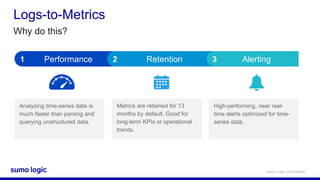
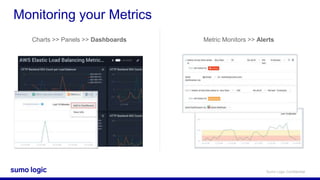
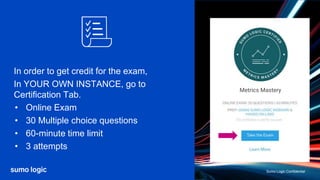
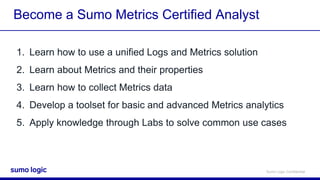
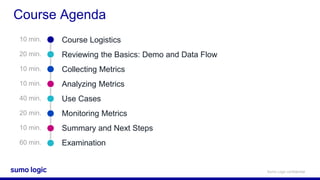
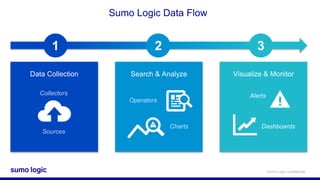
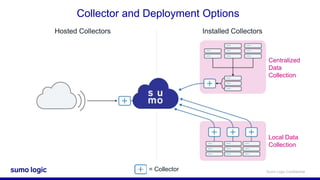
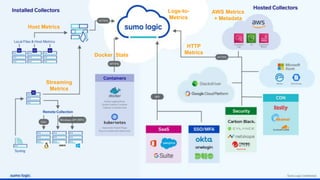
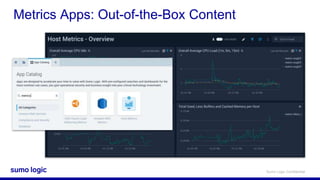
This document outlines the agenda and logistics for a Sumo Metrics Certified Analyst training course. The course will teach students how to use a unified logs and metrics solution, collect metrics data, analyze metrics using tools and queries, and apply their knowledge through hands-on labs covering common use cases. These include monitoring host metrics, analyzing AWS metrics, working with different metric formats, and converting logs to metrics. Students will learn to visualize metrics using charts and dashboards, and configure metric monitors and alerts. Upon completing the course, students will take an online certification exam to test their mastery of the skills covered.






![Sumo Logic Confidential
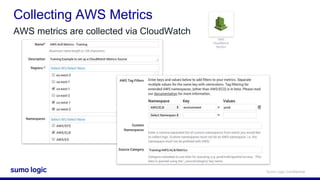
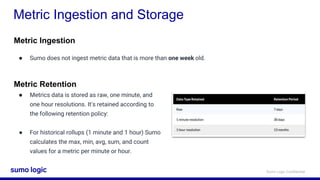
AWS Metrics
AWS metrics are collected via CloudWatch
Detail of each Metric, by source:
https://docs.aws.amazon.com/Amaz
onCloudWatch/latest/monitoring/aw
s-services-cloudwatch-metrics.html
[AWS Docs]](https://image.slidesharecdn.com/certjammetricsanalytics-190911171950/85/Sumo-Logic-Cert-Jam-Metrics-Mastery-23-320.jpg)