Syllabus for Cyber security and Ethical Hacking
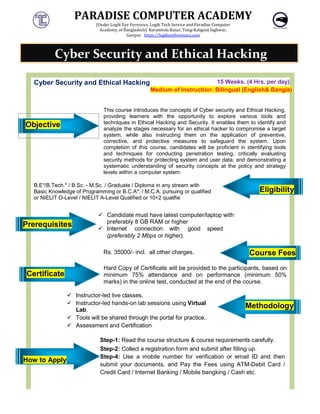
- 1. PARADISE COMPUTER ACADEMY (Under Logik Eye Forensics, Logik Tech Service and Paradise Computer Academy, of Bangladesh) Cyber Security and Ethical Hacking Objective This course introduces the concepts of Cyber security and Ethical Hacking, providing learners with the techniques in Ethical Hacking and Security. It enables them to identify and analyze the stages necessary for an ethical hacker to compromise a target system, while also instructing them on the application of prevent corrective, and protective measures to safeguard the system. Upon completion of this course, candidates will be proficient in identifying tools and techniques for conducting penetration testing, critically evaluating security methods for protecting sy systematic understanding of security concepts at the policy and strategy levels within a computer system B.E*/B.Tech.* / B.Sc. - M.Sc. / Graduate / Diploma in any Basic Knowledge of Programming or B.C.A*. or NIELIT O-Level / NIELIT A-Level Qualified or 10+2 qualifie Prerequisites Candidate preferably 8 Internet (preferably Rs. 3500 Certificate Hard Copy of Certificate will be provided to the participants, based on minimum 75% attendance and on performance (minimum 50% marks) in the online test, conducted at the end of the course. Instructor-led live classes. Instructor-led hands Lab. Tools will be shared through the portal for practice. Assessment and Certification How to Apply Step-1: Read Step-2: Collect a Step-4: Use a submit your Credit Card / Internet Banking / Mobile bangking / Cash Cyber Security and Ethical Hacking PARADISE COMPUTER ACADEMY Logik Eye Forensics, Logik Tech Service and Paradise Computer Bangladesh) Karamtola Bazar, Tong-Kaligonj highwar, Gazipur https://logikeyeforensics.com Cyber Security and Ethical Hacking 15 Weeks. Medium of Instruction: Bilingual This course introduces the concepts of Cyber security and Ethical Hacking, providing learners with the opportunity to explore various tools and techniques in Ethical Hacking and Security. It enables them to identify and analyze the stages necessary for an ethical hacker to compromise a target system, while also instructing them on the application of prevent corrective, and protective measures to safeguard the system. Upon completion of this course, candidates will be proficient in identifying tools and techniques for conducting penetration testing, critically evaluating security methods for protecting system and user data, and demonstrating a systematic understanding of security concepts at the policy and strategy levels within a computer system. M.Sc. / Graduate / Diploma in any stream with B.C.A*. / M.C.A. pursuing or qualified Level Qualified or 10+2 qualifie Candidate must have latest computer/laptop with preferably 8 GB RAM or higher Internet connection with good speed (preferably 2 Mbps or higher). 000/- incl. all other charges. Hard Copy of Certificate will be provided to the participants, based on minimum 75% attendance and on performance (minimum 50% marks) in the online test, conducted at the end of the course. classes. hands-on lab sessions using Virtual Tools will be shared through the portal for practice.. Certification Read the course structure & course requirements Collect a registration form and submit after filling up Use a mobile number for verification or email submit your documents, and Pay the Fees using ATM rd / Internet Banking / Mobile bangking / Cash Cyber Security and Ethical Hacking PARADISE COMPUTER ACADEMY Weeks. (4 Hrs. per day) Bilingual (English& Bangla) This course introduces the concepts of Cyber security and Ethical Hacking, opportunity to explore various tools and techniques in Ethical Hacking and Security. It enables them to identify and analyze the stages necessary for an ethical hacker to compromise a target system, while also instructing them on the application of preventive, corrective, and protective measures to safeguard the system. Upon completion of this course, candidates will be proficient in identifying tools and techniques for conducting penetration testing, critically evaluating stem and user data, and demonstrating a systematic understanding of security concepts at the policy and strategy Eligibility Course Fees Hard Copy of Certificate will be provided to the participants, based on minimum 75% attendance and on performance (minimum 50% marks) in the online test, conducted at the end of the course. Methodology requirements carefully. submit after filling up. email ID and then using ATM-Debit Card / rd / Internet Banking / Mobile bangking / Cash etc. Cyber Security and Ethical Hacking
- 2. PARADISE COMPUTER ACADEMY (Under Logik Eye Forensics, Logik Tech Service and Paradise Computer Academy, of Bangladesh) Day Topic Day Day #01 Introduction to Hacking and security Day #02 Day #04 Digital Systems hacking Day #05 Day #07 Smartphone hacking Day #08 Day #10 WiFi network hacking Day #11 Day #13 Aircraft System hacking Day #14 Day #16 Setup Lab and introduction with Linux Day #17 Day #19 Malware attacks analysis Day #20 Day #22 Man-in-the middle attack Day #23 Day #25 Cyber Crime & Law Day #26 Course Mehedi Hasan Founder Owner LOGIK EYE FORENSICS, PARADISE COMPUTER ACADEMY, LOGIK TECH SERVICE Email: mehedi0001@yahoo.com Mobile Number: +8801766442199 CLICK PARADISE COMPUTER ACADEMY Logik Eye Forensics, Logik Tech Service and Paradise Computer Bangladesh) Karamtola Bazar, Tong-Kaligonj highwar, Gazipur https://logikeyeforensics.com Course Content Topic Day Information & Network Reconnaissance Day #03 IP and Network Scanning Web Applications hacking Day #06 Social Engineering Satellite data signal hacking Day #09 Deep-Fake technology Radio frequency hacking Day #12 GSM Network hacking Signal jamming Day #15 Cloud system hacking Crypto-currency and Cryptography Day #18 Vulnerability assessment and Analysis Phishing attack Day #21 Smart Card Hacking Concepts of Digital Forensics Day #24 Hacking Exploit development with python Project and Paper writing Course Coordinator Founder Owner, LOGIK EYE FORENSICS, PARADISE COMPUTER LOGIK TECH SERVICE mehedi0001@yahoo.com Number: +8801601019511, +8801766442199 CLICK HERE TO REGISTER PARADISE COMPUTER ACADEMY Topic IP and Network Scanning Social Engineering Fake technology GSM Network hacking Cloud system hacking Vulnerability assessment and Analysis Smart Card Hacking Hacking Exploit development with python
- 3. PARADISE COMPUTER ACADEMY (Under Logik Eye Forensics, Logik Tech Service and Paradise Computer Academy, of Bangladesh) Karamtola Bazar, Tong-Kaligonj highwar, Gazipur https://logikeyeforensics.com Course Syllabus Day Detailed Conceptual Topic Hands On lab Day1 Introduction to Hacking and security Understanding Ethical Hacking Hacking vs. Ethical Hacking VPN and IP changer Location changer MAC/IMEI Changer Virtual Machine setup OS Setup on VMware Machine Dark Web with Tor browser Ensure security and be confirm you are an anonymous user IP Address Scanning Find real IP Study of ethical hacking, Information security, IP Address, virtual machine, MAC/IMEI. Practice on VPN installation, IP address changing, MAC changer, virtual machine setup, Install tor browser, access in dark wave. Day2 Information & Network Reconnaissance Introduction to Information Gathering, Phases of I.G Information Gathering Techniques Foot printing Steps of hacking Popular hacking tools IP hacking with link IP hacking with Email Practice on information gathering; install hacking tools, creating a https link to capture remote locations IP address. Creating an account to get someone’s IP address by email sending. Day3 IP and Network Scanning Scanning Tools and Techniques Concept of Email Spoofing, E-mail Security Port Scanning and Service Enumeration IP Tracking System Remote IP hacking technique IP Address Analysis Hands-on lab on Information Gathering and its countermeasures. Day4 Digital Systems hacking Exploiting System Vulnerabilities Introduction to Virus/Trojan/Spyware/Keylogger Windows OS hacking Password Cracking types Brute Force Attacks IoT Hacking tools ( With Raspberry pi ) IoT system hacking Hands-on lab on vulnerability assessment with kali linux, windows system hacking with keylogger.
- 4. PARADISE COMPUTER ACADEMY (Under Logik Eye Forensics, Logik Tech Service and Paradise Computer Academy, of Bangladesh) Karamtola Bazar, Tong-Kaligonj highwar, Gazipur https://logikeyeforensics.com Day5 Web Applications hacking Common Web Application Vulnerabilities, Denial of Service (DoS), SQL Injection, XSS, CSRF, and more Web Application Scanners Email Hacking Email Header collection, Email header analysis Password Cracking Brute Force Attack in Web Application Hands on Lab on Trojan Virus & its Countermeasures, email hacking, email header collection, header analysis, Day6 Social Engineering Psychology of Social Engineering Phishing with java script, SET and Web Stereography Information Hiding Stego Analysis SMS and Call spoofing Social Engineering Countermeasures Hands on lab on Steganography, SMSspoofing, Callspoofing, Day7 Smartphone hacking Mobile Device Security Android and iOS Exploits APK exploit Termux and basic application Android Device hacking Android Spy Android Exploit Hands on lab on Android spy, Operation ou Termux, android device hacking and countermeasures Day8 Satellite data signal hacking Satellite Communication Overview Introduction with NOAA, ROSMOSCOS and others satellite Intercepting and Decoding Weather Satellite Signals Introducing with GNU Radio Capturing and decoding satellite signals Security Implications Hands on lab on satellite data receiving and decoding, GNU Radio setup, find a target satellite and capture signal. Day9 Deep-Fake technology Understanding Deep-Fakes Technology Making Deep-Fakes video or image Creating Deep-fake movie with python script Deep-face detection and Action Hands on lab on Deep- fake, Creating Deep- fake video and image.
- 5. PARADISE COMPUTER ACADEMY (Under Logik Eye Forensics, Logik Tech Service and Paradise Computer Academy, of Bangladesh) Karamtola Bazar, Tong-Kaligonj highwar, Gazipur https://logikeyeforensics.com Day10 WiFi network hacking Wireless Network Security WEP, WPA, and WPA2 Cracking WiFi hacking with Kali Linux Hands on lab wifi hacking Day11 Radio frequency hacking Basic Concept RF Communication Intercepting RF Signals Software define radio setup Receive and Decrypt different types of RF signals. RF Security Measures Basic operation of Antenna Basic concept of Wireshartk Hands on lab on radio signal receiving tools install, recording and decoding, Day12 GSM Network hacking GSM Architecture and Vulnerabilities Intercepting BTS Traffic Mobile Network Security Detect Fake BTS open BTS etc. Basic concept of 2G Interceptor Capturing SMS and 1G GSM Data with Wireshark Hands on lab on sniffing bts, base station, collect IMSI number, LAC, CELL ID, Find fake BTS, SMS capturing system with wireshark and its Countermeasures. Day13 Aircraft LD System hacking Introduction with Aircraft Landing System ADS-B signal decoding ADS-B Airplane Tracking Basic concept of Global Civil Aviation System Case Studies and Mitigation Hands on lab on ADS- B setup, Civil aviation tracking, Source and target Location tracking, Day14 Signal jamming Jamming Techniques and Equipment FM signal jamming (short range) WiFi Jamming (short range) MW signal jamming (short range) GSM signal jamming (short range) Jamming Detection and Prevention Hands on lab on FM, WiFi, MW, GSM jamming and its Countermeasures. Day15 Cloud system hacking Cloud Security Models Google Drive Hands-on lab on cloud based systems information capturing. Day16 Setup Lab and introduction with Linux Lab Environment Setup Introduction to Kali Linux, Arch Linux, Ubuntu etc. Hands-on lab on Installing and configuring
- 6. PARADISE COMPUTER ACADEMY (Under Logik Eye Forensics, Logik Tech Service and Paradise Computer Academy, of Bangladesh) Karamtola Bazar, Tong-Kaligonj highwar, Gazipur https://logikeyeforensics.com Day17 Crypto-currency and Cryptography Crypto currency Fundamentals Cryptographic Techniques Hands-on lab on crypt currency account opening. Day18 Vulnerability assessment and Analysis Introduction with Assessment Web based Vulnerability Assessment System based Vulnerability Assessment Metasploit framework Nessus Professional Nicto, OpenVAS Introducing with Acunetix web vulnerability scanner Hands-on lab on Penetration Testing using Metasploit Day19 Malware attacks analysis Malware Types and Analysis Basic of Static and Dynamic Analysis Malware Defense Strategies Hands-on lab malware analysis Day20 Phishing attack Phishing Techniques Phishing with Metasploit and SET Phishing and Vesting Email and Website Spoofing Anti-Phishing Measures Hands-on lab on SET, Gmail phishing, facebook fishing, phishing with java script. Day21 Smart Card Hacking RFID Hacking Basic concept of microchip Credit card cloning NID cloning Hands-on lab microcio hex file extraction, Credit card number generating, NID and RFID cloning technique. Day22 Man-in-the middle attack MITM Concepts and Techniques ARP Poisoning and SSL Stripping MITM Detection and Prevention GSM Sniffing RF Poisoning IMSI Catcher LTE Interceptor Hands-on lab on GSM sniffing Day23 Concepts of Digital Forensics Digital Forensics Fundamentals Evidence Handling and Preservation USB Forensics Windows Forensics Gmail Forensics Hands-on lab on windows forensics, USB forensics, imaging, etc.
- 7. PARADISE COMPUTER ACADEMY (Under Logik Eye Forensics, Logik Tech Service and Paradise Computer Academy, of Bangladesh) Karamtola Bazar, Tong-Kaligonj highwar, Gazipur https://logikeyeforensics.com Digital Forensic Tools Digital Forensics Report Lost Data Recovery Partition Recovery Day24 Hacking Exploit development with python Python for Hacking Exploit Development Basics Modifying Custom Exploits Hands-on lab on exploit development Day25 Cyber Crime & Law Cybercrime Laws and Regulations Legal and Ethical Aspects of Hacking Ethical Hacking Codes of Conduct Open discussion Day26 Penetration testing using Metasploit Framework Introduction to Penetration Testing, Penetration testing methodology and types, Popular penetration testing tools Hands-on lab on penetration testing with metasploit framework. Assessment Final Project Presentation Research Paper Writing Quizzes and Assignments Hands-On Labs and Projects Final Exam Research Paper Prerequisites: Basic understanding of computer networking and operating systems. Note: Ethical hacking should always be conducted within legal and ethical boundaries. The course will emphasize responsible and legal hacking practices.
- 8. PARADISE COMPUTER ACADEMY (Under Logik Eye Forensics, Logik Tech Service and Paradise Computer Academy, of Bangladesh) Karamtola Bazar, Tong-Kaligonj highwar, Gazipur https://logikeyeforensics.com Appendix Few International Hacking Certifications include CEH GIAC OSCP CREST Useful Websites to Learn Ethical Hacking Hack this Site Link: https://www.hackthissite.org Hack a day Link : https://hackaday.com Hacker 101 Link : https://www.hacker101.com EC-Council Link : https://www.eccouncil.org Cybrary Link : https://www.cybrary.it Hack This Site Link: https://www.hackthissite.org Hacking Tutorial Link http://www.hacking-tutorial.com Break the security Link: https://breakthesecurity.cysecurity.org THE END
