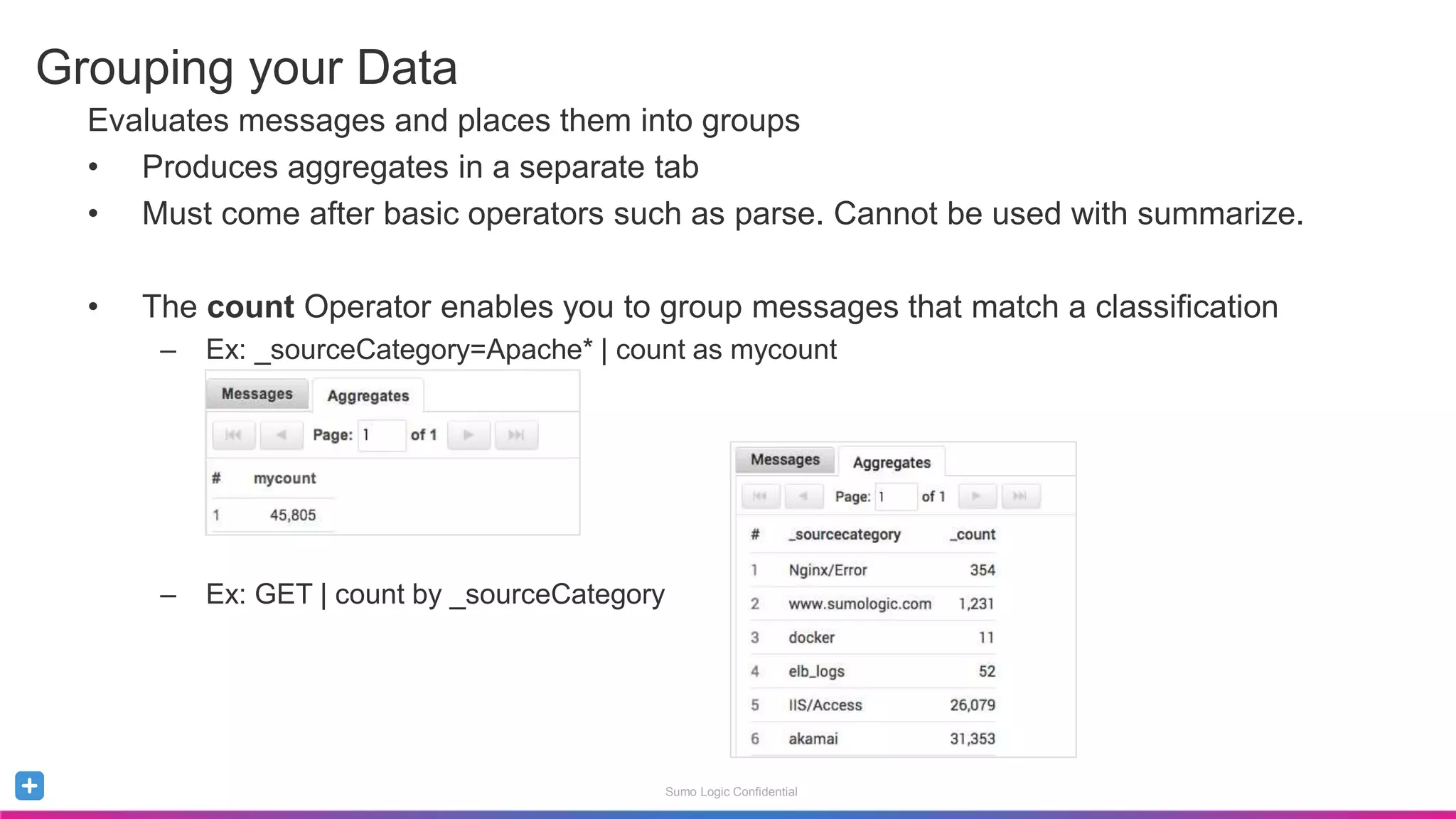
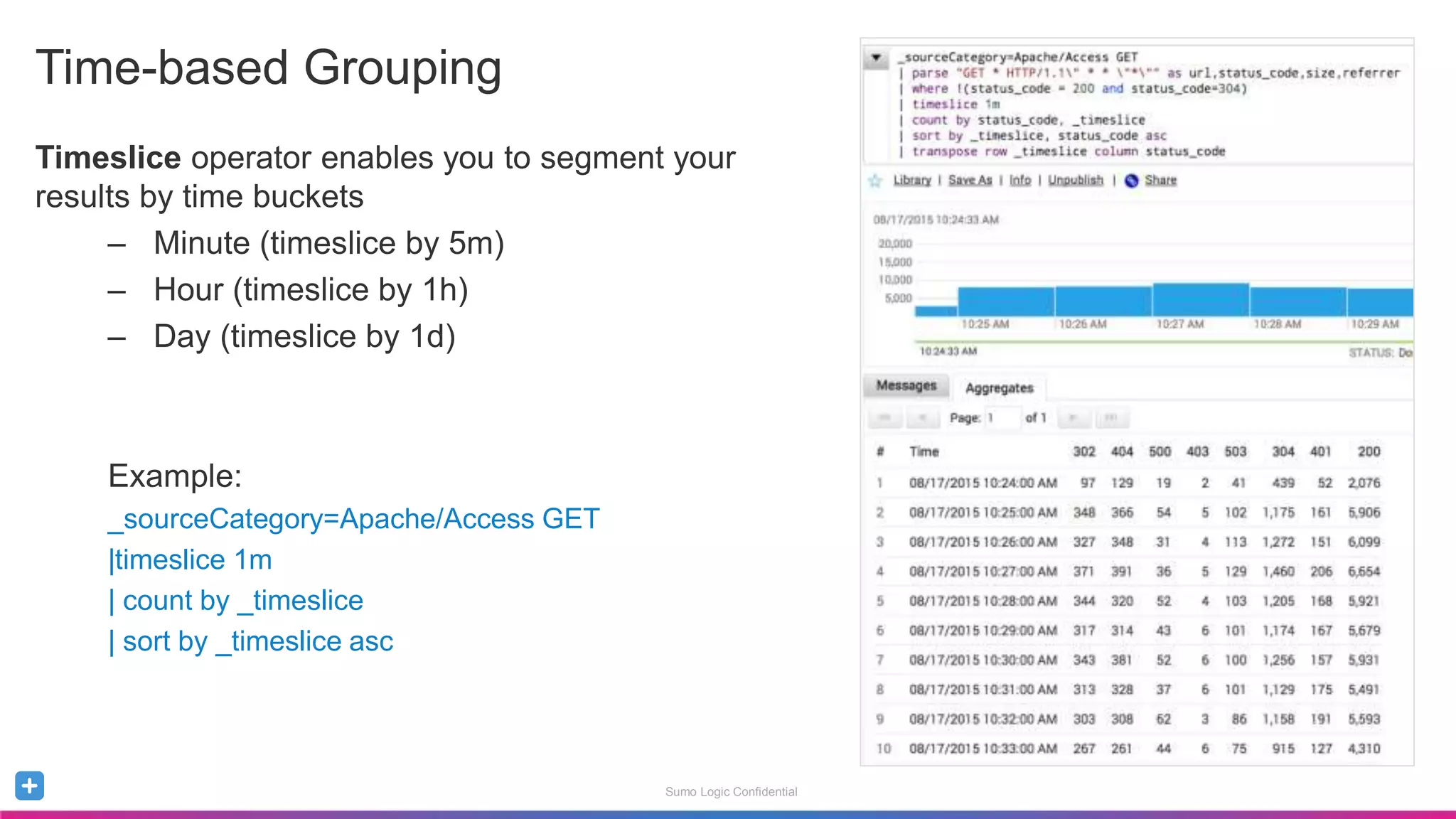
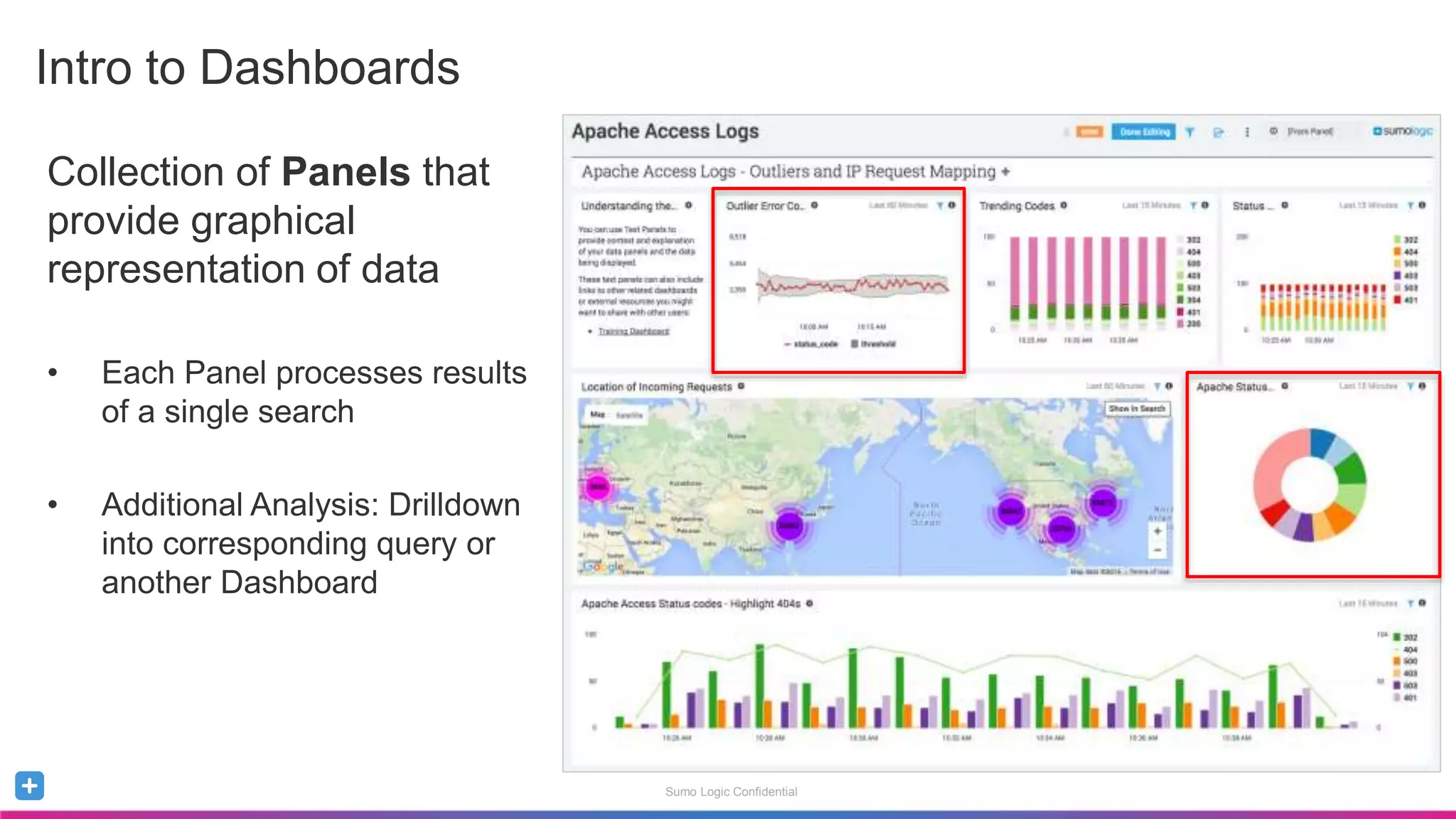
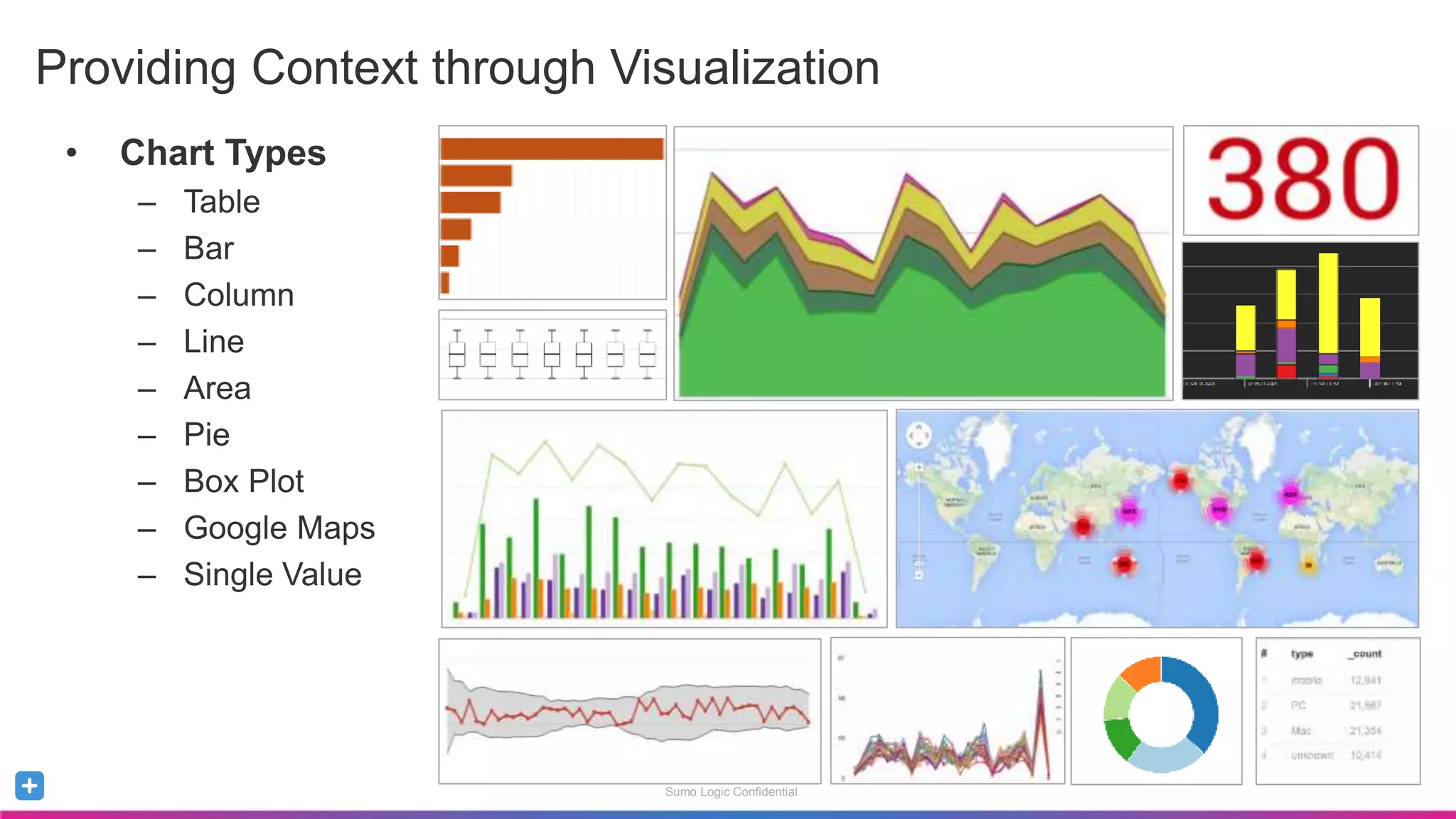
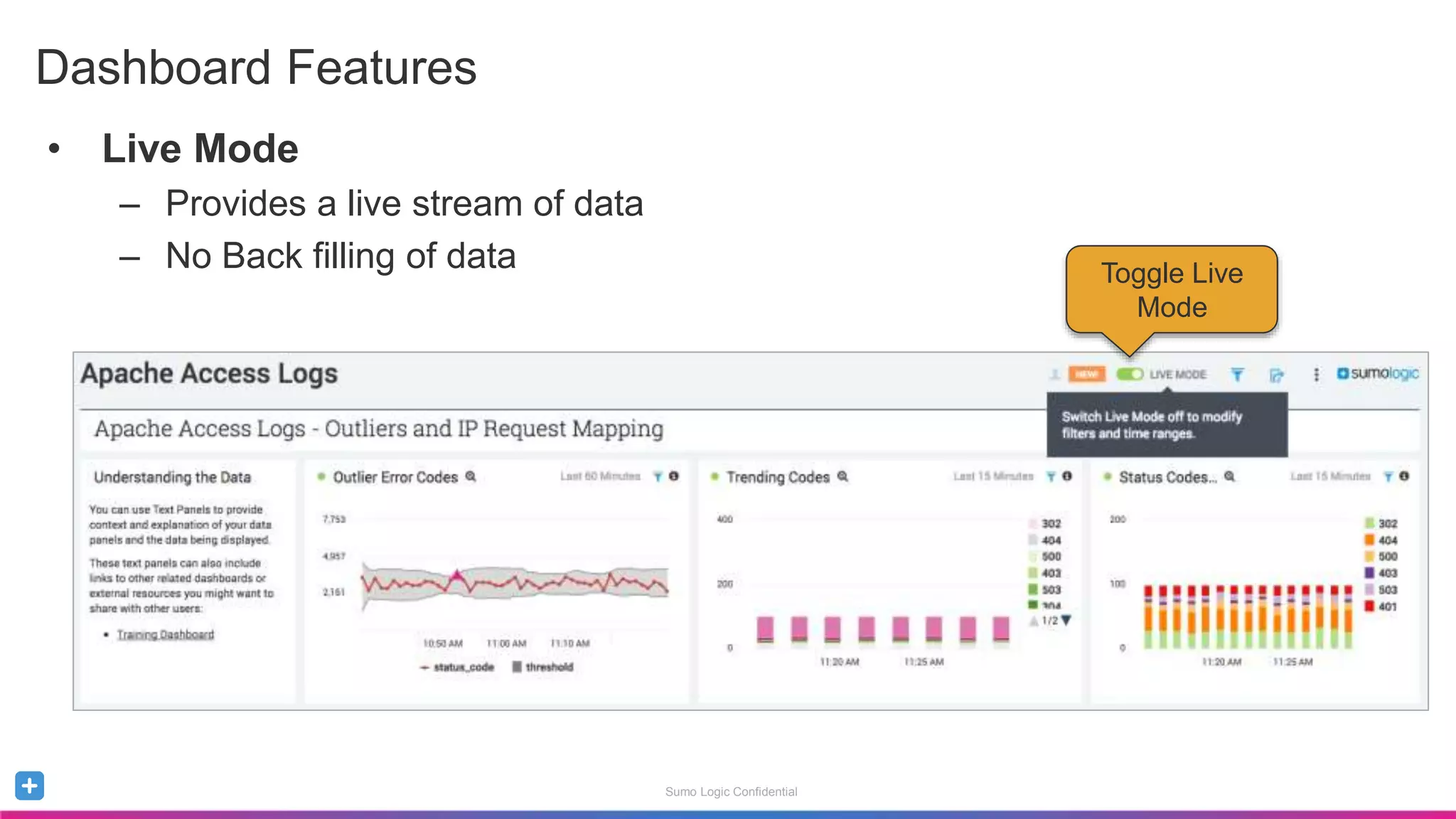
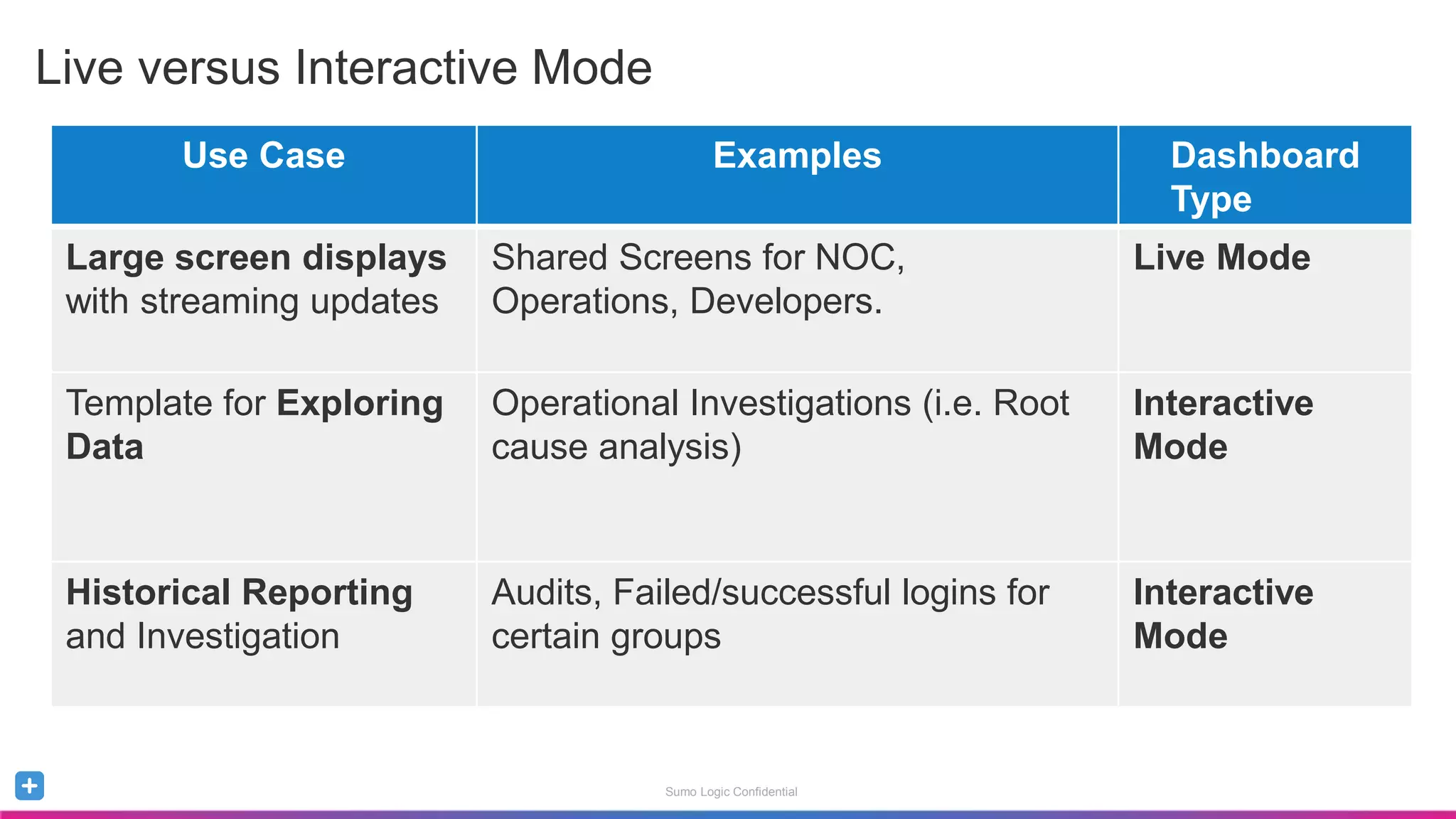
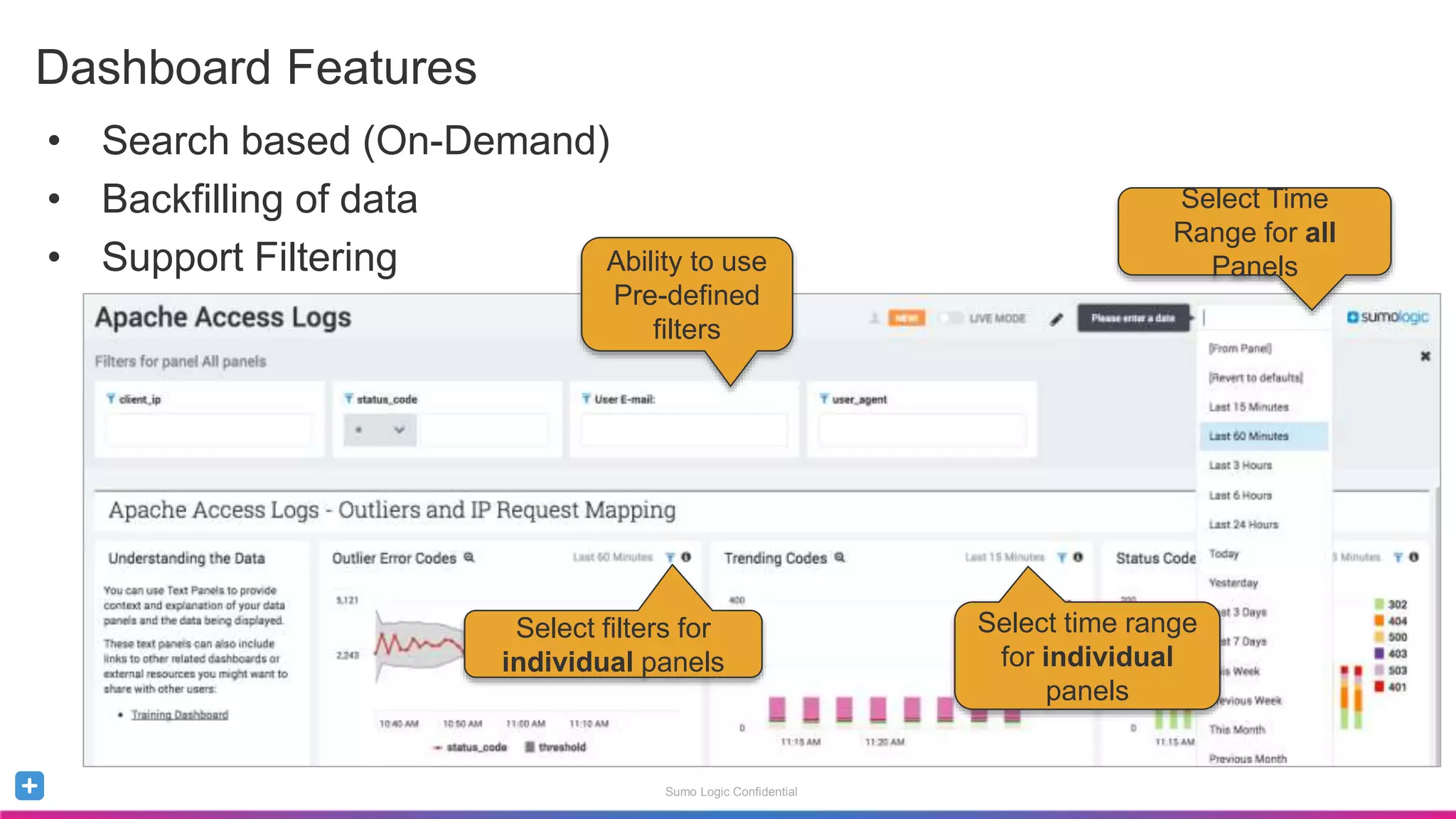
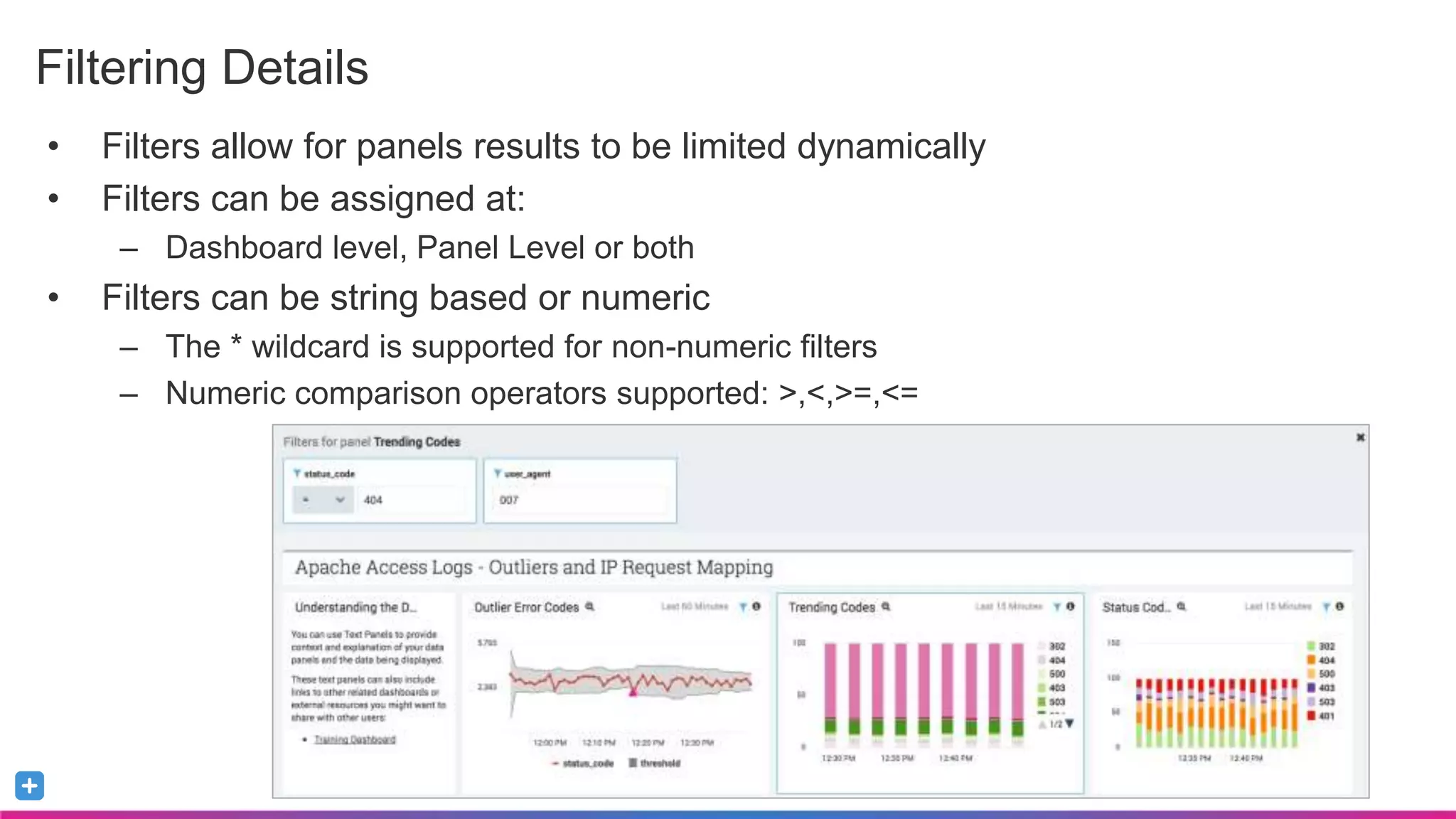
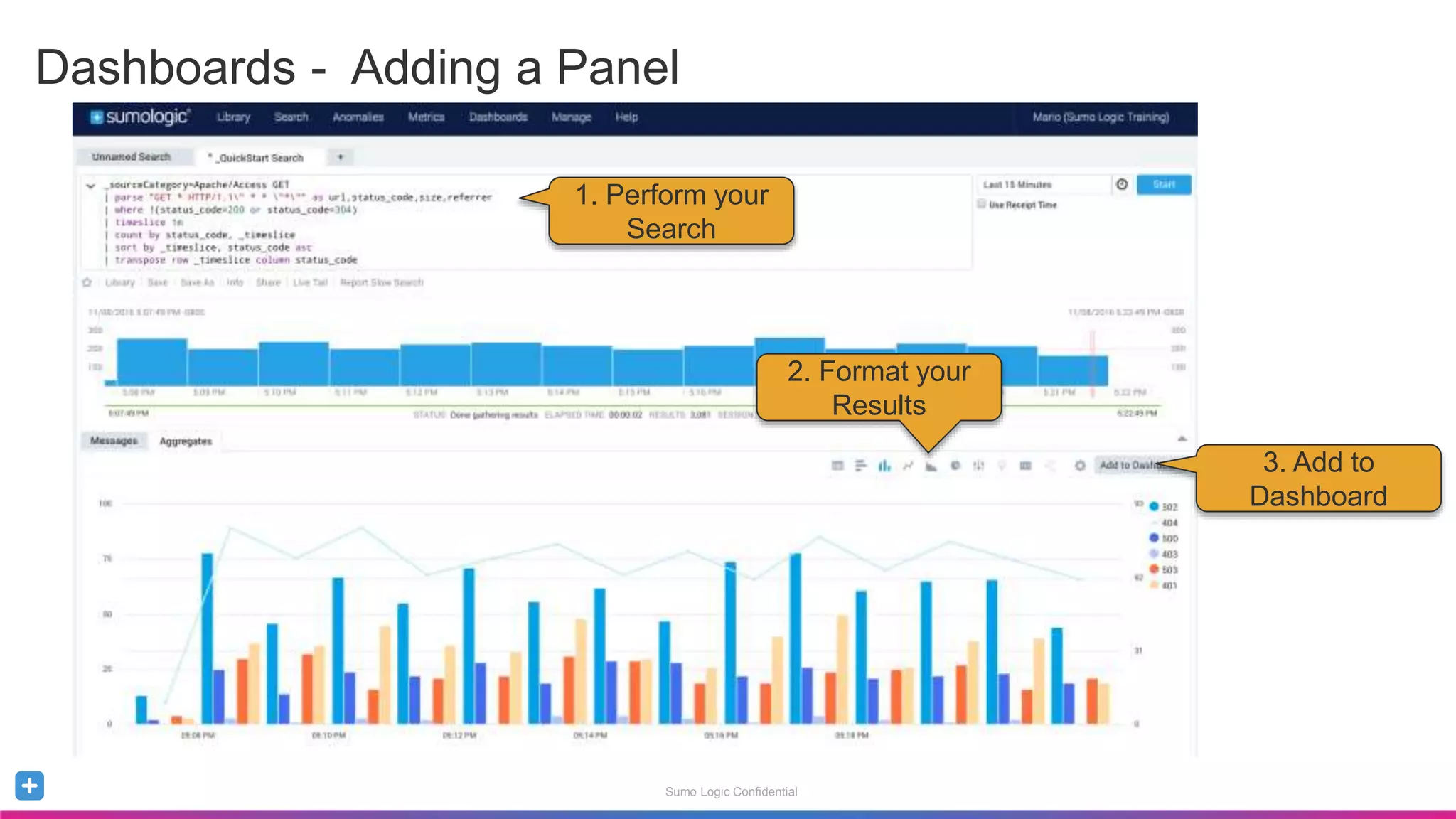
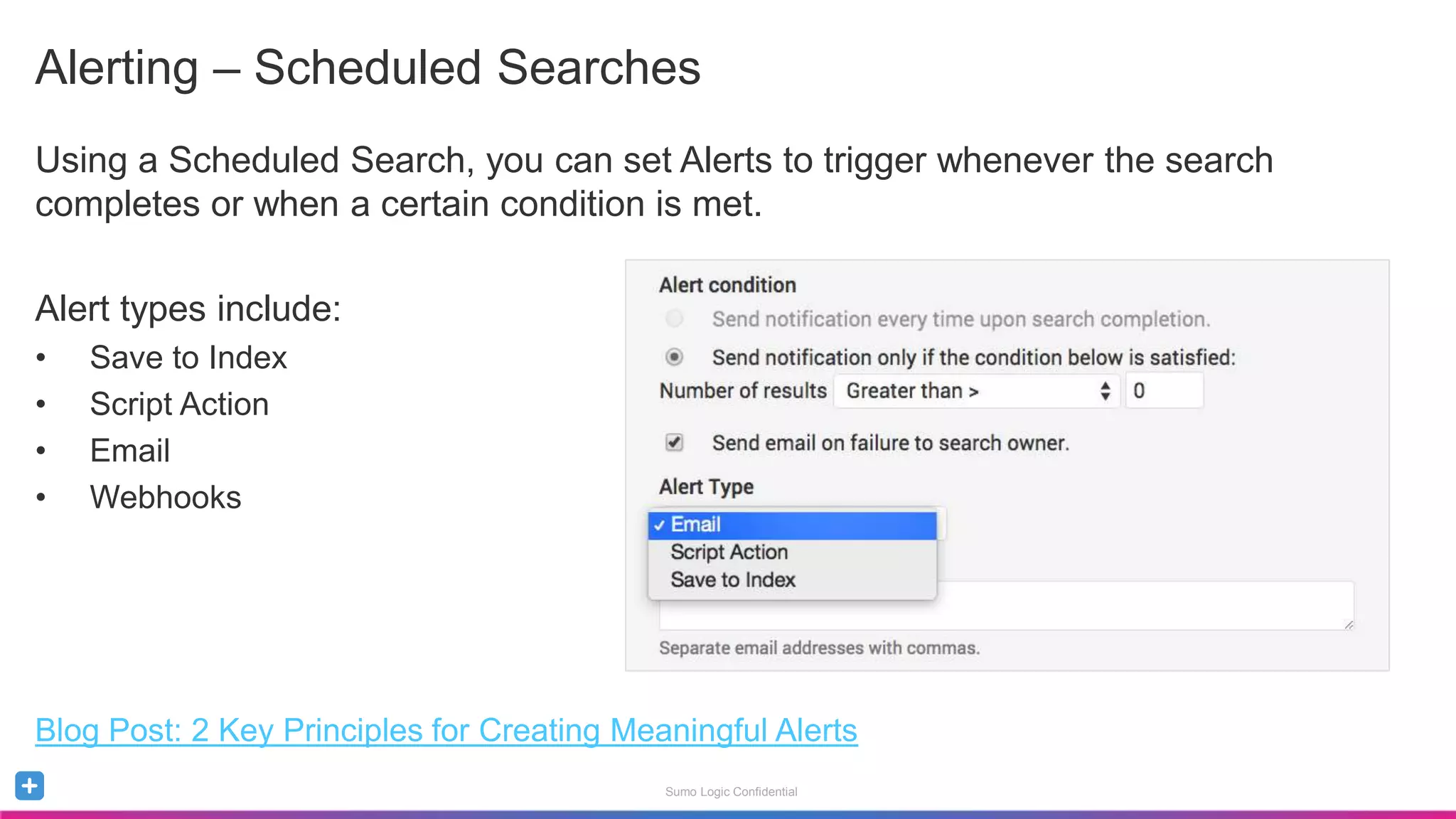
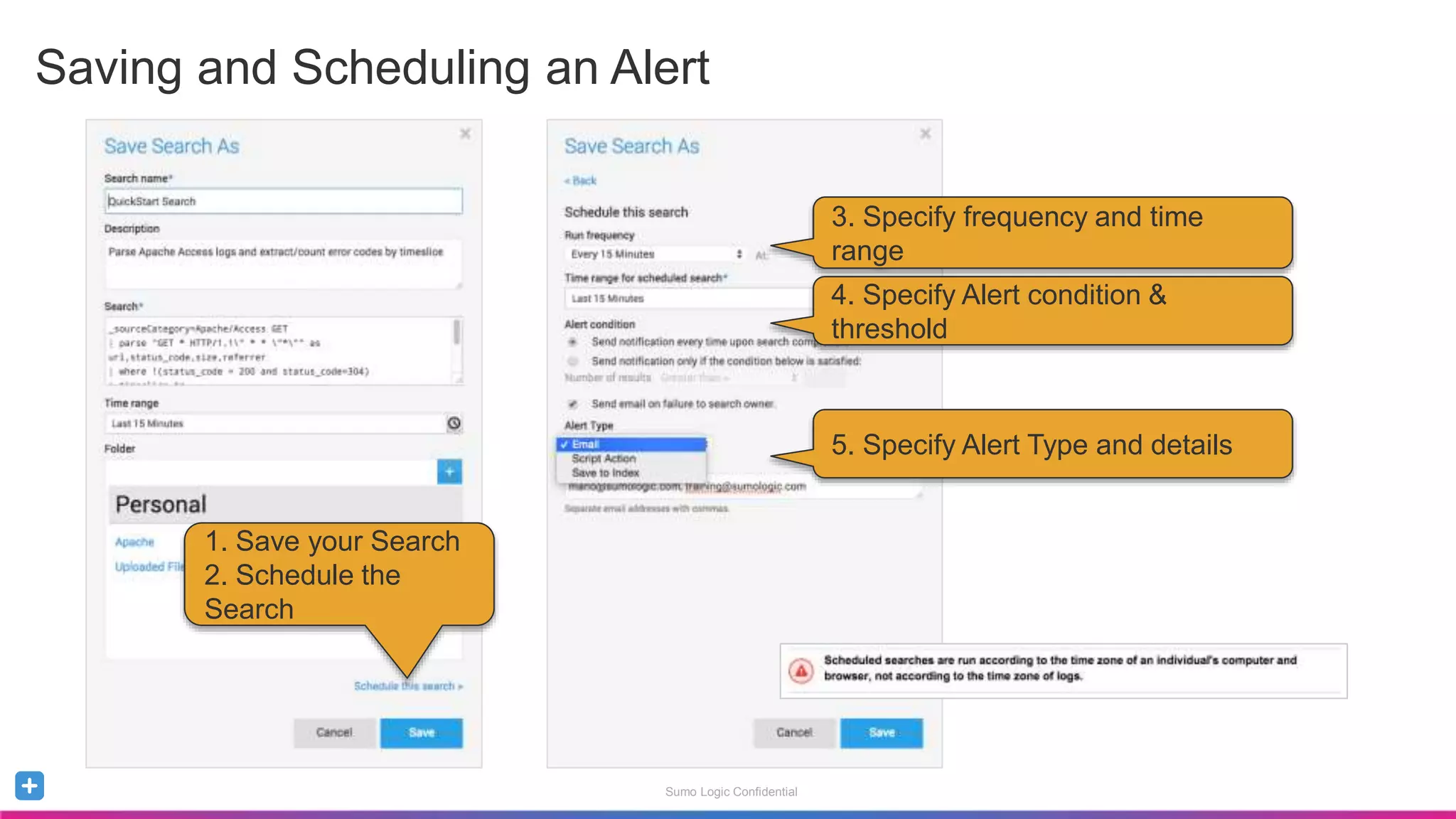
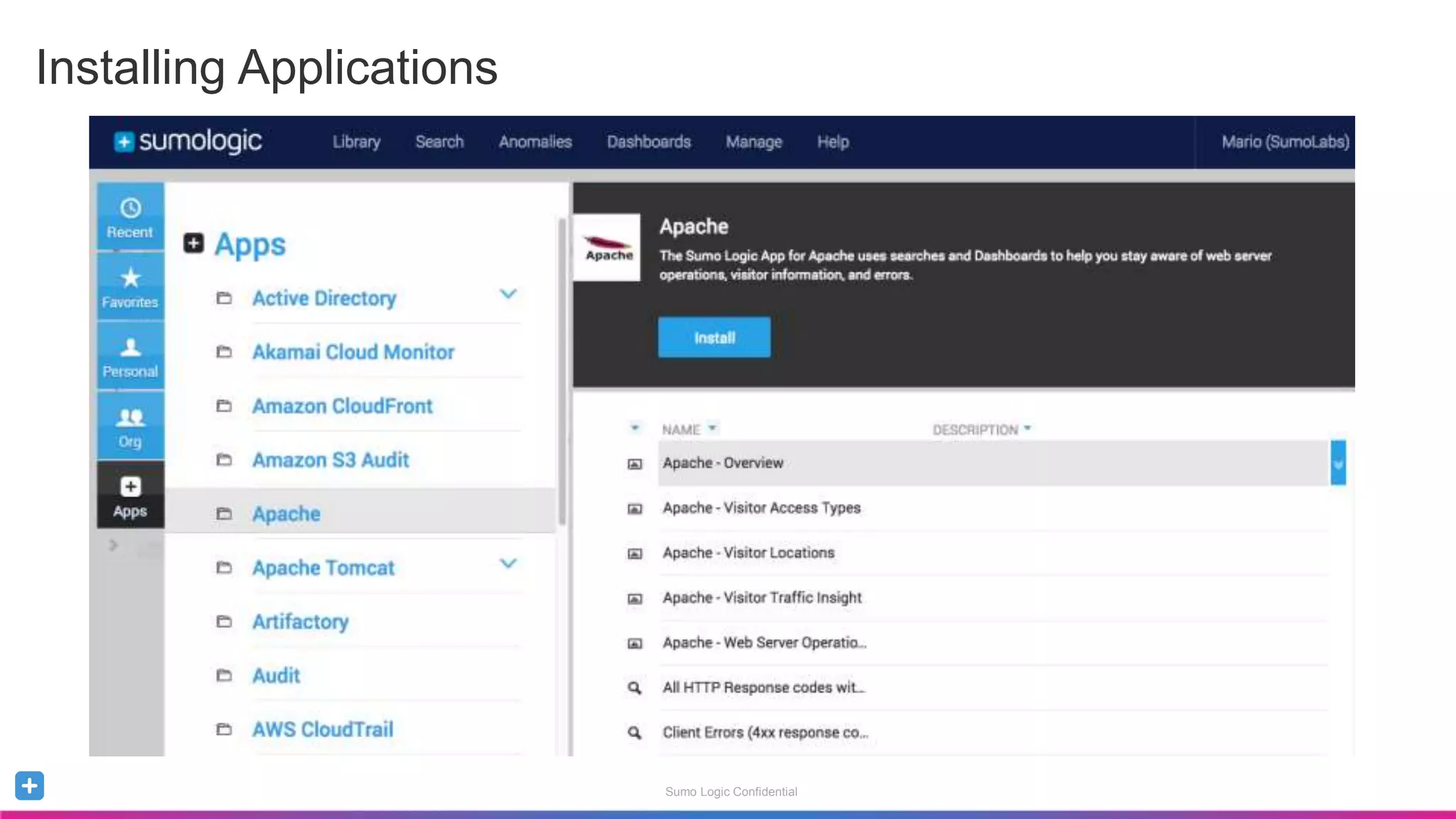
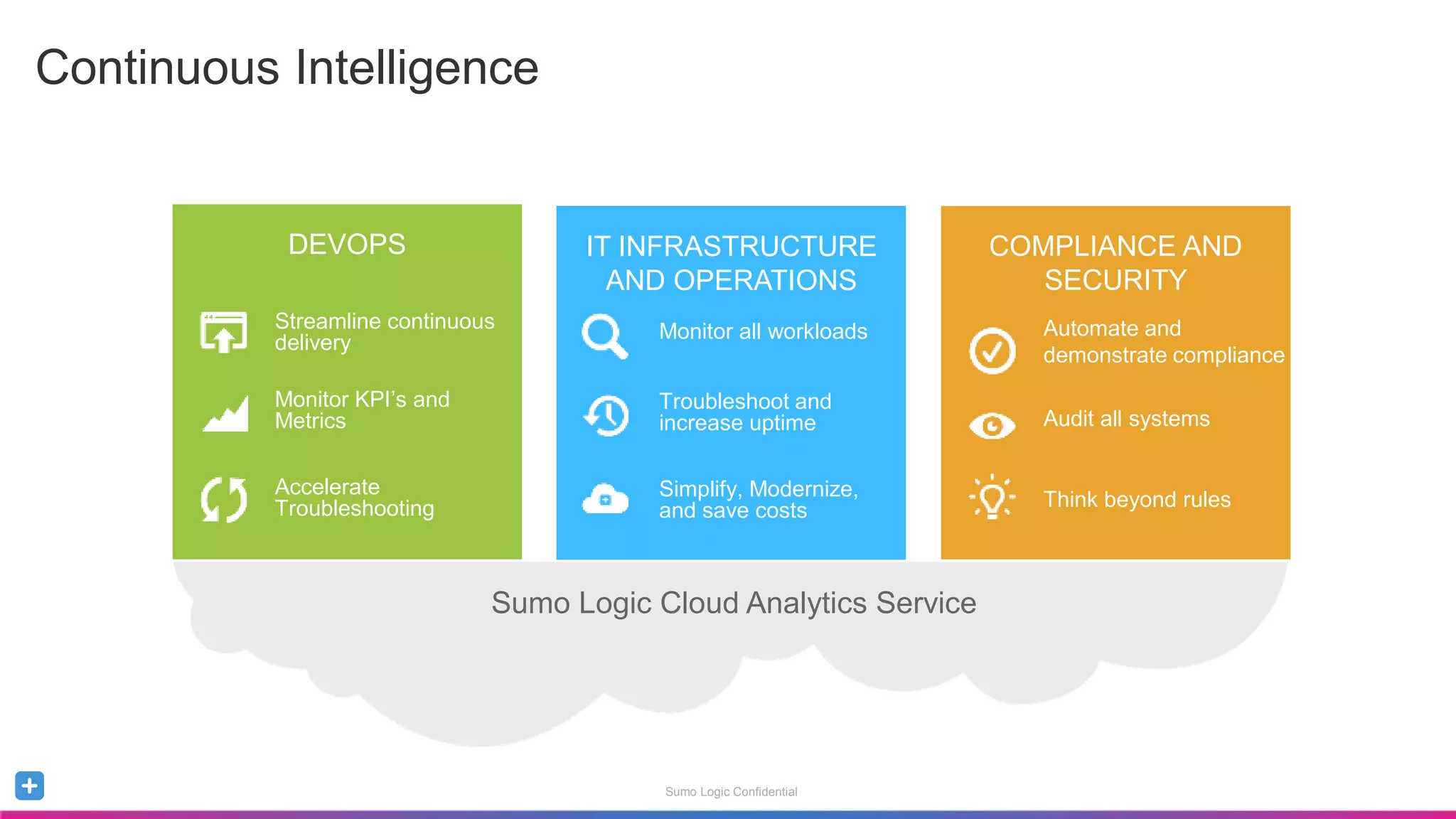
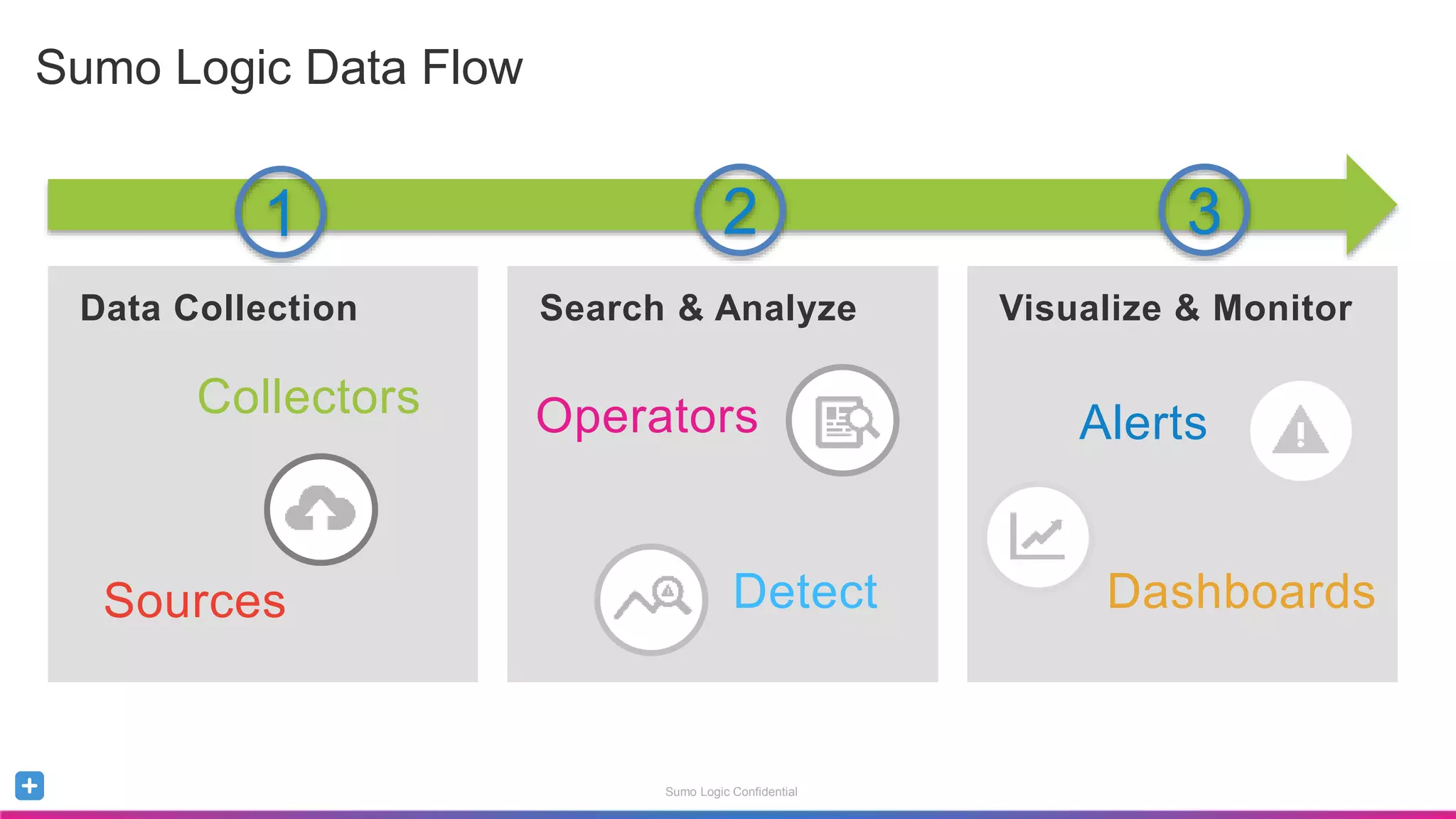
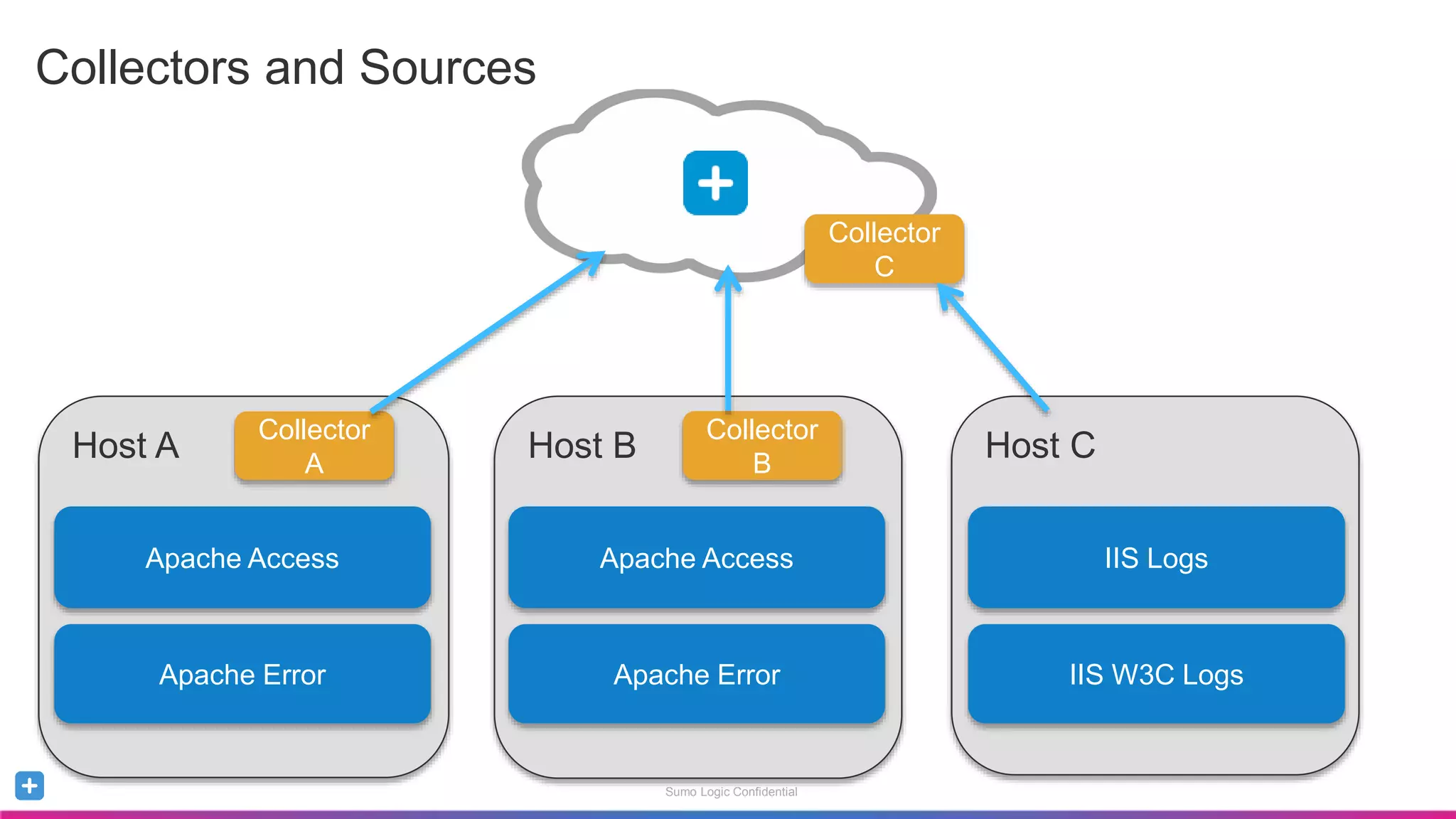
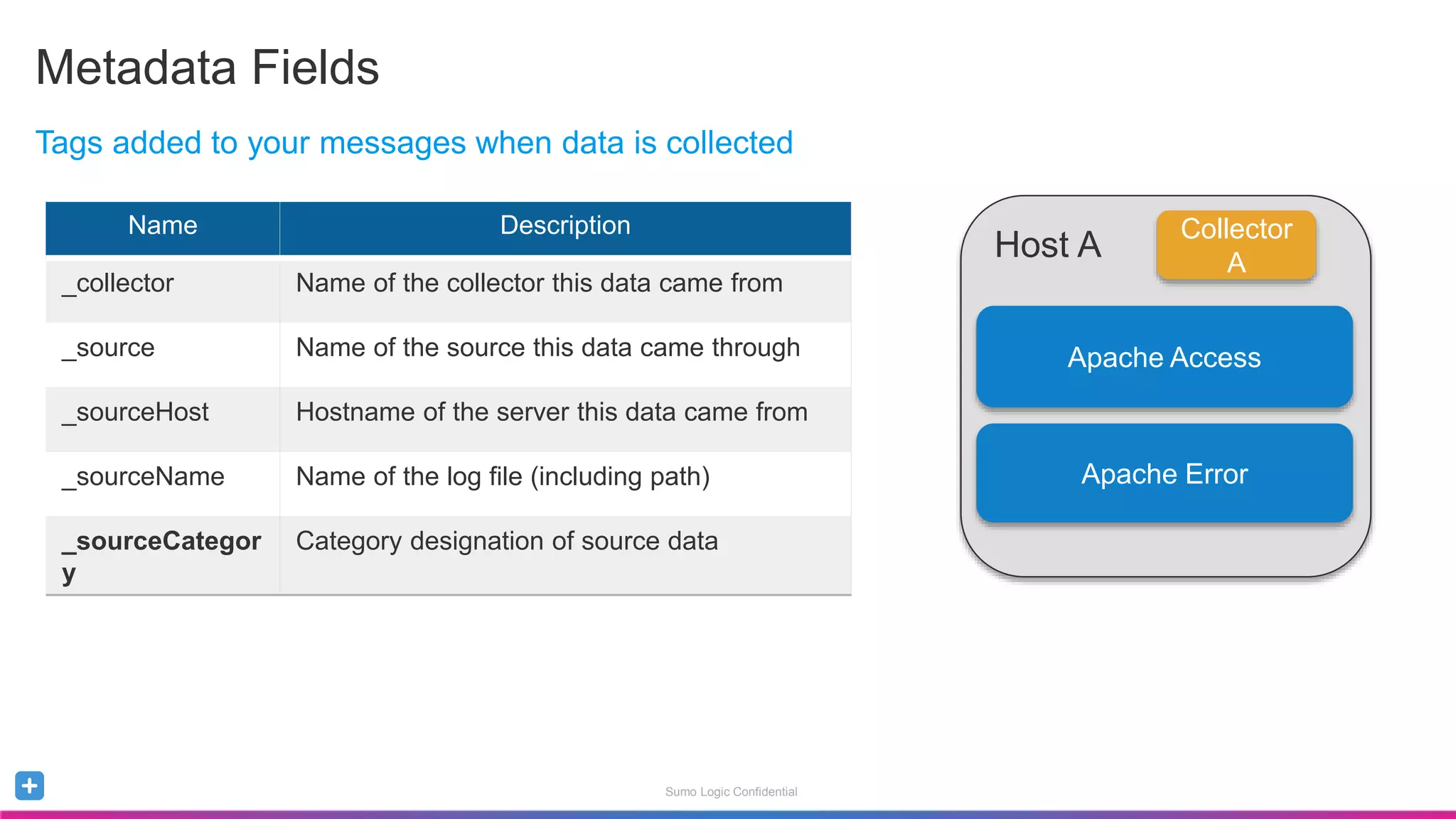
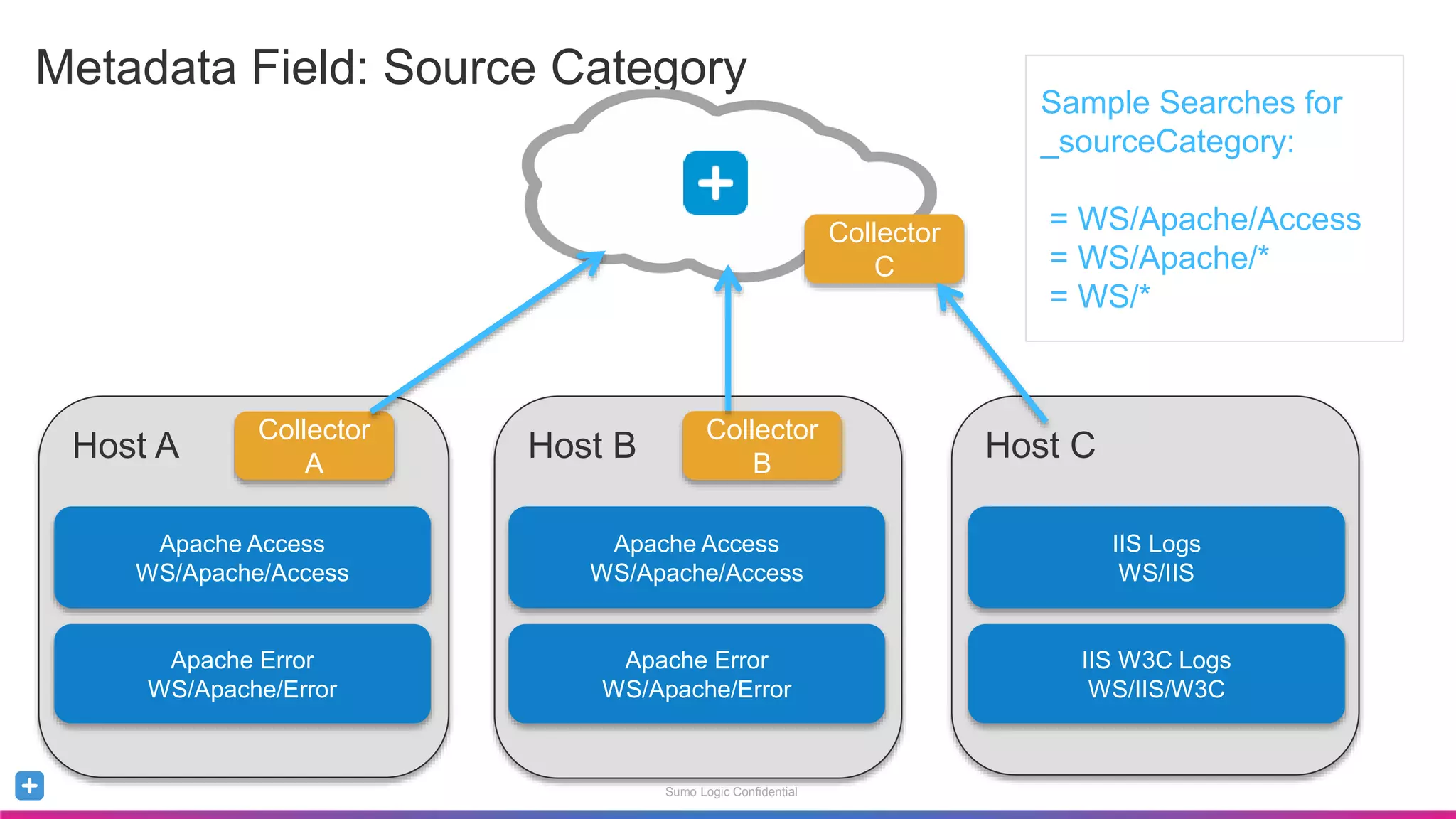
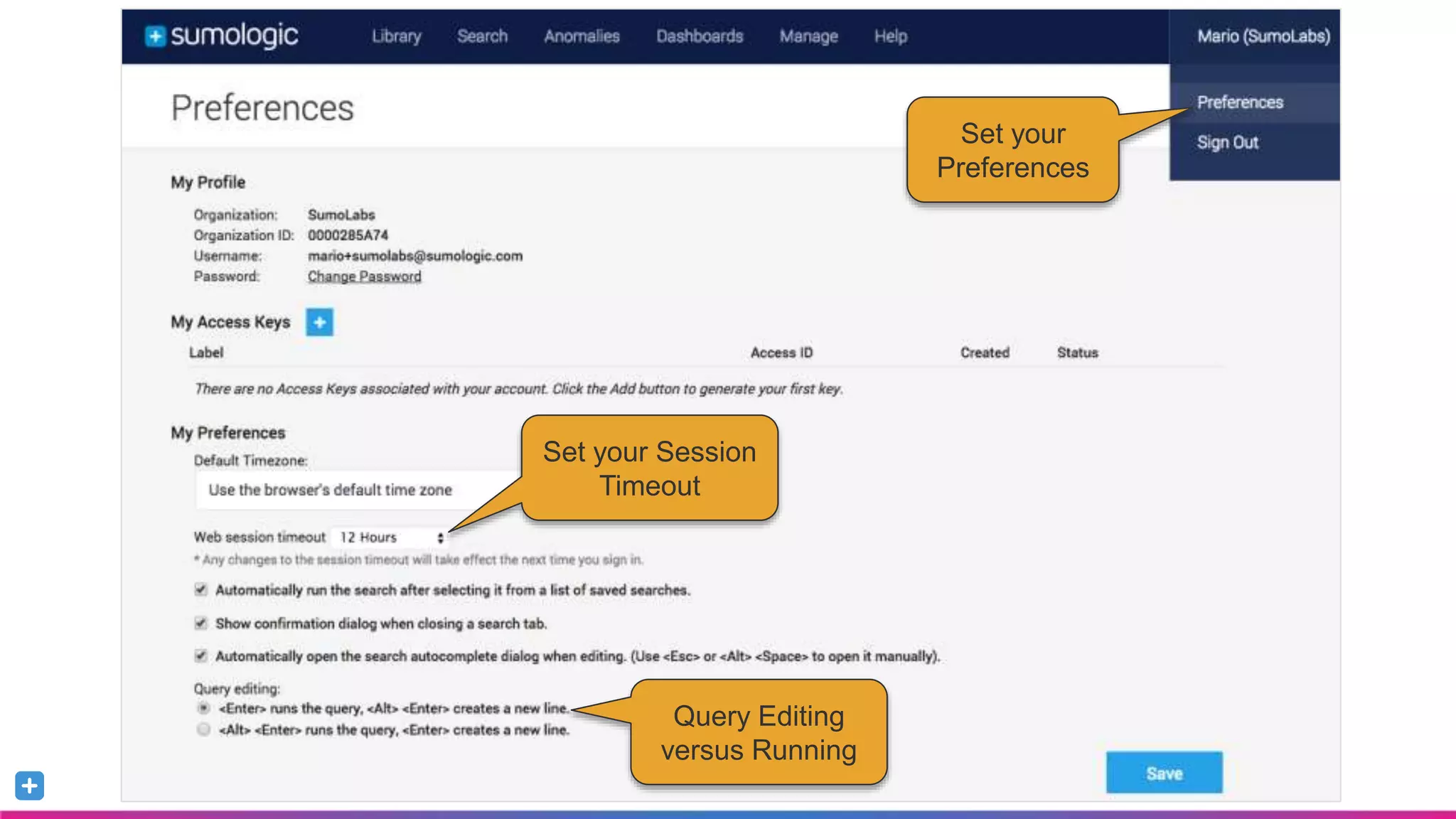
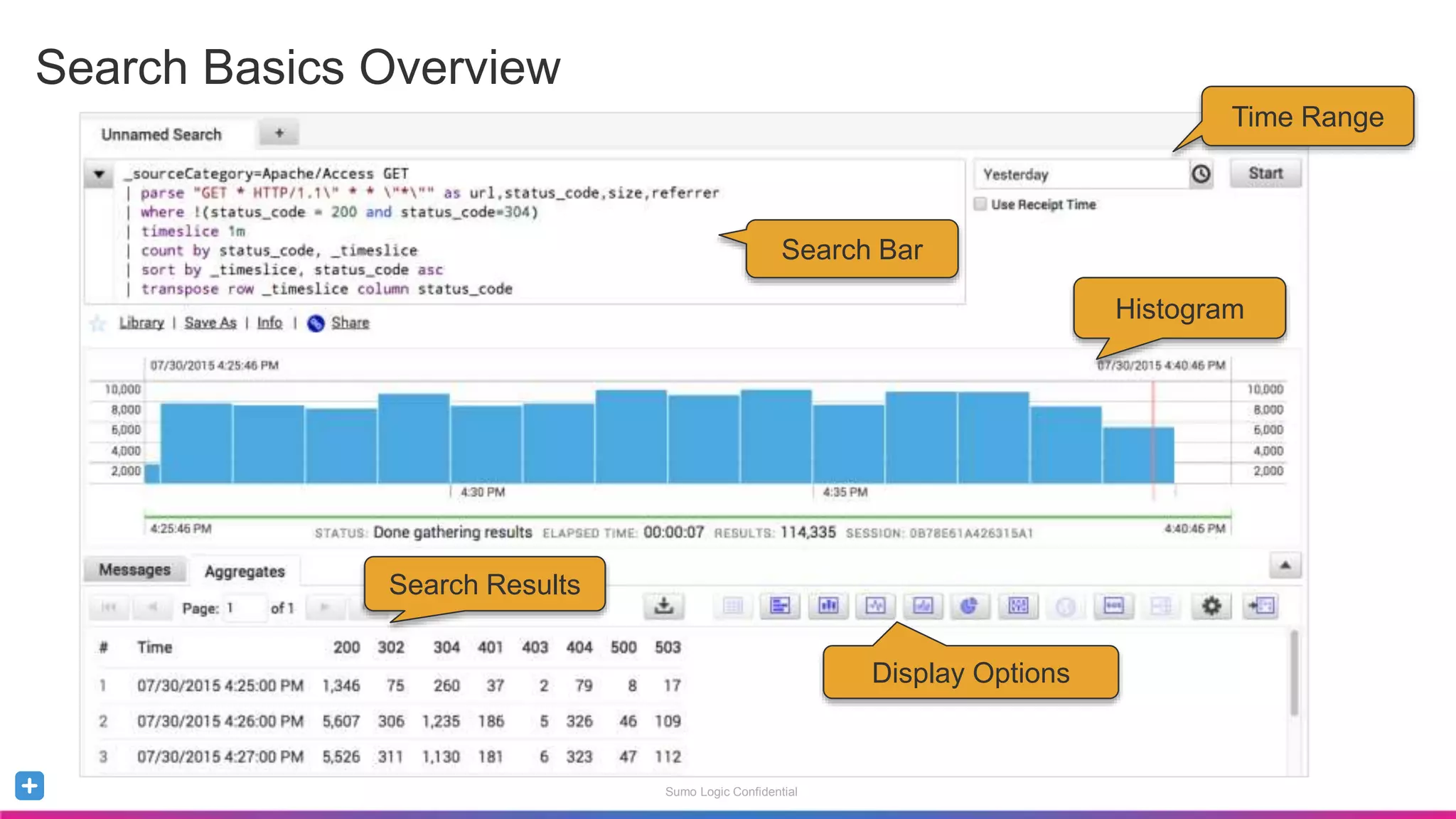
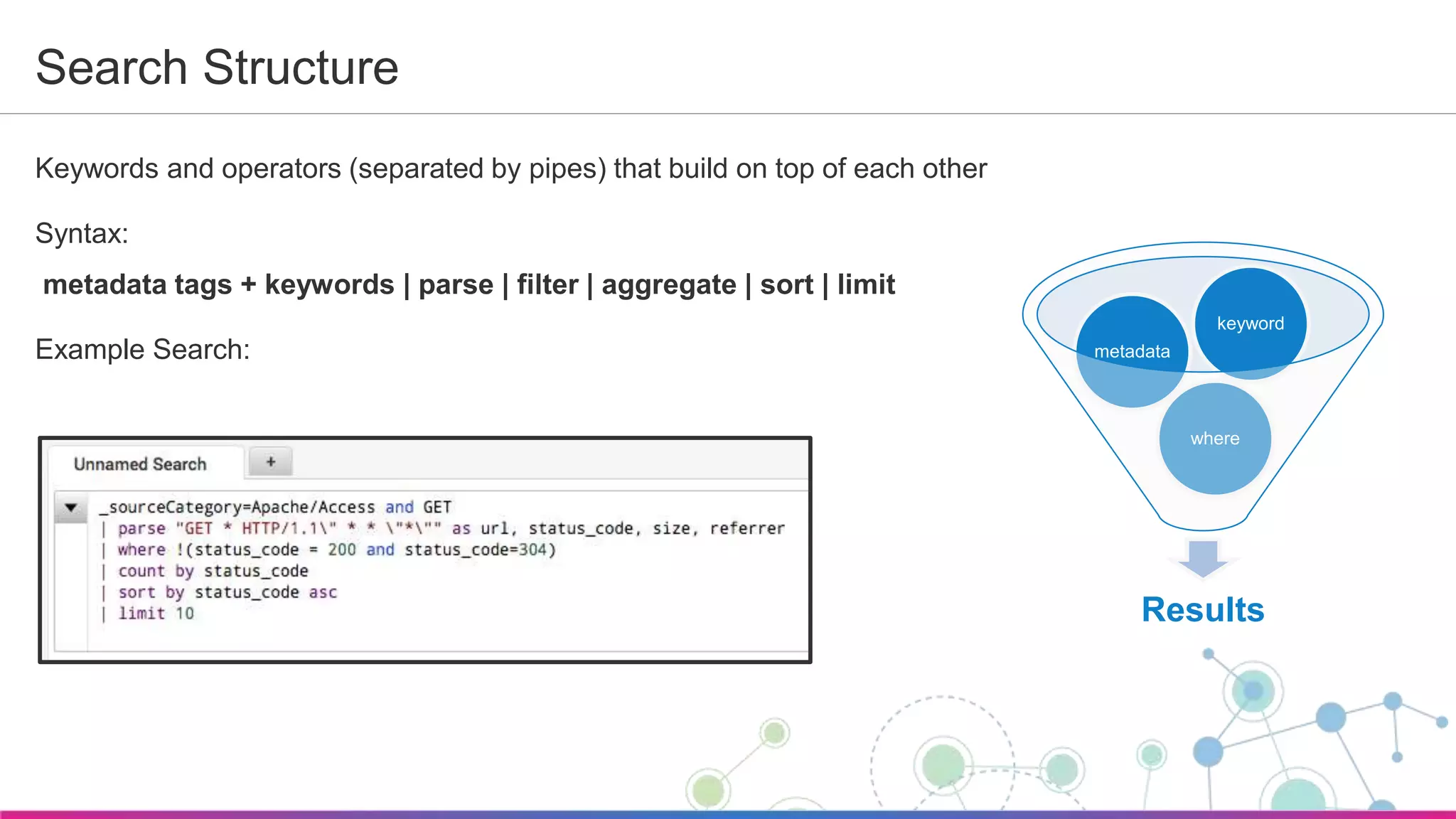
The document is a guide for a Sumo Logic webinar that covers the fundamentals of data collection, search, analysis, and visualization within the Sumo Logic platform. It includes details on managing metadata, utilizing alerts, and building dashboards to enhance operational intelligence. Key features and examples demonstrate how to maximize the use of Sumo Logic tools for effective monitoring and reporting.


![Sumo Logic Confidential
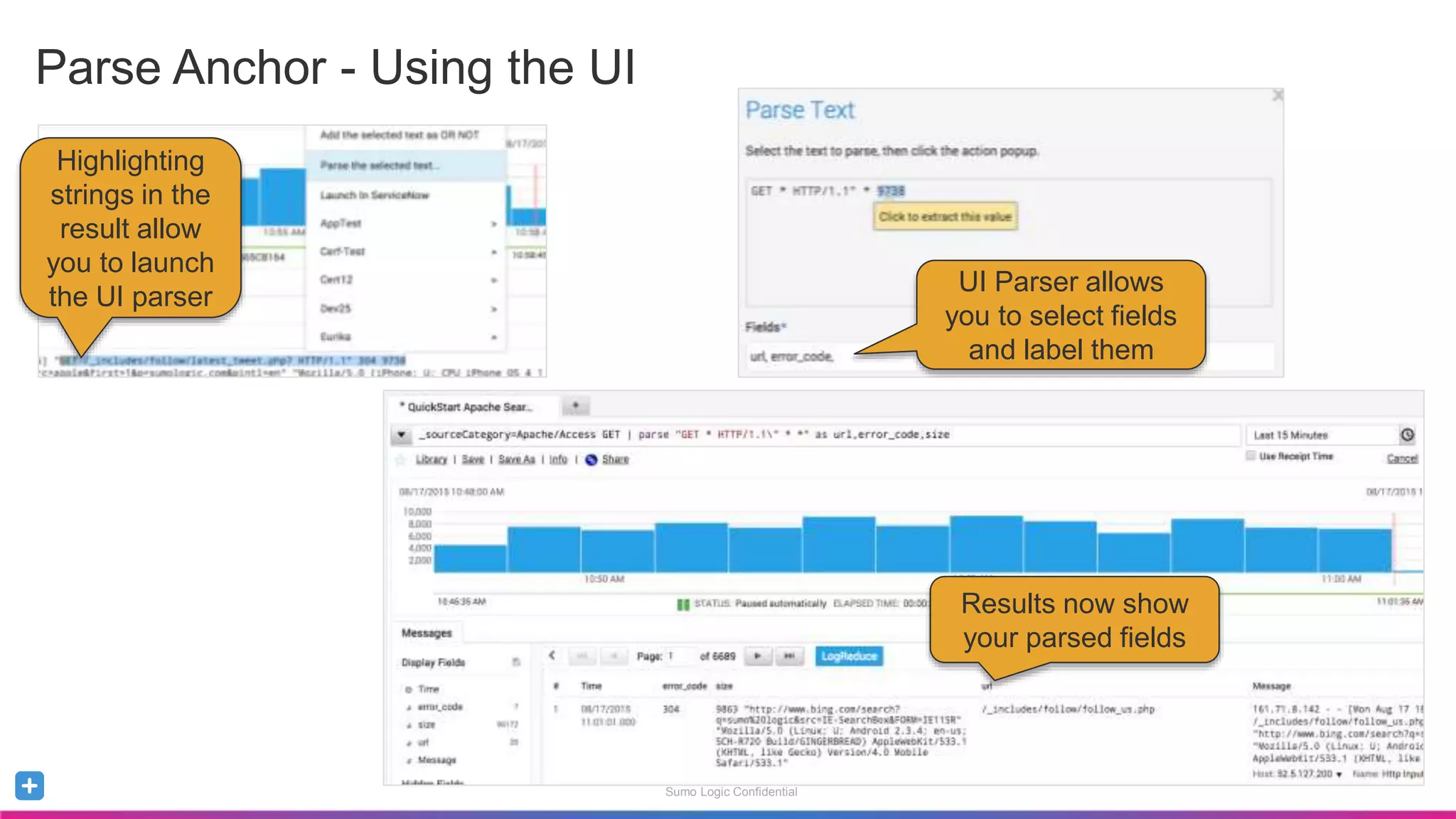
• Extracts nested information via regular expressions
• Use if the construct of the messages is inconsistent
_sourceCategory=Apache/Access
| parse regex "[A-Z]+s(?<url>/S*)sHTTP/1.d+"s(?<status_code>d+)s"
Parse Regex](https://image.slidesharecdn.com/sumologicquickstartdec2016-161215234720/75/Sumo-Logic-QuickStart-Webinar-Dec-2016-25-2048.jpg)