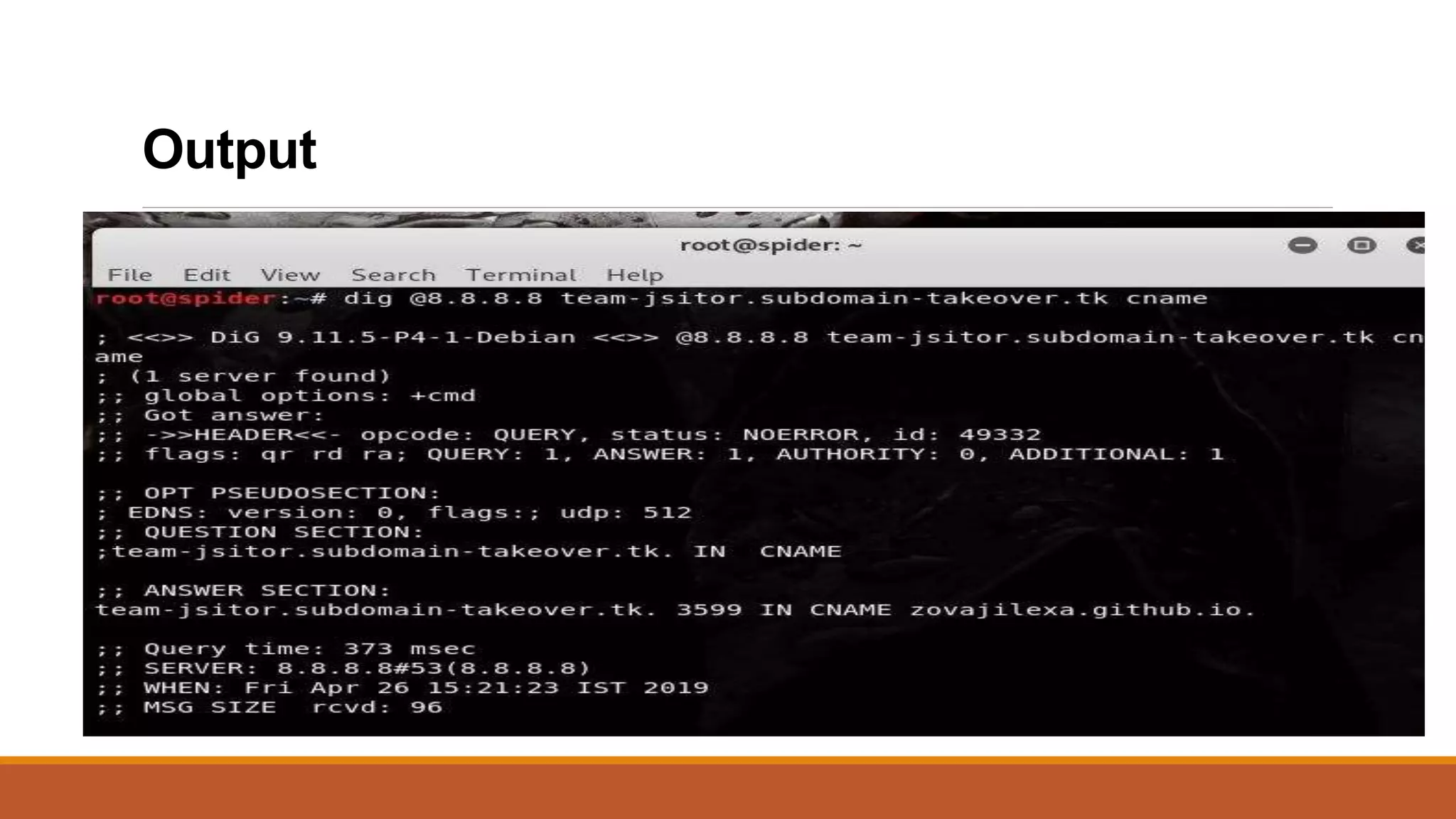
This document explains subdomain takeover, a vulnerability resulting from misconfigured DNS CNAME records that can allow attackers to claim subdomains pointing to unutilized external services. It describes what subdomains and CNAME records are, the impact of subdomain takeovers, and methods for discovering CNAME records. Mitigation strategies include removing outdated DNS configurations and utilizing domain monitoring services.