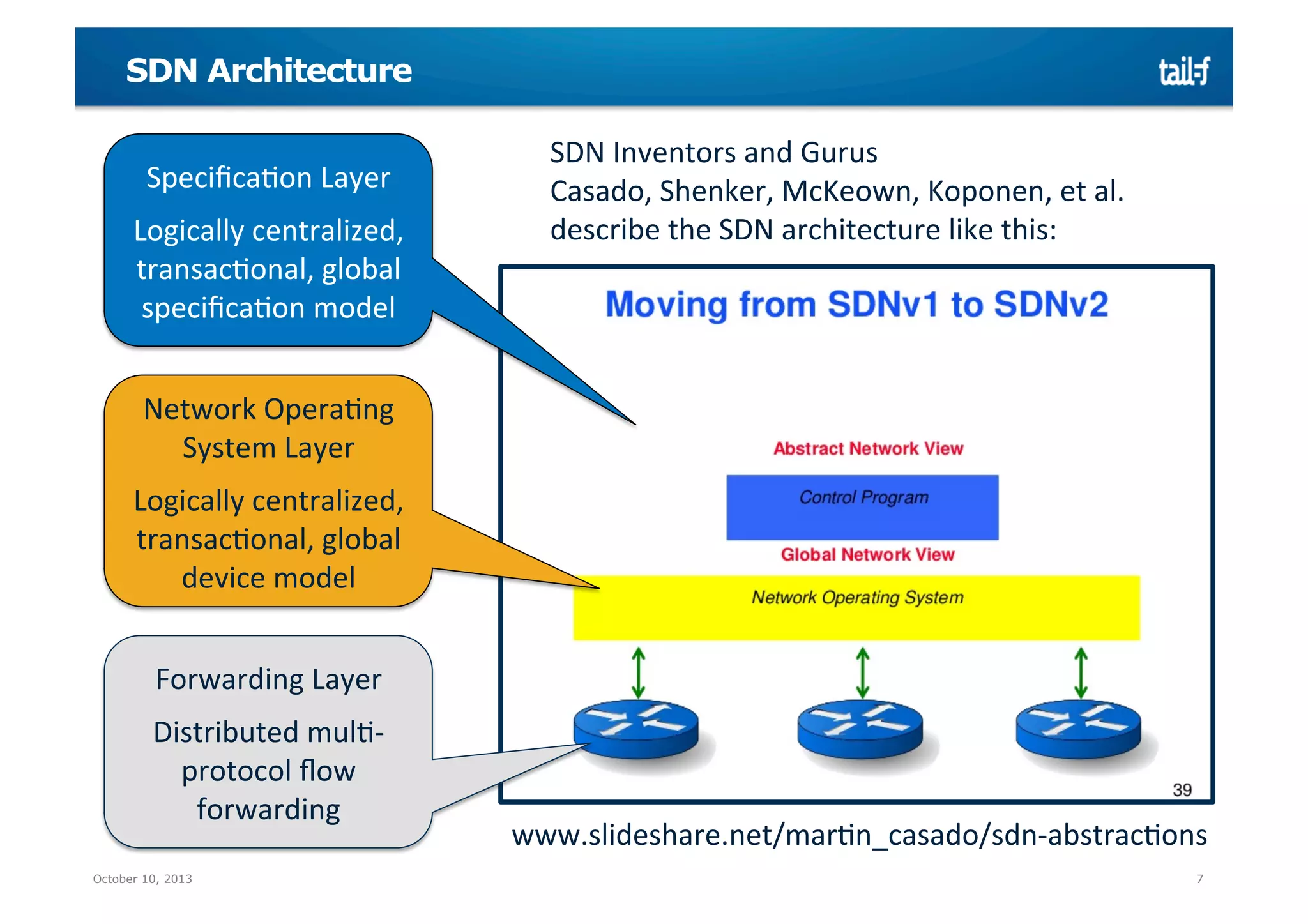
The document discusses dynamic service chaining in SDN and OpenFlow, emphasizing the importance of integrating multiple vendor technologies and enhancing service delivery for networking environments. It highlights the role of Tail-f Systems and its solutions for service providers by enabling agile and scalable service implementations. Additionally, it outlines the benefits of SDN architecture, including centralized management and the ability to handle complex network operations effectively.
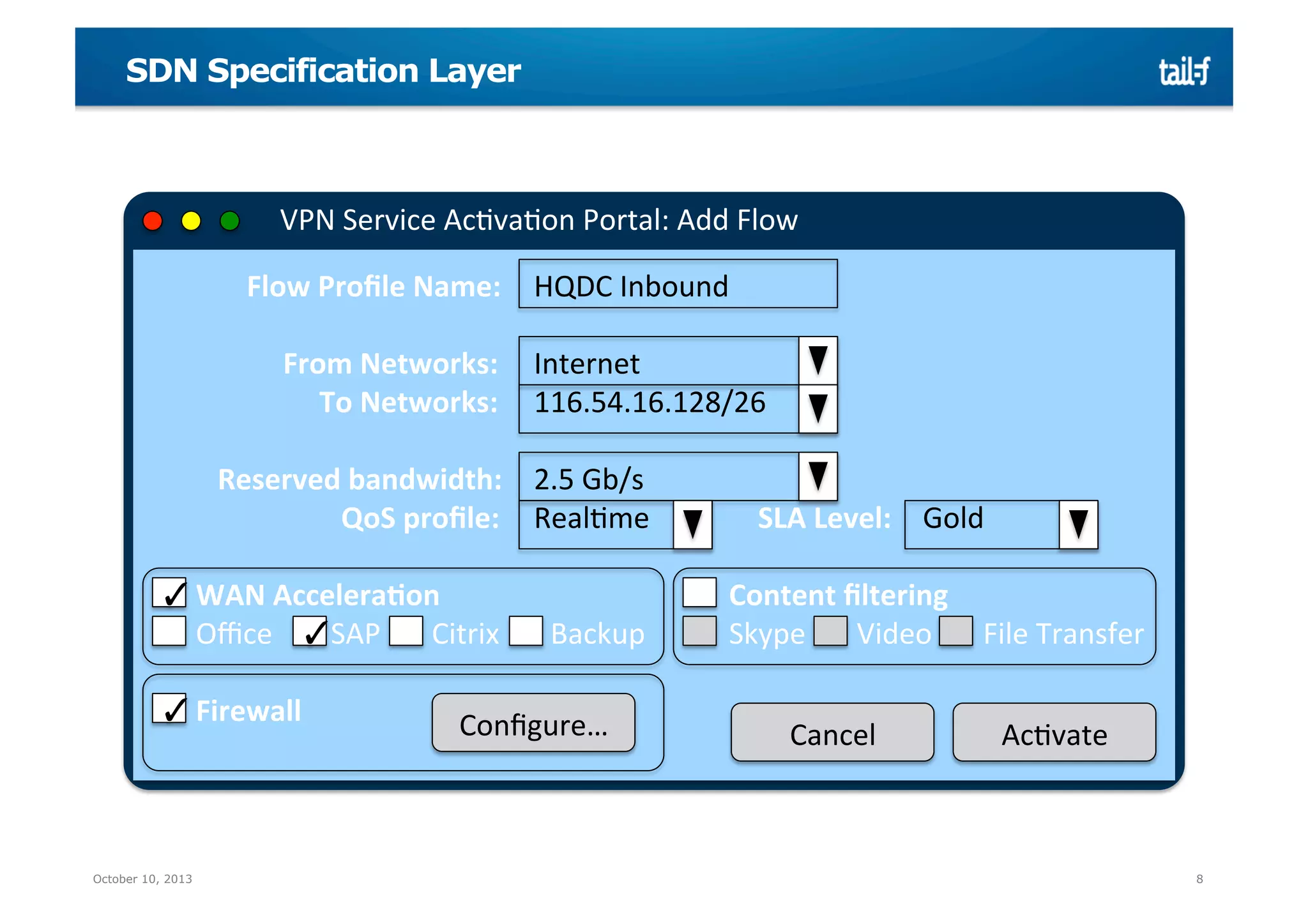
![Service Application: Model-to-model mapper
VPN
Service
Model
Flow
Profile
Name:
unique
string
Key
SDN
ProperMes
• Logically
centralized
APIs
• Model-‐to-‐model
mapping
• Transac@ons
VPN
Service
AcMvaMon
Portal:
Add
Flow
From
Networks:
[
IP-‐address/mask
]
To
Networks:
[
IP-‐address/mask
]
Reserved
bandwidth:
integer
>
0
Service
ApplicaMon
Traffic
Steering
Device
Model
db
Nice
if
APIs,
UIs,
DB
schemas
are
rendered
from
service
model
Firewall
Device
Model
Port:
unique
integer
0..47
Src:
IP-‐address/mask
Dst:
IP-‐address/mask
AcMon:
drop
|
output(N)
|
…
October 10, 2013
Src:
IP-‐address/mask
Dst:
IP-‐address/mask
Port:
integer
1..65535
AcMon:
drop
|
allow
9](https://image.slidesharecdn.com/tail-f-lindblad-dynamicservicechaining-131024073225-phpapp01/75/Dynamic-Service-Chaining-9-2048.jpg)