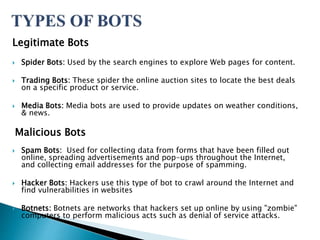
This document discusses different types of bots on the internet, including spam bots. It describes how spam bots work by harvesting email addresses from websites and messages to build mailing lists for sending unsolicited emails. Spam bots pose a significant threat to cybersecurity as they enable cybercrimes like phishing and denial of service attacks. The document provides source code examples for a basic spam bot written in Python.